Dutch police sell fake tickets to show how easily scams work
If you can’t beat them, copy them. That seems to be the thinking behind an unusual campaign by the Dutch police, who set up a fake ticket website selling tickets that don’t exist.
The website, TicketBewust.nl, invites people to order tickets for events like football matches and concerns. But the offers were never real. The entire site was a deliberate sting, designed to show people how easily ticket fraud works.
The Netherlands’ National Police created the site to warn people about ticket fraud. They worked with the Fraud Helpdesk and online marketplace Marktplaats to run ads promoting “exclusive tickets” for sold-out concerts. If anyone got far enough to try and buy a ticket, the fake site took them to a police webpage explaining that they’d just interacted with a fake online shop.
People fell for these too-good-to-be-true deals—and that’s the most interesting part of this story. Many of us assume we’re far too savvy to fall prey to such online shenanigans, but a surprisingly large number of people do.
More than 300,000 people saw the police ads on Marktplaats between October 30, 2025, and January 11, 2026. Over 30,000 people opened opened it to take a look. 7,402 of them clicked the link to the fake site that was in the ad, and 3,432 people tried to order tickets.
That’s a reminder that online crime works a lot like regular ecommerce. Whether you’re selling real tickets or fake ones, it’s just a numbers game. Only a small percentage of people who see an ad will ever convert—but even a tiny fraction can be lucrative.
In this case, around 1% of people that saw the ad took the bait, but that represents a big profit for scammers. Fake ticket sellers raked in an average of $672 per victim in the US between 2020 and 2024, according to data from the Better Business Bureau (BBB).
Why ticket fraud is so common
Dutch police get around 50,000 online fraud complaints annually, with 10% involving fake tickets. It’s a problem in other countries too, with UK losses to gig ticket scams doubling in 2024 to £1.6 million (around $2.1 million).
Part of the reason fake ticket scams are so effective is that many cases never get reported. Some victims don’t think the loss is significant enough, while others simply don’t want to admit they were tricked. But there’s another, more fundamental reason these scams work so well: the audience is already primed to buy.
People searching for tickets are usually doing so because they don’t want to miss out. Scammers lean hard into that fear of missing out (FOMO), pairing it with scarcity cues like “sold out,” “limited availability,” or time-limited offers. People under emotional pressure from urgency and scarcity tend to do irrational things and take risks they shouldn’t. It’s why people invest erratically or take gambles on dodgy online sales.
How to protect yourself from fake ticket sites
The advice for avoiding shady ticket sellers looks a lot like advice for avoiding scams in general:
- Watch what you click on social media. Social media accounts for 52% of concert ticket fraud cases, according to the BBB data. Stick to official channels like Ticketmaster, AXS, or the venue’s box office—and double check the URL you’re accessing.
- Don’t let emotions get the better of you. Ticket sellers target high-demand events because they know people are desperate to attend and might let their guard down. That’s why fake ticket scams spiked after Oasis announced their reunion tour.
- Don’t be fooled by support lines. Just because they’re on the phone doesn’t mean they’re legit.
- Never pay via Zelle, Venmo, Cash App, gift cards or crypto. Use credit cards or other payment methods that offer purchase protection.
A little skepticism can go a long way when looking for sought-after tickets. So if you see an online ad offering you the seats of a lifetime, take a minute to research the seller. It could save you hundreds of dollars and a heap of disappointment.
We don’t just report on scams—we help detect them
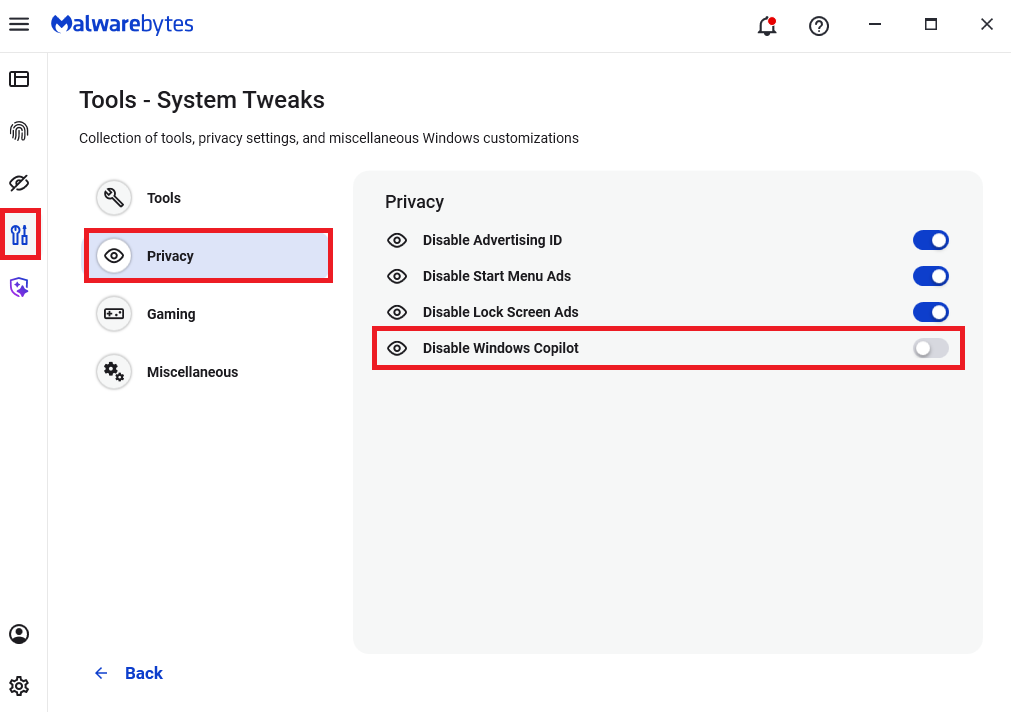
Cybersecurity risks should never spread beyond a headline. If something looks dodgy to you, check if it’s a scam using Malwarebytes Scam Guard, a feature of our mobile protection products. Submit a screenshot, paste suspicious content, or share a text or phone number, and we’ll tell you if it’s a scam or legit. Download Malwarebytes Mobile Security for iOS or Android and try it today!