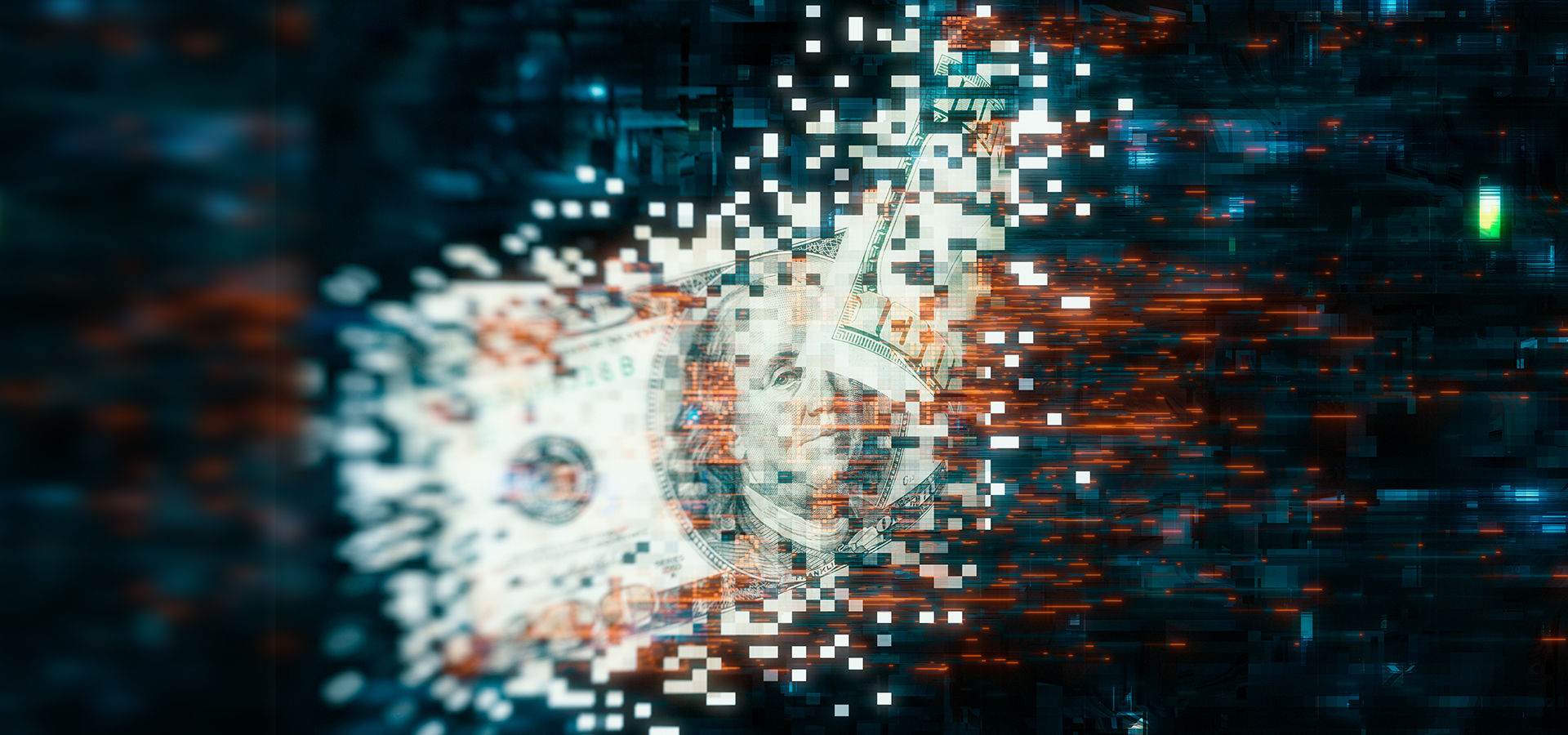
01flip: Multi-Platform Ransomware Written in Rust
01flip is a new ransomware family fully written in Rust. Activity linked to 01flip points to alleged dark web data leaks.
The post 01flip: Multi-Platform Ransomware Written in Rust appeared first on Unit 42.