How the National Cyber Strategy Secures Our Digital Way of Life
A Pivotal Moment for National Security
As the digital landscape undergoes profound shifts, the recently released National Cyber Strategy provides the essential foundation for enduring American leadership. By prioritizing the disruption of hostile actors, future-proofing networks, accelerating quantum readiness, and securing the AI frontier, the strategy provides the strategic clarity necessary to protect our digital way of life from sophisticated adversaries. Palo Alto Networks commends National Cyber Director Sean Cairncross for his leadership and looks forward to working with the administration to operationalize this strategy.
Each pillar of the strategy galvanizes meaningful action to advance our collective defense:
Shape Adversary Behavior (Pillar 1)
This signals a decisive shift toward the proactive disruption of malicious actors. The Trump Administration has made clear that the U.S. Government should impose real costs on adversaries to change their behavior. While the private sector is already executing discrete disruptions against malicious actors, coordination has historically been fragmented. The strategy identifies that increased collaboration with private sector entities, who possess unique insight into adversary behavior, can in turn enable more impactful deterrence.
Promote Common Sense Regulation (Pillar 2)
The strategy appropriately recognizes that complexity is the enemy of security. A focus on measurable improvements in cyber outcomes (versus check-the-box compliance exercises) collectively makes us all safer. While much attention is rightfully paid toward harmonizing incident reporting requirements, which Palo Alto Networks wholeheartedly supports, let’s not stop there. The federal government can lead by example by consolidating and streamlining federal government software compliance certifications. For example, there should be logical reciprocity between FedRAMP High and DoW IL-5 certifications.
Modernize and Secure Federal Government Networks (Pillar 3)
In addition to the necessary attention on AI-powered cyber defense, cloud security and zero trust network architecture, Palo Alto Networks applauds the discrete focus on quantum-safe security ahead of “Q-Day,” the point where quantum computing capabilities will compromise legacy public key encryption that has underpinned cybersecurity for decades. As Federal CISO Mike Duffy recently stated, "Modernization without considering PQC readiness or cryptographic agility is really creating technical debt in the future, something that we don’t want to see ever.”
To address this challenge, Palo Alto Networks provides a structured quantum-safe framework organized into four stages:
- Continuous Discovery – Automating ecosystem ingestion to identify cryptographic dependencies.
- Risk Assessment & Prioritization – Evaluating vulnerabilities to establish a data-driven remediation roadmap.
- Comprehensive Remediation – Executing the transition to post-quantum algorithms across the architecture.
- Governance & Crypto-Hygiene – Maintaining long-term visibility and management.
The bottom line is that 2035 is too late. Quantum readiness must accelerate today, and this strategy will set a critical North Star to drive the necessary urgency.
Secure Critical Infrastructure (Pillar 4)
Critical infrastructure resilience is central to our homeland security, economic security, public health and safety. Unfortunately, critical infrastructure entities are increasingly under assault from emboldened cyber adversaries.
In fact, Palo Alto Networks research shows some form of operational disruption in up to 86% of major cyber incidents. Our 2026 Global Incident Response Report underscores another sobering reality: These entities are under assault from all angles. In 87% of cyber incidents, attacks targeted multiple attack surfaces, which spanned the network, cloud, endpoints and identity.
Recognizing that you can’t secure what you can’t see, we need a national-level effort to identify, prioritize and harden the critical infrastructure that the American people depend upon. This strategy puts an important marker in the ground to revitalize those efforts.
Sustain Superiority in Critical and Emerging Technologies (Pillar 5)
Palo Alto Networks was pleased to see the strategy reinforces the core tenets of the AI Action Plan, emphasizing that "secure-by-design" principles for AI technologies are non-negotiable and that AI adoption and AI security can and must be inexorably linked.
Enterprises should be able to deploy AI confidently without fear of data leakage, model tampering or rogue AI agents. However, despite our research showing an 88% success rate of “jailbreaking” techniques against widely deployed AI models, only 6% of organizations currently have an AI security strategy. It’s time to flip this paradigm and put defenders back in the driver’s seat in this AI-first moment.
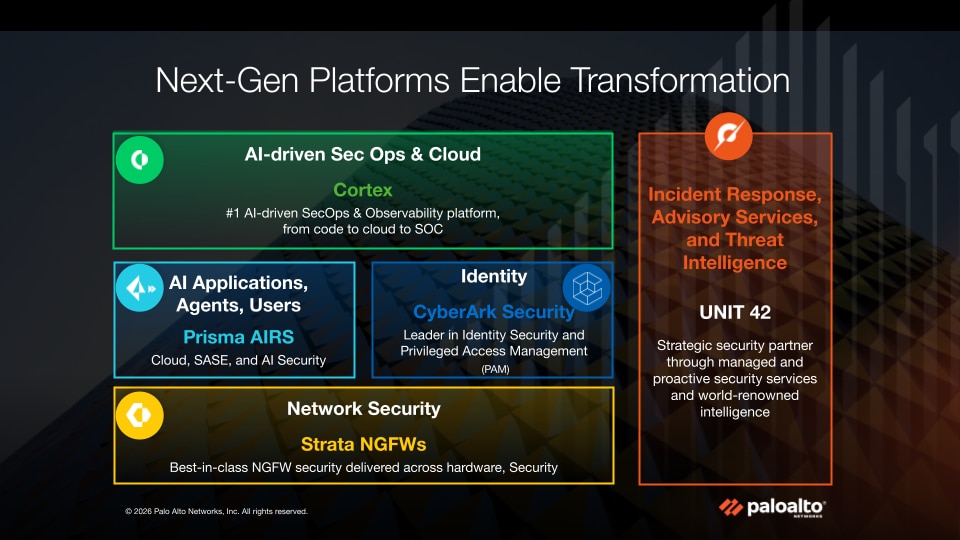
To support this emerging consensus around the importance of promoting AI security, we developed the Secure AI by Design Policy Roadmap. This framework provides a four-part construct to evaluate the evolving dimensions of threats to AI systems. Palo Alto Networks is also proud to make its comprehensive AI security suite, Prisma® AIRS , available to all federal agencies at substantial discounts through GSA’s OneGov Initiative.
, available to all federal agencies at substantial discounts through GSA’s OneGov Initiative.
Build Talent and Capacity (Pillar 6)
Recognizing America’s cyber workforce as a “strategic asset,” the strategy calls for a pragmatic and accessible pipeline for developing talent. The explicit recognition that we should take advantage of existing avenues across government, industry and academia is important. For example, Palo Alto Networks is proud of the impact of its Cybersecurity Academy – that provides free, NIST Framework-aligned curricula covering essential domains, such as cybersecurity fundamentals, enterprise and network security, cloud security, security operations and the AI/cybersecurity nexus.
Resources like this, and those for other entities, can form the basis of a renewed focus on cyber talent development.
Turning Strategic Vision Into Action
Palo Alto Networks views itself as more than a cybersecurity vendor. We see ourselves as an integrated national security partner of the federal government at a moment when defending our digital way of life demands all of us working together. To that end, we are ready to do our part to turn strategic vision into action.
This strategy should be applauded. Let’s roll up our sleeves and get to work.
The post How the National Cyber Strategy Secures Our Digital Way of Life appeared first on Palo Alto Networks Blog.