Normal view
01flip: Multi-Platform Ransomware Written in Rust
01flip is a new ransomware family fully written in Rust. Activity linked to 01flip points to alleged dark web data leaks.
The post 01flip: Multi-Platform Ransomware Written in Rust appeared first on Unit 42.

Auditd Field Spoofing: Now You Auditd Me, Now You Auditdon’t
![]()
moth // Introduction One fateful night in June of 2022, Ethan sent a message to the crew: “Anyone know ways to fool Auditd on Linux? I’m trying to figure out how to change the auid (audit […]
The post Auditd Field Spoofing: Now You Auditd Me, Now You Auditdon’t appeared first on Black Hills Information Security, Inc..
Linux System Call Monitoring
![]()
moth // I’ve been diving deep into Linux lately, with my latest kick being exploring the Linux kernel. I’ve found “The Linux Programming Interface” (TLPI) by Michael Kerrisk, among others, […]
The post Linux System Call Monitoring appeared first on Black Hills Information Security, Inc..
-
Black Hills Information Security, Inc.
- Webcast: Linux Forensics Magical Mystery Tour With Hal Pomeranz
Webcast: Linux Forensics Magical Mystery Tour With Hal Pomeranz
![]()
One of our favorite BHIS guest presenters, Hal Pomeranz, returns for more of the Linux goodness. Roll up for a magical tour through the mysteries of Linux file systems! Relative […]
The post Webcast: Linux Forensics Magical Mystery Tour With Hal Pomeranz appeared first on Black Hills Information Security, Inc..
Webcast: Linux Command Line Dojo with Hal Pomeranz
![]()
In this webcast, we have our friend Hal Pomeranz sharing his massive knowledge on Linux. If you’re new to Linux, or if you know it and just want to hear […]
The post Webcast: Linux Command Line Dojo with Hal Pomeranz appeared first on Black Hills Information Security, Inc..
Fixing EyeWitness Install Errors on Kali Linux
![]()
Darin Roberts // I recently had to install a new gold image as my Kali Linux testing virtual machine. Almost on every test I do, I clone the gold image […]
The post Fixing EyeWitness Install Errors on Kali Linux appeared first on Black Hills Information Security, Inc..
-
Black Hills Information Security, Inc.
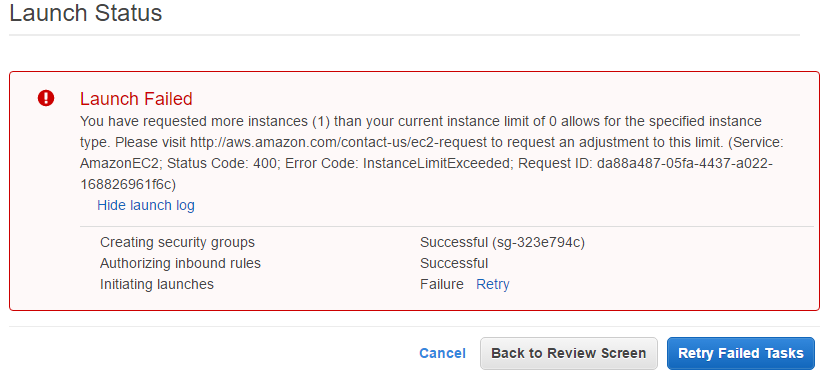
- How to Crack Passwords in the Cloud with GPU Acceleration (Kali 2017)
How to Crack Passwords in the Cloud with GPU Acceleration (Kali 2017)
![]()
Carrie Roberts* // How does password cracking in the cloud compare to down here on earth? Maybe not as heavenly as imagined. I saw this on the web and got […]
The post How to Crack Passwords in the Cloud with GPU Acceleration (Kali 2017) appeared first on Black Hills Information Security, Inc..
-
Black Hills Information Security, Inc.

- How to DIY a Mobile Hacking Platform – Kali NetHunter on a Rooted Nexus7
How to DIY a Mobile Hacking Platform – Kali NetHunter on a Rooted Nexus7
![]()
Derek Banks // As pentesters, it is probably not a surprise that we tend to make fairly heavy use of Kali Linux on a fairly regular basis. The folks at Offensive […]
The post How to DIY a Mobile Hacking Platform – Kali NetHunter on a Rooted Nexus7 appeared first on Black Hills Information Security, Inc..
Two Button PWNage
![]()
Logan Lembke // Step One: Power. Step Two: Enter. Step Three: ???? Step Four: Profit. In the security industry, we love our encryption. However sometimes, the complexity introduced by encryption […]
The post Two Button PWNage appeared first on Black Hills Information Security, Inc..
Lawrence’s List 090216
Lawrence Hoffmann // Election fraud is something I’ve mentioned here recently. The reality we must face here is that any time a digital system is used for voting there is […]
The post Lawrence’s List 090216 appeared first on Black Hills Information Security, Inc..
Time To Bash on Windows (Bourne Again Shell That Is)
Editor’s Note: This is another awesome guest post from our friend, Robert Schwass. If you’d like to guest post contact us here. Robert Schwass // I had heard the rumors about […]
The post Time To Bash on Windows (Bourne Again Shell That Is) appeared first on Black Hills Information Security, Inc..
Lawrence’s List 071516
Lawrence Hoffman // Hey, I’m back! Vacation was great. I spent part of last week on an Island so I was unable to scratch the keep-up-with-the-media itch. Now that I’m […]
The post Lawrence’s List 071516 appeared first on Black Hills Information Security, Inc..
Securing Your Way to Restful Sleep with Ansible Galaxy
Jordan Drysdale // Life as a ‘blue-teamer’ can often be a stressful experience. Working in an environment with a strong Linux infrastructure can help some, but Ansible can help […]
The post Securing Your Way to Restful Sleep with Ansible Galaxy appeared first on Black Hills Information Security, Inc..
SSH Config Files
Ethan Robish // Here’s a short intro for anyone not familiar with ssh config files, which are usually located at ~/.ssh/config As an example, you have ssh running on port […]
The post SSH Config Files appeared first on Black Hills Information Security, Inc..
Lawrence’s List 061316
Editor’s Note: We’ll feature Lawrence’s List every week. It will include interesting things he’s come across during the week as he’s an avid consumer of internet garbage and follows a […]
The post Lawrence’s List 061316 appeared first on Black Hills Information Security, Inc..
How to create a SOHO router using Ubuntu Linux
![]()
Joff Thyer // This post is cross-posted from Packet Header on 3/1/16. __________ On Security Weekly Episode 452, I presented a technical segment on how to build your own […]
The post How to create a SOHO router using Ubuntu Linux appeared first on Black Hills Information Security, Inc..
Check Your Image
Lawrence Hoffman // Today I’ll walk through the process I use to verify ISO images before I install them. If you downloaded Linux Mint 17.3 Cinnamon on February 20th there’s […]
The post Check Your Image appeared first on Black Hills Information Security, Inc..