[updated] A fake cloud storage alert that ends at Freecash
Last week we talked about an app that promises users they can make money testing games, or even just by scrolling through TikTok.
Imagine our surprise when we ended up on a site promoting that same Freecash app while investigating a “cloud storage” phish. We’ve all probably seen one of those. They’re common enough and according to recent investigation by BleepingComputer, there’s a
“large-scale cloud storage subscription scam campaign targeting users worldwide with repeated emails falsely warning recipients that their photos, files, and accounts are about to be blocked or deleted due to an alleged payment failure.”
Based on the description in that article, the email we found appears to be part of this campaign.

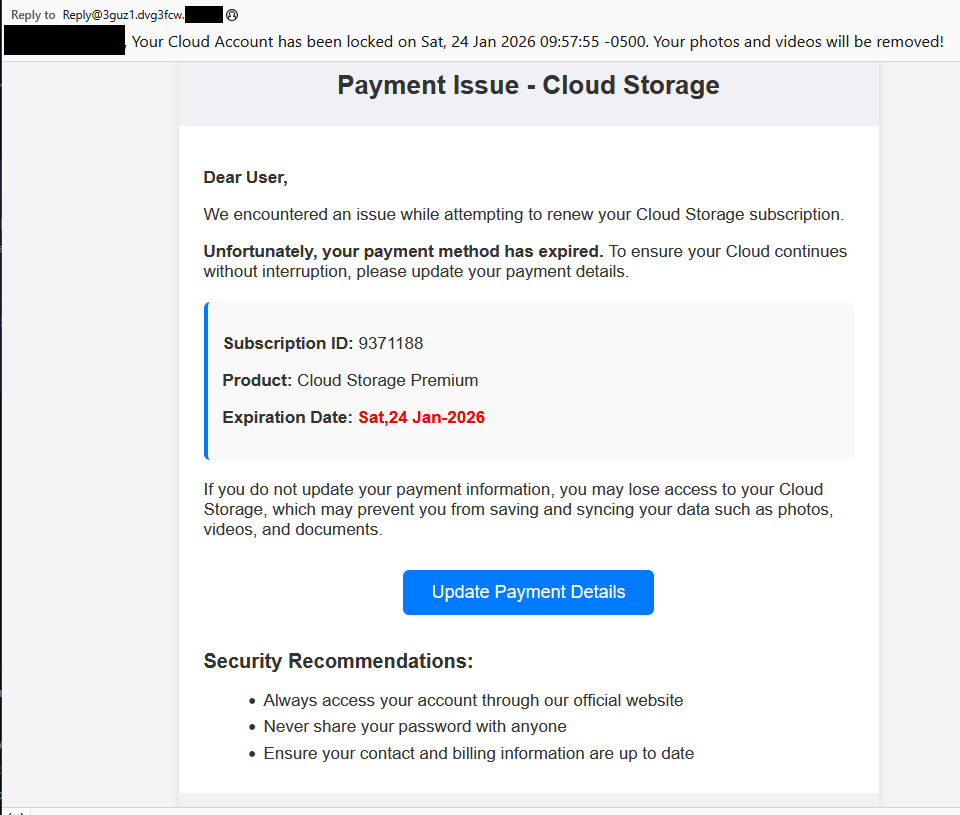
The subject line of the email is:
“{Recipient}. Your Cloud Account has been locked on Sat, 24 Jan 2026 09:57:55 -0500. Your photos and videos will be removed!”
This matches one of the subject lines that BleepingComputer listed.
And the content of the email:
“Payment Issue – Cloud Storage
Dear User,
We encountered an issue while attempting to renew your Cloud Storage subscription.
Unfortunately, your payment method has expired. To ensure your Cloud continues without interruption, please update your payment details.
Subscription ID: 9371188
Product: Cloud Storage Premium
Expiration Date: Sat,24 Jan-2026
If you do not update your payment information, you may lose access to your Cloud Storage, which may prevent you from saving and syncing your data such as photos, videos, and documents.
Update Payment Details {link button}
Security Recommendations:
- Always access your account through our official website
- Never share your password with anyone
- Ensure your contact and billing information are up to date”
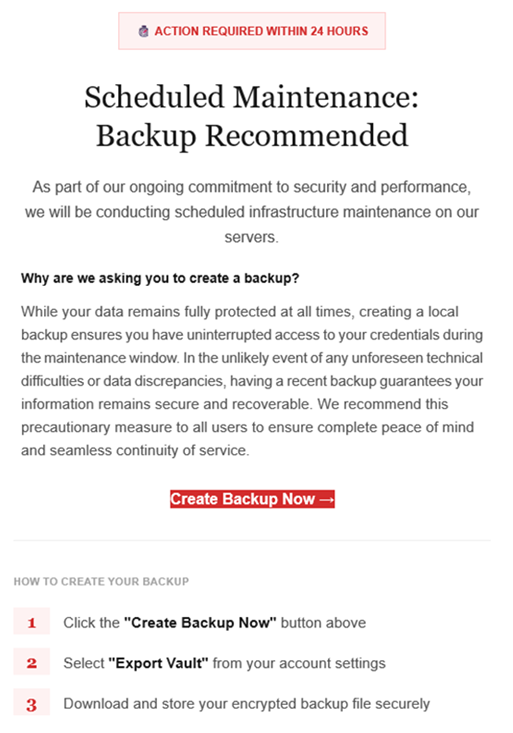
The link in the email leads to https://storage.googleapis[.]com/qzsdqdqsd/dsfsdxc.html#/redirect.html, which helps the scammer establish a certain amount of trust because it points to Google Cloud Storage (GCS). GCS is a legitimate service that allows authorized users to store and manage data such as files, images, and videos in buckets. However, as in this case, attackers can abuse it for phishing.
The redirect carries some parameters to the next website.

The feed.headquartoonjpn[.]com domain was blocked by Malwarebytes. We’ve seen it before in an earlier campaign involving an Endurance-themed phish.

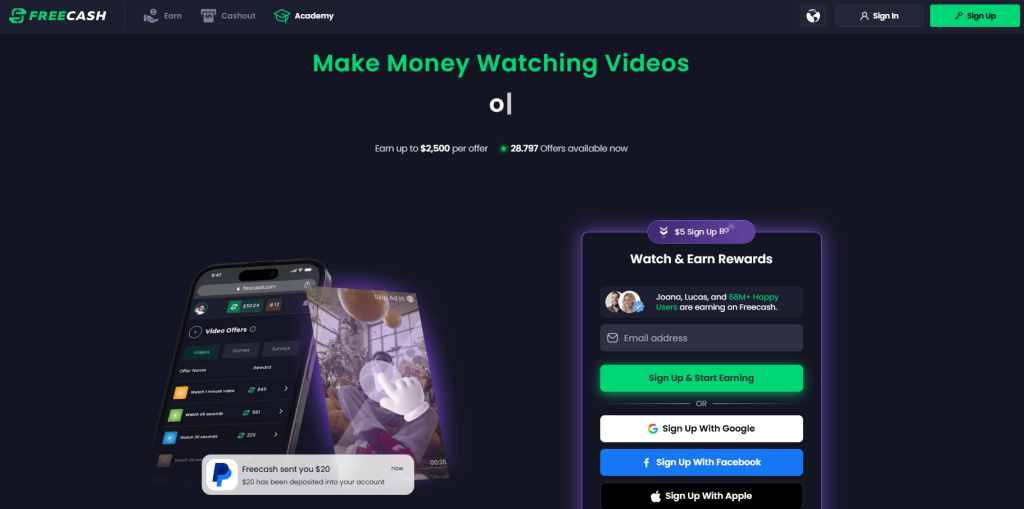
After a few more redirects, we ended up at hx5.submitloading[.]com, where a fake CAPTCHA triggered the last redirect to freecash[.]com, once it was solved.

The end goal of this phish likely depends on the parameters passed along during the redirects, so results may vary.
Rather than stealing credentials directly, the campaign appears designed to monetize traffic, funneling victims into affiliate offers where the operators get paid for sign-ups or conversions.
BleepingComputer noted that they were redirected to affiliate marketing websites for various products.
“Products promoted in this phishing campaign include VPN services, little-known security software, and other subscription-based offerings with no connection to cloud storage.”
How to stay safe
Ironically, the phishing email itself includes some solid advice:
- Always access your account through our official website.
- Never share your password with anyone.
We’d like to add:
- Never click on links in unsolicited emails without verifying with a trusted source.
- Use an up-to-date, real-time anti-malware solution with a web protection component.
- Do not engage with websites that attract visitors like this.
Pro tip: Malwarebytes Scam Guard would have helped you identify this email as a scam and provided advice on how to proceed.
Redirect flow (IOCs)
storage.googleapis[.]com/qzsdqdqsd/dsfsdxc.html
feed.headquartoonjpn[.]com
revivejudgemental[.]com
hx5.submitloading[.]com
freecash[.]com
Update February 5, 2026
Almedia GmbH, the company behind the Freecash platform, reached out to us for information about the chain of redirects that lead to their platform. And after an investigation they notified us that:
“Following Malwarebytes’ reporting and the additional information they shared with us, we investigated the issue and identified an affiliate operating in breach of our policies. That partner has been removed from our network.
Almedia does not sell user data, and we take compliance, user trust, and responsible advertising seriously.”
We don’t just report on scams—we help detect them
Cybersecurity risks should never spread beyond a headline. If something looks dodgy to you, check if it’s a scam using Malwarebytes Scam Guard, a feature of our mobile protection products. Submit a screenshot, paste suspicious content, or share a text or phone number, and we’ll tell you if it’s a scam or legit. Download Malwarebytes Mobile Security for iOS or Android and try it today!