Normal view
RedVDS Cybercrime Service Disrupted by Microsoft and Law Enforcement
RedVDS enables threat actors to set up servers that can be used for phishing, BEC attacks, account takeover, and fraud.
The post RedVDS Cybercrime Service Disrupted by Microsoft and Law Enforcement appeared first on SecurityWeek.
Microsoft: Windows 365 update blocks access to Cloud PC sessions
New Windows updates replace expiring Secure Boot certificates
Microsoft releases Windows 10 KB5073724 extended security update
Windows 11 KB5074109 & KB5073455 cumulative updates released
Microsoft January 2026 Patch Tuesday fixes 3 zero-days, 114 flaws
Deze gevaarlijke malware is ontdekt op 400.000 Windows-computers

Nieuwe AI-agents van Microsoft kunnen autonoom taken rond beveiliging uitvoeren

Microsoft is retiring the Lens scanner app for iOS, Android
Microsoft is retiring 'Send to Kindle' in Word
Dynamic Device Code Phishing
![]()
rvrsh3ll // Introduction This blog post is intended to give a light overview of device codes, access tokens, and refresh tokens. Here, I focus on the technical how-to for standing […]
The post Dynamic Device Code Phishing appeared first on Black Hills Information Security, Inc..
Rainy Day Windows Command Research Results
![]()
Sally Vandeven // We have all heard people talk about how much cooler Linux is than Windows, so much easier to use, etc. Well, they are not necessarily wrong… but we […]
The post Rainy Day Windows Command Research Results appeared first on Black Hills Information Security, Inc..
PODCAST: Hacker Tools, Compliments of Microsoft
![]()
Sally Vandeven & David Fletcher // This is the podcast version of Sally & David’s webcast. For the whole webcast see our webcast post. Links that are mentioned in this […]
The post PODCAST: Hacker Tools, Compliments of Microsoft appeared first on Black Hills Information Security, Inc..
WEBCAST: Hacker Tools, Compliments of Microsoft
![]()
David Fletcher & Sally Vandeven// Join David “Fletch” and Sally as they explore the cornucopia of wonderful, free tools in the SysInternals Suite that conveniently are signed by Microsoft and […]
The post WEBCAST: Hacker Tools, Compliments of Microsoft appeared first on Black Hills Information Security, Inc..
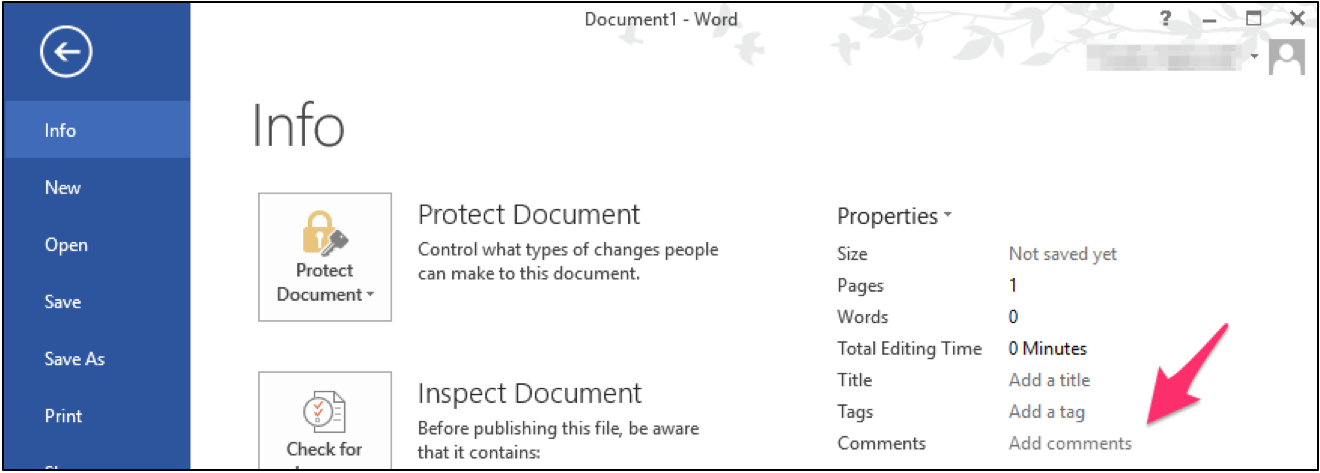
Hide Payload in MS Office Document Properties
![]()
Carrie Roberts* // Can you think of a reason why you might want to put a lengthy comment into the properties of an MS Office document? If you can, then […]
The post Hide Payload in MS Office Document Properties appeared first on Black Hills Information Security, Inc..
WEBCAST: Wrangling Internal Network Vulnerabilities
![]()
Jordan Drysdale & Kent Ickler // In this webcast, we demonstrate some standard methodologies utilized during an internal network review. We also discuss various tools used to test network defenses […]
The post WEBCAST: Wrangling Internal Network Vulnerabilities appeared first on Black Hills Information Security, Inc..
Abusing Exchange Mailbox Permissions with MailSniper
![]()
Beau Bullock // Overview Microsoft Exchange users have the power to grant other users various levels of access to their mailbox folders. For example, a user can grant other users […]
The post Abusing Exchange Mailbox Permissions with MailSniper appeared first on Black Hills Information Security, Inc..
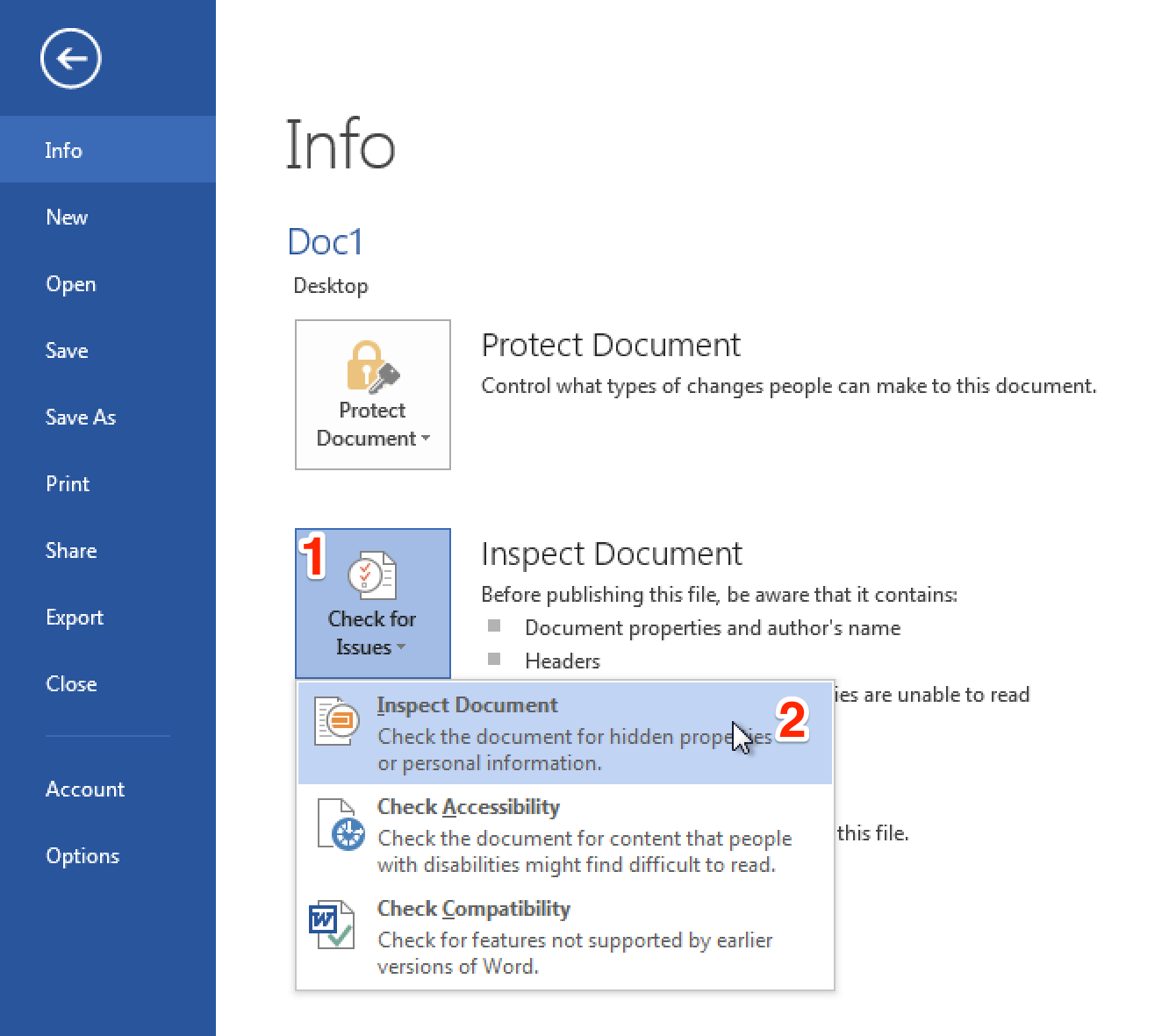
Bugging Microsoft Files: Part 3 – Clearing Metadata
![]()
Ethan Robish // In my last two posts I showed how to insert tracking bugs in both .docx (Part 1) and .xlsx files (Part 2). But don’t let all that effort go […]
The post Bugging Microsoft Files: Part 3 – Clearing Metadata appeared first on Black Hills Information Security, Inc..
-
Black Hills Information Security, Inc.

- Bugging Microsoft Files: Part 1 – Docx Files using Microsoft Word
Bugging Microsoft Files: Part 1 – Docx Files using Microsoft Word
![]()
Ethan Robish // If you’re familiar with ADHD and Web Word Bugs, you likely already know the method to create web tracking software using .html files renamed as .doc files. […]
The post Bugging Microsoft Files: Part 1 – Docx Files using Microsoft Word appeared first on Black Hills Information Security, Inc..