Dynamic Device Code Phishing
![]()
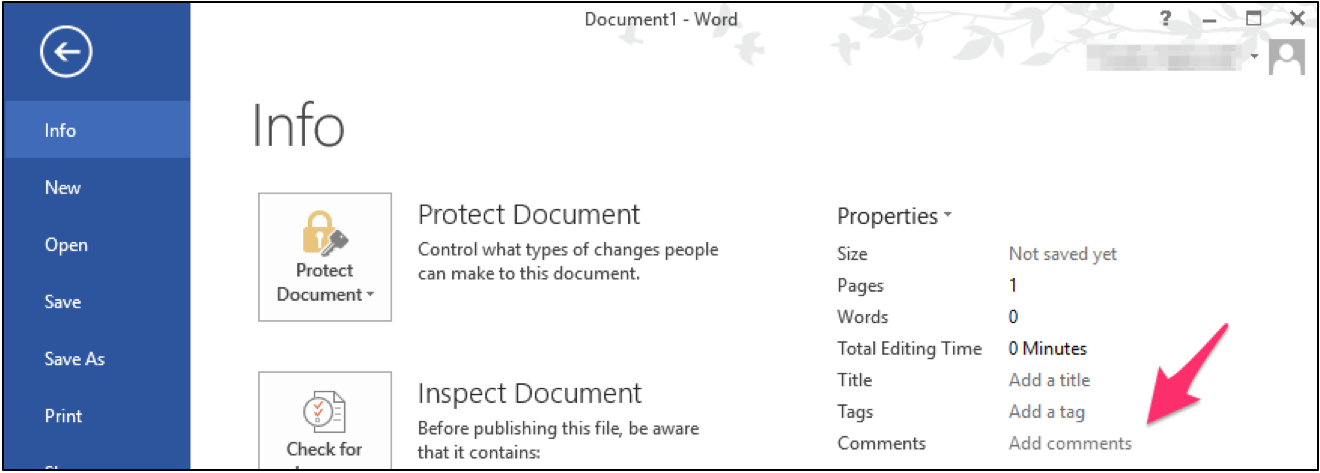
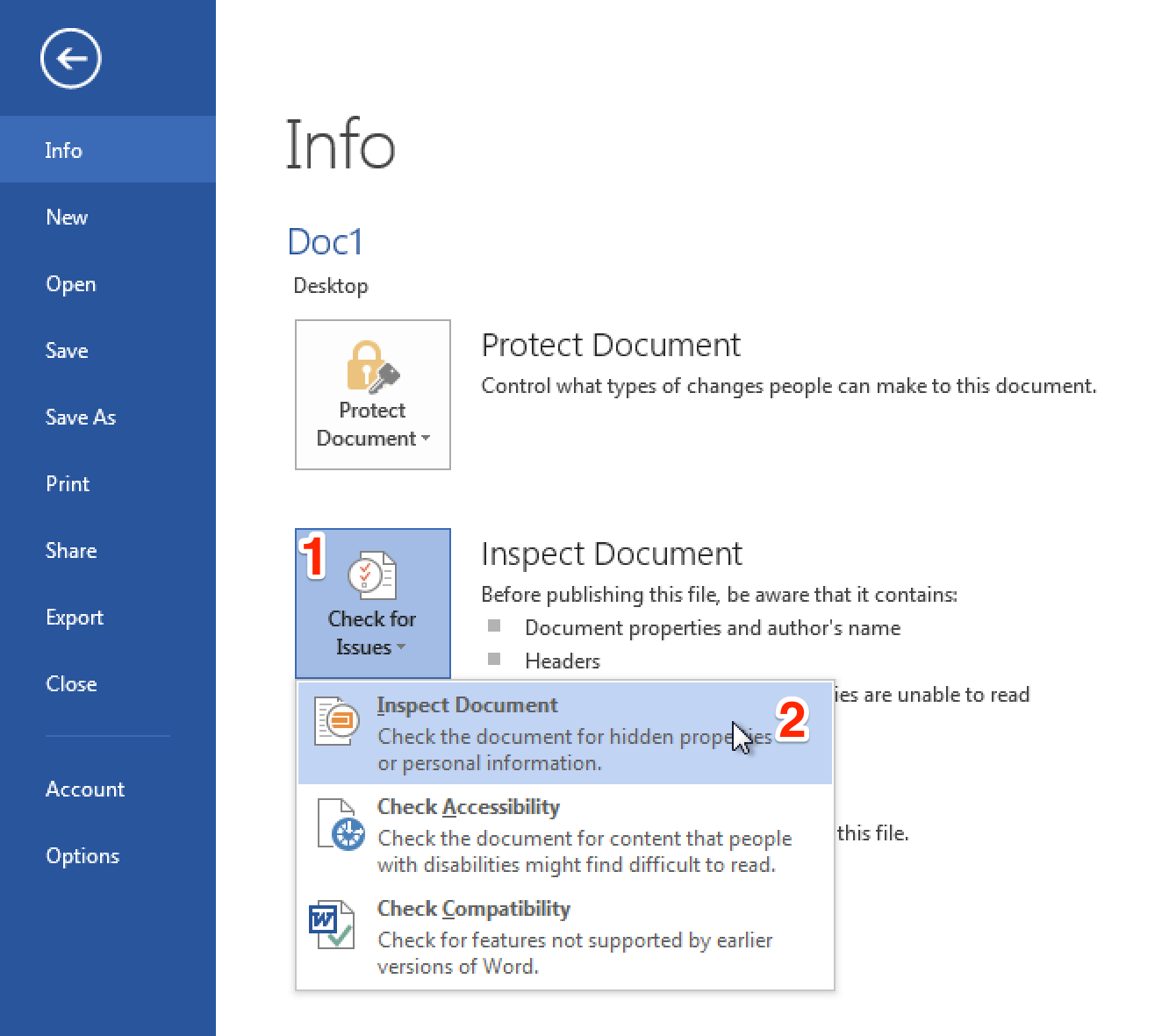
rvrsh3ll // Introduction This blog post is intended to give a light overview of device codes, access tokens, and refresh tokens. Here, I focus on the technical how-to for standing […]
The post Dynamic Device Code Phishing appeared first on Black Hills Information Security, Inc..