Deze gevaarlijke malware is ontdekt op 400.000 Windows-computers



rvrsh3ll // Introduction This blog post is intended to give a light overview of device codes, access tokens, and refresh tokens. Here, I focus on the technical how-to for standing […]
The post Dynamic Device Code Phishing appeared first on Black Hills Information Security, Inc..
Sally Vandeven // We have all heard people talk about how much cooler Linux is than Windows, so much easier to use, etc. Well, they are not necessarily wrong… but we […]
The post Rainy Day Windows Command Research Results appeared first on Black Hills Information Security, Inc..
Sally Vandeven & David Fletcher // This is the podcast version of Sally & David’s webcast. For the whole webcast see our webcast post. Links that are mentioned in this […]
The post PODCAST: Hacker Tools, Compliments of Microsoft appeared first on Black Hills Information Security, Inc..

David Fletcher & Sally Vandeven// Join David “Fletch” and Sally as they explore the cornucopia of wonderful, free tools in the SysInternals Suite that conveniently are signed by Microsoft and […]
The post WEBCAST: Hacker Tools, Compliments of Microsoft appeared first on Black Hills Information Security, Inc..
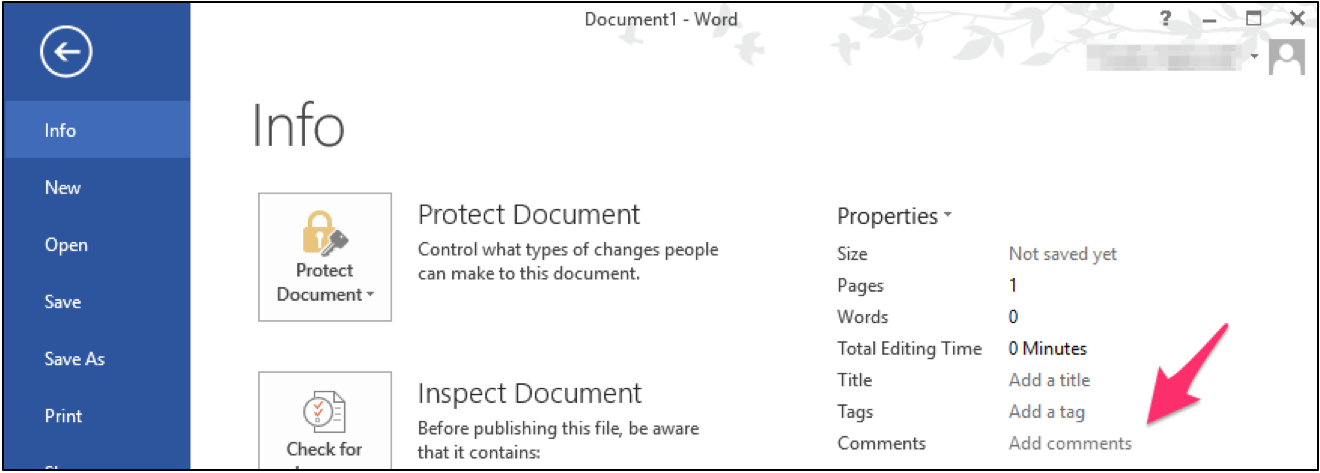
Carrie Roberts* // Can you think of a reason why you might want to put a lengthy comment into the properties of an MS Office document? If you can, then […]
The post Hide Payload in MS Office Document Properties appeared first on Black Hills Information Security, Inc..

Jordan Drysdale & Kent Ickler // In this webcast, we demonstrate some standard methodologies utilized during an internal network review. We also discuss various tools used to test network defenses […]
The post WEBCAST: Wrangling Internal Network Vulnerabilities appeared first on Black Hills Information Security, Inc..
Beau Bullock // Overview Microsoft Exchange users have the power to grant other users various levels of access to their mailbox folders. For example, a user can grant other users […]
The post Abusing Exchange Mailbox Permissions with MailSniper appeared first on Black Hills Information Security, Inc..
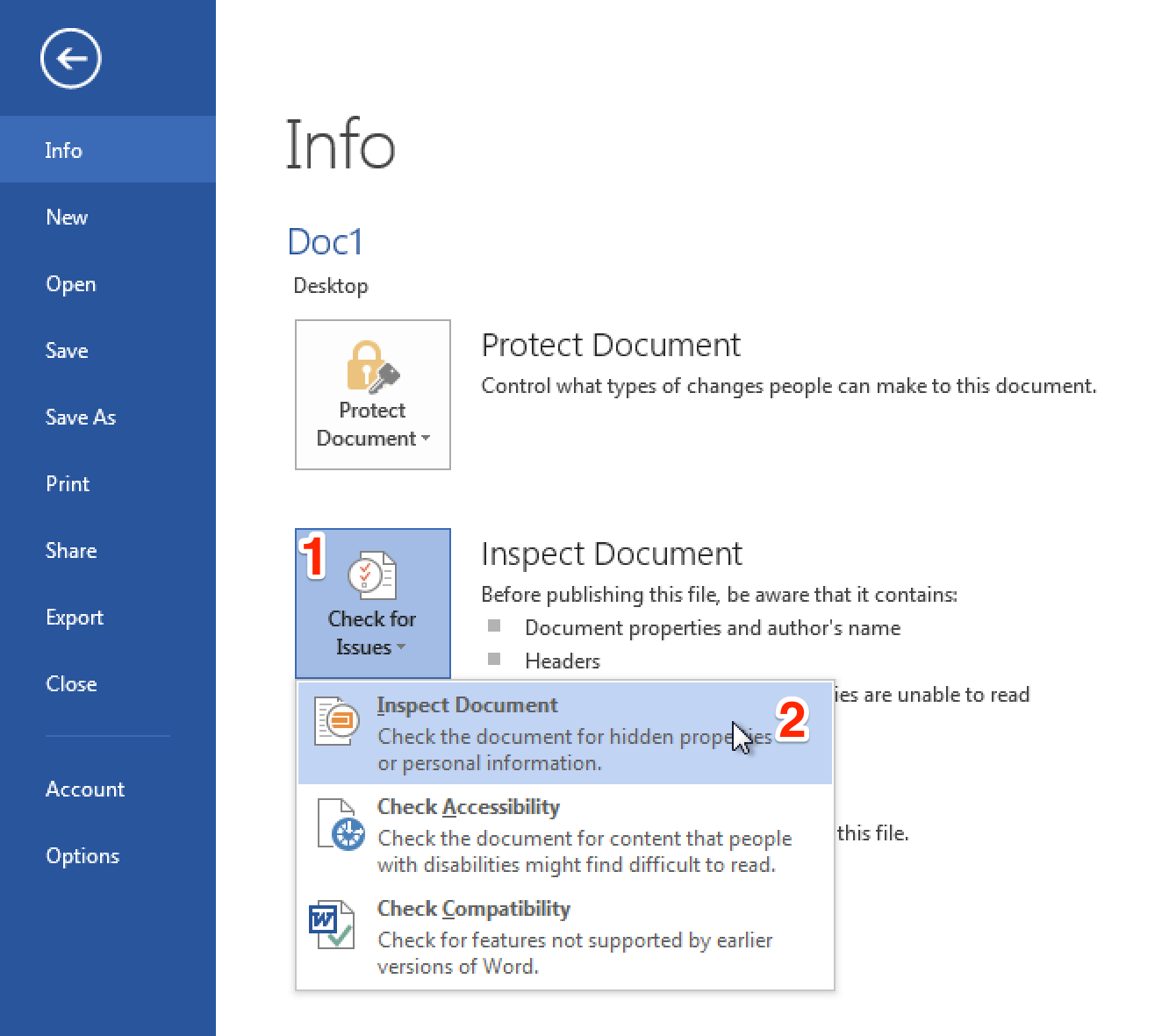
Ethan Robish // In my last two posts I showed how to insert tracking bugs in both .docx (Part 1) and .xlsx files (Part 2). But don’t let all that effort go […]
The post Bugging Microsoft Files: Part 3 – Clearing Metadata appeared first on Black Hills Information Security, Inc..

Ethan Robish // If you’re familiar with ADHD and Web Word Bugs, you likely already know the method to create web tracking software using .html files renamed as .doc files. […]
The post Bugging Microsoft Files: Part 1 – Docx Files using Microsoft Word appeared first on Black Hills Information Security, Inc..

Beau Bullock // Full Disclosure: Black Hills Information Security believes in responsible disclosure of vulnerabilities. This vulnerability was reported to Microsoft on September 28th, 2016. As of the publication date of […]
The post Bypassing Two-Factor Authentication on OWA & Office365 Portals appeared first on Black Hills Information Security, Inc..
Lawrence Hoffman // So Microsoft is open sourcing PowerShell and putting it on Linux. Realistically Linux already has a full suite of administrative tools and some very powerful scripting languages […]
The post Lawrence’s List 081916 appeared first on Black Hills Information Security, Inc..
Lawrence Hoffmann // So, Apple announced a new bug bounty program at BlackHat, and there are some interesting deviations from the norm in their plan to implement and pay out. […]
The post Lawrence’s List 081216 appeared first on Black Hills Information Security, Inc..
Carrie Roberts // Answer: Enough to make it worth it! Penetration testers love to perform password spraying attacks against publicly available email portals as described here in this great post by Beau Bullock. […]
The post Question: What Can I Learn from Password Spraying a 2FA Microsoft Web App Portal? appeared first on Black Hills Information Security, Inc..
Editor’s Note: We’re excited to publish our first guest post! If you’d like to guest post on our blog DM us on Twitter, or use our contact form to contact us […]
The post Bitlocker Ransomware: Using BitLocker for Nefarious Reasons appeared first on Black Hills Information Security, Inc..