March 2026 Patch Tuesday fixes two zero-day vulnerabilities
Microsoft releases important security updates on the second Tuesday of every month, known as Patch Tuesday. This month’s update fixes 79 Microsoft CVEs including two zero-day vulnerabilities.
Microsoft defines a zero-day as “a flaw in software for which no official patch or security update is available yet.” So, since the patch is now available, those two are no longer zero-days. There is also no reason to believe they were ever actively exploited.
But let’s have a look at the possible consequences if you don’t install the update.
The vulnerability tracked as CVE-2026-21262 (CVSS score 8.8 out of 10) is a bug in Microsoft SQL Server that lets a logged-in user quietly climb the privilege ladder and potentially become a full database administrator (sysadmin). With that level of control, they can read, change, or delete data, create new accounts, and tamper with database configurations or jobs. Where SQL Server is supposed to check what each user is allowed to do, in this case it can be tricked into granting more power than intended.
There is no user interaction required once the attacker has that foothold: exploitation can happen over the network using crafted SQL requests that abuse the flawed permission checks. In a typical real‑world scenario, this bug would be the second act in an attack chain: first get in with low privileges, then use CVE-2026-21262 to quietly promote yourself to database king and start rewriting the script.
CVE-2026-26127 (CVSS score 7.5 out of 10) is a bug in Microsoft’s .NET platform that lets an attacker remotely crash .NET applications, effectively taking them offline for a while. The flaw lives in Microsoft .NET 9.0 and 10.0, across Windows, macOS, and Linux, in the .NET runtime or libraries, not in a specific app. In other words, it’s a bug in the engine that runs .NET code, so any app created with affected .NET versions could be at risk until patched.
The main outcome is denial of service: an attacker can cause targeted .NET processes to crash or become unstable, leading to downtime or degraded performance. For a public‑facing web API, a payment service, or any line‑of‑business app built on .NET, this can mean real‑world outages and angry users while services are repeatedly knocked over.
Vulnerabilities affecting Microsoft Office users are two remote code execution flaws in Microsoft Office (CVE-2026-26110 and CVE-2026-26113) which can both be exploited via the preview pane, and a Microsoft Excel information disclosure flaw (CVE-2026-26144), which could be used to exfiltrate data via Microsoft Copilot. Office vulnerabilities appear regularly in Patch Tuesday releases, and in this case none have been reported as actively exploited.
How to apply fixes and check if you’re protected
These updates fix security problems and keep your Windows PC protected. Here’s how to make sure you’re up to date:
1. Open Settings
- Click the Start button (the Windows logo at the bottom left of your screen).
- Click on Settings (it looks like a little gear).
2. Go to Windows Update
- In the Settings window, select Windows Update (usually at the bottom of the menu on the left).
3. Check for updates
- Click the button that says Check for updates.
- Windows will search for the latest Patch Tuesday updates.
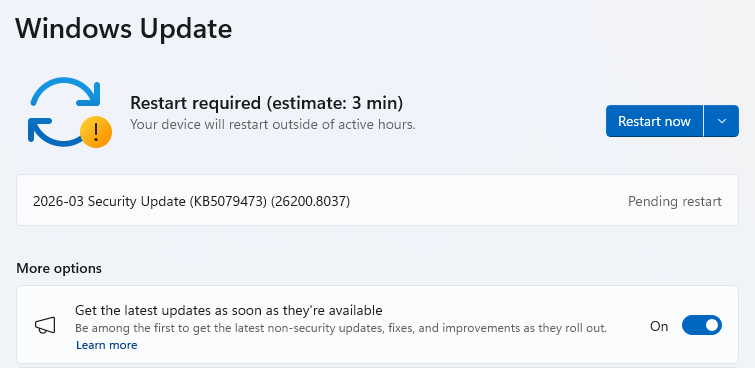
- If you have selected to get the latest updates as soon as they’re available, you may see this under More options.
- In which case you may see a Restart required message. Restart your system and the update will complete.

- If not, continue with the steps below.
4. Download and Install
- If updates are found, they’ll start downloading right away. Once complete, you’ll see a button that says Install or Restart now.
- Click Install if needed and follow any prompts. Your computer will usually need a restart to finish the update. If it does, click Restart now.

5. Double-check you’re up to date
- After restarting, go back to Windows Update and check again. If it says You’re up to date, you’re all set!
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.