238,000 Impacted by Bell Ambulance Data Breach
Hackers stole personal information such as names, Social Security numbers, and driver’s license numbers.
The post 238,000 Impacted by Bell Ambulance Data Breach appeared first on SecurityWeek.
Hackers stole personal information such as names, Social Security numbers, and driver’s license numbers.
The post 238,000 Impacted by Bell Ambulance Data Breach appeared first on SecurityWeek.
The cybercriminals have leaked more than 300GB of files allegedly stolen from the tire giant.
The post Michelin Confirms Data Breach Linked to Oracle EBS Attack appeared first on SecurityWeek.
The Conduent data breach affects at least 25 million individuals, up from 10 million estimated a few months ago.
The post Conduent Breach Hits Volvo Group: Nearly 17,000 Employees’ Data Exposed appeared first on SecurityWeek.
Potential breach at Flickr exposes usernames, email addresses, IP addresses, and activity data.
The post Flickr Security Incident Tied to Third-Party Email System appeared first on SecurityWeek.
The hacker claims to have stolen nearly 700,000 Substack user records, including email addresses and phone numbers.
The post Substack Discloses Security Incident After Hacker Leaks Data appeared first on SecurityWeek.
ShinyHunters has claimed the theft of 14 million records from the US bakery-cafe chain’s systems.
The post Hackers Leak 5.1 Million Panera Bread Records appeared first on SecurityWeek.
Domains set up by the threat actor suggest attacks aimed at Atlassian, Canva, Epic Games, HubSpot, Moderna, ZoomInfo, and WeWork.
The post Over 100 Organizations Targeted in ShinyHunters Phishing Campaign appeared first on SecurityWeek.
Crunchbase was targeted alongside SoundCloud and Betterment in a ShinyHunters campaign.
The post Crunchbase Confirms Data Breach After Hacking Claims appeared first on SecurityWeek.
The WorldLeaks cybercrime group claims to have stolen information from the footwear and apparel giant’s systems.
The post Nike Probing Potential Security Incident as Hackers Threaten to Leak Data appeared first on SecurityWeek.
Under Armour is investigating a recent data breach that purloined customers’ email addresses and other personal information.
The post Under Armour Looking Into Data Breach Affecting Customers’ Email Addresses appeared first on SecurityWeek.
The compromised personal information includes names, dates of birth, Social Security numbers, and employment-related data.
The post 42,000 Impacted by Ingram Micro Ransomware Attack appeared first on SecurityWeek.
The incident impacted the personal information of CIRO member firms and their registered employees.
The post 750,000 Impacted by Data Breach at Canadian Investment Watchdog appeared first on SecurityWeek.
Hackers stole patients’ personal, treatment, and health insurance information from the organization’s IT systems.
The post Central Maine Healthcare Data Breach Impacts 145,000 Individuals appeared first on SecurityWeek.
Hackers stole the personal and reservation information of people with a Eurail pass and those who made a seat reservation with the company.
The post Traveler Information Stolen in Eurail Data Breach appeared first on SecurityWeek.
A threat actor breached Betterment’s systems, accessed customer information, and sent scam crypto-related messages.
The post Robo-Advisor Betterment Discloses Data Breach appeared first on SecurityWeek.
The law firm Fried Frank seems to be informing high-profile clients about a recent data security incident.
The post After Goldman, JPMorgan Discloses Law Firm Data Breach appeared first on SecurityWeek.
Hackers stole complete customer information, including contact details, national identity numbers, and payment details.
The post Spanish Energy Company Endesa Hacked appeared first on SecurityWeek.
After a recent data breach that affected Pornhub Premium members, Pornhub has updated its online statement to warn users about potential direct contact from cybercriminals.
“We are aware that the individuals responsible for this incident have threatened to contact impacted Pornhub Premium users directly. You may therefore receive emails claiming they have your personal information. As a reminder, we will never ask for your password or payment information by email.”
Pornhub is one of the world’s most visited adult video-sharing websites, allowing users to view content anonymously or create accounts to upload and interact with videos.
Pornhub has reported that on November 8, 2025, a security breach at third-party analytics provider Mixpanel exposed “a limited set of analytics events for certain users.” Pornhub stressed that this was not a breach of Pornhub’s own systems, and said that passwords, payment details, and financial information were not exposed.
Mixpanel confirmed it experienced a security incident on November 8, 2025, but disputes that the Pornhub data originated from that breach. The company stated there is:
“No indication that this data was stolen from Mixpanel during our November 2025 security incident or otherwise.”
Regardless of the source, cybercriminals commonly attempt to monetize stolen user data through direct extortion. At the moment, it is unclear how many users are affected, although available information suggests that only Premium members had their data exposed.
In October, we reported that one in six mobile users are targeted by sextortion scams. Sextortion is a form of online blackmail where criminals threaten to share a person’s private, nude, or sexually explicit images or videos unless the victim complies with their demands—often for more sexual content, sexual favors, or money.
Having your email address included in a dataset of known Pornhub users makes you a likely target for this type of blackmail.
Unless you used a dedicated throwaway email address to sign up for Pornhub Premium, you should be prepared to receive a sextortion-type email. If one arrives:
Use STOP, our simple scam response framework to help protect against scams.
Should you have doubts about the legitimacy of any communications, submit them to Malwarebytes Scam Guard. It will help you determine whether it’s a scam and provide advice on how to act.
We don’t just report on threats—we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your, and your family’s, personal information by using identity protection.
After a recent data breach that affected Pornhub Premium members, Pornhub has updated its online statement to warn users about potential direct contact from cybercriminals.
“We are aware that the individuals responsible for this incident have threatened to contact impacted Pornhub Premium users directly. You may therefore receive emails claiming they have your personal information. As a reminder, we will never ask for your password or payment information by email.”
Pornhub is one of the world’s most visited adult video-sharing websites, allowing users to view content anonymously or create accounts to upload and interact with videos.
Pornhub has reported that on November 8, 2025, a security breach at third-party analytics provider Mixpanel exposed “a limited set of analytics events for certain users.” Pornhub stressed that this was not a breach of Pornhub’s own systems, and said that passwords, payment details, and financial information were not exposed.
Mixpanel confirmed it experienced a security incident on November 8, 2025, but disputes that the Pornhub data originated from that breach. The company stated there is:
“No indication that this data was stolen from Mixpanel during our November 2025 security incident or otherwise.”
Regardless of the source, cybercriminals commonly attempt to monetize stolen user data through direct extortion. At the moment, it is unclear how many users are affected, although available information suggests that only Premium members had their data exposed.
In October, we reported that one in six mobile users are targeted by sextortion scams. Sextortion is a form of online blackmail where criminals threaten to share a person’s private, nude, or sexually explicit images or videos unless the victim complies with their demands—often for more sexual content, sexual favors, or money.
Having your email address included in a dataset of known Pornhub users makes you a likely target for this type of blackmail.
Unless you used a dedicated throwaway email address to sign up for Pornhub Premium, you should be prepared to receive a sextortion-type email. If one arrives:
Use STOP, our simple scam response framework to help protect against scams.
Should you have doubts about the legitimacy of any communications, submit them to Malwarebytes Scam Guard. It will help you determine whether it’s a scam and provide advice on how to act.
We don’t just report on threats—we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your, and your family’s, personal information by using identity protection.
South Korean law enforcement has arrested four suspects linked to the breach of approximately 120 000 IP cameras installed in private homes and commercial spaces — including karaoke lounges, pilates studios, and a gynecology clinic. Two of the hackers sold sexually explicit footage from the cameras through a foreign adult website. In this post, we explain what IP cameras are, and where their vulnerabilities lie. We also dive into the details of the South Korea incident and share practical advice on how to avoid becoming a target for attackers hunting for intimate video content.
An IP camera is a video camera connected to the internet via the Internet Protocol (IP), which lets you view its feed remotely on a smartphone or computer. Unlike traditional CCTV surveillance systems, these cameras don’t require a local surveillance hub — like you see in the movies — or even a dedicated computer to be plugged into. An IP camera streams video directly in real time to any device that connects to it over the internet. Most of today’s IP camera manufacturers also offer optional cloud storage plans, letting you access recorded footage from anywhere in the world.
In recent years, IP cameras have surged in popularity to become ubiquitous, serving a wide range of purposes — from monitoring kids and pets at home to securing warehouses, offices, short-term rental apartments (often illegally), and small businesses. Basic models can be picked up online for as little as US$25–40.
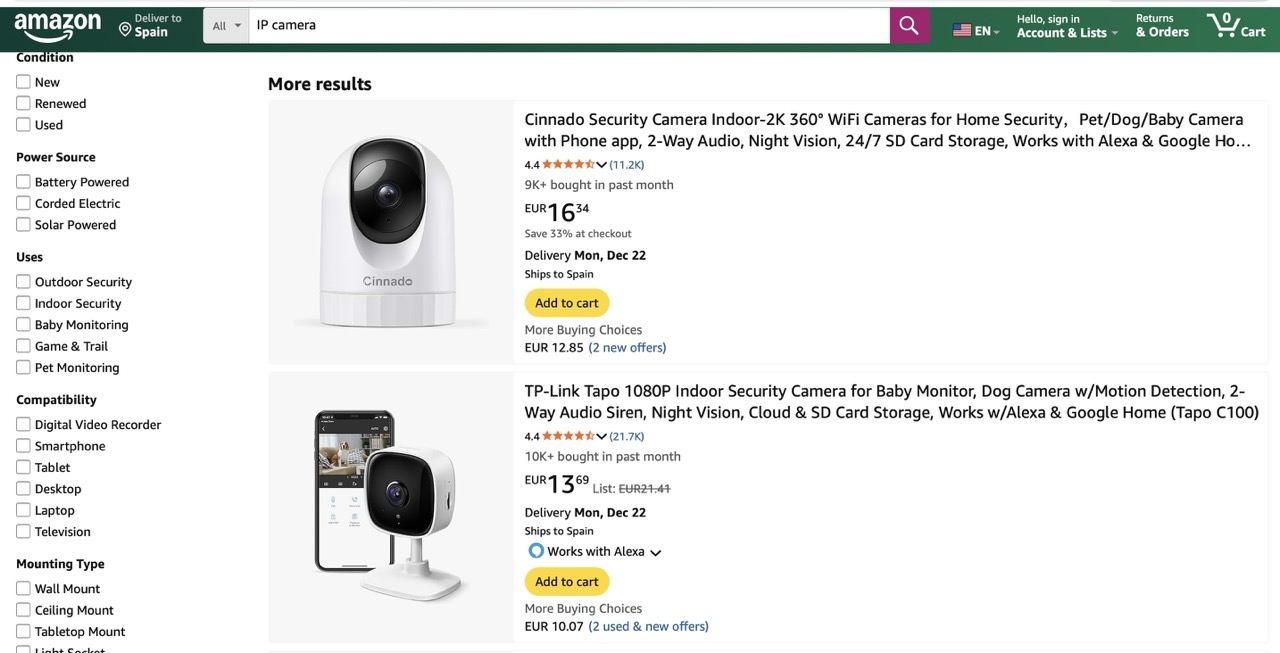
You can find a Full HD IP camera on an online marketplace for under US$25 — affordable prices have made them incredibly popular for both home and small business use
One of the defining features of IP cameras is that they’re originally designed for remote access. The camera connects to the internet and silently accepts incoming connections — ready to stream video to anyone who knows its address and has the password. And this leads to two common problems with these devices.
Let’s rewind to what unfolded this fall in South Korea. Law-enforcement authorities reported a breach of roughly 120 000 IP cameras, and the arrest of four suspects in connection with the attacks. Here’s what we know about each of them.
The astute reader may have noticed the numbers don’t quite add up — the figures above totaling well over 120 000. South Korean law enforcement hasn’t provided a clear explanation for this discrepancy. Journalists speculate that some of the devices may have been compromised by multiple attackers.
The investigation has revealed that only two of the accused actually sold the sexual content they’d stolen. However, the scale of their operation is staggering. Last year, the website hosting voyeurism and sexual exploitation content — which both perpetrators used to sell their videos — received 62% of its uploads from just these two individuals. In essence, this video enthusiast duo supplied the majority of the platform’s illegal content. It’s also been reported that three buyers of these videos were detained.
South Korean investigators were able to identify 58 specific locations of the hacked cameras. They’ve notified the victims and provided guidance on changing the passwords to secure their IP cameras. This suggests — although the investigators haven’t disclosed any details about the method of compromise — that the attackers used brute-forcing to crack the cameras’ simple passwords.
Another possibility is that the camera owners, as is often the case, simply never changed the default usernames and passwords. These default credentials are frequently widely known, so it’s entirely plausible that to gain access the attackers only needed to know the camera’s IP address and try a handful of common username and password combinations.
The takeaways from this whole South Korean dorama drama are straight from our playbook:
These rules are universal: they apply just as much to your social media and banking accounts as they do to your robot vacuums, IP cameras, and every other smart device in your home.
To keep all those unique passwords organized without losing your mind, we strongly recommend a reliable password manager. Kaspersky Password Manager can both store all your credentials securely and generate truly random, complex, and uncrackable passwords for you. With it, you can be confident that no one will guess the passwords to your accounts or devices. Plus, it helps you generate one-time codes for two-factor authentication, save and autofill passkeys, and sync your sensitive data — not just logins and passwords, but also bank card details, documents, and even private photos — in encrypted form across all your devices.
Wondering if a hidden camera is filming you? Read more in our posts:



