Normal view
Microsoft rolls out native Sysmon monitoring in Windows 11
Microsoft is Giving the FBI BitLocker Keys
Microsoft gives the FBI the ability to decrypt BitLocker in response to court orders: about twenty times per year.
It’s possible for users to store those keys on a device they own, but Microsoft also recommends BitLocker users store their keys on its servers for convenience. While that means someone can access their data if they forget their password, or if repeated failed attempts to login lock the device, it also makes them vulnerable to law enforcement subpoenas and warrants.
Microsoft: January update shutdown bug affects more Windows PCs
Microsoft fixes bug causing password sign-in option to disappear
Microsoft to disable NTLM by default in future Windows releases
Microsoft fixes Outlook bug blocking access to encrypted emails
Windows 11 KB5074105 update fixes boot, sign-in, and activation issues
Microsoft links Windows 11 boot failures to failed December 2025 update
Microsoft Office zero-day lets malicious documents slip past security checks
Microsoft issued an emergency patch for a high-severity zero-day vulnerability in Office that allows attackers to bypass document security checks and is being exploited in the wild via malicious files.
Microsoft pushed the emergency patch for the zero‑day, tracked as CVE-2026-21509, and classified it as a “Microsoft Office Security Feature Bypass Vulnerability” with a CVSS score of 7.8 out of 10.
The flaw allows attackers to bypass Object Linking and Embedding (OLE) mitigations that are designed to block unsafe COM/OLE controls inside Office documents. This means a malicious attachment could infect a PC despite built-in protections.
In a real-life scenario, an attacker creates a fake Word, Excel, or PowerPoint file containing hidden “mini‑programs” or special objects. They can run code and do other things on the affected computer. Normally, Office has safety checks that would block those mini-programs because they’re risky.
However, the vulnerability allows the attacker to tweak the file’s structure and hidden information in a way that tricks Office into thinking the dangerous mini‑program inside the document is harmless. As a result, Office skips the usual security checks and allows the hidden code to run.
As code to test the bypass is publicly available, increasing the risk of exploitation, users are under urgent advice to apply the patch.

How to protect your system
What you need to do depends on which version of Office you’re using.
The affected products include Microsoft Office 2016, 2019, LTSC 2021, LTSC 2024, and Microsoft 365 Apps (both 32‑bit and 64‑bit).
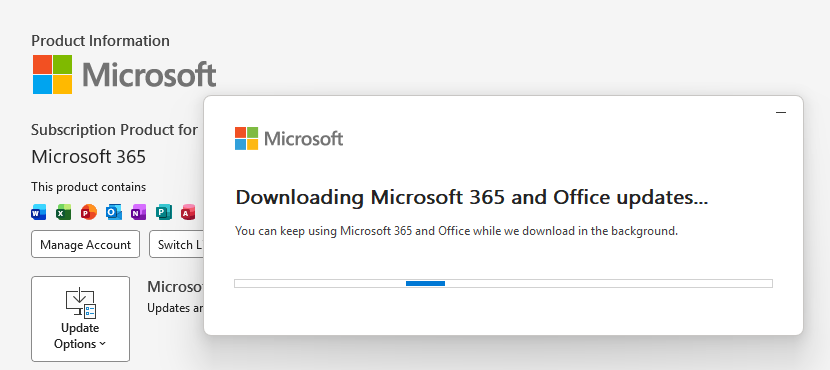
Office 2021 and later are protected via a server‑side change once Office is restarted. To apply it, close all Office apps and restart them.
Office 2016 and 2019 require a manual update. Run Windows Update with the option to update other Microsoft products turned on.
If you’re running build 16.0.10417.20095 or higher, no action is required. You can check your build number by opening any Office app, going to your account page, and selecting About for whichever application you have open. Make sure the build number at the top reads 16.0.10417.20095 or higher.
What always helps:
- Don’t open unsolicited attachments without verifying them with a trusted sender.
- Treat all unexpected documents, especially those asking to “enable content” or “enable editing,” as suspicious.
- Keep macros disabled by default and only allow signed macros from trusted publishers.
- Use an up-to-date real-time anti-malware solution.
- Keep your operating system and software fully up to date.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
Microsoft Office zero-day lets malicious documents slip past security checks
Microsoft issued an emergency patch for a high-severity zero-day vulnerability in Office that allows attackers to bypass document security checks and is being exploited in the wild via malicious files.
Microsoft pushed the emergency patch for the zero‑day, tracked as CVE-2026-21509, and classified it as a “Microsoft Office Security Feature Bypass Vulnerability” with a CVSS score of 7.8 out of 10.
The flaw allows attackers to bypass Object Linking and Embedding (OLE) mitigations that are designed to block unsafe COM/OLE controls inside Office documents. This means a malicious attachment could infect a PC despite built-in protections.
In a real-life scenario, an attacker creates a fake Word, Excel, or PowerPoint file containing hidden “mini‑programs” or special objects. They can run code and do other things on the affected computer. Normally, Office has safety checks that would block those mini-programs because they’re risky.
However, the vulnerability allows the attacker to tweak the file’s structure and hidden information in a way that tricks Office into thinking the dangerous mini‑program inside the document is harmless. As a result, Office skips the usual security checks and allows the hidden code to run.
As code to test the bypass is publicly available, increasing the risk of exploitation, users are under urgent advice to apply the patch.

How to protect your system
What you need to do depends on which version of Office you’re using.
The affected products include Microsoft Office 2016, 2019, LTSC 2021, LTSC 2024, and Microsoft 365 Apps (both 32‑bit and 64‑bit).
Office 2021 and later are protected via a server‑side change once Office is restarted. To apply it, close all Office apps and restart them.
Office 2016 and 2019 require a manual update. Run Windows Update with the option to update other Microsoft products turned on.
If you’re running build 16.0.10417.20095 or higher, no action is required. You can check your build number by opening any Office app, going to your account page, and selecting About for whichever application you have open. Make sure the build number at the top reads 16.0.10417.20095 or higher.
What always helps:
- Don’t open unsolicited attachments without verifying them with a trusted sender.
- Treat all unexpected documents, especially those asking to “enable content” or “enable editing,” as suspicious.
- Keep macros disabled by default and only allow signed macros from trusted publishers.
- Use an up-to-date real-time anti-malware solution.
- Keep your operating system and software fully up to date.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
New Microsoft Teams feature will let you report suspicious calls
Microsoft Patches Office Zero-Day Likely Exploited in Targeted Attacks
The vulnerability is tracked as CVE-2026-21509 and it can be exploited to bypass security features.
The post Microsoft Patches Office Zero-Day Likely Exploited in Targeted Attacks appeared first on SecurityWeek.
Microsoft patches actively exploited Office zero-day vulnerability
Microsoft investigates Windows 11 boot failures after January updates
Microsoft releases emergency OOB update to fix Outlook freezes
Malicious AI extensions on VSCode Marketplace steal developer data
Microsoft: Outlook for iOS crashes, freezes due to coding error
Phishers Abuse SharePoint in New Campaign Targeting Energy Sector
Threat actors are leveraging the file-sharing service for payload delivery in AitM phishing and BEC attacks.
The post Phishers Abuse SharePoint in New Campaign Targeting Energy Sector appeared first on SecurityWeek.