Normal view
Received an Instagram password reset email? Here’s what you need to know
Last week, many Instagram users began receiving unsolicited emails from the platform that warned about a password reset request.

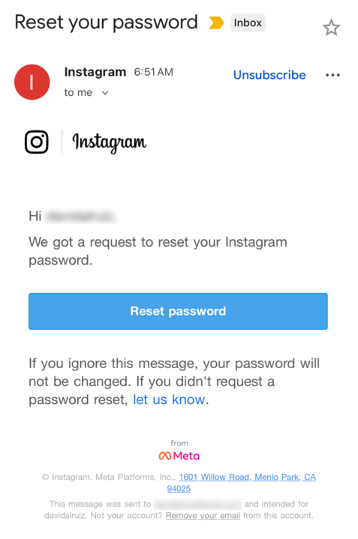
The message said:
“Hi {username},
We got a request to reset your Instagram password.
If you ignore this message, your password will not be changed. If you didn’t request a password reset, let us know.”
Around the same time that users began receiving these emails, a cybercriminal using the handle “Solonik” offered data that alleged contains information about 17 million Instagram users for sale on a Dark Web forum.

These 17 million or so records include:
- Usernames
- Full names
- User IDs
- Email addresses
- Phone numbers
- Countries
- Partial locations
Please note that there are no passwords listed in the data.
Despite the timing of the two events, Instagram denied this weekend that these events are related. On the platform X, the company stated they fixed an issue that allowed an external party to request password reset emails for “some people.”

So, what’s happening?
Regarding the data found on the dark web last week, Shahak Shalev, global head of scam and AI research at Malwarebytes, shared that “there are some indications that the Instagram data dump includes data from other, older, alleged Instagram breaches, and is a sort of compilation.” As Shalev’s team investigates the data, he also said that the earliest password reset requests reported by users came days before the data was first posted on the dark web, which might mean that “the data may have been circulating in more private groups before being made public.”
However, another possibility, Shalev said, is that “another vulnerability/data leak was happening as some bad actor tried spraying for [Instagram] accounts. Instagram’s announcement seems to reference that spraying. Besides the suspicious timing, there’s no clear connection between the two at this time.”
But, importantly, scammers will not care whether these incidents are related or not. They will try to take advantage of the situation by sending out fake emails.
“We felt it was important to alert people about the data availability so that everyone could reset their passwords, directly from the app, and be on alert for other phishing communications,” Shalev said.
If and when we find out more, we’ll keep you posted, so stay tuned.
How to stay safe
If you have enabled 2FA on your Instagram account, we think it is indeed safe to ignore the emails, as proposed by Meta.
Should you want to err on the safe side and decide to change your password, make sure to do so in the app and not click any links in the email, to avoid the risk that you have received a fake email. Or you might end up providing scammers with your password.
Another thing to keep in mind is that these are Meta-data. Which means some users may have reused or linked them to their Facebook or WhatsApp accounts. So, as a precaution, you can check recent logins and active sessions on Instagram, WhatsApp, and Facebook, and log out from any devices or locations you do not recognize.
If you want to find out whether your data was included in an Instagram data breach, or any other for that matter, try our free Digital Footprint scan.
Received an Instagram password reset email? Here’s what you need to know
Last week, many Instagram users began receiving unsolicited emails from the platform that warned about a password reset request.

The message said:
“Hi {username},
We got a request to reset your Instagram password.
If you ignore this message, your password will not be changed. If you didn’t request a password reset, let us know.”
Around the same time that users began receiving these emails, a cybercriminal using the handle “Solonik” offered data that alleged contains information about 17 million Instagram users for sale on a Dark Web forum.

These 17 million or so records include:
- Usernames
- Full names
- User IDs
- Email addresses
- Phone numbers
- Countries
- Partial locations
Please note that there are no passwords listed in the data.
Despite the timing of the two events, Instagram denied this weekend that these events are related. On the platform X, the company stated they fixed an issue that allowed an external party to request password reset emails for “some people.”

So, what’s happening?
Regarding the data found on the dark web last week, Shahak Shalev, global head of scam and AI research at Malwarebytes, shared that “there are some indications that the Instagram data dump includes data from other, older, alleged Instagram breaches, and is a sort of compilation.” As Shalev’s team investigates the data, he also said that the earliest password reset requests reported by users came days before the data was first posted on the dark web, which might mean that “the data may have been circulating in more private groups before being made public.”
However, another possibility, Shalev said, is that “another vulnerability/data leak was happening as some bad actor tried spraying for [Instagram] accounts. Instagram’s announcement seems to reference that spraying. Besides the suspicious timing, there’s no clear connection between the two at this time.”
But, importantly, scammers will not care whether these incidents are related or not. They will try to take advantage of the situation by sending out fake emails.
“We felt it was important to alert people about the data availability so that everyone could reset their passwords, directly from the app, and be on alert for other phishing communications,” Shalev said.
If and when we find out more, we’ll keep you posted, so stay tuned.
How to stay safe
If you have enabled 2FA on your Instagram account, we think it is indeed safe to ignore the emails, as proposed by Meta.
Should you want to err on the safe side and decide to change your password, make sure to do so in the app and not click any links in the email, to avoid the risk that you have received a fake email. Or you might end up providing scammers with your password.
Another thing to keep in mind is that these are Meta-data. Which means some users may have reused or linked them to their Facebook or WhatsApp accounts. So, as a precaution, you can check recent logins and active sessions on Instagram, WhatsApp, and Facebook, and log out from any devices or locations you do not recognize.
If you want to find out whether your data was included in an Instagram data breach, or any other for that matter, try our free Digital Footprint scan.
CISA orders feds to patch Gogs RCE flaw exploited in zero-day attacks
'Bad actor' hijacks Apex Legends characters in live matches
Meta sloot 1,6 procent van accounts op Facebook, Insta en Threads in Australië
Fable-bedenker Peter Molyneux brengt Masters of Albion in april uit
University of Hawaii Cancer Center hit by ransomware attack
Verbod op AI-diensten in WhatsApp gaat niet gelden in Italië
-
The Register – Security
- Businesses in 2026: Maybe we should finally look into that AI security stuff
Businesses in 2026: Maybe we should finally look into that AI security stuff
Survey finds security checks nearly doubled in a year as leaders wise up
The number of organizations that have implemented methods for identifying security risks in the AI tools they use has almost doubled in the space of a year.…
Reflecting on AI in 2025: Faster Attacks, Same Old Tradecraft

Activity-masking infostealer dropper | Kaspersky official blog
Our experts have detected a new wave of malicious emails targeting Russian private-sector organizations. The goal of the attack is to infect victims’ computers with an infostealer. This campaign is particularly noteworthy because the attackers tried to disguise their activity as the operations of legitimate software and traffic to the ubiquitously-used state and municipal services website.
How the attack begins
The attackers distribute an email containing a malicious attachment disguised as a regular PDF document. In reality, the file is an executable hiding behind a PDF icon; double-clicking it triggers an infection chain on the victim’s computer. In the campaign we analyzed, the malicious files were named УВЕДОМЛЕНИЕ о возбуждении исполнительного производства (NOTICE of Initiation of Enforcement Proceedings) and Дополнительные выплаты (Additional Payouts), though these are probably not the only document names the attackers employ to trick victims into clicking the files.
Technically, the file disguised as a document is a downloader built with the help of the .NET framework. It downloads a secondary loader that installs itself as a service to establish persistence on the victim’s machine. This other loader then retrieves a JSON string containing encrypted files from the command-and-control server. It saves these files to the compromised computer in C:\ProgramData\Microsoft Diagnostic\Tasks, and executes them one by one.
The key feature of this delivery method is its flexibility: the attackers can provide any malicious payload from the command-and-control server for the malware to download and execute. Presently, the attackers are using an infostealer as the final payload, but this attack could potentially be used to deliver even more dangerous threats – such as ransomware, wipers, or tools for deeper lateral movement within the victim’s infrastructure.
Masking malicious activity
The command-and-control server used to download the malicious payload in this attack was hosted on the domain gossuslugi{.}com. The name is visually similar to Russia’s widely used state and municipal services portal. Furthermore, the second-stage loader has the filename NetworkDiagnostic.exe, which installs itself in the system as a Network Diagnostic Service.
Consequently, an analyst doing only a superficial review of network traffic logs or system events might overlook the server communication and malware execution. This can also complicate any subsequent incident investigation efforts.
What the infostealer collects
The attackers start by gathering information about the compromised system: the computer name, OS version, hardware specifications, and the victim’s IP address. Additionally, the malware is capable of capturing screenshots from the victim’s computer, and harvesting files in formats of interest to the attackers (primarily various documents and archives). Files smaller than 100MB, along with the rest of the collected data, are sent to a separate communication server: ants-queen-dev.azurewebsites{.}net.
The final malicious payload currently in use consists of four files: one executable and three DLL libraries. The executable enables screen capture capabilities. One of the libraries is used to add the executable to startup, another is responsible for data collection, while the third handles data exfiltration.
During network communication, the malware adds an AuthKey header to its requests, which contains the victim’s operating system identifier.
How to stay safe
Our security solutions detect both the malicious code used in this attack and its communication with the attackers’ command-and-control servers. Therefore, we recommend using reliable security solutions on all devices used by your company to access the internet. And to prevent malicious emails from ever reaching your employees, we also advise deploying a security solution at the corporate email gateway level too.




-
Nationaal Cyber Security Centrum - Nieuwsberichten
- Subsidie voor mkb-bedrijven nog 1 maand beschikbaar
Subsidie voor mkb-bedrijven nog 1 maand beschikbaar
-
Nationaal Cyber Security Centrum - Nieuwsberichten
- Cyberweerbaarheidsnetwerk bouwplan voor stevigere basis van cyberweerbaarheid in het Koninkrijk der Nederlanden
Cyberweerbaarheidsnetwerk bouwplan voor stevigere basis van cyberweerbaarheid in het Koninkrijk der Nederlanden
-
Nationaal Cyber Security Centrum - Nieuwsberichten
- Nieuwe kwetsbaarheden in Citrix Netscaler ontdekt
Nieuwe kwetsbaarheden in Citrix Netscaler ontdekt
Casus: Citrix kwetsbaarheid (Update 13-08-2025)
-
Nationaal Cyber Security Centrum - Nieuwsberichten
- Informatie over kwetsbaarheden in Citrix NetScaler ADC en NetScaler Gateway
Informatie over kwetsbaarheden in Citrix NetScaler ADC en NetScaler Gateway
-
Nationaal Cyber Security Centrum - Nieuwsberichten
- Nederlandse organisaties opnieuw doelwit van DDoS-aanvallen
Nederlandse organisaties opnieuw doelwit van DDoS-aanvallen
-
Nationaal Cyber Security Centrum - Nieuwsberichten
- Update 04/08/2025: Naam NCSC misbruikt in phishingcampagne