Normal view
Patch Tuesday, February 2026 Edition
Microsoft today released updates to fix more than 50 security holes in its Windows operating systems and other software, including patches for a whopping six “zero-day” vulnerabilities that attackers are already exploiting in the wild.
![]()
Zero-day #1 this month is CVE-2026-21510, a security feature bypass vulnerability in Windows Shell wherein a single click on a malicious link can quietly bypass Windows protections and run attacker-controlled content without warning or consent dialogs. CVE-2026-21510 affects all currently supported versions of Windows.
The zero-day flaw CVE-2026-21513 is a security bypass bug targeting MSHTML, the proprietary engine of the default Web browser in Windows. CVE-2026-21514 is a related security feature bypass in Microsoft Word.
The zero-day CVE-2026-21533 allows local attackers to elevate their user privileges to “SYSTEM” level access in Windows Remote Desktop Services. CVE-2026-21519 is a zero-day elevation of privilege flaw in the Desktop Window Manager (DWM), a key component of Windows that organizes windows on a user’s screen. Microsoft fixed a different zero-day in DWM just last month.
The sixth zero-day is CVE-2026-21525, a potentially disruptive denial-of-service vulnerability in the Windows Remote Access Connection Manager, the service responsible for maintaining VPN connections to corporate networks.
Chris Goettl at Ivanti reminds us Microsoft has issued several out-of-band security updates since January’s Patch Tuesday. On January 17, Microsoft pushed a fix that resolved a credential prompt failure when attempting remote desktop or remote application connections. On January 26, Microsoft patched a zero-day security feature bypass vulnerability (CVE-2026-21509) in Microsoft Office.
Kev Breen at Immersive notes that this month’s Patch Tuesday includes several fixes for remote code execution vulnerabilities affecting GitHub Copilot and multiple integrated development environments (IDEs), including VS Code, Visual Studio, and JetBrains products. The relevant CVEs are CVE-2026-21516, CVE-2026-21523, and CVE-2026-21256.
Breen said the AI vulnerabilities Microsoft patched this month stem from a command injection flaw that can be triggered through prompt injection, or tricking the AI agent into doing something it shouldn’t — like executing malicious code or commands.
“Developers are high-value targets for threat actors, as they often have access to sensitive data such as API keys and secrets that function as keys to critical infrastructure, including privileged AWS or Azure API keys,” Breen said. “When organizations enable developers and automation pipelines to use LLMs and agentic AI, a malicious prompt can have significant impact. This does not mean organizations should stop using AI. It does mean developers should understand the risks, teams should clearly identify which systems and workflows have access to AI agents, and least-privilege principles should be applied to limit the blast radius if developer secrets are compromised.”
The SANS Internet Storm Center has a clickable breakdown of each individual fix this month from Microsoft, indexed by severity and CVSS score. Enterprise Windows admins involved in testing patches before rolling them out should keep an eye on askwoody.com, which often has the skinny on wonky updates. Please don’t neglect to back up your data if it has been a while since you’ve done that, and feel free to sound off in the comments if you experience problems installing any of these fixes.
SmarterTools Hit by Ransomware via Vulnerability in Its Own Product
SmarterTools says customers were impacted after hackers compromised a data center used for quality control testing.
The post SmarterTools Hit by Ransomware via Vulnerability in Its Own Product appeared first on SecurityWeek.
Critical SmarterMail Vulnerability Exploited in Ransomware Attacks
The security defect allows unauthenticated attackers to execute arbitrary code remotely via malicious HTTP requests.
The post Critical SmarterMail Vulnerability Exploited in Ransomware Attacks appeared first on SecurityWeek.
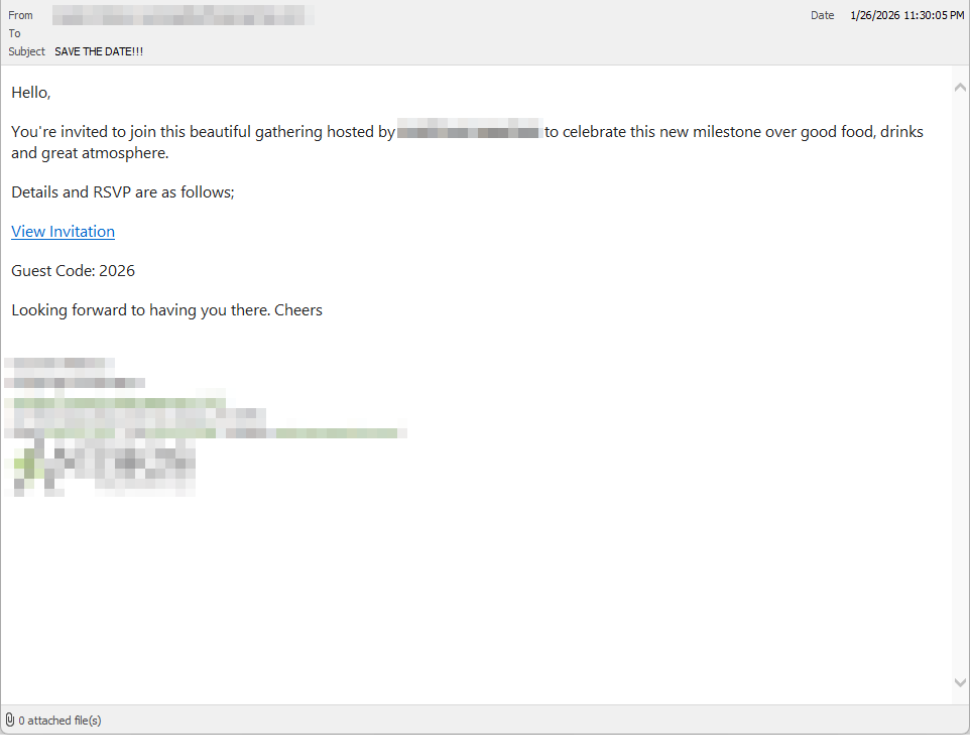
How fake party invitations are being used to install remote access tools
“You’re invited!”
It sounds friendly, familiar and quite harmless. But in a scam we recently spotted, that simple phrase is being used to trick victims into installing a full remote access tool on their Windows computers—giving attackers complete control of the system.
What appears to be a casual party or event invitation leads to the silent installation of ScreenConnect, a legitimate remote support tool quietly installed in the background and abused by attackers.
Here’s how the scam works, why it’s effective, and how to protect yourself.
The email: A party invitation
Victims receive an email framed as a personal invitation—often written to look like it came from a friend or acquaintance. The message is deliberately informal and social, lowering suspicion and encouraging quick action.
In the screenshot below, the email arrived from a friend whose email account had been hacked, but it could just as easily come from a sender you don’t know.
So far, we’ve only seen this campaign targeting people in the UK, but there’s nothing stopping it from expanding elsewhere.
Clicking the link in the email leads to a polished invitation page hosted on an attacker-controlled domain.

The invite: The landing page that leads to an installer
The landing page leans heavily into the party theme, but instead of showing event details, the page nudges the user toward opening a file. None of them look dangerous on their own, but together they keep the user focused on the “invitation” file:
- A bold “You’re Invited!” headline
- The suggestion that a friend had sent the invitation
- A message saying the invitation is best viewed on a Windows laptop or desktop
- A countdown suggesting your invitation is already “downloading”
- A message implying urgency and social proof (“I opened mine and it was so easy!”)
Within seconds, the browser is redirected to download RSVPPartyInvitationCard.msi
The page even triggers the download automatically to keep the victim moving forward without stopping to think.
This MSI file isn’t an invitation. It’s an installer.

The guest: What the MSI actually does
When the user opens the MSI file, it launches msiexec.exe and silently installs ScreenConnect Client, a legitimate remote access tool often used by IT support teams.
There’s no invitation, RSVP form, or calendar entry.
What happens instead:
- ScreenConnect binaries are installed under
C:\Program Files (x86)\ScreenConnect Client\ - A persistent Windows service is created (for example, ScreenConnect Client 18d1648b87bb3023)
- ScreenConnect installs multiple .NET-based components
- There is no clear user-facing indication that a remote access tool is being installed
From the victim’s perspective, very little seems to happen. But at this point, the attacker can now remotely access their computer.
The after-party: Remote access is established
Once installed, the ScreenConnect client initiates encrypted outbound connections to ScreenConnect’s relay servers, including a uniquely assigned instance domain.
That connection gives the attacker the same level of access as a remote IT technician, including the ability to:
- See the victim’s screen in real time
- Control the mouse and keyboard
- Upload or download files
- Keep access even after the computer is restarted
Because ScreenConnect is legitimate software commonly used for remote support, its presence isn’t always obvious. On a personal computer, the first signs are often behavioral, such as unexplained cursor movement, windows opening on their own, or a ScreenConnect process the user doesn’t remember installing.
Why this scam works
This campaign is effective because it targets normal, predictable human behavior. From a behavioral security standpoint, it exploits our natural curiosity and appears to be a low risk.
Most people don’t think of invitations as dangerous. Opening one feels passive, like glancing at a flyer or checking a message, not installing software.
Even security-aware users are trained to watch out for warnings and pressure. A friendly “you’re invited” message doesn’t trigger those alarms.
By the time something feels off, the software is already installed.
Signs your computer may be affected
Watch for:
- A download or executed file named
RSVPPartyInvitationCard.msi - An unexpected installation of ScreenConnect Client
- A Windows service named ScreenConnect Client with random characters
- Your computer makes outbound HTTPS connections to ScreenConnect relay domains
- Your system resolves the invitation-hosting domain used in this campaign, xnyr[.]digital
How to stay safe
This campaign is a reminder that modern attacks often don’t break in—they’re invited in. Remote access tools give attackers deep control over a system. Acting quickly can limit the damage.
For individuals
If you receive an email like this:
- Be suspicious of invitations that ask you to download or open software
- Never run MSI files from unsolicited emails
- Verify invitations through another channel before opening anything
If you already clicked or ran the file:
- Disconnect from the internet immediately
- Check for ScreenConnect and uninstall it if present
- Run a full security scan
- Change important passwords from a clean, unaffected device
For organisations (especially in the UK)
- Alert on unauthorized ScreenConnect installations
- Restrict MSI execution where feasible
- Treat “remote support tools” as high-risk software
- Educate users: invitations don’t come as installers
This scam works by installing a legitimate remote access tool without clear user intent. That’s exactly the gap Malwarebytes is designed to catch.
Malwarebytes now detects newly installed remote access tools and alerts you when one appears on your system. You’re then given a choice: confirm that the tool is expected and trusted, or remove it if it isn’t.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
How fake party invitations are being used to install remote access tools
“You’re invited!”
It sounds friendly, familiar and quite harmless. But in a scam we recently spotted, that simple phrase is being used to trick victims into installing a full remote access tool on their Windows computers—giving attackers complete control of the system.
What appears to be a casual party or event invitation leads to the silent installation of ScreenConnect, a legitimate remote support tool quietly installed in the background and abused by attackers.
Here’s how the scam works, why it’s effective, and how to protect yourself.
The email: A party invitation
Victims receive an email framed as a personal invitation—often written to look like it came from a friend or acquaintance. The message is deliberately informal and social, lowering suspicion and encouraging quick action.
In the screenshot below, the email arrived from a friend whose email account had been hacked, but it could just as easily come from a sender you don’t know.
So far, we’ve only seen this campaign targeting people in the UK, but there’s nothing stopping it from expanding elsewhere.
Clicking the link in the email leads to a polished invitation page hosted on an attacker-controlled domain.

The invite: The landing page that leads to an installer
The landing page leans heavily into the party theme, but instead of showing event details, the page nudges the user toward opening a file. None of them look dangerous on their own, but together they keep the user focused on the “invitation” file:
- A bold “You’re Invited!” headline
- The suggestion that a friend had sent the invitation
- A message saying the invitation is best viewed on a Windows laptop or desktop
- A countdown suggesting your invitation is already “downloading”
- A message implying urgency and social proof (“I opened mine and it was so easy!”)
Within seconds, the browser is redirected to download RSVPPartyInvitationCard.msi
The page even triggers the download automatically to keep the victim moving forward without stopping to think.
This MSI file isn’t an invitation. It’s an installer.

The guest: What the MSI actually does
When the user opens the MSI file, it launches msiexec.exe and silently installs ScreenConnect Client, a legitimate remote access tool often used by IT support teams.
There’s no invitation, RSVP form, or calendar entry.
What happens instead:
- ScreenConnect binaries are installed under
C:\Program Files (x86)\ScreenConnect Client\ - A persistent Windows service is created (for example, ScreenConnect Client 18d1648b87bb3023)
- ScreenConnect installs multiple .NET-based components
- There is no clear user-facing indication that a remote access tool is being installed
From the victim’s perspective, very little seems to happen. But at this point, the attacker can now remotely access their computer.
The after-party: Remote access is established
Once installed, the ScreenConnect client initiates encrypted outbound connections to ScreenConnect’s relay servers, including a uniquely assigned instance domain.
That connection gives the attacker the same level of access as a remote IT technician, including the ability to:
- See the victim’s screen in real time
- Control the mouse and keyboard
- Upload or download files
- Keep access even after the computer is restarted
Because ScreenConnect is legitimate software commonly used for remote support, its presence isn’t always obvious. On a personal computer, the first signs are often behavioral, such as unexplained cursor movement, windows opening on their own, or a ScreenConnect process the user doesn’t remember installing.
Why this scam works
This campaign is effective because it targets normal, predictable human behavior. From a behavioral security standpoint, it exploits our natural curiosity and appears to be a low risk.
Most people don’t think of invitations as dangerous. Opening one feels passive, like glancing at a flyer or checking a message, not installing software.
Even security-aware users are trained to watch out for warnings and pressure. A friendly “you’re invited” message doesn’t trigger those alarms.
By the time something feels off, the software is already installed.
Signs your computer may be affected
Watch for:
- A download or executed file named
RSVPPartyInvitationCard.msi - An unexpected installation of ScreenConnect Client
- A Windows service named ScreenConnect Client with random characters
- Your computer makes outbound HTTPS connections to ScreenConnect relay domains
- Your system resolves the invitation-hosting domain used in this campaign, xnyr[.]digital
How to stay safe
This campaign is a reminder that modern attacks often don’t break in—they’re invited in. Remote access tools give attackers deep control over a system. Acting quickly can limit the damage.
For individuals
If you receive an email like this:
- Be suspicious of invitations that ask you to download or open software
- Never run MSI files from unsolicited emails
- Verify invitations through another channel before opening anything
If you already clicked or ran the file:
- Disconnect from the internet immediately
- Check for ScreenConnect and uninstall it if present
- Run a full security scan
- Change important passwords from a clean, unaffected device
For organisations (especially in the UK)
- Alert on unauthorized ScreenConnect installations
- Restrict MSI execution where feasible
- Treat “remote support tools” as high-risk software
- Educate users: invitations don’t come as installers
This scam works by installing a legitimate remote access tool without clear user intent. That’s exactly the gap Malwarebytes is designed to catch.
Malwarebytes now detects newly installed remote access tools and alerts you when one appears on your system. You’re then given a choice: confirm that the tool is expected and trusted, or remove it if it isn’t.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
Deceptive-Auditing: An Active Directory Honeypots Tool
![]()
Deceptive-Auditing is a tool that deploys Active Directory honeypots and automatically enables auditing for those honeypots.
The post Deceptive-Auditing: An Active Directory Honeypots Tool appeared first on Black Hills Information Security, Inc..
A Beginner’s Guide to the CVE Database
Keeping websites and applications secure starts with knowing which vulnerabilities exist, how severe they are, and whether they affect your stack. That’s exactly where the CVE program shines. Below, we’ll cover some CVE fundamentals, including what they are, how to search and understand the data, and how to translate this information into actionable steps.
Introduction to the CVE database
So, what is CVE?
CVE stands for Common Vulnerabilities and Exposures, a community-driven program that assigns unique identifiers to publicly known vulnerabilities.
Continue reading A Beginner’s Guide to the CVE Database at Sucuri Blog.
GoSpoof – Turning Attacks into Intel
![]()
Imagine this: You’re an attacker ready to get their hands on valuable data that you can sell to afford going on a sweet vacation. You do your research, your recon, everything, ensuring that there’s no way this can go wrong. The day of the attack, you brew some coffee, crack your knuckles, and get started. A few hours into the service scan, you come to realize that all the network ports are open, but in use.
The post GoSpoof – Turning Attacks into Intel appeared first on Black Hills Information Security, Inc..
-
Black Hills Information Security, Inc.
- Wrangling Windows Event Logs with Hayabusa & SOF-ELK (Part 2)
Wrangling Windows Event Logs with Hayabusa & SOF-ELK (Part 2)
![]()
But what if we need to wrangle Windows Event Logs for more than one system? In part 2, we’ll wrangle EVTX logs at scale by incorporating Hayabusa and SOF-ELK into my rapid endpoint investigation workflow (“REIW”)!
The post Wrangling Windows Event Logs with Hayabusa & SOF-ELK (Part 2) appeared first on Black Hills Information Security, Inc..
DomCat: A Domain Categorization Tool
![]()
DomCat is a command-line tool written in Golang that helps the user find expired domains with desirable categorizations.
The post DomCat: A Domain Categorization Tool appeared first on Black Hills Information Security, Inc..
Stop Spoofing Yourself! Disabling M365 Direct Send
![]()
Remember the good ‘ol days of Zip drives, Winamp, the advent of “Office 365,” and copy machines that didn’t understand email authentication? Okay, maybe they weren’t so good! For a […]
The post Stop Spoofing Yourself! Disabling M365 Direct Send appeared first on Black Hills Information Security, Inc..
-
Black Hills Information Security, Inc.
- Offensive Tooling Cheatsheets: An Infosec Survival Guide Resource
Offensive Tooling Cheatsheets: An Infosec Survival Guide Resource
![]()
An Infosec Survival Guide Resource, released as blog posts, with fully designed, printer-friendly PDF cheatsheets.
The post Offensive Tooling Cheatsheets: An Infosec Survival Guide Resource appeared first on Black Hills Information Security, Inc..
DNS Triage Cheatsheet
![]()
DNS Triage is a reconnaissance tool that finds information about an organization's infrastructure, software, and third-party services as fast as possible. The goal of DNS Triage is not to exhaustively find every technology asset that exists on the internet. The goal is to find the most commonly abused items of interest for real attackers.
The post DNS Triage Cheatsheet appeared first on Black Hills Information Security, Inc..
GraphRunner Cheatsheet
![]()
GraphRunner is a collection of post-exploitation PowerShell modules for interacting with the Microsoft Graph API. It provides modules for enumeration, exfiltration, persistence, and more!
The post GraphRunner Cheatsheet appeared first on Black Hills Information Security, Inc..
Burp Suite Cheatsheet
![]()
Burp Suite is an intercepting HTTP proxy that can also scan a web-based service for vulnerabilities. A tool like this is indispensable for testing web applications. Burp Suite is written in Java and comes bundled with a JVM, so it works on any operating system you're likely to use.
The post Burp Suite Cheatsheet appeared first on Black Hills Information Security, Inc..
Impacket Cheatsheet
![]()
Impacket is an extremely useful tool for post exploitation. It is a collection of Python scripts that provides low-level programmatic access to the packets and for some protocols, such as DCOM, Kerberos, SMB1, and MSRPC, the protocol implementation itself.
The post Impacket Cheatsheet appeared first on Black Hills Information Security, Inc..
Wireshark Cheatsheet
![]()
Wireshark is an incredible tool used to read and analyze network traffic coming in and out of an endpoint. Additionally, it can load previously captured traffic to assist with troubleshooting network issues or analyze malicious traffic to help determine what a threat actor is doing on your network.
The post Wireshark Cheatsheet appeared first on Black Hills Information Security, Inc..
Hashcat Cheatsheet
![]()
Hashcat is a powerful tool for recovering lost passwords, and, thanks to GPU acceleration, it’s one of the fastest. It works by rapidly trying different password guesses to determine the original password from its scrambled (hashed) version.
The post Hashcat Cheatsheet appeared first on Black Hills Information Security, Inc..
EyeWitness Cheatsheet
![]()
Offensive Purpose: Efficient way to gather info about web services & their hosting infrastructure. Automates taking screenshots for quick & easy review.
The post EyeWitness Cheatsheet appeared first on Black Hills Information Security, Inc..