Nucleus Raises $20 Million for Exposure Management
The company will use the investment to scale operations and deepen intelligence and automation.
The post Nucleus Raises $20 Million for Exposure Management appeared first on SecurityWeek.
The company will use the investment to scale operations and deepen intelligence and automation.
The post Nucleus Raises $20 Million for Exposure Management appeared first on SecurityWeek.
In this post we explore the data-driven shrinkage of the Time to Exploit (TTE) window from 745 days to just 44, and examine why N-day vulnerabilities have become the “turn-key” weapon of choice for modern threat actors.

The race between defenders and threat actors has entered a new, more volatile phase: the rapidly accelerating exploitation of N-day vulnerabilities. Different from zero-days, N-day vulnerabilities are known security flaws that have been publicly disclosed but remain unpatched or unmitigated on an organization’s systems.
Historically, enterprises operated under the assumption of a “patching grace period,” the designated window of time allowed for a vendor to test and deploy a fix before a system is considered non-compliant or at high risk. However, this window is effectively collapsing, with Flashpoint finding that N-days now represent over 80% of all Known Exploited Vulnerabilities (KEVs) tracked over the past four years.
The most sobering trend for security operations (SecOps) and exposure management teams is the dramatic reduction in Time to Exploit (TTE). In 2020, the average TTE, the time between a vulnerability’s disclosure and its first observed exploitation, was 745 days. By 2025, Flashpoint found that this window has now plummeted to an average of just 44 days.
| 2025 | 2024 | 2023 | 2022 | 2021 | 2020 | |
| Average TTE | 44 | 115 | 296 | 405 | 518 | 745 |
This contraction represents a strategic shift in adversary tempo. Attackers are no longer waiting for complex, bespoke exploits; they are moving at breakneck speeds to weaponize public disclosures.
Adversaries have gained a significant advantage through the rapid weaponization of researcher-published Proof-of-Concept (PoC) code. When a fully functional exploit is released alongside a vulnerability disclosure, it becomes a “turn-key” solution for attackers. By combining these ready-made exploits with internet-wide scanning tools like Shodan or FOFA, even unsophisticated threat actors can conduct mass exploitation across large segments of the internet in hours.
A prime example of this path of least resistance approach was observed in the leaked internal chat logs of the BlackBasta ransomware group. Analysis revealed that of the 65 CVEs discussed by the group, 54 were already known KEVs. Rather than spending resources on original zero-day research, threat actors are simply leveraging known, yet unpatched and exploitable vulnerabilities for their campaigns.
The very software designed to protect enterprise firewalls, VPN gateways, and edge networking devices is consistently the most targeted category for both N-day and zero-day exploitation.
Because cybersecurity devices must be internet-facing to function, they provide a constant, unauthenticated attack surface. In 2025 alone, Flashpoint observed 37 N-days and 52 zero-days specifically targeting security and perimeter software. The requirement for these systems to remain open to external traffic means they will continue to be disproportionately targeted by advanced persistent threat (APT) groups and cybercriminals alike.
While tracking the “how” of an attack is critical, tracking who is responsible remains a fragmented challenge for the industry. Attribution is often hampered by naming fatigue, where different vendors assign their own designated unique monikers to the same actor. For instance, the widely known threat actor group Lazarus has over 40 distinct designations across the industry, including “Diamond Sleet,” “NICKEL ACADEMY,” and “Guardians of Peace”.
Despite these naming complexities, global activity patterns remain clear. China remains the most active nation-state actor in the vulnerability exploitation space, consistently outpacing Russia, Iran, and North Korea in both the volume and scope of their campaigns.
Why are organizations struggling to keep pace? The primary factor isn’t a lack of effort, but a lack of visibility.
The single greatest breakthrough an enterprise can achieve is not a new AI tool, but a complete asset inventory. Most large organizations are lucky to have an accurate inventory of even 25% of their total assets. Without knowing what you own, vulnerability scans can take days or weeks to return results that the adversary is already using to probe your network.
Most traditional security tools are CVE-dependent. However, thousands of vulnerabilities are disclosed every year that never receive an official CVE ID. These “missing” vulnerabilities represent a massive blindspot for standard scanners. Intelligence-led exposure management requires looking beyond the CVE ecosystem into proprietary databases like Flashpoint’s VulnDB , which tracks over 105,000 vulnerabilities that public sources miss.
, which tracks over 105,000 vulnerabilities that public sources miss.
To survive in an era where weaponization can happen in under 24 hours, organizations must shift from reactive patching to a threat-informed and proactive security approach. This means:
The goal of exposure management is to look at your organization through the adversary’s lens. By understanding which N-days threat actors are actually discussing and weaponizing in the wild, defenders can finally start to close the window of exposure before a potential compromise can occur.
Flashpoint’s vulnerability threat intelligence can help your organization go from reactive to proactive. Request a demo today and gain access to quality vulnerability intelligence that enables intelligence-led exposure management.
The post N-Day Vulnerability Trends: The Shrinking Window of Exposure and the Rise of “Turn-Key” Exploitation appeared first on Flashpoint.
This latest infusion, led by SYN Ventures, brings the company’s total funding to $16.9 million.
The post Nullify Secures $12.5 Million in Seed Funding for Cybersecurity AI Workforce appeared first on SecurityWeek.
The company will use the latest capital to scale its go-to-market efforts and expand its platform’s capabilities.
The post RapidFort Raises $42M to Automate Software Supply Chain Security appeared first on SecurityWeek.
Aisy has emerged from stealth mode with $2.3 million in seed funding for its AI-assisted platform.
The post Aisy Launches Out of Stealth to Transform Vulnerability Management appeared first on SecurityWeek.
Anticipate, contextualize, and prioritize vulnerabilities to effectively address threats to your organization.


Flashpoint’s VulnDB documents over 400,000 vulnerabilities and has over 6,000 entries in Flashpoint’s KEV database, making it a critical resource as vulnerability exploitation rises. However, if your organization is relying solely on CVE data, you may be missing critical vulnerability metadata and insights that hinder timely remediation. That’s why we created this weekly series—where we surface and analyze the most high priority vulnerabilities security teams need to know about.
documents over 400,000 vulnerabilities and has over 6,000 entries in Flashpoint’s KEV database, making it a critical resource as vulnerability exploitation rises. However, if your organization is relying solely on CVE data, you may be missing critical vulnerability metadata and insights that hinder timely remediation. That’s why we created this weekly series—where we surface and analyze the most high priority vulnerabilities security teams need to know about.
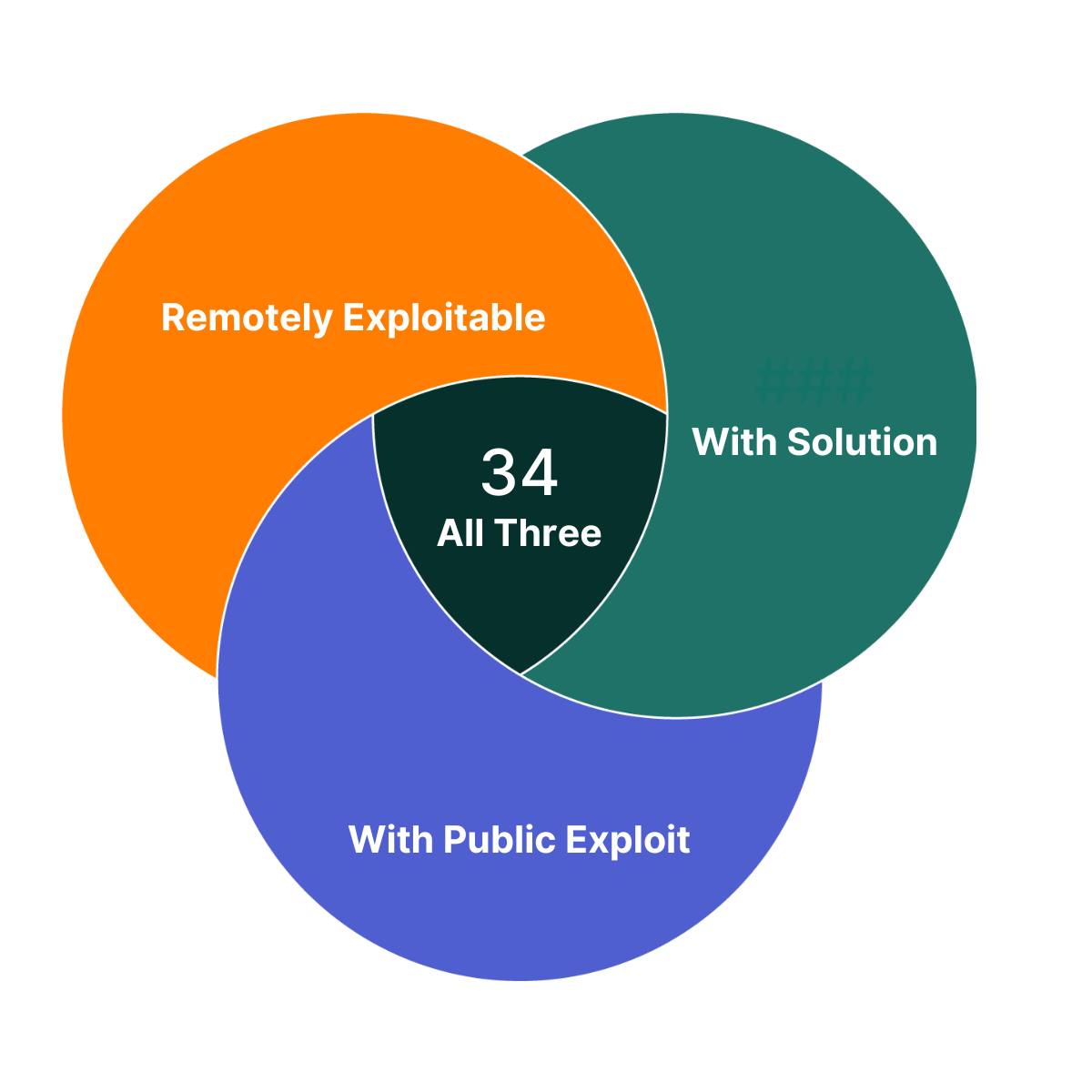
Of the vulnerabilities Flashpoint published this week, there are 34 that you can take immediate action on. They each have a solution, a public exploit exists, and are remotely exploitable. As such, these vulnerabilities are a great place to begin your prioritization efforts.
Of the vulnerabilities Flashpoint published last week, four are highlighted in this week’s Vulnerability Insights and Prioritization Report because they contain one or more of the following criteria:
In addition, all of these vulnerabilities are easily discoverable and therefore should be investigated and fixed immediately.
To proactively address these vulnerabilities and ensure comprehensive coverage beyond publicly available sources on an ongoing basis, organizations can leverage Flashpoint Vulnerability Intelligence. Flashpoint provides comprehensive coverage encompassing IT, OT, IoT, CoTs, and open-source libraries and dependencies. It catalogs over 100,000 vulnerabilities that are not included in the NVD or lack a CVE ID, ensuring thorough coverage beyond publicly available sources. The vulnerabilities that are not covered by the NVD do not yet have CVE ID assigned and will be noted with a VulnDB ID.
| CVE ID | Title | CVSS Scores (v2, v3, v4) | Exploit Status | Exploit Consequence | Ransomware Likelihood Score | Social Risk Score | Solution Availability |
| CVE-2025-33222 | NVIDIA Isaac Launchable Unspecified Hardcoded Credentials | 5.0 9.8 9.3 | Private | Credential Disclosure | High | Low | Yes |
| CVE-2025-33223 | NVIDIA Isaac Launchable Unspecified Improper Execution Privileges Remote Code Execution | 10.0 9.8 9.3 | Private | Remote Code Execution | High | Low | Yes |
| CVE-2025-68613 | n8n Package for Node.js packages/workflow/src/expression-evaluator-proxy.ts Workflow Expression Evaluation Remote Code Execution | 9.0 9.9 9.4 | Public | Remote Code Execution | High | High | Yes |
| CVE-2025-14847 | MongoDB transport/message_compressor_zlib.cpp ZlibMessageCompressor::decompressData() Function Zlib Compressed Protocol Header Handling Remote Uninitialized Memory Disclosure (Mongobleed) | 10.0 9.8 9.3 | Public | Uninitialized Memory Disclosure | High | High | Yes |
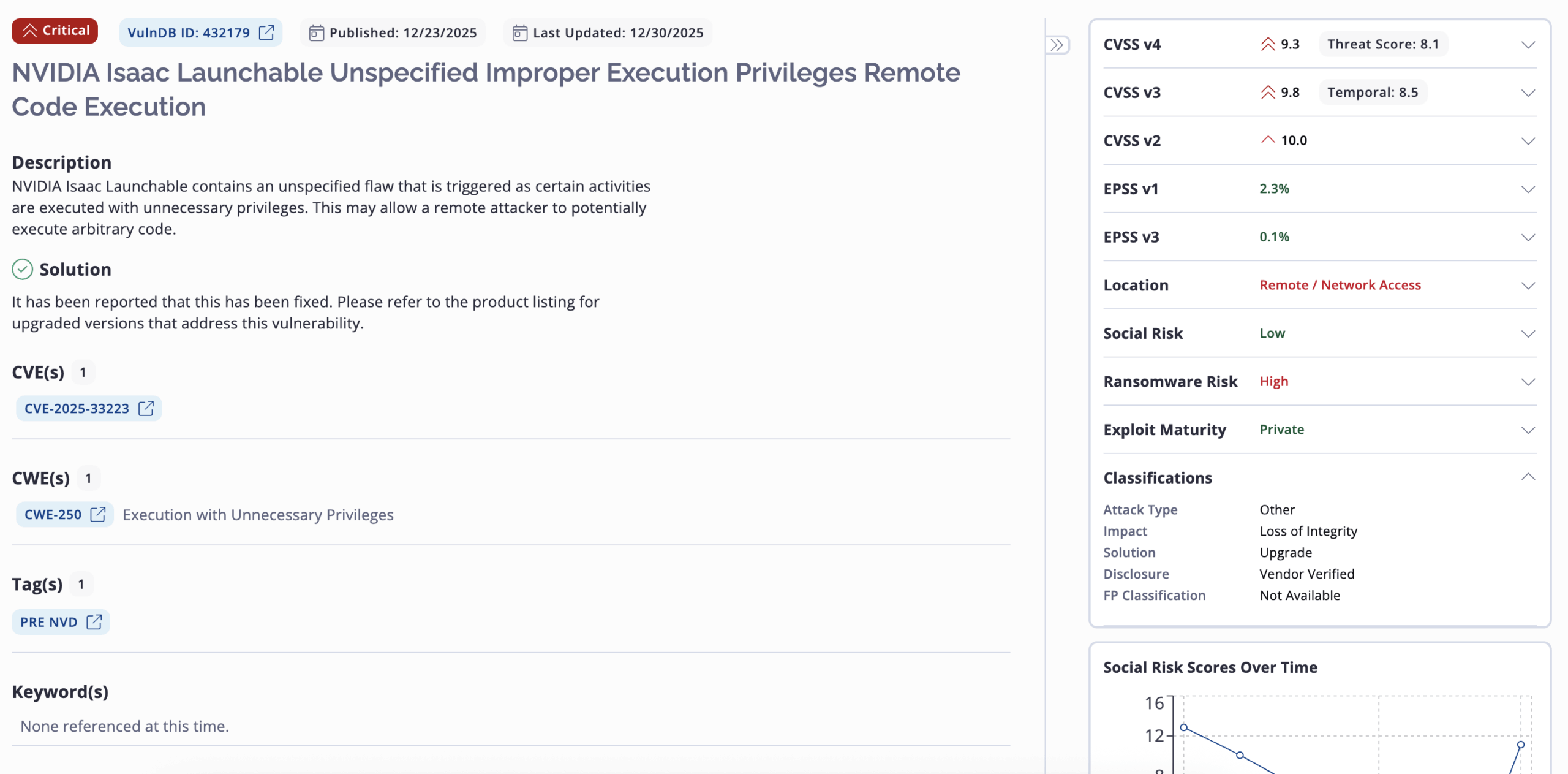
Flashpoint Ignite lays all of these components out. Below is an example of what this vulnerability record for CVE-2025-33223 looks like.
Below, Flashpoint analysts describe the five vulnerabilities highlighted above as vulnerabilities that should be of focus for remediation if your organization is exposed.
NVIDIA Isaac Launchable contains a flaw that is triggered by the use of unspecified hardcoded credentials. This may allow a remote attacker to trivially gain privileged access to the program.
NVIDIA Isaac Launchable contains an unspecified flaw that is triggered as certain activities are executed with unnecessary privileges. This may allow a remote attacker to potentially execute arbitrary code.
n8n Package for Node.js contains a flaw in packages/workflow/src/expression-evaluator-proxy.ts that is triggered as workflow expressions are evaluated in an improperly isolated execution context. This may allow an authenticated, remote attacker to execute arbitrary code with the privileges of the n8n process.
MongoDB contains a flaw in the ZlibMessageCompressor::decompressData() function in mongo/transport/message_compressor_zlib.cpp that is triggered when handling mismatched length fields in Zlib compressed protocol headers. This may allow a remote attacker to disclose uninitialized memory contents on the heap.
| CVE/VulnDB ID | Flashpoint Published Date |
| CVE-2025-21218 | Week of January 15, 2025 |
| CVE-2024-57811 | Week of January 15, 2025 |
| CVE-2024-55591 | Week of January 15, 2025 |
| CVE-2025-23006 | Week of January 22, 2025 |
| CVE-2025-20156 | Week of January 22, 2025 |
| CVE-2024-50664 | Week of January 22, 2025 |
| CVE-2025-24085 | Week of January 29, 2025 |
| CVE-2024-40890 | Week of January 29, 2025 |
| CVE-2024-40891 | Week of January 29, 2025 |
| VulnDB ID: 389414 | Week of January 29, 2025 |
| CVE-2025-25181 | Week of February 5, 2025 |
| CVE-2024-40890 | Week of February 5, 2025 |
| CVE-2024-40891 | Week of February 5, 2025 |
| CVE-2024-8266 | Week of February 12, 2025 |
| CVE-2025-0108 | Week of February 12, 2025 |
| CVE-2025-24472 | Week of February 12, 2025 |
| CVE-2025-21355 | Week of February 24, 2025 |
| CVE-2025-26613 | Week of February 24, 2025 |
| CVE-2024-13789 | Week of February 24, 2025 |
| CVE-2025-1539 | Week of February 24, 2025 |
| CVE-2025-27364 | Week of March 3, 2025 |
| CVE-2025-27140 | Week of March 3, 2025 |
| CVE-2025-27135 | Week of March 3, 2025 |
| CVE-2024-8420 | Week of March 3, 2025 |
| CVE-2024-56196 | Week of March 10, 2025 |
| CVE-2025-27554 | Week of March 10, 2025 |
| CVE-2025-22224 | Week of March 10, 2025 |
| CVE-2025-1393 | Week of March 10, 2025 |
| CVE-2025-24201 | Week of March 17, 2025 |
| CVE-2025-27363 | Week of March 17, 2025 |
| CVE-2025-2000 | Week of March 17, 2025 |
| CVE-2025-27636 CVE-2025-29891 | Week of March 17, 2025 |
| CVE-2025-1496 | Week of March 24, 2025 |
| CVE-2025-27781 | Week of March 24, 2025 |
| CVE-2025-29913 | Week of March 24, 2025 |
| CVE-2025-2746 | Week of March 24, 2025 |
| CVE-2025-29927 | Week of March 24, 2025 |
| CVE-2025-1974 CVE-2025-2787 | Week of March 31, 2025 |
| CVE-2025-30259 | Week of March 31, 2025 |
| CVE-2025-2783 | Week of March 31, 2025 |
| CVE-2025-30216 | Week of March 31, 2025 |
| CVE-2025-22457 | Week of April 2, 2025 |
| CVE-2025-2071 | Week of April 2, 2025 |
| CVE-2025-30356 | Week of April 2, 2025 |
| CVE-2025-3015 | Week of April 2, 2025 |
| CVE-2025-31129 | Week of April 2, 2025 |
| CVE-2025-3248 | Week of April 7, 2025 |
| CVE-2025-27797 | Week of April 7, 2025 |
| CVE-2025-27690 | Week of April 7, 2025 |
| CVE-2025-32375 | Week of April 7, 2025 |
| VulnDB ID: 398725 | Week of April 7, 2025 |
| CVE-2025-32433 | Week of April 12, 2025 |
| CVE-2025-1980 | Week of April 12, 2025 |
| CVE-2025-32068 | Week of April 12, 2025 |
| CVE-2025-31201 | Week of April 12, 2025 |
| CVE-2025-3495 | Week of April 12, 2025 |
| CVE-2025-31324 | Week of April 17, 2025 |
| CVE-2025-42599 | Week of April 17, 2025 |
| CVE-2025-32445 | Week of April 17, 2025 |
| VulnDB ID: 400516 | Week of April 17, 2025 |
| CVE-2025-22372 | Week of April 17, 2025 |
| CVE-2025-32432 | Week of April 29, 2025 |
| CVE-2025-24522 | Week of April 29, 2025 |
| CVE-2025-46348 | Week of April 29, 2025 |
| CVE-2025-43858 | Week of April 29, 2025 |
| CVE-2025-32444 | Week of April 29, 2025 |
| CVE-2025-20188 | Week of May 3, 2025 |
| CVE-2025-29972 | Week of May 3, 2025 |
| CVE-2025-32819 | Week of May 3, 2025 |
| CVE-2025-27007 | Week of May 3, 2025 |
| VulnDB ID: 402907 | Week of May 3, 2025 |
| VulnDB ID: 405228 | Week of May 17, 2025 |
| CVE-2025-47277 | Week of May 17, 2025 |
| CVE-2025-34027 | Week of May 17, 2025 |
| CVE-2025-47646 | Week of May 17, 2025 |
| VulnDB ID: 405269 | Week of May 17, 2025 |
| VulnDB ID: 406046 | Week of May 19, 2025 |
| CVE-2025-48926 | Week of May 19, 2025 |
| CVE-2025-47282 | Week of May 19, 2025 |
| CVE-2025-48054 | Week of May 19, 2025 |
| CVE-2025-41651 | Week of May 19, 2025 |
| CVE-2025-20289 | Week of June 3, 2025 |
| CVE-2025-5597 | Week of June 3, 2025 |
| CVE-2025-20674 | Week of June 3, 2025 |
| CVE-2025-5622 | Week of June 3, 2025 |
| CVE-2025-5419 | Week of June 3, 2025 |
| CVE-2025-33053 | Week of June 7, 2025 |
| CVE-2025-5353 | Week of June 7, 2025 |
| CVE-2025-22455 | Week of June 7, 2025 |
| CVE-2025-43200 | Week of June 7, 2025 |
| CVE-2025-27819 | Week of June 7, 2025 |
| CVE-2025-49132 | Week of June 13, 2025 |
| CVE-2025-49136 | Week of June 13, 2025 |
| CVE-2025-50201 | Week of June 13, 2025 |
| CVE-2025-49125 | Week of June 13, 2025 |
| CVE-2025-24288 | Week of June 13, 2025 |
| CVE-2025-6543 | Week of June 21, 2025 |
| CVE-2025-3699 | Week of June 21, 2025 |
| CVE-2025-34046 | Week of June 21, 2025 |
| CVE-2025-34036 | Week of June 21, 2025 |
| CVE-2025-34044 | Week of June 21, 2025 |
| CVE-2025-7503 | Week of July 12, 2025 |
| CVE-2025-6558 | Week of July 12, 2025 |
| VulnDB ID: 411705 | Week of July 12, 2025 |
| VulnDB ID: 411704 | Week of July 12, 2025 |
| CVE-2025-6222 | Week of July 12, 2025 |
| CVE-2025-54309 | Week of July 18, 2025 |
| CVE-2025-53771 | Week of July 18, 2025 |
| CVE-2025-53770 | Week of July 18, 2025 |
| CVE-2025-54122 | Week of July 18, 2025 |
| CVE-2025-52166 | Week of July 18, 2025 |
| CVE-2025-53942 | Week of July 25, 2025 |
| CVE-2025-46811 | Week of July 25, 2025 |
| CVE-2025-52452 | Week of July 25, 2025 |
| CVE-2025-41680 | Week of July 25, 2025 |
| CVE-2025-34143 | Week of July 25, 2025 |
| CVE-2025-50454 | Week of August 1, 2025 |
| CVE-2025-8875 | Week of August 1, 2025 |
| CVE-2025-8876 | Week of August 1, 2025 |
| CVE-2025-55150 | Week of August 1, 2025 |
| CVE-2025-25256 | Week of August 1, 2025 |
| CVE-2025-43300 | Week of August 16, 2025 |
| CVE-2025-34153 | Week of August 16, 2025 |
| CVE-2025-48148 | Week of August 16, 2025 |
| VulnDB ID: 416058 | Week of August 16, 2025 |
| CVE-2025-32992 | Week of August 16, 2025 |
| CVE-2025-7775 | Week of August 24, 2025 |
| CVE-2025-8424 | Week of August 24, 2025 |
| CVE-2025-34159 | Week of August 24, 2025 |
| CVE-2025-57819 | Week of August 24, 2025 |
| CVE-2025-7426 | Week of August 24, 2025 |
| CVE-2025-58367 | Week of September 1, 2025 |
| CVE-2025-58159 | Week of September 1, 2025 |
| CVE-2025-58048 | Week of September 1, 2025 |
| CVE-2025-39247 | Week of September 1, 2025 |
| CVE-2025-8857 | Week of September 1, 2025 |
| CVE-2025-58321 | Week of September 8, 2025 |
| CVE-2025-58366 | Week of September 8, 2025 |
| CVE-2025-58371 | Week of September 8, 2025 |
| CVE-2025-55728 | Week of September 8, 2025 |
| CVE-2025-55190 | Week of September 8, 2025 |
| VulnDB ID: 419253 | Week of September 13, 2025 |
| CVE-2025-10035 | Week of September 13, 2025 |
| CVE-2025-59346 | Week of September 13, 2025 |
| CVE-2025-55727 | Week of September 13, 2025 |
| CVE-2025-10159 | Week of September 13, 2025 |
| CVE-2025-20363 | Week of September 20, 2025 |
| CVE-2025-20333 | Week of September 20, 2025 |
| CVE-2022-4980 | Week of September 20, 2025 |
| VulnDB ID: 420451 | Week of September 20, 2025 |
| CVE-2025-9900 | Week of September 20, 2025 |
| CVE-2025-52906 | Week of September 27, 2025 |
| CVE-2025-51495 | Week of September 27, 2025 |
| CVE-2025-27224 | Week of September 27, 2025 |
| CVE-2025-27223 | Week of September 27, 2025 |
| CVE-2025-54875 | Week of September 27, 2025 |
| CVE-2025-41244 | Week of September 27, 2025 |
| CVE-2025-61928 | Week of October 6, 2025 |
| CVE-2025-61882 | Week of October 6, 2025 |
| CVE-2025-49844 | Week of October 6 2025 |
| CVE-2025-57870 | Week of October 6, 2025 |
| CVE-2025-34224 | Week of October 6, 2025 |
| CVE-2025-34222 | Week of October 6, 2025 |
| CVE-2025-40765 | Week of October 11, 2025 |
| CVE-2025-59230 | Week of October 11, 2025 |
| CVE-2025-24990 | Week of October 11, 2025 |
| CVE-2025-61884 | Week of October 11, 2025 |
| CVE-2025-41430 | Week of October 11, 2025 |
| VulnDB ID: 424051 | Week of October 18, 2025 |
| CVE-2025-62645 | Week of October 18, 2025 |
| CVE-2025-61932 | Week of October 18, 2025 |
| CVE-2025-59503 | Week of October 18, 2025 |
| CVE-2025-43995 | Week of October 18, 2025 |
| CVE-2025-62168 | Week of October 18, 2025 |
| VulnDB ID: 425182 | Week of October 25, 2025 |
| CVE-2025-62713 | Week of October 25, 2025 |
| CVE-2025-54964 | Week of October 25, 2025 |
| CVE-2024-58274 | Week of October 25, 2025 |
| CVE-2025-41723 | Week of October 25, 2025 |
| CVE-2025-20354 | Week of November 1, 2025 |
| CVE-2025-11953 | Week of November 1, 2025 |
| CVE-2025-60854 | Week of November 1, 2025 |
| CVE-2025-64095 | Week of November 1, 2025 |
| CVE-2025-11833 | Week of November 1, 2025 |
| CVE-2025-64446 | Week of November 8, 2025 |
| CVE-2025-36250 | Week of November 8, 2025 |
| CVE-2025-64400 | Week of November 8, 2025 |
| CVE-2025-12686 | Week of November 8, 2025 |
| CVE-2025-59118 | Week of November 8, 2025 |
| VulnDB ID: 426231 | Week of November 8, 2025 |
| VulnDB ID: 427979 | Week of November 22, 2025 |
| CVE-2025-55796 | Week of November 22, 2025 |
| CVE-2025-64428 | Week of November 22, 2025 |
| CVE-2025-62703 | Week of November 22, 2025 |
| VulnDB ID: 428193 | Week of November 22, 2025 |
| CVE-2025-65018 | Week of November 22, 2025 |
| CVE-2025-54347 | Week of November 22, 2025 |
| CVE-2025-55182 | Week of November 29, 2025 |
| CVE-2024-14007 | Week of November 29, 2025 |
| CVE-2025-66399 | Week of November 29, 2025 |
| CVE-2022-35420 | Week of November 29, 2025 |
| CVE-2025-66516 | Week of November 29, 2025 |
| CVE-2025-59366 | Week of November 29, 2025 |
| CVE-2025-14174 | Week of December 6, 2026 |
| CVE-2025-43529 | Week of December 6, 2026 |
| CVE-2025-8110 | Week of December 6, 2026 |
| CVE-2025-59719 | Week of December 6, 2026 |
| CVE-2025-59718 | Week of December 6, 2026 |
| CVE-2025-14087 | Week of December 6, 2026 |
| CVE-2025-62221 | Week of December 6, 2026 |
Request a demo today to see how Flashpoint can transform your vulnerability intelligence, vulnerability management, and exposure identification program.
CVE-2025-55182 (VulnDB ID: 428930), is a severe, unauthenticated RCE impacting a major component of React and its ecosystem, putting global applications at immediate, high-fidelity risk.
The React team disclosed a critical vulnerability impacting three products in the React Server Components (RSC) that allows for unauthenticated remote code execution.
Flashpoint’s vulnerability research team assesses significant enterprise and supply chain risk given React’s ubiquity: the impacted JavaScript library underpins modern UIs, with 168,640 dependents and more than 51 million weekly downloads.
CVE-2025-55182 (VulnDB ID: 428930) impacts all React versions since 19.0.0, meaning that this issue has been potentially exploitable since November 14, 2024. This vulnerability stems from how React handles payloads sent to React Server Function endpoints and deserializes them.
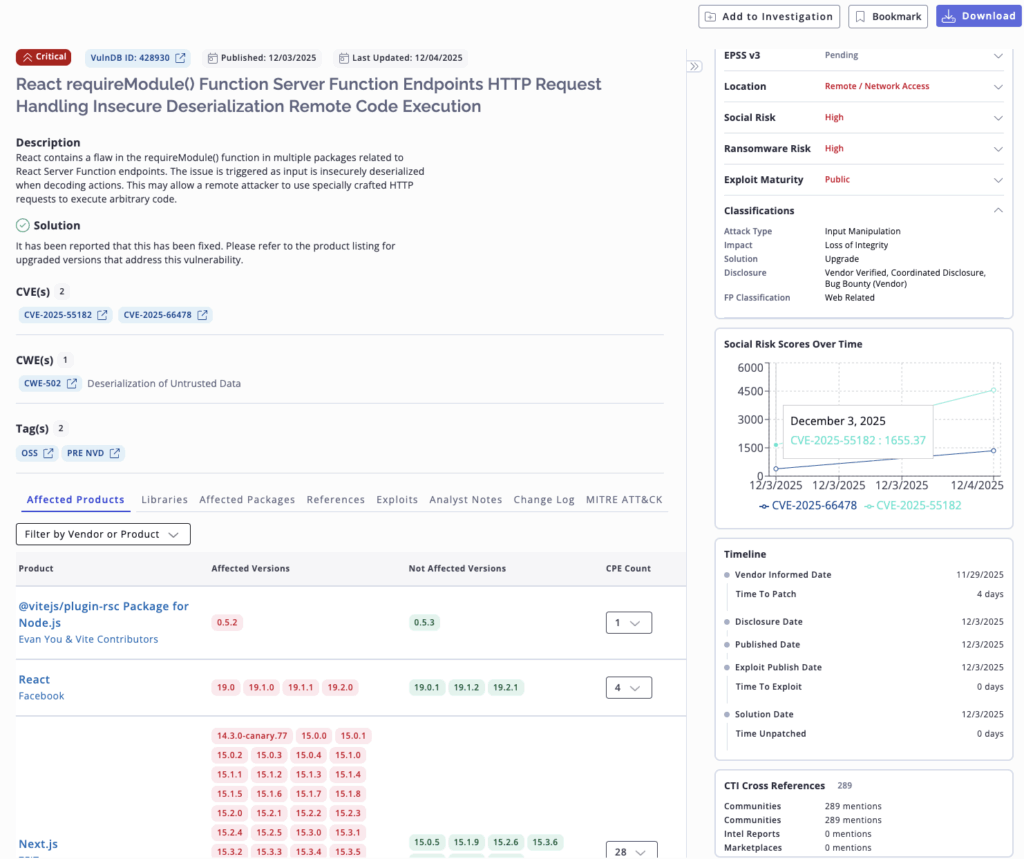
Depending on the implementation of this library, a remote, unauthenticated threat actor could send a crafted payload that would be deserialized in a way that causes remote code execution. This would lead to a total compromise of the system hosting the application, allowing for malware such as infostealers, ransomware, or cryptojackers (cryptocurrency mining) to be downloaded.
A working exploit for CVE-2025-55182 has already been published that is effective against some installations. In addition, Amazon has reported that two threat actors, attributed to Chinese Advanced Persistent Threat Groups (APTs), have begun to exploit this vulnerability. Those groups are:
It is critical that security teams fully understand the potential downstream scope and impact so that they can fully focus on mitigation, rather than time-consuming research. While the vendor has provided a full disclosure, there are several important caveats to understand about CVE-2025-55182:
Additionally, several React frameworks and bundlers have been discovered to leverage vulnerable React packages in various ways. The following frameworks and bundlers are known to be affected:
NPMJS.com currently shows that the react-dom package, which is effectively part of React, has 168,640 dependents. This means that an incredible number of enterprise applications are likely to be affected. Nearly every commercial application is built on hundreds, sometimes thousands of components and dependencies. Furthermore, applications coded via Vibe and similar technology are also likely to leverage React: potentially amplifying the downstream risk this vulnerability poses.
For mitigation, the React library has released versions 19.0.1, 19.1.2, and 19.2.1 that resolve the issue. Flashpoint advises organizations to upgrade their respective libraries urgently. Security teams leveraging dynamic SBOMs (Software Bill of Materials) can drastically increase risk mapping and triage for deployed React versions.
CloudFlare has upgraded their web-application firewall (WAF) to protect against CVE-2025-55182. It is available for both free and paid plans but requires that React application traffic is proxied through the CloudFlare WAF.
To avoid confusion, security teams should ignore CVE-2025-66478. It has been rejected for being a duplicate of the preferred CVE-2025-55182.
Flashpoint strongly recommends security teams treat this vulnerability with utmost urgency. Our vulnerability research team will continue to monitor this vulnerability and its downstream impacts. All updates will be provided via Flashpoint’s VulnDB.
Request a demo today and gain access to quality vulnerability intelligence that helps address critical threats in a timely manner.
The post Digital Supply Chain Risk: Critical Vulnerability Affecting React Allows for Unauthorized Remote Code Execution appeared first on Flashpoint.
Flashpoint’s forward-looking threat insights for security and executive teams, provides the strategic foresight needed to prepare for the convergence of AI, identity, and physical security threats in 2026.

As the global threat landscape accelerates its transformation, 2026 marks an inflection point requiring defensive strategies to fundamentally shift. The volatility observed in 2025 has paved the way for an era soon to be defined by AI-weaponized autonomy, information-stealing malware, systemic instability of public vulnerability systems, and the complete convergence of digital and physical risk.
Flashpoint offers a unique window into these complexities, providing organizations with the foresight needed to navigate what lies ahead. Drawing from Flashpoint’s leading intelligence and primary source collections, we highlight five key trends shaping the 2026 threat landscape. These insights aim to help organizations not only understand what’s next but also build the resilience needed to withstand and adapt to emerging challenges.
2026 will see continued evolution of AI threats, with future attacks centering on autonomy and integration. Across the deep and dark web, Flashpoint is observing threat actors move past experimentation and into operational use of illegal AI.
As attackers train custom fraud-tuned LLMs (Large Language Models) and multilingual phishing tools directly on illicit data, these AI models will become more capable. The criminal intent shaping their misuse will also become more sophisticated. Additionally, 2026 will see a greater marketplace for paid jailbreaking communities and synthetic media kits for KYC (Know Your Customer) bypass.
These advancements are enabling criminals to move beyond simple tools and engage in scaled, autonomous fraud operations, leading to two major shifts:
“The ubiquity of automation has dramatically increased attack tempo, leaving many security teams behind the curve. While automation can replace repetitive tasks across the enterprise, organizations must not make the critical mistake of substituting human judgement for AI at the intelligence level.
Josh Lefkowitz, CEO at Flashpoint
This is paramount because a critical threat in 2026 is Agentic AI autonomy weaponized against soft targets—API integrations and identity systems. The only winning defense will be human-led and AI-scaled, prioritizing purposeful use to keep organizations ahead of this exponential risk.”
These evolving AI threats will force a fundamental shift in defensive strategies. Defenders will have to shift to deploying systems around AI rather than trust them on their own.
Infostealers will become the entry point, the data broker, the reconnaissance layer, and the fuel for everything that comes after a cyberattack. This shift is already in motion and is accelerating rapidly: in just the first half of 2025, infostealers were responsible for 1.8 billion stolen credentials, an 800% spike from the start of the year. However, 2026 will redefine the malware’s role, making its most valuable output being access, rather than disruption.
Infostealers will become the upstream event that powers the rest of the attack chain. Identity and session data will be increasingly targeted, since it gives attackers immediate access into victim environments. Ransomware, fraud, data theft, and extortion will simply be downstream ways to monetize.
This upstream approach defines the new reality of the attack chain, which is already operational. Nearly every major stealer strain Flashpoint observes now exfiltrates the following:
An organization’s attack surface is no longer just composed of their own networks. It is the entire digital identity of their employees and partners. This new reality requires security teams to take a new approach. Instead of attempting to block attacks, they must proactively detect compromised credentials before they are weaponized. This will be the difference between reacting to a data breach and preventing one.
“The infostealer economy has fully industrialized the attack chain, making initial compromise a low-cost commodity. Multiple security incidents in 2025 tie back to credentials found in infostealer logs. This reality has underscored the critical importance of digital trust—specifically, verifying who can access what resources. For 2026, identity is the perimeter to watch, and security teams must proactively hunt for compromised credentials before they’re weaponized.”
Ian Gray, Vice President of Intelligence at Flashpoint
The temporary funding crisis at CVE in April 2025 and the subsequent CISA stopgap extension through March 2026 exposed the systemic fragility of a centralized vulnerability intelligence model. With the future of the CVE/NVD system hanging in the balance, 2026 will be defined by the urgent need for redundancy and diversification in vulnerability intelligence.
In today’s vulnerability intelligence ecosystem, nearly every organization’s vulnerability management framework relies on CVE and NVD—including its “alternatives” such as the EUVD (European Union Vulnerability Database). The CVE system has grown into a critical global cybersecurity utility, relied upon by nearly all vulnerability scanners, SIEM platforms, patch management tools, threat intelligence feeds, and compliance reports. A complete shutdown of CVE would result in a widespread loss of institutional infrastructure.
The next generation of security needs to be built on practices that are resilient, diversified, and intelligence-driven. It should be focused on providing insights that can be used to take action such as threat actor behavior, likelihood of exploitation in the wild, relevance to ransomware campaigns, and business context. Security teams will need to leverage a comprehensive source of vulnerability intelligence such as Flashpoint’s VulnDB that provides full coverage for CVE, while also cataloging more than 100,000 vulnerabilities missed by CVE and NVD.
The continued blurring of lines between cyber, physical, and geopolitical threats will elevate the risk to organizational leadership, turning executive protection into a holistic intelligence function in 2026. The rise of information warfare combined with physical world convergence means the threat to key personnel is no longer purely digital.
In the aftermath of the tragic December 2024 assassination of United Healthcare’s CEO, Flashpoint has seen the continued circulation and glorification of “wanted-style posters” of executives in extremist communities. Additionally, Flashpoint has seen nation-state actors participate, using espionage and influence to target high-value individuals.
Organizations must adopt an integrated approach that connects insights from threat actor chatter and a wealth of other OSINT sources. This fusion of intelligence is essential for applying frameworks to ensure the safety of leadership and key personnel.
2025 was marked by several large-scale extortion campaigns, demonstrating how the threat landscape is rapidly evolving. Ransomware operations have shifted into a straight extortion play. Flashpoint has observed a surge in new entrants to the ransomware market, accompanied by a decline in the quality and decorum of ransomware groups.
Furthermore, vishing campaigns attributed to “Scattered Spider” have highlighted weaknesses in identity, trust, and verification. Campaigns from “Scattered LAPSUS$ Hunters” have also exposed vulnerabilities in third-party integrations. These attacks culminated in extortion, showcasing that modern attacks will target trusted users and trusted applications for initial access, and will forgo ransomware in place of data access.
As this shift continues into 2026, threat actors will increasingly focus their efforts on exploiting human behavior and identity systems. Instead of attempting to spend resources on breaking network perimeters, attackers will instead socially engineer employees to gain access to corporate systems at scale. This change in TTPs will undoubtedly greatly increase supply chain risk, especially for third parties.
These five predictions highlight the transformative trends shaping the future of cybersecurity and threat intelligence. Staying ahead of these challenges demands more than just reactive measures—it requires actionable intelligence, strategic foresight, and cross-sector collaboration. By embracing these principles and investing in proactive security strategies, organizations can not only mitigate risks but also seize opportunities to enhance their resilience.
As the threat landscape continues to rapidly evolve, staying informed and prepared are critical components of risk mitigation. With the right tools, insights, and partnerships, security teams can navigate the complexities ahead and safeguard what matters most.
The post Flashpoint’s Top 5 Predictions for the 2026 Threat Landscape appeared first on Flashpoint.
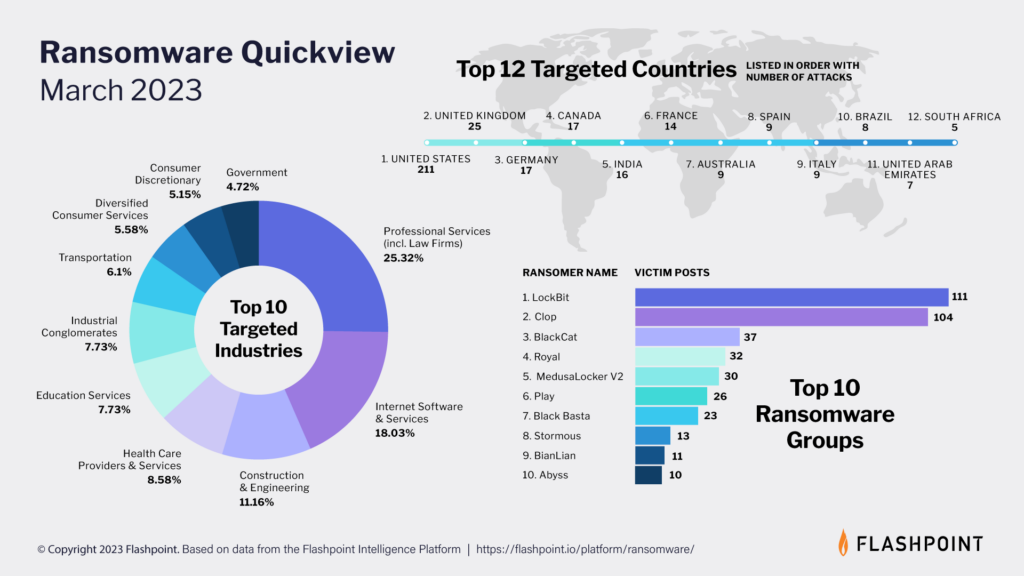
Flashpoint’s monthly look at the cyber risk ecosystem affecting organizations around the world, including intelligence, news, data, and analysis about ransomware, vulnerabilities, insider threats, and takedowns of illicit forums and shops.
Flashpoint’s latest ransomware infographic paints a sobering picture of the evolving threat landscape, as cybercriminals employ increasingly sophisticated—and effective—tactics. Last month, our analysts observed a total of 397 ransomware attacks.
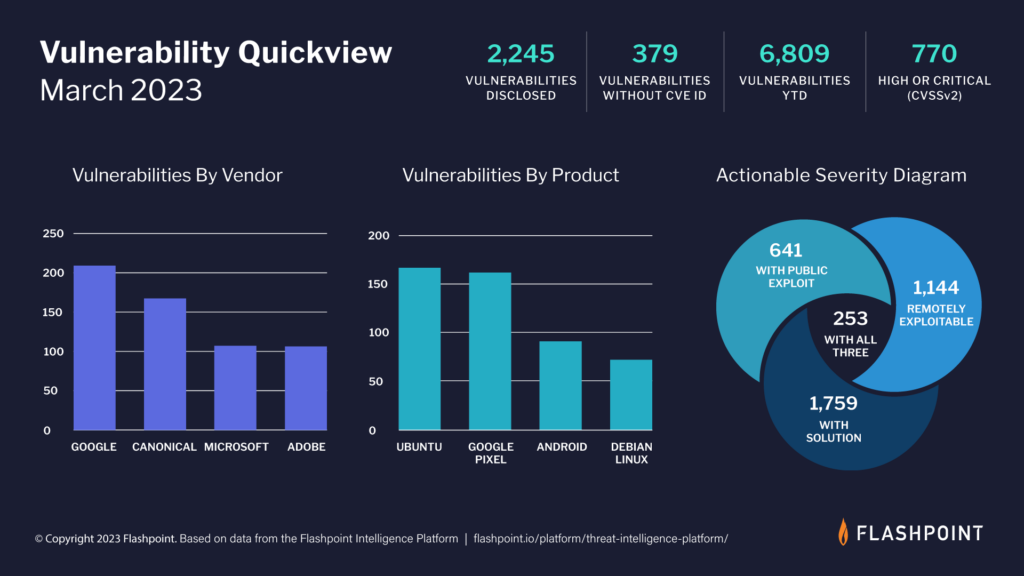
According to our intelligence, 2,245 new vulnerabilities were reported in March, with 379 of them being missed by the Common Vulnerabilities and Exposures (CVE) and National Vulnerability Database (NVD).
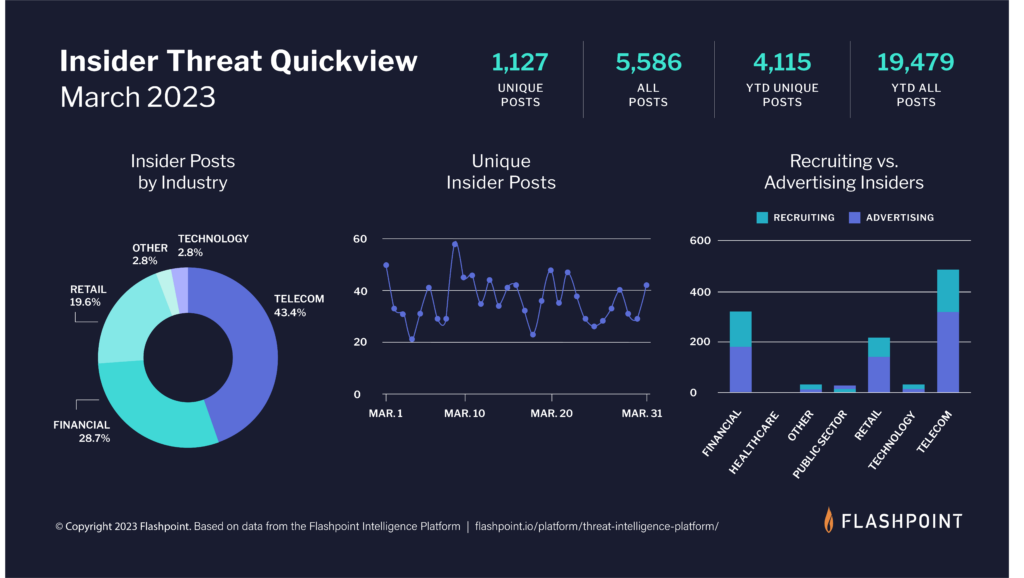
The tactic of recruiting insiders has become immensely popular amongst threat actors aiming to breach systems and/or commit ransomware attacks.
In March, our analysts collected 5,586 posts advertising insider services—both from threat actors seeking insiders and malicious employees offering their services. Of those, 1,127 were unique posts from individuals in illicit and underground communities.
In March 2023, there were numerous takedowns, voluntary shutdowns, and arrests affecting ransomware, markets, account shops, card shops, and individual cybercriminals. Here are the high-profile takedowns.
On March 21, 2023, mid-tier hacking forum Breach Forums was shut down following the arrest of its administrator, Conor Brian Fitzpatrick (aka “pompompurin”), six days prior.
Read the court doc here.
On March 3, a US Magistrate Judge issued a seizure warrant for Worldwiredlabs[.]com, a domain used by cybercriminals to sell malware, including remote access trojan (RAT) “NetWire,” which is capable of targeting and infecting major computer operating systems.
On March 7, an international law enforcement effort led to the seizure of Worldwiredlabs. The FBI had begun its investigation in 2020, and uncovered that it was the only known online distributor of NetWire.
Read the court doc here.
The following data is derived from the Flashpoint Intelligence Platform and VulnDB, the most comprehensive and timely source of vulnerability intelligence available. Sign up for a free trial today.

Jordan Drysdale// tl;dr Vulnerability management is a part of doing business and operating on the public internet these days. Include training as part of this Critical Control. Users should be […]
The post Small and Medium Business Security Strategies: Part 4 appeared first on Black Hills Information Security, Inc..