Normal view
Intimate products producer Tenga spilled customer data
Tenga confirmed reports published by several outlets that the company notified customers of a data breach.
The Japanese manufacturer of adult products appears to have fallen victim to a phishing attack targeting one of its employees. Tenga reportedly wrote in the data breach notification:
“An unauthorized party gained access to the professional email account of one of our employees.”
This unauthorized access exposed the contents of said account’s inbox, potentially including customer names, email addresses, past correspondence, order details, and customer service inquiries.
In its official statement, Tenga said a “limited segment” of US customers who interacted with the company were impacted by the incident. Regarding the scope of the stolen data, it stated:
“The information involved was limited to customer email addresses and related correspondence history. No sensitive personal data, such as Social Security numbers, billing/credit card information, or TENGA/iroha Store passwords were jeopardized in this incident.”
From the wording of Tenga’s online statement, it seems the compromised account was used to send spam emails that included an attachment.
“Attachment Safety: We want to state clearly that there is no risk to your device or data if the suspicious attachment was not opened. The risk was limited to the potential execution of the attachment within the specific ‘spam’ window (February 12, 2026, between 12am and 1am PT).”
See if your personal data has been exposed.
We reached out to Tenga about this “suspicious attachment” but have not heard back at the time of writing. We’ll keep you posted.
Tenga proactively contacted potentially affected customers. It advises them to change passwords and remain vigilant about any unusual activity. We would add that affected customers should be on the lookout for sextortion-themed phishing attempts.
What to do if your data was in a breach
If you think you have been affected by a data breach, here are steps you can take to protect yourself:
- Check the company’s advice. Every breach is different, so check with the company to find out what’s happened and follow any specific advice it offers.
- Change your password. You can make a stolen password useless to thieves by changing it. Choose a strong password that you don’t use for anything else. Better yet, let a password manager choose one for you.
- Enable two-factor authentication (2FA). If you can, use a FIDO2-compliant hardware key, laptop, or phone as your second factor. Some forms of 2FA can be phished just as easily as a password, but 2FA that relies on a FIDO2 device can’t be phished.
- Watch out for impersonators. The thieves may contact you posing as the breached platform. Check the official website to see if it’s contacting victims and verify the identity of anyone who contacts you using a different communication channel.
- Take your time. Phishing attacks often impersonate people or brands you know, and use themes that require urgent attention, such as missed deliveries, account suspensions, and security alerts.
- Consider not storing your card details. It’s definitely more convenient to let sites remember your card details, but it increases risk if a retailer suffers a breach.
- Set up identity monitoring, which alerts you if your personal information is found being traded illegally online and helps you recover after.
- Use our free Digital Footprint scan to see whether your personal information has been exposed online.
What do cybercriminals know about you?
Use Malwarebytes’ free Digital Footprint scan to see whether your personal information has been exposed online.
Meta patents AI that could keep you posting from beyond the grave
Tech bros have been wanting to become immortal for years. Until they get there, their fallback might be continuing to post nonsense on social media from the afterlife.
On December 30, 2025, Meta was granted US patent 12513102B2: Simulation of a user of a social networking system using a language model. It describes a system that trains an AI on a user’s posts, comments, chats, voice messages, and likes, then deploys a bot to respond to newsfeeds, DMs, and even simulated audio or video calls.
Filed in November 2023 by Meta CTO Andrew Bosworth, it sounds innocuous enough. Perhaps some people would use it to post their political hot takes while they’re asleep.
Dig deeper, though, and the patent veers from absurd to creepy. It’s designed to be used not just from beyond the pillow but beyond the grave.
From the patent:
“The language model may be used for simulating the user when the user is absent from the social networking system, for example, when the user takes a long break or if the user is deceased.”
A Meta spokesperson told Business Insider that the company has no plans to act on the patent. And tech companies have a habit of laying claim to bizarre ideas that never materialize. But Facebook’s user numbers have stalled, and it presumably needs all the engagement it can get. We already know that the company loves the idea of AI ‘users’, having reportedly piloted them in late 2024, much to human users’ annoyance.
If the company ever did decide to pull the trigger on this technology, it would be a departure from its own memorialization policy, which preserves accounts without changes. One reason the company might not be willing to step over the line is that the world simply isn’t ready for AI conversations with the dead. Other companies have considered and even tested similar systems. Microsoft patented a chatbot that would allow you to talk to AI versions of deceased individuals in 2020; its own AI general manager called it disturbing, and it never went into production. Amazon demonstrated Alexa mimicking a dead grandmother’s voice from under a minute of audio in 2022, framing it as preserving memories. That never launched either.
Some projects that did ship left people wishing they hadn’t. Startup 2Wai’s avatar app originally offered the chance to preserve loved ones as AI avatars. Users called it “nightmare fuel” and “demonic”. The company seems to have pivoted to safer ground like social avatars and personal AI coaches now.
The legal minefield
The other thing holding Meta back could be the legal questions. Unsurprisingly for such a new idea, there isn’t a uniform US framework on the use of AI to represent the dead. Several states recognize post-mortem right of publicity, although states like New York limit that to people whose voices and images have commercial value (typically meaning celebrities). California’s AB 1836 specifically targets AI-generated impersonations of the deceased, though.
Meta would also need to tiptoe carefully around the law in Europe. The company had to pause AI training on European users in 2024 under regulatory pressure, but then launched it anyway in March last year. Then it refused to sign the EU’s GPAI Code of Practice last July (the only major AI firm to do so). Meta’s relationship with EU regulators is strained at best.
Europe’s General Data Protection Regulation (GDPR) excludes deceased persons’ data, but Article 85 of the French Data Protection law lets anyone leave instructions about the retention, deletion and communication of their personal data after death. The EU AI Act’s Article 50 (fully applicable this August) will also require AI systems to disclose they are AI, with penalties up to €15 million or 3% of worldwide turnover for companies that don’t comply.
Hopefully Meta really will file this in the “just because we can do it doesn’t mean we should” drawer, and leave erstwhile social media sharers to rest in peace.
We don’t just report on threats – we help protect your social media
Cybersecurity risks should never spread beyond a headline. Protect your social media accounts by using Malwarebytes Identity Theft Protection.
Arkanix Stealer: a C++ & Python infostealer
![]()
Introduction
In October 2025, we discovered a series of forum posts advertising a previously unknown stealer, dubbed “Arkanix Stealer” by its authors. It operated under a MaaS (malware-as-a-service) model, providing users not only with the implant but also with access to a control panel featuring configurable payloads and statistics. The set of implants included a publicly available browser post-exploitation tool known as ChromElevator, which was delivered by a native C++ version of the stealer. This version featured a wide range of capabilities, from collecting system information to stealing cryptocurrency wallet data. Alongside that, we have also discovered Python implementation of the stealer capable of dynamically modifying its configuration. The Python version was often packed, thus giving the adversary multiple methods for distributing their malware. It is also worth noting that Arkanix was rather a one-shot malicious campaign: at the time of writing this article, the affiliate program appears to be already taken down.
Kaspersky products detect this threat as Trojan-PSW.Win64.Coins.*, HEUR:Trojan-PSW.Multi.Disco.gen, Trojan.Python.Agent.*.
Technical details
Background
In October 2025, a series of posts was discovered on various dark web forums, advertising a stealer referred to by its author as “Arkanix Stealer”. These posts detail the features of the stealer and include a link to a Discord server, which serves as the primary communication channel between the author and the users of the stealer.
Upon further research utilizing public resources, we identified a set of implants associated with this stealer.
Initial infection or spreading
The initial infection vector remains unknown. However, based on some of the file names (such as steam_account_checker_pro_v1.py, discord_nitro_checker.py, and TikTokAccountBotter.exe) of the loader scripts we obtained, it can be concluded with high confidence that the initial infection vector involved phishing.
Python loader
| MD5 | 208fa7e01f72a50334f3d7607f6b82bf |
| File name | discord_nitro_code_validator_right_aligned.py |
The Python loader is the script responsible for downloading and executing the Python-based version of the Arkanix infostealer. We have observed both plaintext Python scripts and those bundled using PyInstaller or Nuitka, all of which share a common execution vector and are slightly obfuscated. These scripts often serve as decoys, initially appearing to contain legitimate code. Some of them do have useful functionality, and others do nothing apart from loading the stealer. Additionally, we have encountered samples that employ no obfuscation at all, in which the infostealer is launched in a separate thread via Python’s built-in threading module.
Upon execution, the loader first installs the required packages — namely, requests, pycryptodome, and psutil — via the pip package manager, utilizing the subprocess module. On Microsoft Windows systems, the loader also installs pywin32. In some of the analyzed samples, this process is carried out twice. Since the loader does not perform any output validation of the module installation command, it proceeds to make a POST request to hxxps://arkanix[.]pw/api/session/create to register the current compromised machine on the panel with a predefined set of parameters even if the installation failed. After that, the stealer makes a GET request to hxxps://arkanix[.]pw/stealer.py and executes the downloaded payload.
Python stealer version
| MD5 | af8fd03c1ec81811acf16d4182f3b5e1 |
| File name | – |
During our research, we obtained a sample of the Python implementation of the Arkanix stealer, which was downloaded from the endpoint hxxps://arkanix[.]pw/stealer.py by the previous stage.
The stealer’s capabilities — or features, as referred to by the author — in this version are configurable, with the default configuration predefined within the script file. To dynamically update the feature list, the stealer makes a GET request to hxxps://arkanix[.]pw/api/features/{payload_id}, indicating that these capabilities can be modified on the panel side. The feature list is identical to the one that was described in the GDATA report.
Prior to executing the information retrieval-related functions, the stealer makes a request to hxxps://arkanix[.]pw/upload_dropper.py, saves the response to %TEMP%\upd_{random 8-byte name}.py, and executes it. We do not have access to the contents of this script, which is referred to as the “dropper” by the attackers.
During its main information retrieval routine, at the end of each processing stage, the collected information is serialized into JSON format and saved to a predefined path, such as %LOCALAPPDATA\Arkanix_lol\%info_class%.json.
In the following, we will provide a more detailed description of the Python version’s data collection features.
System info collection
Arkanix Stealer is capable of collecting a set of info about the compromised system. This info includes:
- OS version
- CPU and GPU info
- RAM size
- Screen resolution
- Keyboard layout
- Time zone
- Installed software
- Antivirus software
- VPN
Information collection is performed using standard shell commands with the exception of the VPN check. The latter is implemented by querying the endpoint hxxps://ipapi[.]co/json/ and verifying whether the associated IP address belongs to a known set of VPNs, proxies, or Tor exit nodes.
Browser features
This stealer is capable of extracting various types of data from supported browsers (22 in total, ranging from the widely popular Google Chrome to the Tor Browser). The list of supported browsers is hardcoded, and unlike other parameters, it cannot be modified during execution. In addition to a separate Chrome grabber module (which we’ll discuss later), the stealer itself supports the extraction of diverse information, such as:
- Browser history (URLs, visit count and last visit)
- Autofill information (email, phone, addresses and payment cards details)
- Saved passwords
- Cookies
- In case of Chromium-based browsers, 0Auth2 data is also extracted
All information is decrypted using either the Windows DPAPI or AES, where applicable, and searched for relevant keywords. In the case of browser information collection, the stealer searches exclusively for keywords related to banking (e.g., “revolut”, “stripe”, “bank”) and cryptocurrencies (e.g., “binance”, “metamask”, “wallet”). In addition to this, the stealer is capable of extracting extension data from a hardcoded list of extensions associated with cryptocurrencies.
Telegram info collection
Telegram data collection begins with terminating the Telegram.exe process using the taskkill command. Subsequently, if the telegram_optimized feature is set to False, the malware zips the entire tdata directory (typically located at %APPDATA%\Roaming\Telegram Desktop\tdata) and transmits it to the attacker. Otherwise, it selectively copies and zips only the subdirectories containing valuable info, such as message log. The generated archive is sent to the endpoint /delivery with the filename tdata_session.zip.
Discord capabilities
The stealer includes two features connected with Discord: credentials stealing and self-spreading. The first one can be utilized to acquire credentials both from the standard client and custom clients. If the client is Chromium-based, the stealer employs the same data exfiltration mechanism as during browser credentials stealing.
The self-spreading feature is configurable (meaning it can be disabled in the config). The stealer acquires the list of user’s friends and channels via the Discord API and sends a message provided by the attacker. This stealer does not support attaching files to such messages.
VPN data collection
The VPN collector is searching for a set of known VPN software to extract account credentials from the credentials file with a known path that gets parsed with a regular expression. The extraction occurs from the following set of applications:
- Mullvad VPN
- NordVPN
- ExpressVPN
- ProtonVPN
File retrieval
File retrieval is performed regardless of the configuration. The script relies on a predefined set of paths associated with the current user (such as Desktop, Download, etc.) and file extensions mainly connected with documents and media. The script also has a predefined list of filenames to exfiltrate. The extracted files are packed into a ZIP archive which is later sent to the C2 asynchronously. An interesting aspect is that the filename list includes several French words, such as “motdepasse” (French for “password”), “banque” (French for “bank”), “secret” (French for “secret”), and “compte” (French for “account”).
Other payloads
We were able to identify additional modules that are downloaded from the C2 rather than embedded into the stealer script; however, we weren’t able to obtain them. These modules can be described by the following table, with the “Details” column referring to the information that could be extracted from the main stealer code.
| Module name | Endpoint to download | Details |
| Chrome grabber | /api/chrome-grabber-template/{payload_id} | – |
| Wallet patcher | /api/wallet-patcher/{payload_id} | Checks whether “Exodus” and “Atomic” cryptocurrency wallets are installed |
| Extra collector | /api/extra-collector/{payload_id} | Uses a set of options from the config, such as collect_filezilla, collect_vpn_data, collect_steam, and collect_screenshots |
| HVNC | /hvnc | Is saved to the Startup directory (%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\hvnc.py) to execute upon system boot |
The Wallet patcher and Extra collector scripts are received in an encrypted form from the C2 server. To decrypt them, the attackers utilize the AES-GCM algorithm in conjunction with PBKDF2 (HMAC and SHA256). After decryption, the additional payload has its template placeholders replaced and is stored under a partially randomized name within a temporary folder.
Once all operations are completed, the stealer removes itself from the drive, along with the artifacts folder (Arkanix_lol in this case).
Native version of stealer
| MD5 | a3fc46332dcd0a95e336f6927bae8bb7 |
| File name | ArkanixStealer.exe |
During our analysis, we were able to obtain both the release and debug versions of the native implementation, as both were uploaded to publicly available resources. The following are the key differences between the two:
- The release version employs VMProtect, but does not utilize code virtualization.
- The debug version communicates with a Discord bot for command and control (C2), whereas the release version uses the previously mentioned C2 domain
arkanix[.]pw. - The debug version includes extensive logging, presumably for the authors’ debugging purposes.
Notably, the native implementation explicitly references the name of the stealer in the VersionInfo resources. This naming convention is consistent across both the debug version and certain samples containing the release version of the implant.
After launching, the stealer implements a series of analysis countermeasures to verify that the application is not being executed within a sandboxed environment or run under a debugger. Following these checks, the sample patches AmsiScanBuffer and EtwEventWrite to prevent the triggering of any unwanted events by the system.
Once the preliminary checks are completed, the sample proceeds to gather information about the system. The list of capabilities is hardcoded and cannot be modified from the server side, in contrast to the Python version. What is more, the feature list is quite similar to the Python version except a few ones.
RDP connections
The stealer is capable of collecting information about known RDP connections that the compromised user has. To achieve this, it searches for .rdp files in %USERPROFILE%\Documents and extracts the full server address, password, username and server port.
Gaming files
The stealer also targets gamers and is capable to steal credentials from the popular gaming platform clients, including:
- Steam
- Epic Games Launcher
- net
- Riot
- Origin
- Unreal Engine
- Ubisoft Connect
- GOG
Screenshots
The native version, unlike its Python counterpart, is capable of capturing screenshots for each monitor via capCreateCaptureWindowA WinAPI.
In conclusion, this sample communicates with the C2 server through the same endpoints as the Python version. However, in this instance, all data is encrypted using the same AES-GCM + PBKDF2 (HMAC and SHA256) scheme as partially employed in the Python variant. In some observed samples, the key used was arkanix_secret_key_v20_2024. Alongside that, the C++ sample explicitly sets the User-Agent to ArkanixStealer/1.0.
Post-exploitation browser data extractor
| MD5 | 3283f8c54a3ddf0bc0d4111cc1f950c0 |
| File name | – |
This is an implant embedded within the resources of the C++ implementation. The author incorporated it into the resource section without applying any obfuscation or encryption. Subsequently, the stealer extracts the payload to a temporary folder with a randomly generated name composed of hexadecimal digits (0-9 and A-F) and executes it using the CreateProcess WinAPI. The payload itself is the unaltered publicly available project known as “ChromElevator”. To summarize, this tool consists of two components: an injector and the main payload. The injector initializes a direct syscall engine, spawns a suspended target browser process, and injects the decrypted code into it via Nt syscalls. The injected payload then decrypts the browser master key and exfiltrates data such as cookies, login information, web data, and so on.
Infrastructure
During the Arkanix campaign, two domains used in the attacks were identified. Although these domains were routed through Cloudflare, a real IP address was successfully discovered for one of them, namely, arkanix[.]pw. For the second one we only obtained a Cloudflare IP address.
| Domain | IP | First seen | ASN |
| arkanix[.]pw | 195.246.231[.]60 | Oct 09, 2025 | – |
| arkanix[.]ru | 172.67.186[.]193 | Oct 19, 2025 | – |
Both servers were also utilized to host the stealer panel, which allows attackers to monitor their victims. The contents of the panel are secured behind a sign-in page. Closer to the end of our research, the panel was seemingly taken down with no message or notice.
Stealer promotion
During the research of this campaign, we noticed that the forum posts advertising the stealer contained a link leading to a Discord server dubbed “Arkanix” by the authors. The server posed as a forum where authors posted various content and clients could ask various questions regarding this malicious software. While users mainly thank and ask about when the feature promised by the authors will be released and added into the stealer, the content made by the authors is broader. The adversary builds up the communication with potential buyers using the same marketing and communication methods real companies employ. To begin with, they warm up the audience by posting surveys about whether they should implement specific features, such as Discord injection and binding with a legitimate application (sic!).
Additionally, the author promised to release a crypter as a side project in four to six weeks, at the end of October. As of now, the stealer seems to have been taken down without any notice while the crypter was never released.
Furthermore, the Arkanix Stealer authors decided to implement a referral program to attract new customers. Referrers were promised an additional free hour to their premium license, while invited customers received seven days of free “premium” trial use. As stated in forum posts, the premium plan included the following features:
- C++ native stealer
- Exodus and Atomic cryptocurrency wallets injection
- Increased payload generation, up to 10 payloads
- Priority support
Speaking of technical details, based on the screenshot of the Visual Studio stealer project that was sent to the Discord server, we can conclude that the author is German-speaking.
This same screenshot also serves as a probable indicator of AI-assisted development as it shares the common patterns of such assistants, e.g. the presence of the utils.cpp file. What provides even more confidence is the overall code structure, the presence of comments and extensive debugging log output.
Conclusions
Information stealers have always posed as a serious threat to users’ data. Arkanix is no exception as it targets a wide range of users, from those interested in cryptocurrencies and gaming to those using online banking. It collects a vast amount of information including highly sensitive personal data. While being quite functional, it contains probable traces of LLM-assisted development which suggests that such assistance might have drastically reduced development time and costs. Hence it follows that this campaign tends to be more of a one-shot campaign for quick financial gains rather than a long-running infection. The panel and the Discord chat were taken down around December 2025, leaving no message or traces of further development or a resurgence.
In addition, the developers behind the Arkanix Stealer decided to address the public, implementing a forum where they posted development insights, conducted surveys and even ran a referral program where you could get bonuses for “bringing a friend”. This behavior makes Arkanix more of a public software product than a shady stealer.
Indicators of Compromise
Additional IoCs are available to customers of our Threat Intelligence Reporting service. For more details, contact us at crimewareintel@kaspersky.com.
File hashes
752e3eb5a9c295ee285205fb39b67fc4
c1e4be64f80bc019651f84ef852dfa6c
a8eeda4ae7db3357ed2ee0d94b963eff
c0c04df98b7d1ca9e8c08dd1ffbdd16b
88487ab7a666081721e1dd1999fb9fb2
d42ba771541893eb047a0e835bd4f84e
5f71b83ca752cb128b67dbb1832205a4
208fa7e01f72a50334f3d7607f6b82bf
e27edcdeb44522a9036f5e4cd23f1f0c
ea50282fa1269836a7e87eddb10f95f7
643696a052ea1963e24cfb0531169477
f5765930205719c2ac9d2e26c3b03d8d
576de7a075637122f47d02d4288e3dd6
7888eb4f51413d9382e2b992b667d9f5
3283f8c54a3ddf0bc0d4111cc1f950c0
Domains and IPs
arkanix[.]pw
arkanix[.]ru




Betterment data breach might be worse than we thought
Betterment LLC is an investment advisor registered with US Securities and Exchange Commission (SEC). The company disclosed a January 2026 incident in which an attacker used social engineering to access a third‑party platform used for customer communications, then abused it to send crypto‑themed phishing messages and exfiltrate contact and identity data for more than a million people.
What makes this particularly concerning is the depth of the exposed information. This isn’t just a list of email addresses. The leaked files include retirement plan details, financial interests, internal meeting notes, and pipeline data. It’s information that gives cybercriminals real context about a person’s finances and professional life.
What’s worse is that ransomware group Shiny Hunters claims that, since Betterment refused to pay their demanded ransom, it is publishing the stolen data.

While Betterment has not revealed the number of affected customers in its online communications, general consensus indicates that the data of 1.4 million customers was involved. And now, every cybercriminal can download this information at their leisure.
We analyzed some of the data and found one particularly worrying CSV file with detailed data on 181,487 people. This file included information such as:
- Full names (first and last)
- Personal email addresses (e.g., Gmail)
- Work email addresses
- Company name and employer info
- Job titles and roles
- Phone numbers (both mobile and work numbers)
- Addresses and company websites
- Plan details—company retirement/401k plans, assets, participants
- Survey responses, deal and client pipeline details, meeting notes
- Financial needs/interests (e.g., requesting a securities-backed line of credit for a house purchase)
See if your personal data has been exposed.
This kind of data is a gold mine for phishers, who can use it in targeted attacks. It has enough context to craft convincing, individually tailored phishing emails. For example:
- Addressing someone by their real name, company, and job title
- Referencing the company’s retirement or financial plans
- Impersonating Betterment advisors or plan administrators
- Initiating scam calls about financial advice
Combined with data from other breaches it could even be worse and lead to identity theft.
What to do if your data was in a breach
If you think you have been affected by a data breach, here are steps you can take to protect yourself:
- Check the company’s advice. Every breach is different, so check with the company to find out what’s happened and follow any specific advice it offers.
- Change your password. You can make a stolen password useless to thieves by changing it. Choose a strong password that you don’t use for anything else. Better yet, let a password manager choose one for you.
- Enable two-factor authentication (2FA). If you can, use a FIDO2-compliant hardware key, laptop, or phone as your second factor. Some forms of 2FA can be phished just as easily as a password, but 2FA that relies on a FIDO2 device can’t be phished.
- Watch out for impersonators. The thieves may contact you posing as the breached platform. Check the official website to see if it’s contacting victims and verify the identity of anyone who contacts you using a different communication channel.
- Take your time. Phishing attacks often impersonate people or brands you know, and use themes that require urgent attention, such as missed deliveries, account suspensions, and security alerts.
- Consider not storing your card details. It’s definitely more convenient to let sites remember your card details, but it increases risk if a retailer suffers a breach.
- Set up identity monitoring, which alerts you if your personal information is found being traded illegally online and helps you recover after.
Use Malwarebytes’ free Digital Footprint scan to see whether your personal information has been exposed online.
We don’t just report on threats—we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your, and your family’s, personal information by using identity protection.
A milestone achievement in our journey to carbon negative
The post A milestone achievement in our journey to carbon negative appeared first on Microsoft On the Issues.
Cyber Risk Is a Board Responsibility and Training Is the Missing Link
-
Fortinet All Blogs
- Voice of the Customer at Accelerate: Practical Lessons from Real-World Security and Networking Leaders
Voice of the Customer at Accelerate: Practical Lessons from Real-World Security and Networking Leaders
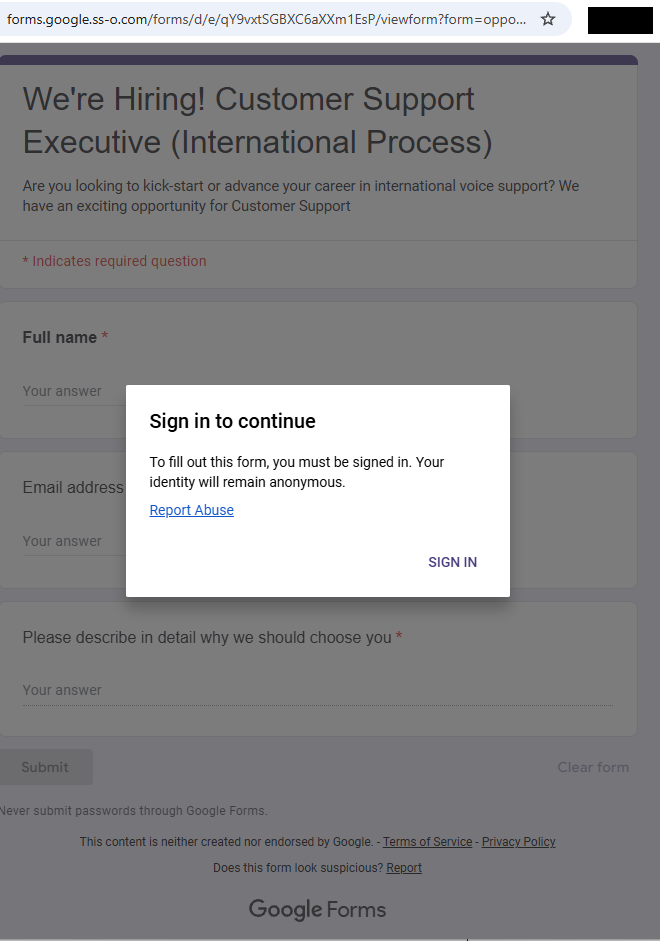
Job scam uses fake Google Forms site to harvest Google logins
As part of our investigation into a job-themed phishing campaign, we came across several suspicious URLs that all looked like this:
https://forms.google.ss-o[.]com/forms/d/e/{unique_id}/viewform?form=opportunitysec&promo=
The subdomain forms.google.ss-o[.]com is a clear attempt to impersonate the legitimate forms.google.com. The “ss-o” is likely introduced to look like “single sign-on,” an authentication method that allows users to securely log in to multiple, independent applications or websites using one single set of credentials (username and password).
Unfortunately, when we tried to visit the URLs we were redirected to the local Google search website. This is a common phisher’s tactic to prevent victims from sharing their personalized links with researchers or online analysis.
After some digging, we found a file called generation_form.php on the same domain, which we believe the phishing crew used to create these links. The landing page for the campaign was: https://forms.google.ss-o[.]com/generation_form.php?form=opportunitysec
The generation_form.php script does what the name implies: It creates a personalized URL for the person clicking that link.
With that knowledge in hand, we could check what the phish was all about. Our personalized link brought us to this website:

The greyed out “form” behind the prompt promises:
- We’re Hiring! Customer Support Executive (International Process)
- Are you looking to kick-start or advance your career…
- The fields in the form: Full Name, Email address, and an essay field “Please describe in detail why we should choose you”
- Buttons: “Submit” and “Clear form.”
The whole web page emulates Google Forms, including logo images, color schemes, a notice about not “submitting passwords,” and legal links. At the bottom, it even includes the typical Google Forms disclaimer (“This content is neither created nor endorsed by Google.”) for authenticity.
Clicking the “Sign in” button took us to https://id-v4[.]com/generation.php, which has now been taken down. The domain id-v4.com has been used in several phishing campaigns for almost a year. In this case, it asked for Google account credentials.
Given the “job opportunity” angle, we suspect links were distributed through targeted emails or LinkedIn messages.
How to stay safe
Lures that promise remote job opportunities are very common these days. Here are a few pointers to help keep you safe from targeted attacks like this:
- Do not click on links in unsolicited job offers.
- Use a password manager, which would not have filled in your Google username and password on a fake website.
- Use an up to date, real-time anti-malware solution with a web protection component.
Pro tip: Malwarebytes Scam Guard identified this attack as a scam just by looking at the URL.
IOCs
id-v4[.]com
forms.google.ss-o[.]com

We don’t just report on scams—we help detect them
Cybersecurity risks should never spread beyond a headline. If something looks dodgy to you, check if it’s a scam using Malwarebytes Scam Guard. Submit a screenshot, paste suspicious content, or share a link, text or phone number, and we’ll tell you if it’s a scam or legit. Available with Malwarebytes Premium Security for all your devices, and in the Malwarebytes app for iOS and Android.
Two Types of Threat Intelligence That Make Security Work
The problem isn’t that we lack threat intelligence. It’s that we lack the right kind of intelligence, intelligence that connects what’s happening inside your environment with what attackers are planning outside it. That’s why two types of threat intelligence matter: internal and external. Alone, each tells part of the story. Together, they create clarity. Why Threat Intelligence Alone Falls Short Most organizations subscribe to multiple threat feeds. They pour in from every direction, generic, fragmented, and often delayed. Instead of clarifying risk, they confuse it. “Organizations still make critical decisions based on incomplete or underrefined threat data.” — Gartner, The […]
The post Two Types of Threat Intelligence That Make Security Work appeared first on Check Point Blog.
Carelessness versus craftsmanship in cryptography
Two popular AES libraries, aes-js and pyaes, “helpfully” provide a default IV in their AES-CTR API, leading to a large number of key/IV reuse bugs. These bugs potentially affect thousands of downstream projects. When we shared one of these bugs with an affected vendor, strongSwan, the maintainer provided a model response for security vendors. The aes-js/pyaes maintainer, on the other hand, has taken a more… cavalier approach.
Trail of Bits doesn’t usually make a point of publicly calling out specific products as unsafe. Our motto is that we don’t just fix bugs—we fix software. We do better by the world when we work to address systemic threats, not individual bugs. That’s why we work to provide static analysis tools, auditing tools, and documentation for folks looking to implement cryptographic software. When you improve systems, you improve software.
But sometimes, a single bug in a piece of software has an outsized impact on the cryptography ecosystem, and we need to address it.
This is the story of how two developers reacted to a security problem, and how their responses illustrate the difference between carelessness and craftsmanship.
Reusing initialization vectors
Reusing a key/IV pair leads to serious security issues: if you encrypt two messages in CTR mode or GCM with the same key and IV, then anybody with access to the ciphertexts can recover the XOR of the plaintexts, and that’s a very bad thing. Like, “your security is going to get absolutely wrecked” bad. One of our cryptography analysts has written an excellent introduction to the topic, in case you’d like more details; it’s great reading.
Even if the XOR of the plaintexts doesn’t help an attacker, it still makes the encryption very brittle: if you’re encrypting all your secrets by XORing them against a fixed mask, then recovering just one of those secrets will reveal the mask. Once you have that, you can recover all the other secrets. Maybe all your secrets will remain secure against prying eyes, but the fact remains: in the very best case, the security of all your secrets becomes no better than the security of your weakest secret.
aes-js and pyaes
As you might guess from the names, aes-js and pyaes are JavaScript and Python libraries that implement the AES block cipher. They’re pretty widely used: the Node.js package manager (npm) repository lists 850 aes-js dependents as of this writing, and GitHub estimates that over 700,000 repositories integrate aes-js and nearly 23,000 repositories integrate pyaes, either as direct or indirect dependencies.
Unfortunately, despite their widespread adoption, aes-js and pyaes suffer from a careless mistake that creates serious security problems.
The default IV problem
We’ll start with the biggest concern Trail of Bits identified: when instantiating AES in CTR mode, aes-js and pyaes do not require an IV. Instead, if no IV is specified, libraries will supply a default IV of 0x00000000_00000000_00000000_00000001.
Worse still, the documentation provides examples of this behavior as typical behavior. For example, this comes from the pyaes README:
aes = pyaes.AESModeOfOperationCTR(key)
plaintext = "Text may be any length you wish, no padding is required"
ciphertext = aes.encrypt(plaintext)The first line ought to be something like aes = pyaes.AESModeOfOperationCTR(key, iv), where iv is a randomly generated value. Users who follow this example will always wind up with the same IV, making it inevitable that many (if not most) will wind up with a key/IV reuse bug in their software. Most people are looking for an easy-to-use encryption library, and what’s simpler than just passing in the key?
That apparent simplicity has led to widespread use of the “default,” creating a multitude of key/IV reuse vulnerabilities.
Other issues
Lack of modern cipher modes
aes-js and pyaes don’t support modern cipher modes like AES-GCM and AES-GCM-SIV. In most contexts where you want to use AES, you likely want to use these modes, as they offer authentication in addition to encryption. This is no small issue: even for programs that use aes-js or pyaes with distinct key/IV pairs, AES CTR ciphertexts are still malleable: if an attacker changes the bits in the ciphertext, then the resulting bits in the plaintext will change in exactly the same way, and CTR mode doesn’t provide any way to detect this. This can allow an attacker to recover an ECDSA key by tricking the user into signing messages with a series of related keys.
Cipher modes like GCM and GCM-SIV prevent this by computing keyed “tags” that will fail to authenticate when the ciphertext is modified, even by a single bit. Pretty nifty feature, but support is completely absent from aes-js and pyaes.
Timing problems
On top of that, both aes-js and pyaes are vulnerable to side-channel attacks. Both libraries use lookup tables for the AES S-box, which enables cache-timing attacks. On top of that, there are timing issues in the PKCS7 implementation, enabling a padding oracle attack when used in CBC mode.
Lack of updates
aes-js hasn’t been updated since 2018. pyaes hasn’t been touched since 2017. Since then, a number of issues have been filed against both libraries. Here are just a few examples:
- Outdated distribution tools for pyaes (it relies on
distutils, which has been deprecated since October 2023) - Performance issues in the streaming API
- UTF-8 encoding problems in aes-js
- Lack of IV and key generation routines in both
Developer response
Finally, in 2022, an issue was filed against aes-js about the default IV problem. The developer’s response ended with the following:
The AES block cipher is a cryptographic primitive, so it’s very important to understand and use it properly, based on its application. It’s a powerful tool, and with great power, yadda, yadda, yadda. :)
Look, even at the best of times, cryptography is a minefield: a space full of hidden dangers, where one wrong step can blow things up entirely. When designing tools for others, developers have a responsibility to help their users avoid foreseeable mistakes—or at the very least, to avoid making it more likely that they’ll step on such landmines. Writing off a serious concern like this with “yadda, yadda, yadda” is deeply concerning.
In November 2025, we reached out to the maintainer via email and via X, but we received no response.
The original design decision to include a default IV was a mistake, but an understandable one for somebody trying to make their library accessible to as many people as possible. And mistakes happen, especially in cryptography. The problem is what came next. When a user raised the concern, it was written off with ‘yadda, yadda, yadda.’ The landmine wasn’t removed. The documentation still suggests the best way to step on it. This is what carelessness looks like: not the initial mistake, but the choice to leave it unfixed when its danger became clear.
Craftsmanship
We identified several pieces of software impacted by the default IV behavior in pyaes and aes-js. Many of the programs we found have been deprecated, and we even found a couple of vulnerable wallets for cryptocurrencies that are no longer traded. We also picked out a large number of programs where the security impact of key/IV reuse was minimal or overshadowed by larger security concerns (for instance, there were a few programs that reused key/IV pairs, but the key was derived from a 4-digit PIN).
However, one of the programs we found struck us as important: a VPN management suite.
strongMan VPN Manager
strongMan is a web-based management tool for folks using the strongSwan VPN suite. It allows for credential and user management, initiation of VPN connections, and more. It’s a pretty slick piece of software; if you’re into IPsec VPNs, you should definitely give it a look.
strongMan stored PKCS#8-encoded keys in a SQLite database, encrypted with AES. As you’ve probably guessed, it used pyaes to encrypt them in CTR mode, relying on the default IV. In PKCS#8 key files, RSA private keys include both the decryption exponent and the factors of the public modulus. For the same modulus size, the factors of the modulus will “line up” to start at the same place in the private key encodings about 99.6% of the time. For a pair of 2048-bit moduli, we can use the XOR of the factors to recover the factors in a matter of seconds.
Even worse, the full X.509 certificates were also encrypted using the same key/IV pair used to encrypt the private keys. Since certificates include a huge amount of predictable or easily guessable data, it’s easy to recover the keystream from the known X.509 data, and then use the recovered keystream to decrypt the private keys without resorting to any fancy XORed-factors mathematical trickery.
In short, if a hacker could recover a strongMan user’s SQLite file, they could immediately impersonate anyone whose certificates are stored in the database and even mount person-in-the-middle attacks. Obviously, this is not a great outcome.
We privately reported this issue to the strongSwan team. Tobias Brunner, the strongMan maintainer, provided an absolute model response to a security issue of this severity. He immediately created a security-fix branch and collaborated with Trail of Bits to develop stronger protection for his users. This patch has since been rolled out, and the update includes migration tools to help users update their old databases to the new format.
Doing it right
There were several viable approaches to fixing this issue. Adding a unique IV for each encrypted entry in the database would have allowed strongMan to keep using pyaes, and would have addressed the immediate issue. But if the code has to be changed, it may as well be updated to something modern.
After some discussion, several changes were made to the application:
- pyaes was replaced with a library that supports modern cipher modes.
- CTR mode was replaced with GCM-SIV, a cipher mode that includes authentication tags.
- Tag-checking was integrated into the decryption routines.
- A per-entry key derivation scheme is now used to ensure that key/IV pairs don’t repeat.
On top of all that, there are now migration scripts to allow strongMan users to seamlessly update their databases.
There will be a security advisory for strongMan issued in conjunction with this fix, outlining the nature of the problem, its severity, and the measures taken to address it. Everything will be out in the open, with full transparency for all strongMan users.
What Tobias did in this case has a name: craftsmanship. He sweated the details, thought extensively about his decisions, and moved with careful deliberation.
A difference in approaches
Mistakes in cryptography are not a sin, even if they can have a serious impact. They’re simply a fact of life. As somebody once said, “cryptography is nightmare magic math that cares what color pen you use.” We’re all going to get stuff wrong if we stick around long enough to do something interesting, and there’s no reason to deride somebody for making a mistake.
What matters—what separates carelessness from craftsmanship—is the response to a mistake. A careless developer will write off a mistake as no big deal or insist that it isn’t really a problem—yadda, yadda, yadda. A craftsman will respond by fixing what’s broken, examining their tools and processes, and doing what they can to prevent it from happening again.
In the end, only you can choose which way you go. Hopefully, you’ll choose craftsmanship.
Scammers use fake “Gemini” AI chatbot to sell fake “Google Coin”
Scammers have found a new use for AI: creating custom chatbots posing as real AI assistants to pressure victims into buying worthless cryptocurrencies.
We recently came across a live “Google Coin” presale site featuring a chatbot that claimed to be Google’s Gemini AI assistant. The bot guided visitors through a polished sales pitch, answered their questions about investment, projecting returns, and ultimately ended with victims sending an irreversible crypto payment to the scammers.
Google does not have a cryptocurrency. But as “Google Coin” has appeared before in scams, anyone checking it out might think it’s real. And the chatbot was very convincing.

AI as the closer
The chatbot introduced itself as,
“Gemini — your AI assistant for the Google Coin platform.”
It used Gemini-style branding, including the sparkle icon and a green “Online” status indicator, creating the immediate impression that it was an official Google product.
When asked, “Will I get rich if I buy 100 coins?”, the bot responded with specific financial projections. A $395 investment at the current presale price would be worth $2,755 at listing, it claimed, representing “approximately 7x” growth. It cited a presale price of $3.95 per token, an expected listing price of $27.55, and invited further questions about “how to participate.”
This is the kind of personalized, responsive engagement that used to require a human scammer on the other end of a Telegram chat. Now the AI does it automatically.

A persona that never breaks
What stood out during our analysis was how tightly controlled the bot’s persona was. We found that it:
- Claimed consistently to be “the official helper for the Google Coin platform”
- Refused to provide any verifiable company details, such as a registered entity, regulator, license number, audit firm, or official email address
- Dismissed concerns and redirected them to vague claims about “transparency” and “security”
- Refused to acknowledge any scenario in which the project could be a scam
- Redirected tougher questions to an unnamed “manager” (likely a human closer waiting in the wings)
When pressed, the bot doesn’t get confused or break character. It loops back to the same scripted claims: a “detailed 2026 roadmap,” “military-grade encryption,” “AI integration,” and a “growing community of investors.”
Whoever built this chatbot locked it into a sales script designed to build trust, overcome doubt, and move visitors toward one outcome: sending cryptocurrency.

Why AI chatbots change the scam model
Scammers have always relied on social engineering. Build trust. Create urgency. Overcome skepticism. Close the deal.
Traditionally, that required human operators, which limited how many victims could be engaged at once. AI chatbots remove that bottleneck entirely.
A single scam operation can now deploy a chatbot that:
- Engages hundreds of visitors simultaneously, 24 hours a day
- Delivers consistent, polished messaging that sounds authoritative
- Impersonates a trusted brand’s AI assistant (in this case, Google’s Gemini)
- Responds to individual questions with tailored financial projections
- Escalates to human operators only when necessary
This matches a broader trend identified by researchers. According to Chainalysis, roughly 60% of all funds flowing into crypto scam wallets were tied to scammers using AI tools. AI-powered scam infrastructure is becoming the norm, not the exception. The chatbot is just one piece of a broader AI-assisted fraud toolkit—but it may be the most effective piece, because it creates the illusion of a real, interactive relationship between the victim and the “brand.”
The bait: a polished fake
The chatbot sits on top of a convincing scam operation. The Google Coin website mimics Google’s visual identity with a clean, professional design, complete with the “G” logo, navigation menus, and a presale dashboard. It claims to be in “Stage 5 of 5” with over 9.9 million tokens sold and a listing date of February 18—all manufactured urgency.
To borrow credibility, the site displays logos of major companies—OpenAI, Google, Binance, Squarespace, Coinbase, and SpaceX—under a “Trusted By Industry” banner. None of these companies have any connection to the project.
If a visitor clicks “Buy,” they’re taken to a wallet dashboard that looks like a legitimate crypto platform, showing balances for “Google” (on a fictional “Google-Chain”), Bitcoin, and Ethereum.
The purchase flow lets users buy any number of tokens they want and generates a corresponding Bitcoin payment request to a specific wallet address. The site also layers on a tiered bonus system that kicks in at 100 tokens and scales up to 100,000: buy more and the bonuses climb from 5% up to 30% at the top tier. It’s a classic upsell tactic designed to make you think it’s smarter to spend more.
Every payment is irreversible. There is no exchange listing, no token with real value, and no way to get your money back.

What to watch for
We’re entering an era where the first point of contact in a scam may not be a human at all. AI chatbots give scammers something they’ve never had before: a tireless, consistent, scalable front-end that can engage victims in what feels like a real conversation. When that chatbot is dressed up as a trusted brand’s official AI assistant, the effect is even more convincing.
According to the FTC’s Consumer Sentinel data, US consumers reported losing $5.7 billion to investment scams in 2024 (more than any other type of fraud, and up 24% on the previous year). Cryptocurrency remains the second-largest payment method scammers use to extract funds, because transactions are fast and irreversible. Now add AI that can pitch, persuade, and handle objections without a human operator—and you have a scalable fraud model.
AI chatbots on scam sites will become more common. Here’s how to spot them:
They impersonate known AI brands. A chatbot calling itself “Gemini,” “ChatGPT,” or “Copilot” on a third-party crypto site is almost certainly not what it claims to be. Anyone can name a chatbot anything.
They won’t answer due diligence questions. Ask what legal entity operates the platform, what financial regulator oversees it, or where the company is registered. Legitimate operations can answer those questions, scam bots try to avoid them (and if they do answer, verify it).
They project specific returns. No legitimate investment product promises a specific future price. A chatbot telling you that your $395 will become $2,755 is not giving you financial information—it’s running a script.
They create urgency. Pressure tactics like, “stage 5 ends soon,” “listing date approaching,” “limited presale” are designed to push you into making fast decisions.
How to protect yourself
Google does not have a cryptocurrency. It has not launched a presale. And its Gemini AI is not operating as a sales assistant on third-party crypto sites. If you encounter anything suggesting otherwise, close the tab.
- Verify claim on the official website of the company being referenced.
- Don’t rely on a chatbot’s branding. Anyone can name a bot anything.
- Never send cryptocurrency based on projected returns.
- Search the project name along with “scam” or “review” before sending any money.
- Use web protection tools like Malwarebytes Browser Guard, which is free to use and blocks known and unknown scam sites.
If you’ve already sent funds, report it to your local law enforcement, the FTC at reportfraud.ftc.gov, and the FBI’s IC3 at ic3.gov.
IOCs
0xEc7a42609D5CC9aF7a3dBa66823C5f9E5764d6DA
98388xymWKS6EgYSC9baFuQkCpE8rYsnScV4L5Vu8jt
DHyDmJdr9hjDUH5kcNjeyfzonyeBt19g6G
TWqzJ9sF1w9aWwMevq4b15KkJgAFTfH5im
bc1qw0yfcp8pevzvwp2zrz4pu3vuygnwvl6mstlnh6
r9BHQMUdSgM8iFKXaGiZ3hhXz5SyLDxupY
We don’t just report on scams—we help detect them
Cybersecurity risks should never spread beyond a headline. If something looks dodgy to you, check if it’s a scam using Malwarebytes Scam Guard. Submit a screenshot, paste suspicious content, or share a link, text or phone number, and we’ll tell you if it’s a scam or legit. Available with Malwarebytes Premium Security for all your devices, and in the Malwarebytes app for iOS and Android.
-
CrowdStrike Blog
- Introducing "AI Unlocked: Decoding Prompt Injection," a New Interactive Challenge
Introducing "AI Unlocked: Decoding Prompt Injection," a New Interactive Challenge
Exposing Insider Threats through Data Protection, Identity, and HR Context
GrayCharlie Hijacks Law Firm Sites in Suspected Supply-Chain Attack
Executive Summary
Insikt Group has been monitoring GrayCharlie, a threat actor overlapping with SmartApeSG and active since mid-2023, for some time, and is now publishing its first report on the group. GrayCharlie compromises WordPress sites and injects them with links to externally hosted JavaScript that redirects visitors to NetSupport RAT payloads delivered via fake browser update pages or ClickFix mechanisms. These infections often progress to the deployment of Stealc and SectopRAT. Insikt Group identified a large amount of infrastructure linked to GrayCharlie, primarily tied to MivoCloud and HZ Hosting Ltd. This includes NetSupport RAT command-and-control (C2) servers, both actor-controlled and compromised staging infrastructure, and higher-tier infrastructure used to administer operations. While most compromised websites appear to be opportunistic and span numerous industries, Insikt Group identified a cluster of United States (US) law firm sites that were likely compromised around November 2025, possibly through a supply-chain compromise involving a shared IT provider.
To protect against GrayCharlie, security defenders should block IP addresses and domains tied to associated remote access trojans (RATs) and infostealers, flag and potentially block connections to compromised websites, and deploy updated detection rules (YARA, Snort, Sigma) for current and historical infections. Other controls include implementing email filtering and data exfiltration monitoring. See the Mitigations section of this report for implementation guidance and Appendix A for a complete list of indicators of compromise (IoCs).
Key Findings
- GrayCharlie, which overlaps with SmartApeSG and first emerged in mid-2023, is a threat actor that injects links to externally hosted JavaScript into compromised WordPress sites. These links redirect victims to NetSupport RAT infections delivered via fake browser update pages or ClickFix techniques, ultimately resulting in Stealc and SectopRAT infections.
- Insikt Group identified a wide range of GrayCharlie infrastructure, largely associated with MivoCloud and HZ Hosting Ltd. This includes NetSupport RAT command-and-control (C2) servers, staging infrastructure made up of both actor-controlled and compromised infrastructure, as well as components of GrayCharlie’s higher-tier infrastructure used to manage its operations.
- Insikt Group identified two primary attack chains associated with GrayCharlie: one in which victims encounter fake browser update pages after visiting compromised websites, and another in which they are presented with a ClickFix pop-up, a technique that has become increasingly common in 2025.
Background
GrayCharlie is Insikt Group’s designation for a threat activity group that first appeared in mid-2023 and is behind SmartApeSG, also referred to as ZPHP or HANEYMANEY. The group’s operations typically involve injecting malicious JavaScript into legitimate but compromised WordPress sites. Visitors to these sites are shown convincing, browser-specific fake update prompts (such as for Chrome, Edge, or Firefox) that encourage them to download what appears to be an update but is actually malware.
In late March or early April 2025, SmartApeSG shifted from using fake browser updates to deploying ClickFix lures, mirroring a broader trend among threat actors of increasingly adopting ClickFix.
GrayCharlie predominantly delivers NetSupport RAT; however, deployments of Stealc and, more recently, SectopRAT, have been observed in rare instances. The group’s ultimate objectives remain uncertain. Current evidence suggests a focus on data theft and financial gain, with a theoretical, but unsubstantiated, possibility that it may sell or transfer access to other threat actors.
Threat Analysis
Insikt Group has been tracking GrayCharlie for an extended period and has observed the actor’s persistent behavior since its emergence in 2023. GrayCharlie continues to conduct the same types of operations, regularly deploying large volumes of new infrastructure and adhering to consistent tactics, techniques, and procedures (TTPs), including continued use of the same infection chains and NetSupport RAT payloads. The group targets organizations worldwide, with a particular focus on the US. The following sections provide a detailed examination of GrayCharlie’s operational infrastructure and its two primary attack chains.
Infrastructure Analysis
NetSupport RAT Clusters
Insikt Group identified two main NetSupport RAT clusters linked to GrayCharlie based on factors such as TLS certificates, NetSupport serial numbers and license keys, and the timing of the activity (see Figure 1). In addition, Insikt Group identified a range of other NetSupport RAT C2 servers linked to GrayCharlie activity, but which are not currently attributed to either of the two main clusters. Insikt Group assesses that these clusters may correspond either to different individuals associated with GrayCharlie or to distinct GrayCharlie campaigns. The clusters are further described below.
Cluster 1
Cluster 1 comprises NetSupport RAT C2 servers whose TLS certificates display a recurring monthly naming pattern. All servers in this cluster are hosted by MivoCloud and were deployed between March and August 2025. Notably, NetSupport RAT samples associated with the cluster’s March and April infrastructure used the license key DCVTTTUUEEW23 and serial number NSM896597, before shifting to the license key EVALUSION and serial number NSM165348 in subsequent deployments. The C2 servers associated with this cluster are listed in Table 1.
Table 1: NetSupport RAT C2 servers linked to Cluster 1 (Source: Recorded Future)
Notably, the NetSupport RAT C2 servers in Cluster 1 are connected not only through the characteristics previously described, but also by the near-simultaneous creation of their TLS certificates. For example, the TLS certificate with the common name june5ebatquot associated with IP address 94[.]158[.]245[.]135 was generated on June 30, 2025 at 4:55:20 PM, while the certificate with the common name june6 linked to 94[.]158[.]245[.]174 was created only 20 seconds later.
Cluster 2
Cluster 2 comprises NetSupport RAT command-and-control servers whose TLS certificates typically start with two or more repetitions of “s”, followed by an “i” and a number (so “sssi3”, for example). NetSupport RAT samples linked to Cluster 2 used the license key XMLCTL and serial number NSM303008. The NetSupport RAT C2 servers typically also host an instance of the vulnerability scanner Acunetix. The C2 servers associated with this cluster are listed in Table 2. Notably, all TLS certificates associated with this cluster were created in a single batch on June 17, 2025.
Table 2: NetSupport RAT C2 servers linked to Cluster 2 (Source: Recorded Future)
Of note, one NetSupport RAT C2 server (94[.]158[.]245[.]56) used a TLS certificate with the common name 23sss, created in May 2025, and was linked to a NetSupport RAT sample that carried the same license key (EVALUSION) and serial number (NSM165348) previously observed in Cluster 1.
Other NetSupport RAT C2 Servers
Insikt Group identified an additional set of NetSupport RAT C2 servers linked to GrayCharlie that did not form a distinct cluster (see Table 3). However, all the servers were hosted by MivoCloud and were associated with NetSupport RAT samples using license key and serial number combinations observed in Clusters 1 and 2.
Table 3: Additional NetSupport RAT C2 servers linked to GrayBravo (Source: Recorded Future)
Staging Infrastructure
Once GrayCharlie victims land on the compromised WordPress sites, thereby satisfying the conditional logic, the payload is typically fetched from the attacker-controlled infrastructure and injected into the compromised WordPress sites. Insikt Group has identified two distinct types of staging infrastructure, each characterized by different website templates. Type 1 is modeled after “Wiser University,” and Type 2 is modeled after “Activitar.”
Type 1: “Wiser University”
The IP addresses associated with the Type 1 staging infrastructure are linked to websites impersonating “Wiser University” (see Figure 2), a fictional entity used to demonstrate Wiser, a free Bootstrap HTML5 education website template for school, college, and university websites. (As a sidenote, Oreshnik is the name of a Russian intermediate-range ballistic missile reportedly capable of speeds exceeding Mach 10.) Appendix B lists the IP addresses associated with the Type 1 staging infrastructure. All IP addresses, except for one, are announced by AS202015 (HZ Hosting Ltd).
Suspected Testing Infrastructure
Although most IP addresses associated with the Type 1 staging infrastructure are announced by AS202015, as shown in Appendix B, Insikt Group also identified a small subset announced by other ASNs that host the same websites (see Table 4). On average, approximately one such IP address appears to be established each month. Notably, most of these IP addresses appear to geolocate to Russia, and the same ASNs are consistently reused within the same timeframe.
Table 4: Additional infrastructure possibly linked to GrayCharlie (Source: Recorded Future)
Type 2: “Activitar”
Insikt Group identified an additional set of staging infrastructure, referred to as “Type 2.” The IP addresses in this cluster commonly host specific websites (see Figure 3). Insikt Group assesses that this template was sourced elsewhere and is not unique to GrayCharlie.
A subset of domains and IP addresses associated with Type 2 is presented in Table 5. Notably, most of the IP addresses are also announced by AS202015 (HZ Hosting Ltd), and one domain in Table 5, filmlerzltyazilimsx[.]shop, is linked to the email address oreshnik[@]mailum[.]com through its WHOIS record.
Table 5: Domains and IP addresses linked to Type 2 staging infrastructure (Source: Recorded Future)
Compromised Infrastructure
GrayCharlie commonly injects malicious scripts into the Document Object Model (DOM) of compromised WordPress sites using script tags. Insikt Group has identified several recurring URL patterns tied to this activity: some URLs load externally hosted JavaScript files (such as hxxps://joiner[.]best/work/original[.]js), while others call a PHP file on specific endpoints using an ID parameter (such as hxxps://signaturepl[.]com/work/index[.]php?abje2LAw). Notably, these URLs are updated over time by the threat actor, complicating detection and indicating the threat actor maintains ongoing access to a large pool of compromised WordPress installations. Appendix A lists a subset of WordPress websites infected by GrayCharlie.
Although the exact initial access vector is unknown, it is likely that the actors either purchase access, such as via malware logs containing WordPress admin credentials, or exploit vulnerable WordPress plugins. The latter remains the most frequent cause of all WordPress compromises.
Suspected Compromise of “Law Firm Acceleration Company” SMB Team
While the GrayCharlie-linked compromised WordPress sites span a wide range of industry verticals, in a few rare instances, the threat actors appear to have obtained, either through their own intrusions or via a third party, a more targeted set of WordPress domains. Specifically, at least fifteen websites belonging to US law firms were observed loading the external JavaScript hosted at hxxps://persistancejs[.]store/work/original[.]js (see Table 6).
Insikt Group assesses that GrayCharlie (or the third party GrayCharlie works with) likely compromised these websites through a supply-chain vector. One potential avenue is SMB Team, the self-described “fastest-growing law firm acceleration company,” which has supported thousands of firms across North America, according to its website, as its logo and other references appear across many of the websites listed in Table 6 (see Figure 4). Notably, credentials associated with an SMB Team email address used for a WordPress hosting platform surfaced around the same time that the domain persistancejs[.]store first began resolving. This temporal overlap suggests that the threat actors may have gained access to SMB Team-related infrastructure through the use of legitimate, compromised credentials.
Table 6: Compromised law firm websites linked to GrayCharlie (Source: Recorded Future)
![]()
![]()
Notably, while an SMB Team compromise is possible, Insikt Group also assesses that the actors may have exploited a specific version of WordPress or its plugins used by SMB Team, which could explain the simultaneous compromise of all affected websites.
In some instances, the same compromised WordPress sites are compromised by multiple threat actors simultaneously. For example, bianchilawgroup[.]com was also breached by TAG-124 (also known as LandUpdate808 or Kongtuke) since at least December 2025, which used the domain vimsltd[.]com.
Higher-Tier Analysis
GrayCharlie administers its staging infrastructure primarily over SSH, though other ports are used intermittently. The group manages its NetSupport RAT C2 servers over TCP port 443. Overall, Insikt Group assesses that GrayCharlie relies extensively on proxy services to administer its infrastructure. Additionally, based on presumed browsing activity from higher-tier servers, at least some individuals linked to GrayCharlie are assessed to be Russian-speaking.
Attack-Chain Analysis
GrayCharlie has been observed using two different attack chains to deliver NetSupport RAT. The first chain uses compromised websites to distribute a fake browser update that triggers the retrieval and installation of a script-based payload; the second chain uses compromised WordPress sites and a ClickFix-style lure that copies a command to fetch and install the RAT. Both culminate in NetSupport execution from %AppData%, Registry Run key persistence, and C2 connectivity; the technical details are expanded below.
Attack Chain 1: Fake Browser Update Leading to NetSupport RAT
According to public reporting, when GrayCharlie first became active in mid-2023, it relied on fake browser updates to deliver the NetSupport RAT. Although the group later shifted to the ClickFix technique, Insikt Group observed a return to fake browser updates as early as October 12, 2025. Figure 5 provides an overview of Attack Chain 1.
- Website compromise and lure delivery. Threat actors modify legitimate sites to load malicious scripts that render a browser-specific “update” prompt. Selecting the prompt initiates download of a ZIP “update” package containing a primary JavaScript file alongside decoy
.datfiles. - User-executed JavaScript loader. The victim manually runs the
.jsscript. The script mimics a benign browser component to reduce suspicion while silently initiating the next stage of the attack. - PowerShell staging via WScript. The JavaScript launches
wscript.exe, which spawnspowershell.exe. PowerShell reaches out to a remote host to fetch an obfuscated JavaScript containing encoded tasking. - Secondary payload retrieval. PowerShell decodes instructions and downloads the actual payload ZIP archive. This archive contains a complete NetSupport RAT client set, including
client32.exeand required DLLs. - File deployment and execution. The archive is extracted under the user profile (for example,
%AppData%\Roaming\...).client32.exeis started in the background to minimize visible indicators to the user. - Persistence establishment. A Windows Run registry key is created to automatically launch
client32.exeat logon, ensuring the NetSupport RAT remains active after reboots without requiring further user interaction. - C2 readiness. With the NetSupport RAT client running on the infected host, the endpoint is prepared to establish command-and-control connectivity with the attacker's infrastructure.
Attack Chain 2: WordPress Redirects and ClickFix Leading to NetSupport RAT
As early as April 2025, GrayCharlie began using ClickFix as a secondary attack chain, consistent with industry reporting that many threat actors have adopted ClickFix techniques due to their effectiveness. Figure 6 provides an overview of Attack Chain 2.
- Initial delivery and redirection. Phishing emails, malicious PDFs, or links on gaming sites direct users to compromised WordPress pages that embed attacker JavaScript.
- Background script and profiling. A background script loads when the site is visited, injects an iframe, and profiles the environment (such as the operating system and browser) to deliver the next stage.
- ClickFix fake CAPTCHA. The page presents a fake CAPTCHA that quietly copies a malicious command to the user’s clipboard and instructs them to paste it into the Windows Run dialog (Win+R), turning social engineering into user-assisted execution (see Figure 7).
- Command-driven staging. The pasted command retrieves a batch file that downloads a ZIP containing NetSupport RAT and uses PowerShell to extract it into
%AppData%\Roaming\(see Figure 8).
powershell -Win^dow Style Hidden -Command "Add-Type -AssemblyName 'System. IO.Compression FileSystem'; [IO.Compression.ZipFile]::ExtractToDirectory('!CF0JOAXML!','!WFHEYHKMZ!')"Figure 8: PowerShell command (Source: Cybereason)
- NetSupport RAT launch and persistence. The batch file starts
client32.exeand sets a Run registry key to automatically relaunch the NetSupport RAT client at startup, establishing persistence on the endpoint. - Remote access and follow-on actions. Once connected to C2, operators can interact with the system, perform reconnaissance (for example, domain group membership queries), transfer files, execute additional commands, and potentially move laterally using access acquired from the host.
Observed Operator Activity
In October 2025, Insikt Group detonated a NetSupport RAT sample (SHA256: 31804c48f9294c9fa7c165c89e487bfbebeda6daf3244ad30b93122bf933c79c) with the C2 server 5[.]181[.]156[.]234[:]443 linked to GrayCharlie within a controlled environment. Later that day, approximately three hours later, the threat actor connected using NetSupport RAT, compressed and moved two files, and then executed group and account reconnaissance commands. The same actor returned three days later and repeated the previously observed reconnaissance commands (see Figure 9).
net group /domain "Domain COmputers"
C:\Windows\system32\net1 group /domain "Domain COmputers"
Figure 9: Reconnaissance commands (Source: Recorded Future)
When both files were compressed into a single ZIP archive and the executable was detonated, the process sideloaded a DLL identified as Sectop RAT (SHA256: 59e7e7698d77531bfbfea4739d29c14e188b5d3109f63881b9bcc87c72e9de78) with the C2 server 85[.]158[.]110[.]179[:]15847. The executable (SHA256: 5f1bd92ad6edea67762c7101cb810dc28fd861f7b8c62e6459226b7ea54e1428) was identified as “Merge XML Files”, version 1.2.0.0, developed by Vovsoft, and was signed with a digital certificate that expired on October 31, 2025.
Mitigations
- Leverage the IoCs in Appendix A and Appendix B to investigate potential past or ongoing infections, both successful and attempted; Recorded Future customers can use the Recorded Future Intelligence Operations Platform to monitor for future IoCs associated with GrayCharlie.
- Monitor for validated infrastructure associated with the malware families discussed in this report, including NetSupport RAT and Stealc, as well as numerous others identified and validated by Insikt Group, and integrate these indicators into relevant detection and monitoring systems.
- Leverage the Sigma, YARA, and Snort rules provided in Appendices D, E, and F in your security information and event management (SIEM) or endpoint detection and response (EDR) tools to detect the presence or execution of NetSupport RAT. Customers can use additional detection rules available in the Recorded Future Intelligence Operations Platform.
- Use Recorded Future Network Intelligence to detect instances of data exfiltration from your corporate infrastructure to known malicious infrastructure.
- Use the Recorded Future Intelligence Operations Platform to monitor GrayCharlie, other threat actors, and the broader cybercriminal ecosystem, ensuring visibility into the latest tactics, techniques, and procedures (TTPs), preferred tools and services (for example, specific threat activity enablers [TAEs] used by threat actors), and emerging developments.
- Use Recorded Future AI’s reporting feature to generate tailored reports on topics that matter to your company. For example, if you want to stay informed about activities related to GrayCharlie, you can receive regular AI-generated updates on this threat actor.
Outlook
GrayCharlie has been operating for more than two years, and despite shifts in its tactics, such as alternating between fake updates and ClickFix techniques or transitioning from SmartApe to other hosting providers like MivoCloud, the group’s core behaviors have remained consistent. Given its sustained activity, GrayCharlie is highly likely to remain active and continue targeting organizations worldwide, with a current emphasis on US entities, as indicated by Recorded Future Network Intelligence.
Insikt Group will continue to closely monitor GrayCharlie to detect emerging threats and evaluate the group’s strategic direction within the broader cybercriminal ecosystem.
Appendix A: Indicators of Compromise
Cluster 1 NetSupport RAT C2 IP Addresses:
5[.]181[.]159[.]60
5[.]252[.]178[.]23
5[.]252[.]178[.]123
94[.]158[.]245[.]13
94[.]158[.]245[.]63
94[.]158[.]245[.]66
94[.]158[.]245[.]81
94[.]158[.]245[.]104
94[.]158[.]245[.]111
94[.]158[.]245[.]115
94[.]158[.]245[.]118
94[.]158[.]245[.]131
94[.]158[.]245[.]135
94[.]158[.]245[.]137
94[.]158[.]245[.]140
94[.]158[.]245[.]174
185[.]163[.]45[.]30
185[.]163[.]45[.]41
185[.]163[.]45[.]61
185[.]163[.]45[.]73
185[.]163[.]45[.]87
185[.]163[.]45[.]97
185[.]163[.]45[.]130
185[.]225[.]17[.]74
194[.]180[.]191[.]17
194[.]180[.]191[.]51
194[.]180[.]191[.]168
194[.]180[.]191[.]171
194[.]180[.]191[.]189
Cluster 2 NetSupport RAT C2 IP Addresses:
5[.]181[.]159[.]9
5[.]181[.]159[.]38
5[.]181[.]159[.]112
5[.]181[.]159[.]139
5[.]181[.]159[.]140
5[.]181[.]159[.]142
5[.]181[.]159[.]143
Other NetSupport RAT C2 Servers:
5[.]181[.]156[.]234
5[.]181[.]156[.]244
5[.]181[.]159[.]29
5[.]181[.]159[.]62
5[.]252[.]177[.]15
5[.]252[.]177[.]120
5[.]252[.]178[.]35
94[.]158[.]245[.]153
94[.]158[.]245[.]170
185[.]163[.]45[.]16
194[.]180[.]191[.]18
194[.]180[.]191[.]121
194[.]180[.]191[.]209
NetSupport RAT Hashes:
06a0a243811e9c4738a9d413597659ca8d07b00f640b74adc9cb351c179b3268
0e9df9294c36702eee970efcb4a70b6ddb433190ab661273e2e559185c55b6c1
112bf17e7c0d0695e9229d60f0d2734c6b96d7edfb41ea3e98e518f4fb1ae6e9
11370e108c8e7a53e52f01df0829c8addb5833145618a7701fbedbb1d837a43d
15dfe9d443027ba01b8f54f415fd74d373b3a06017db8ef110fb55b33357b190
16c8b5e10135d168d73a553a4bda51628e5b4fd419c0ecd47ca4cd7aa864ebd5
18df68d1581c11130c139fa52abb74dfd098a9af698a250645d6a4a65efcbf2d
1900ca9b482273df3127e221526023c025808d8fd65769a418fe1f346e7d41e2
1c389bf1859a00c58b6a97c02fc26c2fe9766c43e06242a94e92b6585b62398b
21a24922b29742977c4f7e25dd2be056dc02bc5e70c98e32ec3e0c6206f4d9ef
312a0e4db34a40cb95ba1fac8bf87deb45d0c5f048d38ac65eb060273b07df67
31804c48f9294c9fa7c165c89e487bfbebeda6daf3244ad30b93122bf933c79c
31f69d67eca6f3fc837e8d10dff4e2fb6643e33c118cff87df4fee2b183bf0e0
37e8b57ff4d724053b1917dc6edaca0708d44ceecd00cab7e4cabb336c2868d7
3ac57bea954ce68dc937f6954ae8a6a19a367a579aeeda7cc93ddd5968fae250
3ada20fbd80ec7f536db8303a5fa029af741a6914de61376ac8f81ac3ac728fd
3b5658532bc4058131689c5641def85d7ae25d5b837d3d1aff3af7bb25581f17
3c499faac4b973c237670f046973691a245ecd735ffebcca3e93337d94b71cde
3c4b87be8450e3120b7ad2b11ff59850950beb39906dc1636b3ee7b6390f2086
4732f025a2a69f6c40787854c5da122689702f00f4f423061bb30ab7fa1e98d3
5381b2a7a77448c4908f5c79d21631f56c88ead0365981cac1dcaafe493c313e
53e9511401000f61c9d910b92cd6d5a58e38ae541975135944885e53fa91ecb7
5dfbd8cf98ebd4977d4f240dcabd5cd67b936c0095c2d5b9a77896daea877df6
5eebdb584a1acd6aacc36c59c22ec51bbd077d2dbbe0890b52e62fa6fb9cf784
5ff742e134e3d17ec7abea435f718e8f5603b95e7984e024b2310ac9ef862ddf
60ff43424c0ba9dc259ab32405345ef325a4cb4d0baf0c0b0c13f9d3672e99eb
68c6411cc9afa68047641932530cf7201f17029167d4811375f1458cae32c7bd
6b2c41b42f75e64d435ba56c2f2b6d79a11b862a2d994487dab3e51e298bc5c9
6b93b7372941a09f1ea69f8b71c5c4e211ea0f8a24061e702002ca84457bcddd
6d0857a9c77f9c5f2a5e6921e1cb9f7e1a5d6b947ad63b364d291157d3f840fb
70f3a6fdbbc5e2ae79c28b48b6478ee3c8ea6f2b705ca9dc9bf8e63a4f6e0c8d
72baf2ecb0a9df607e54b64c0925ffc6739ab5a8b18900bf5c1930bcc799395d
748d546c6db44f6aa4bbb8e586d79f56c63fa87580eb19a0f2d5079cbe0952b7
79040421b5a48dcc6e611dfe187b2f3e355791ad8511adb84f5c0948aa1d6c89
797ae2dbb2c538710fefe75dbe380b9f55b614cb03c4ae09bb3172e8234dd9d9
7a73ae8cca6ce6fa88f89d6154811cb453d6e6db9fa8ed5fbdaf8895aae601a5
7b19538dcf6d4bb84590c458f09c5707c8db53a42861fa56533c49c1a3acd953
7e3634bfd66e601d7585b237437f11f7d614b33705ba5f7bd75ab176c8250d38
858dfa529b960c6f6226b53beb55ba1900d3f498ba7be40724ed5c16d7d5a44b
871e5629d9c8898babf3ed579586e3f5f94a6c4623d3a0a7f9a99bf9d95ffc7b
8763749fd09245e7fa8c0ee2cc797d5520a9ef5d6846f044a0cd7c969c4bd7d4
89d839bbdc786c006304f3c6c6939150380aaa9e84d82bc31cdf0cf7609a6243
8b21fbd40c89763f51d5e06680c0971623500f4724c25958446bac794797057b
8baebd525324297faf86639266060172ded963767c832a609a991fa92c8463ab
8d1ed904d90e08048f42cdc9a25c2159f0f8dc4aa9dc01b0207645ea53abe189
957ab8417606ad41ad31f006d997af3f647dd5215af899551d08b3b472a4bc85
a0332fe0baa316fe793e757f9cf5938b099e97dc4624ead6f3bad8555c8a419b
a1482e62ecc89696a75adea7052c2e98a75c9d37304723abd110d60962bafdb7
a28d0c82a2a37462c2975b5eda7f91e8fc3c2ed50abfe357948ec4faabbd4951
a6637685091835826e62af279cc6c648188797f9edc05a2399a6686349102774
a6f1f68827303e655488c8d54b3be3ce8b1097f3ff374a2e4bc82ff96812781c
abc5b2118bc1d8c82f3726a5e30cf22ae3fa1c572dd3327b281ea6fd97ae9c06
afc45cc0df7f7e481bff45c6f62a6418b6ae4c8b474ec36113e05ab7ca7e2743
b1f91355a8472e364e07f05dc69bbd9c74dc1943e9c4475f46c2b448bb6d6e5d
b2b7218c3f649b9077510aac309357e884c314e0f488abed391415defb249f4c
b6b685fe020c481161060df9dbef0fc205cde479056c18aaeae184daa3f8a9c0
b784301cb2edafea875f779cf24e018f06732561069f6c4c3d86548029671642
ba557bd6b2c1d3297b2c9bd7294e47b9ad9ec6a937cddc879dd563c61a9abcbd
bb451151e52f0868f98e32d26ffa7c2be412b47cd470bf90d3cfe777b4a19f85
bd39f32177dc7a20f5087c5460ebf589035d9051336c69f07a26398f76aec40e
bf37542e9eb7a3b2f51d107e56d7551e6248f06ce18918e3dda2ebe9da1b0e80
bf97c4ff35b5e2c039aa1f1a9a164b7ec4d9339a631c84910b9a4d03b7927b8a
c2ba0018de8dcf0abfb2669cce95ed09377e9a9da7ff8e74e95688c99a025634
c3d797e67edf0dd435808f2f79ff4bfd0cf9177307f4a112b7da09f7dfdd8f2e
c441afb337c4803eed20ae255fbad3cdfac2800475c51e00a55369909efb4c89
cc6ad344d30178e04e49ab16cd43744925676562aded051835fb3f73401f31fa
ceab18331f785d0bf215f551b90f00567e36d339ba8e3ed8e45c0ad410b25808
d02a1eb597c66b602ac7d55095f771345ff5e90905ea12e523df2095030752b6
d6142f48664208710bab9fcab8dfcda66ad75ad756d2ce9c3aa243dcbc29bf4a
d665a8547baf067f2216821ecd4145eab1c75868f024d09140fb265b819d5194
d8d2092e174240d7bac63a9e1c199b442e1cb0f39d7fa32510b1aa7717c3ae38
e24de02415946133176b66017d54a5dcd7270c83f5ef01d79faff4e64d13c63b
e5502722c2bb84876903549445534c47cdaa586a0bb1e5b3a53162d75cc6cb28
e66ae0ac443b5140a1b35b5aaa6899eea296d9d633988eb044a395a34a887431
e92e01977d85f6834f57bd09e29e654b10da798844e4a64470cb22dac78bef93
e9723a2a9ca45787c35b864605a6be71ccf12b2d96dad8e7fc39117f7ba29abb
f28bb7bc5c801d5444ba6816e3a91d5bfaf0307578b7a1529415fc220fd9e9e8
f86b6aa11a276c24dd80db48f43c8a2f0c8df6e5426a7a0fee322c0427421ebb
“Type 1” Staging Server IP Addresses:
77[.]83[.]199[.]3
77[.]83[.]199[.]15
77[.]83[.]199[.]31
77[.]83[.]199[.]42
77[.]83[.]199[.]73
77[.]83[.]199[.]82
77[.]83[.]199[.]88
77[.]83[.]199[.]90
77[.]83[.]199[.]112
77[.]83[.]199[.]123
77[.]83[.]199[.]132
77[.]83[.]199[.]142
77[.]83[.]199[.]170
79[.]141[.]160[.]24
79[.]141[.]160[.]34
79[.]141[.]161[.]50
79[.]141[.]161[.]171
79[.]141[.]162[.]35
79[.]141[.]162[.]37
79[.]141[.]162[.]50
79[.]141[.]162[.]132
79[.]141[.]162[.]149
79[.]141[.]162[.]169
79[.]141[.]162[.]177
79[.]141[.]162[.]181
79[.]141[.]162[.]187
79[.]141[.]162[.]204
79[.]141[.]162[.]229
79[.]141[.]163[.]138
79[.]141[.]163[.]176
79[.]141[.]172[.]204
79[.]141[.]172[.]223
79[.]141[.]172[.]229
79[.]141[.]172[.]232
79[.]141[.]172[.]240
79[.]141[.]173[.]60
79[.]141[.]173[.]161
79[.]141[.]173[.]168
85[.]158[.]111[.]29
85[.]158[.]111[.]38
85[.]158[.]111[.]53
85[.]158[.]111[.]75
85[.]158[.]111[.]81
85[.]158[.]111[.]126
89[.]46[.]38[.]34
89[.]46[.]38[.]48
89[.]46[.]38[.]88
89[.]169[.]12[.]48
91[.]193[.]19[.]32
91[.]193[.]19[.]64
91[.]193[.]19[.]78
91[.]193[.]19[.]127
91[.]193[.]19[.]163
91[.]193[.]19[.]188
91[.]193[.]19[.]190
98[.]142[.]240[.]165
98[.]142[.]240[.]188
98[.]142[.]240[.]214
98[.]142[.]240[.]221
98[.]142[.]240[.]246
98[.]142[.]251[.]26
98[.]142[.]251[.]32
98[.]142[.]251[.]42
98[.]142[.]251[.]53
185[.]33[.]84[.]131
185[.]33[.]84[.]153
185[.]33[.]84[.]169
185[.]33[.]85[.]20
185[.]33[.]85[.]26
185[.]33[.]85[.]33
185[.]33[.]85[.]38
185[.]33[.]85[.]52
185[.]33[.]86[.]37
193[.]42[.]38[.]11
193[.]42[.]38[.]79
193[.]42[.]38[.]85
193[.]42[.]38[.]86
193[.]111[.]208[.]2
193[.]111[.]208[.]17
193[.]111[.]208[.]19
193[.]111[.]208[.]23
193[.]111[.]208[.]24
193[.]111[.]208[.]46
193[.]111[.]208[.]75
193[.]111[.]208[.]97
193[.]111[.]208[.]100
Additional IP Addresses Likely Linked to “Type 1” Staging Infrastructure:
23[.]140[.]40[.]66
45[.]153[.]191[.]245
46[.]29[.]163[.]28
89[.]169[.]12[.]48
89[.]253[.]222[.]25
89[.]253[.]222[.]156
95[.]182[.]123[.]86
185[.]231[.]245[.]158
217[.]114[.]15[.]253
“Type 2” Staging Server IP Addresses:
45[.]61[.]134[.]76
77[.]83[.]199[.]162
79[.]141[.]162[.]135
79[.]141[.]163[.]169
91[.]193[.]19[.]220
144[.]172[.]115[.]211
172[.]86[.]90[.]84
185[.]33[.]86[.]11
185[.]80[.]53[.]79
194[.]15[.]216[.]118
“Type 2” Staging Server Domains:
filmlerzltyazilimsx[.]shop
foolowme[.]com
joiner[.]best
lowi1[.]com
morniksell[.]com
persistancejs[.]store
pomofight[.]com
port4loms[.]com
signaturepl[.]com
yungask[.]com
Domains Linked to oreshnik[@]mailum[.]com:
108zhao[.]shop
1sou[.]top
6hms[.]top
789pettoys[.]shop
7serv[.]top
99wc[.]top
abocamuseum[.]icu
actionmovies[.]top
alcmz[.]top
alhasba[.]com
amxdh1[.]icu
anoteryo[.]top
arearugs[.]top
as5yo[.]top
ashesplayer[.]top
avodaride[.]top
azyaamode[.]shop
baihao[.]shop
baihuah[.]top
bedoueroom[.]top
bestproductreviews[.]xyz
bestrollerballpen[.]top
blogdojhow[.]com
bnpparibas[.]top
bokra[.]top
bond007[.]xyz
boxworld[.]top
bstionline[.]com
buildingjobs[.]xyz
buscavuelosbaratos[.]top
buyedmeds[.]top
buylisinopril[.]top
celebrex[.]top
chaojiwang[.]top
chenyiwen[.]top
chinapark[.]top
christianlouboutin2017[.]top
cialissale[.]top
cinselurunler[.]xyz
coinseasygenerator[.]top
couterfv[.]top
couturella[.]shop
covaticonstructioncorp[.]shop
cozartan[.]top
cryptohardware[.]shop
dcdh4[.]shop
dealermobil[.]top
depechemode[.]shop
directoryframework[.]top
discountmontblanc[.]top
discoveronline[.]top
doodstream[.]shop
downloadfreak[.]top
erectilehelp[.]top
filmezz[.]top
filmlerzltyazilimsx[.]shop
fjs95[.]shop
fmovies123[.]top
forging[.]top
fragzone[.]top
franquicias[.]top
fuckhdmov[.]top
gededewe[.]shop
getin[.]top
glitterygadgets[.]shop
gmartph[.]shop
gmt-a[.]shop
grandzxc[.]bet
guosong[.]top
haidao10[.]top
headtechnologies[.]xyz
healthcareplans[.]top
heim-k[.]shop
helperection[.]top
hilfe-ed[.]top
hirek[.]top
howtogetaloan[.]top
ida-ci[.]com
islighting[.]top
iwine[.]top
izone[.]digital
jerseysus[.]top
jiezishijie[.]top
jkse[.]shop
jsmakert[.]shop
k2bsc[.]top
kaestner[.]top
kamagrafr[.]icu
kanshuwang[.]top
kazumaka[.]top
kfzversicherungskosten[.]top
khusinhthaidanphuong[.]top
kingdomholding[.]top
krediteonlinevergleichen[.]top
lang3666[.]top
langwonet[.]top
layardrama21[.]top
lebensversicherungvergleich[.]top
levciavia[.]top
linhua97[.]top
linksoflondononsale[.]top
linksoflondonsale[.]top
liruo[.]top
liveskortv[.]shop
loanonline[.]top
loispaigesimenson[.]com
losartan[.]top
lovedou[.]top
lqsword[.]top
lx7v9[.]top
lycosex[.]top
machine-a-plastifier[.]com
manwithedhelp[.]top
marmocer[.]top
mbpen163[.]top
medicamentsbonmarche[.]top
meimei68[.]top
menjimmychooonline[.]top
milebox[.]shop
mindsetgrowth[.]shop
mm37[.]icu
monclerjackets[.]top
moruk[.]xyz
motocyclenews[.]top
moviefone[.]top
moviesone[.]top
movtime76[.]shop
movtime78[.]shop
musicdownloader[.]top
my-privatebanker[.]top
mybeststream[.]xyz
nackt-bilder[.]top
nana44[.]shop
newbalancesport[.]top
palcomp3[.]top
parisforrent[.]top
pasangiklan[.]top
patekphillipwatches[.]top
pielsteel[.]top
pravaix[.]top
rag382[.]top
rasin[.]shop
refanprediction[.]shop
regopramide[.]top
rnsddse[.]top
sales2016[.]top
sdnews[.]top
searchgo[.]shop
searchweb[.]top
semikeren[.]icu
simvascor[.]icu
simvascor[.]top
snapcans[.]top
sneakermall[.]top
soap2dayfree[.]top
socialsignals[.]shop
socksforrocks[.]shop
streaming-films[.]xyz
syavsp5[.]top
tdsc[.]top
techradar[.]top
tiffanyearringforwomen[.]top
todoarmarios[.]top
todocalefactores[.]top
todocarritos[.]top
travelplace[.]top
trendings[.]top
universaltechnology[.]top
uochut[.]shop
via345[.]top
villahome[.]top
viloriterso[.]icu
viptravelcentres[.]com
vog168[.]top
wandan[.]top
wap9[.]top
warpdrive[.]top
watchesbest[.]top
wavob[.]top
wdwnp[.]top
xelesex[.]top
ydh7[.]shop
yntz6[.]shop
yourcialsupply[.]top
youtubevideo[.]top
yxta[.]top
yybvf[.]top
zaheirx[.]shop
zakachka[.]top
zerolendnow[.]top
zt45gg[.]top
Compromised Law Firm Websites:
bianchilawgroup[.]com
brattonlawgroup[.]com
brighterdaylaw[.]com
defensegroup[.]com
dwicriminallawcenter[.]com
fisherstonelaw[.]com
jarrettfirm[.]com
raineyandrainey[.]com
rbbfirm[.]com
rmvlawyer[.]com
www[.]brentadams[.]com
www[.]cfblaw[.]com
www[.]gerlinglaw[.]com
www[.]immigration-defense[.]com
www[.]schwartzandschwartz[.]com
Sectop RAT Hash:
59e7e7698d77531bfbfea4739d29c14e188b5d3109f63881b9bcc87c72e9de78
SecTopRAT C2 IP Address:
85[.]158[.]110[.]179[:]15847
Other Hashes:
5f1bd92ad6edea67762c7101cb810dc28fd861f7b8c62e6459226b7ea54e1428
Email Address Linked to GrayCharlie:
oreshnik[@]mailum[.]com

We need to act with urgency to address the growing AI divide
Microsoft announces at the India AI Impact Summit it is on pace to invest USD $50 billion by the end of the decade to help bring AI to countries across the Global South
Artificial intelligence is diffusing at an impressive speed, but its adoption around the world remains profoundly uneven. As Microsoft’s latest AI Diffusion Report shows, AI usage in the Global North is roughly twice that of the Global South. And this divide continues to widen. This disparity impacts not only national and regional economic growth, but whether AI can deliver on its broader promise of expanding opportunity and prosperity around the world.
The India AI Impact Summit rightly has placed this challenge at the center of its agenda. For more than a century, unequal access to electricity exacerbated a growing economic gap between the Global North and South. Unless we act with urgency, a growing AI divide will perpetuate this disparity in the century ahead.
Solutions will not come easily. The needs are multifaceted, and will require substantial investments and hard work by governments, the private sector, and nonprofit organizations. But the opportunity is clear. If AI is deployed broadly and used well by a young and growing population, it offers a real prospect for catch-up economic growth for the Global South. It might even provide the biggest such opportunity of the 21st century.
As a company, we are committed to playing an ambitious and constructive role in supporting this opportunity. This week in Delhi, we’re sharing that Microsoft is on pace to invest $50 billion by the end of the decade to help bring AI to countries across the Global South. This is based on a five-part program to drive AI impact, consisting of the following:
- Building the infrastructure needed for AI diffusion
- Empowering people through technology and skills for schools and nonprofits
- Strengthening multilingual and multicultural AI capabilities
- Enabling local AI innovations that address community needs
- Measuring AI diffusion to guide future AI policies and investments
One thing that is clear this week at the summit in India is that success will require many deep partnerships. These must span borders and bring people and organizations together across the public, private, and nonprofit sectors.
1. Building the infrastructure needed for AI diffusion
Infrastructure is a prerequisite for AI diffusion, requiring reliable electricity, connectivity, and compute capacity. To help address infrastructure gaps and support the growing needs of the Global South, Microsoft has steadily increased its investments in AI-enabling infrastructure across these regions. In our last fiscal year alone, Microsoft invested more than $8 billion in datacenter infrastructure serving the Global South. This includes new infrastructure in India, Mexico, and countries in Africa, South America, Southeast Asia, and the Middle East.
We’re coupling our investments in datacenters with an ambitious effort to help close the Global South’s connectivity divide. We’ve been pursuing aggressively a global goal to extend internet access to 250 million people in unserved and underserved communities in the Global South, including 100 million people in Africa.
As we announced in November, we’ve already reached 117 million people across Africa through partnerships with organizations such as Cassava Technologies, Mawingu, and others that are building last‑mile networks across rural and urban communities alike. We’re closing in on our global goal of reaching 250 million people and will share an update on that progress soon.
We’re investing in AI infrastructure with sensitivity to digital sovereignty needs. We recognize that in a fragmented world, we must offer customers attractive choices for the use of our offerings. This includes sovereign controls in the public cloud, private sovereign offerings, and close collaboration with national partners.
We pursue all this with commitments to protect cybersecurity, privacy, and resilience. In the age of AI, we ensure that our customers’ AI-based innovations and intellectual property remain in their hands and under their control, rather than being transferred to AI providers.
Critically, we balance our focus on national sovereignty with our efforts to support digital trust and stability across borders. The Global South requires enormous investments to fund infrastructure for datacenters, connectivity, and electricity. It is difficult to imagine meeting all these needs without foreign direct investment, including from international technology firms.
This need is part of what informed our announcement last week at the Munich Security Conference of the new Trusted Tech Alliance. This new partnership brings together 16 leading technology companies from 11 countries and four continents. We’ve agreed together that we will adhere to five core principles designed to ensure trust in technology. Ultimately, we believe the Global South—as well as the rest of the world—needs both to protect its digital sovereignty and benefit from new investments and the best digital innovations the world has to offer.
2. Empowering people through technology and skills for schools and nonprofits
Ultimately, datacenters, connectivity, and electricity provide only part of the digital infrastructure a nation needs. History shows that the ability to provide access to technology and technology skills are equally important for economic development.
As a company, we’re focused on this in multiple ways. One critical aspect of our work is based on programs to provide cloud, AI, and other digital technologies to schools and nonprofits across the Global South. Another is our work to advance broad access to AI skills. In our last fiscal year, Microsoft invested more than $2 billion in these programs in the Global South. This includes direct financial grants, technology donations, skilling programs, and below-market product discounts.
AI skills are foundational to ensuring that AI expands opportunity and enables people to pursue more impactful real-world applications. With the launch of Microsoft Elevate in July, we committed to helping 20 million people in and beyond the Global South earn in-demand AI skilling credentials by 2028. After training 5.6 million people across India in 2025, we advanced this work by setting a goal last December to equip 20 million people in India with essential AI skills by 2030.
As part of that commitment, today we are announcing the launch of Elevate for Educators in India to strengthen the capacity of two million teachers across more than 200,000 schools, vocational institutes, and higher education settings. Our goal is to help the country’s teaching workforce lead confidently in an AI‑driven future. The program will be delivered in partnership with India’s national education and workforce training authorities, expanding equitable AI opportunities for eight million students.
Through Microsoft Elevate, we’re also working to introduce new educator credentials and a global professional learning community that enables teachers to share best practices with peers worldwide. This effort will involve large-scale capacity building initiatives, including AI Ambassadors, Educator Academies, AI Productivity Labs, and Centers of Excellence. It will equip 25,000 institutions with inclusive AI infrastructure while integrating AI learning pathways into major government platforms.
3. Strengthening multilingual and multicultural AI capabilities
Language is another major barrier to AI diffusion across the Global South, particularly in regions where digitally underrepresented languages prevail and access to essential services depends on local-language communication. For billions of people worldwide, AI systems perform less consistently in the languages they rely on most than in English.
That’s why we’re announcing this week new steps to increase our investments across the AI lifecycle, from data and models to evaluation and deployment, to strengthen multilingual and multicultural capabilities and support more inclusive AI systems that will better serve the Global South.
First, we’re investing upstream in language data and model capability. This includes support for LINGUA Africa, which builds on what we learned through LINGUA Europe: that investing in language data and model capability in partnership with local communities can materially improve AI performance for underrepresented languages.
Through LINGUA Africa—a $5.5 million open call led by the Masakhane African Languages Hub, Microsoft’s AI for Good Lab, and the Gates Foundation, with additional support from the UK government—we are prioritizing open, responsibly sourced data across text, speech, and vision as well as use-case-driven AI model development. By enabling African languages in high-impact sectors like education, food security, health, and government services, LINGUA Africa aims to ensure AI advances translate into tangible improvements in people’s daily lives.
Second, we’re advancing multilingual and multicultural evaluation tools. We’re helping expand the MLCommons AILuminate benchmark to include major Indic and Asian languages, enabling more reliable measurement of AI safety and security beyond English.
Today, even when automated evaluation tools expand language coverage, they too often rely on machine translation or English-first model behavior, with predictable failures when local expressions shift meaning. Partnering with academic and government institutions in India, Japan, Korea, and Singapore, and with industry, Microsoft is co-leading AILuminate’s multilingual, multicultural, and multimodal expansion that builds from the ground up. With a pilot dataset of 7,000 high-quality text-and-image prompts for Hindi, Tamil, Malay, Japanese, and Korean, we’re developing tools that reflect how risks manifest in local linguistic and cultural contexts, not just how they appear after translation.
Microsoft Research is also advancing Samiksha, a community-centered method for evaluating AI behavior in real-world contexts, in collaboration with Karya and The Collective Intelligence Project in India. Samiksha encodes local language use, culturally specific communication norms, and locally relevant use cases directly into core testing artifacts by surfacing failure modes that English-first evaluations routinely miss.
Finally, we’re working to scale content provenance for linguistic diversity. For trusted AI deployment, the ecosystem benefits from tools to identify the provenance of digital content like images, audio, or video, distinguishing whether it’s AI-generated. With partners in the Coalition for Content Provenance and Authenticity (C2PA), Microsoft is helping extend content provenance standards beyond an English-ready baseline. This includes forthcoming support for multiple Indic languages across metadata, specifications, and UX guidance, alongside efforts to support mobile-first deployment. With these investments, hundreds of millions more people in India will be better equipped to identify synthetic media in their primary language.
4. Enabling local AI innovations that address community needs
As India’s guiding sutras for the AI Impact Summit recognize, AI must be applied to address pressing challenges in collaboration with people and organizations in the Global South. Microsoft’s increasing investments prioritize locally defined problems, locally grounded expertise, and real-world impact. Our goal is straightforward: to ensure that AI solutions are not only technically sound, but socially relevant and sustainable.
Today, Microsoft is announcing a new AI initiative to strengthen food security across Sub-Saharan Africa, starting in Kenya and designed to scale across the region. Across Global South communities, food security and sustainable agriculture are critical to resilience and progress. In collaboration with NASA Harvest, the government of Kenya, the East Africa Grain Council, UNDP AI Hub for Sustainable Development, and FAO, our AI for Good Lab will use AI on top of satellite data to provide critical, timely food security insights. This builds on what we’ve learned in helping to address rice farming challenges in India, where severe groundwater depletion prompted 150,000 farmers in Punjab to adopt water-saving methods. In collaboration with The Nature Conservancy, Microsoft’s AI for Good Lab developed a classification system with satellite imagery to empower policymakers to track adoption of sustainable rice farming practices, target interventions, and measure water management impacts at scale.
Through Project Gecko, Microsoft Research is also co-designing AI technologies with local communities in East Africa and South Asia to support agriculture. This work includes the Paza family of automatic speech recognition models that can operate on mobile devices across six Kenyan languages, multilingual Copilots, and a Multimodal Critical Thinking (MMCT) Agent that can reason over community-generated video, voice, and text. Microsoft also launched PazaBench—the first automatic speech recognition leaderboard, with initial coverage of 39 African languages—and developed two playbooks for multilingual and multicultural capabilities, Paza and Vibhasha. Likewise, our AI for Good Lab developed a reproducible pipeline for adapting open-weight large language models to low-resource languages, demonstrating measurable gains for languages such as Chichewa, Inuktitut, and Māori.
5. Measuring AI diffusion to guide future AI policies and investments
Finally, accelerating diffusion requires a firm understanding of where AI is being used, how it is being adopted, and where gaps persist. Building on our AI Diffusion Reports and Microsoft GitHub’s long track record of contributing to the OECD AI Policy Observatory, the WIPO Global Innovation Index, and other cross‑country analyses, we’re increasing our investments in research and data sharing to track AI diffusion.
We’re advancing new methods for sharing AI adoption metrics. For example, based on models used in public code repositories hosted on Microsoft GitHub and privacy-preserving aggregated usage signals from Azure Foundry, we’re scaling this work through contributions to the forthcoming Global AI Adoption Index developed by the World Bank.
Signals from the global developer community that builds, adapts, and deploys AI-enabled software round out adoption research. At 24 million, the Indian developer community is the second largest national community on GitHub, where developers learn about and collaborate with the world on AI. The Indian community is also the fastest growing among the top 30 largest economies, with growth at more than 26 percent each year since 2020 and a recent surge of over 36 percent in annual growth as of Q4 2025. Indian developers rank second globally in open-source contributions, second in GitHub Education users, and second in contributions to public generative AI projects, with readiness to use tools like GitHub Copilot across academic, enterprise, and public interest settings enabling AI diffusion.
Insights from this evidence base help inform investments in infrastructure, language capabilities, skilling, or beyond, supporting more targeted and effective interventions to expand AI’s benefits. They also create a common empirical baseline to track progress over time—so AI diffusion becomes something we can measure and shape, not just observe.
Sustaining impact at scale through coordinated global action
For AI to diffuse broadly and deliver meaningful impact across regions, several conditions matter. As a company, we are focused on the need for accessible AI infrastructure, systems that work reliably in real-world contexts, and technologies that can be applied toward local challenges and opportunities. Microsoft is committed to working with partners to advance this work, including sharing data to track progress.
The post We need to act with urgency to address the growing AI divide appeared first on Microsoft On the Issues.
Critical Vulnerabilities in Ivanti EPMM Exploited
We discuss widespread exploitation of Ivanti EPMM zero-day vulns CVE-2026-1281 and CVE-2026-1340. Attackers are deploying web shells and backdoors.
The post Critical Vulnerabilities in Ivanti EPMM Exploited appeared first on Unit 42.

A New Denial-of-Service Vector in React Server Components
React Server Components (RSC) have introduced a hybrid execution model that expands application capabilities while increasing the potential attack surface.
Following earlier disclosures and fixes related to React DoS vulnerabilities, an additional analysis of RSC internals was conducted to assess whether similar denial-of-service risks remained.
This analysis identified a new denial-of-service (DoS) condition that, under specific circumstances, can render a React server unreachable.
Context
Previous reports showed that malformed requests could trigger excessive server-side computation during RSC rendering and serialization. While patches addressed the known attack patterns, it remained unclear whether these issues were isolated or indicative of broader weaknesses.
Technical Overview
The analysis focused on the following RSC code paths:
- Server Component request parsing
- Recursive resolution and payload generation
By evaluating server behavior when processing unexpected but syntactically valid inputs, an alternative execution path was identified in which server resources could be exhausted. This behavior is not covered by existing mitigations and could be abused to sustain a denial-of-service condition.
The issue was reported to the React security team. Due to the potential impact, exploitation details are not disclosed here.
Mitigation
While framework-level fixes are under review:
- Imperva customers are protected against this issue.
- Imperva’s Application Security solutions detect and block malicious request patterns that trigger abnormal server-side processing before vulnerable paths are reached.
Conclusion
This work highlights the importance of ongoing security evaluation of modern application architectures and the role of layered protections in mitigating denial-of-service conditions.
The post A New Denial-of-Service Vector in React Server Components appeared first on Blog.

-
Malwarebytes
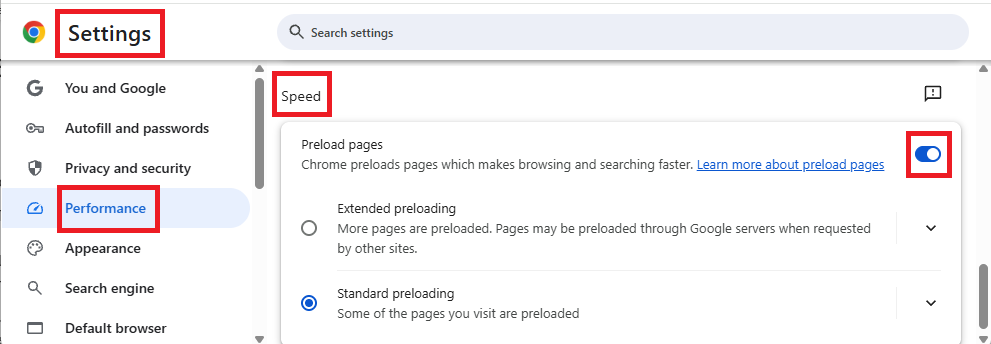
- Chrome “preloading” could be leaking your data and causing problems in Browser Guard
Chrome “preloading” could be leaking your data and causing problems in Browser Guard
This article explains why Chrome’s “preloading” feature can cause scary-looking blocks in Malwarebytes Browser Guard and how to turn it off.
Modern browsers want to provide content instantly. To do that, Chrome includes a feature called page preloading. When this is enabled, Chrome doesn’t just wait for you to click a link. It guesses what you’re likely to click next and starts loading those pages in the background—before you decide whether to visit them.
That guesswork happens in several places. When you type a search into the address bar, Chrome may start preloading one or more of the top search results so that, if you click them, they open almost immediately. It can also preload pages that are linked from the site you’re currently on, based on Google’s prediction that they’re “likely next steps.” All of this happens quietly, without any extra tabs opening, and often without any obvious sign that more pages are being fetched.
From a performance point of view, that’s clever. From a privacy and security point of view, it’s more complicated.
Those preloaded pages can run code, drop cookies, and contact servers, even if you never actually visit them in the traditional sense. In other words, your browser can talk to a site you didn’t consciously choose to open.
Malwarebytes Browser Guard inspects web traffic and blocks connections to domains it considers malicious or suspicious. So, if Chrome decides to preload a search result that leads to a site on our blocklist, Browser Guard will still do its job and stop that background connection. The result can be confusing: You see a warning page (called a block page) for a site you don’t recognize and are sure you never clicked.
Nothing unusual is happening there, and it does not mean your browser is “clicking links by itself.” It simply means Chrome’s preloading feature made a behind-the-scenes request, and Browser Guard intercepted it as designed. Other privacy tools take a similar approach. Some popular content blockers disable preloading by default because it leaks more data and can contact unwanted sites.
For now, the simplest way to stop these unexpected block pages is to turn off preloading in Chrome’s settings, which prevents those speculative background requests.
How to manage Chrome’s preloading setting
We recommend turning off page preloading in Chrome to protect your browsing privacy and to stop seeing unexpected block pages when searching the web. If you don’t want to turn off page preloading, you can try using a different browser and repeating your search.
To turn off page preloading:
- In your browser search bar, enter:
chrome://settings - In the left sidebar, click Performance.
- Scroll down to Speed, then toggle Preload pages off.

We don’t just report on data privacy—we help you remove your personal information
Cybersecurity risks should never spread beyond a headline. With Malwarebytes Personal Data Remover, you can scan to find out which sites are exposing your personal information, and then delete that sensitive data from the internet.
-
Microsoft Security Blog
- Unify now or pay later: New research exposes the operational cost of a fragmented SOC
Unify now or pay later: New research exposes the operational cost of a fragmented SOC
Security operations are entering a pivotal moment: the operating model that grew around network logs and phishing emails is now buckling under tool sprawl, manual triage, and threat actors that outpace defender capacity. New research from Microsoft and Omdia shows just how heavy the burden can be—security operations centers (SOCs) juggle double-digit consoles, teams manually ingest data several times a week, and nearly half of all alerts go uninvestigated. The result is a growing gap between cyberattacker speed and defender capacity. Read State of the SOC—Unify Now or Pay Later to learn how hidden operational pressures impact resilience—compelling evidence to why unification, automation, and AI-powered workflows are quickly becoming non-negotiables for modern SOC performance.
The forces pushing modern SOC operations to a breaking point
The report surfaces five specific operational pressures shaping the modern SOC—spanning fragmentation, manual toil, signal overload, business-level risk exposure, and detection bias. Separately, each data point is striking. But taken together, they reveal a more consequential reality: analysts spend their time stitching context across consoles and working through endless queues, while real cyberattacks move in parallel. When investigations stall and alerts go untriaged, missed signals don’t just hurt metrics—they create the conditions for preventable compromises. Let’s take a closer look at each of the five issues:
1. Fragmentation
Fragmented tools and disconnected data force analysts to pivot across an average of 10.9 consoles1 and manually reconstruct context, slowing investigations and increasing the likelihood of missed signals. These gaps compound when only about 59% of tools push data to the security information and event management (SIEM), leaving most SOCs manually ingesting data and operating with incomplete visibility.
2. Manual toil
Manual, repetitive data work consumes an outsized share of analyst capacity, with 66% of SOCs losing 20% of their week to aggregation and correlation—an operational drain that delays investigations, suppresses threat hunting, and weakens the SOC’s ability to reduce real risk.
3. Security signal overload
Surging alert volumes bury analysts in noise with an estimated 46% of alerts proving false positives and 42% going uninvestigated, overwhelming capacity, driving fatigue, and increasing the likelihood real cyberthreats slip through unnoticed.
4. Operational gaps
Operational gaps are directly translating into business disrupting incidents, with 91% of security leaders reporting serious events and more than half experiencing five or more in the past year—exposing organizations to financial loss, downtime, and reputational damage.
5. Detection bias
Detection bias keeps SOCs focused on tuning alerts for familiar cyberthreats—52% of positive alerts map to known vulnerabilities—leaving dangerous blind spots for emerging tactics, techniques, and procedures (TTPs). This reactive posture slows proactive threat hunting and weakens readiness for novel attacks even as 75% of security leaders worry the SOC is losing pace with new cyberthreats.
Read the full report for the deeper story, including chief information security officer (CISO)-level takeaways, expanded data, and the complete analysis behind each operational pressure, as well as insights that can help security professionals strengthen their strategy and improve real world SOC outcomes.
What CISOs can do now to strengthen resilience
Security leaders have a clear path to easing today’s operational strain: unify the environment, automate what slows teams down, and elevate identity and endpoint as a single control plane. The shift is already underway as forward-leaning organizations focus on high-impact wins—automating routine lookups, reducing noise, streamlining triage, and eliminating the fragmentation and manual toil that drain analyst capacity. Identity remains the most critical failure point, and leaders increasingly view unified identity to endpoint protection as foundational to reducing exposure and restoring defender agility. And as environments unify, the strength of the underlying graph and data lake becomes essential for connecting signals at scale and accelerating every defender workflow.
As AI matures, leaders are also looking for governable, customizable approaches—not black box automation. They want AI agents they can shape to their environment, integrate deeply with their SIEM, and extend across cloud, identity, and on-premises signals. This mindset reflects a broader operational shift: modern key performance indicators (KPIs) will improve only when tools, workflows, and investigations are unified, and automation frees analysts for higher value work.
The report details a roadmap for CISOs that emphasizes unifying signals, embedding AI into core workflows, and strengthening identity as the primary control point for reducing risk. It shows how leaders can turn operational friction into strategic momentum by consolidating tools, automating routine investigation steps, elevating analysts to higher value work, and preparing their SOCs for a future defined by integrated visibility, adaptive defenses, and AI-assisted decision making.
Chart your path forward
The pressures facing today’s SOCs are real, but the path forward is increasingly clear. As this report shows, organizations that take these steps aren’t just reducing operational friction—they’re building a stronger foundation for rapid detection, decisive response, and long-term readiness. Read State of the SOC—Unify Now or Pay Later for deeper guidance, expanded findings, and a phased roadmap that can help security professionals chart the next era of their SOC evolution.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us on LinkedIn (Microsoft Security) and X (@MSFTSecurity) for the latest news and updates on cybersecurity.
1The study, commissioned by Microsoft, was conducted by Omdia from June 25, 2025, to July 23, 2025. Survey respondents (N=300) included security professionals responsible for SOC operations at mid-market and enterprise organizations (more than 750 employees) across the United States, United Kingdom, and Australia and New Zealand. All statistics included in this post are from the study.
The post Unify now or pay later: New research exposes the operational cost of a fragmented SOC appeared first on Microsoft Security Blog.