Six Android Malware Families Target Pix Payments, Banking Apps, and Crypto Wallets



China’s National Computer Network Emergency Response Technical Team has warned locals that the OpenClaw agentic AI tool poses significant security risks.…
This update adds option forcedecompress when using options -f and -s.
More info: Analyzing “Zombie Zip” Files (CVE-2026-0866).
zipdump_v0_0_35.zip (http)
(Note: This post is also cross-posted on the Let's Encrypt blog)
As announced earlier this year, Let's Encrypt now issues IP address and six-day certificates to the general public. The Certbot team here at the Electronic Frontier Foundation has been working on two improvements to support these features: the --preferred-profile flag released last year in Certbot 4.0, and the --ip-address flag, new in Certbot 5.3. With these improvements together, you can now use Certbot to get those IP address certificates!
If you want to try getting an IP address certificate using Certbot, install version 5.4 or higher (for webroot support with IP addresses), and run this command:
sudo certbot certonly --staging \--preferred-profile shortlived \--webroot \--webroot-path <filesystem path to webserver root> \--ip-address <your ip address>
Two things of note:
--staging flag to get a publicly trusted certificate.shortlived" profile, which will be good for 6 days. This is a Let's Encrypt requirement for IP address certificates.As of right now, Certbot only supports getting IP address certificates, not yet installing them in your web server. There's work to come on that front. In the meantime, edit your webserver configuration to load the newly issued certificate from /etc/letsencrypt/live/<ip address>/fullchain.pem and /etc/letsencrypt/live/<ip address>/privkey.pem.
The command line above uses Certbot's "webroot" mode, which places a challenge response file in a location where your already-running webserver can serve it. This is nice since you don't have to temporarily take down your server.
There are two other plugins that support IP address certificates today: --manual and --standalone. The manual plugin is like webroot, except Certbot pauses while you place the challenge response file manually (or runs a user-provided hook to place the file). The standalone plugin runs a simple web server that serves a challenge response. It has the advantage of being very easy to configure, but has the disadvantage that any running webserver on port 80 has to be temporarily taken down so Certbot can listen on that port. The nginx and apache plugins don't yet support IP addresses.
You should also be sure that Certbot is set up for automatic renewal. Most installation methods for Certbot set up automatic renewal for you. However, since the webserver-specific installers don't yet support IP address certificates, you'll have to set a --deploy-hook that tells your webserver to load the most up-to-date certificates from disk. You can provide this --deploy-hook through the certbot reconfigure command using the rest of the flags above.
We hope you enjoy using IP address certificates with Let's Encrypt and Certbot, and as always if you get stuck you can ask for help in the Let's Encrypt Community Forum.

Iran has reportedly designated Amazon, Google, IBM, Microsoft, Nvidia, Oracle, and Palantir facilities as legitimate targets of retaliatory strikes, according to an Al Jazeera report citing Iran’s state-affiliated Tasnim news agency.…
A hacking crew with ties to Iran's intelligence agency claimed to be behind a global network outage at med-tech firm Stryker on Wednesday, and said the cyberattack was in response to the US-Israel airstrikes.…
A recurring lure in phishing emails impersonating United Healthcare is the promise of a free Oral-B toothbrush. But the interesting part isn’t the toothbrush. It’s the link.

Recently we found that these phishers have moved from using Microsoft Azure Blob Storage (links looking like this:
https://{string}.blob.core.windows.net/{same string}/1.html
to links obfuscated by using an IPv6-mapped IPv4 address to hide the IP in a way that looks confusing but is still perfectly valid and routable. For example:
http://[::ffff:5111:8e14]/
In URLs, putting an IP in square brackets means it’s an IPv6 literal. So [::ffff:5111:8e14] is treated as an IPv6 address.
::ffff:x:y is a standard form called an IPv4-mapped IPv6 address, used to represent an IPv4 address inside IPv6 notation. The last 32 bits (the x:y part) encode the IPv4 address.
So we need to convert 5111:8e14 to an IPv4 address. 5111 and 8e14 are hexadecimal numbers. In theory that means:
But for IPv4-mapped addresses we really treat that last 32 bits as four bytes. If we unpack 0x51 0x11 0x8e 0x14:
So, the IPv4 address this URL leads to is 81.17.142.20
The emails are variations on a bogus reward from scammers pretending to be United Healthcare that uses a premium Oral‑B iO toothbrush as bait. Victims are sent to a fast‑rotating landing page where the likely endgame is the collection of personally identifiable information (PII) and card data under the guise of confirming eligibility or paying a small shipping fee.
If you submitted your card details:
Other ways to stay safe:
81.17.142.40
15.204.145.84
redirectingherenow[.]com
redirectofferid[.]pro
We don’t just report on scams—we help detect them
Cybersecurity risks should never spread beyond a headline. If something looks dodgy to you, check if it’s a scam using Malwarebytes Scam Guard. Submit a screenshot, paste suspicious content, or share a link, text or phone number, and we’ll tell you if it’s a scam or legit. Available with Malwarebytes Premium Security for all your devices, and in the Malwarebytes app for iOS and Android.
Not every scam starts with malware or a compromised account. Sometimes all it takes is a friend request or a link shared via chat.…


A hacktivist group with links to Iran’s intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker’s largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at Stryker’s main U.S. headquarters says the company is currently experiencing a building emergency.
Based in Kalamazoo, Michigan, Stryker [NYSE:SYK] is a medical and surgical equipment maker that reported $25 billion in global sales last year. In a lengthy statement posted to Telegram, an Iranian hacktivist group known as Handala (a.k.a. Handala Hack Team) claimed that Stryker’s offices in 79 countries have been forced to shut down after the group erased data from more than 200,000 systems, servers and mobile devices.
A manifesto posted by the Iran-backed hacktivist group Handala, claiming a mass data-wiping attack against medical technology maker Stryker.
“All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity and the exposure of injustice and corruption,” a portion of the Handala statement reads.
The group said the wiper attack was in retaliation for a Feb. 28 missile strike that hit an Iranian school and killed at least 175 people, most of them children. The New York Times reports today that an ongoing military investigation has determined the United States is responsible for the deadly Tomahawk missile strike.
Handala was one of several Iran-linked hacker groups recently profiled by Palo Alto Networks, which links it to Iran’s Ministry of Intelligence and Security (MOIS). Palo Alto says Handala surfaced in late 2023 and is assessed as one of several online personas maintained by Void Manticore, a MOIS-affiliated actor.
Stryker’s website says the company has 56,000 employees in 61 countries. A phone call placed Wednesday morning to the media line at Stryker’s Michigan headquarters sent this author to a voicemail message that stated, “We are currently experiencing a building emergency. Please try your call again later.”
A report Wednesday morning from the Irish Examiner said Stryker staff are now communicating via WhatsApp for any updates on when they can return to work. The story quoted an unnamed employee saying anything connected to the network is down, and that “anyone with Microsoft Outlook on their personal phones had their devices wiped.”
“Multiple sources have said that systems in the Cork headquarters have been ‘shut down’ and that Stryker devices held by employees have been wiped out,” the Examiner reported. “The login pages coming up on these devices have been defaced with the Handala logo.”
Wiper attacks usually involve malicious software designed to overwrite any existing data on infected devices. But a trusted source with knowledge of the attack who spoke on condition of anonymity told KrebsOnSecurity the perpetrators in this case appear to have used a Microsoft service called Microsoft Intune to issue a ‘remote wipe’ command against all connected devices.
Intune is a cloud-based solution built for IT teams to enforce security and data compliance policies, and it provides a single, web-based administrative console to monitor and control devices regardless of location. The Intune connection is supported by this Reddit discussion on the Stryker outage, where several users who claimed to be Stryker employees said they were told to uninstall Intune urgently.
Palo Alto says Handala’s hack-and-leak activity is primarily focused on Israel, with occasional targeting outside that scope when it serves a specific agenda. The security firm said Handala also has taken credit for recent attacks against fuel systems in Jordan and an Israeli energy exploration company.
“Recent observed activities are opportunistic and ‘quick and dirty,’ with a noticeable focus on supply-chain footholds (e.g., IT/service providers) to reach downstream victims, followed by ‘proof’ posts to amplify credibility and intimidate targets,” Palo Alto researchers wrote.
The Handala manifesto posted to Telegram referred to Stryker as a “Zionist-rooted corporation,” which may be a reference to the company’s 2019 acquisition of the Israeli company OrthoSpace.
Stryker is a major supplier of medical devices, and the ongoing attack is already affecting healthcare providers. One healthcare professional at a major university medical system in the United States told KrebsOnSecurity they are currently unable to order surgical supplies that they normally source through Stryker.
“This is a real-world supply chain attack,” the expert said, who asked to remain anonymous because they were not authorized to speak to the press. “Pretty much every hospital in the U.S. that performs surgeries uses their supplies.”
John Riggi, national advisor for the American Hospital Association (AHA), said the AHA is not aware of any supply-chain disruptions as of yet.
“We are aware of reports of the cyber attack against Stryker and are actively exchanging information with the hospital field and the federal government to understand the nature of the threat and assess any impact to hospital operations,” Riggi said in an email. “As of this time, we are not aware of any direct impacts or disruptions to U.S. hospitals as a result of this attack. That may change as hospitals evaluate services, technology and supply chain related to Stryker and if the duration of the attack extends.”
This is a developing story. Updates will be noted with a timestamp.
Update, 2:54 p.m. ET: Added comment from Riggi and perspectives on this attack’s potential to turn into a supply-chain problem for the healthcare system.
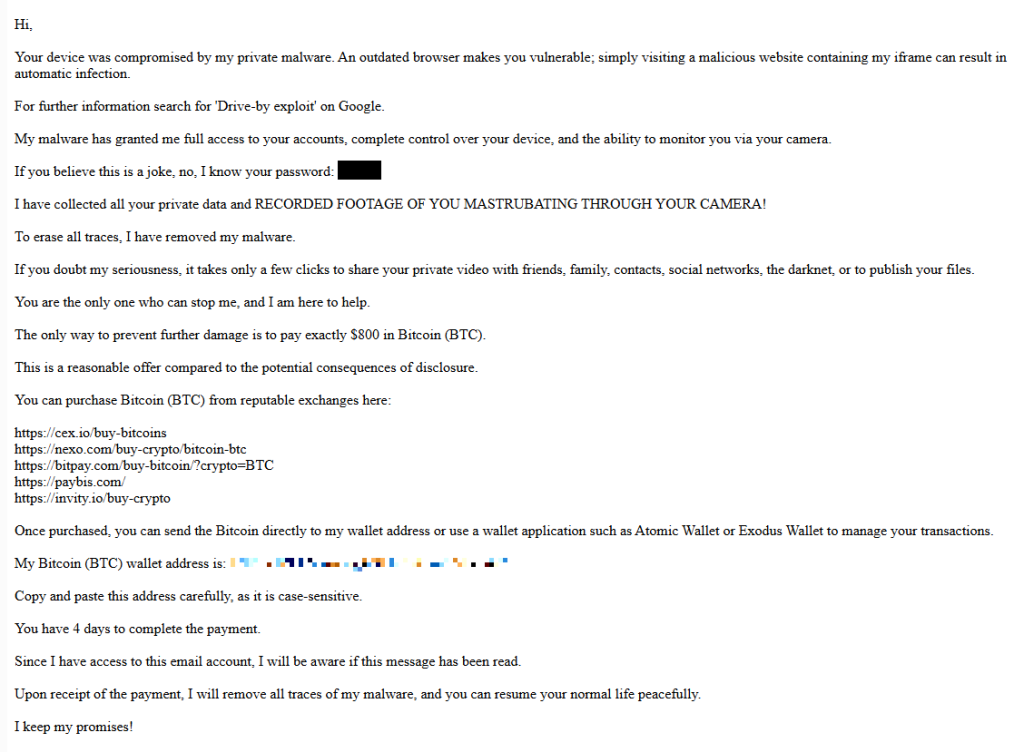
Our malware removal support team recently flagged a new wave of sextortion emails, with the subject line: “You pervert, I recorded you!”
If the message sounds familiar, that’s because it’s a variation of the long-running “Hello pervert” scam.
The email claims the target’s device has been infected by a “drive-by exploit,” which supposedly gave the extortionist full access to the device. To add credibility, the scammer includes a password that actually belongs to the target.
Here’s one of the emails:

Your device was compromised by my private malware. An outdated browser makes you vulnerable; simply visiting a malicious website containing my iframe can result in automatic infection.
For further information search for ‘Drive-by exploit’ on Google.
My malware has granted me full access to your accounts, complete control over your device, and the ability to monitor you via your camera.
If you believe this is a joke, no, I know your password: {an actual password}
I have collected all your private data and RECORDED FOOTAGE OF YOU MASTRUBATING THROUGH YOUR CAMERA!
To erase all traces, I have removed my malware.
If you doubt my seriousness, it takes only a few clicks to share your private video with friends, family, contacts, social networks, the darknet, or to publish your files.
You are the only one who can stop me, and I am here to help.
The only way to prevent further damage is to pay exactly $800 in Bitcoin (BTC).
This is a reasonable offer compared to the potential consequences of disclosure.
You can purchase Bitcoin (BTC) from reputable exchanges here:
{list of crypto-currency exchanges}
Once purchased, you can send the Bitcoin directly to my wallet address or use a wallet application such as Atomic Wallet or Exodus Wallet to manage your transactions.
My Bitcoin (BTC) wallet address is: {bitcoin wallet which has received 1 payment at the time of writing}
Copy and paste this address carefully, as it is case-sensitive.
You have 4 days to complete the payment.
Since I have access to this email account, I will be aware if this message has been read.
Upon receipt of the payment, I will remove all traces of my malware, and you can resume your normal life peacefully.
I keep my promises!
The message is a bit contradictory. Early on, the sender claims they have already removed the malware to “erase all traces,” but later promises to remove it after receiving payment.
I found that one particular sender using the name Jenny Green and the Gmail address JennyGreen64868@gmail.com sent many of these emails to people that use the FakeMailGenerator service.
FakeMailGenerator is a free disposable email service that gives users a temporary, receive‑only inbox they can use instead of their real address, mainly to get around email confirmations or avoid spam.
As mentioned, the addresses are receive‑only, meaning they cannot legitimately send mail and the mailbox is not tied to a specific person. On top of that, there is no login. Anyone who knows the address (or guesses the inbox URL) can see the same inbox.
My guess is that the scammer searched these public inboxes for passwords and then reused those passwords in their sextortion emails.
So users of FakeMailGenerator and similar services should consider this a warning. Your inbox may be publicly accessible, show up in search results, and you may receive a lot more than what you signed up for. Definitely don’t use services like this for anything sensitive.
Knowing these scams exist is the first step to avoiding them. Sextortion emails rely on panic and embarrassment to push people into paying quickly. Here are a few simple steps to protect yourself:
Pro tip: Malwarebytes Scam Guard immediately recognized this for what it is: a sextortion scam.
What do cybercriminals know about you?
Use Malwarebytes’ free Digital Footprint scan to see whether your personal information has been exposed online.

Have you ever seen a really creepy targeted ad online? One that revealed just how much these companies know about your life? It's unsettling enough to see how much companies know about you—but now we have confirmation that the government is also tapping the advertising surveillance machine to get your data. We're explaining the dangers of targeted advertising and location tracking, and the latest in the fight for privacy and free speech online, with our EFFector newsletter.
For over 35 years, EFFector has been your guide to understanding the intersection of technology, civil liberties, and the law. This issue covers a victory for protesters seeking to hold police accountable, a troubling conflict over the Department of Defense's use of AI, and how advertising surveillance enables government surveillance.
Prefer to listen in? Big news: EFFector is now available on all major podcast platforms! In this episode we chat with EFF Staff Attorney Lena Cohen about how targeted advertising can reveal your location to federal law enforcement. You can find the episode and subscribe in your podcast player of choice:
Want to stay in the fight for privacy and free speech online? Sign up for EFF's EFFector newsletter for updates, ways to take action, and new merch drops. You can also fuel the fight against online surveillance when you support EFF today!

The UK's data protection watchdog has fined Police Scotland £66,000 ($88,000) for what it calls a "serious failure" in handling an alleged victim's sensitive data.…
While Americans are sorting through paperwork to get their taxes filed in time, scammers are working overtime to grab a piece of the action.
As tax season ramps up, so does scam activity. Our telemetry shows a spike in robocalls impersonating tax resolution firms, tax relief agencies, and vaguely named “assistance centers.” These calls are designed to create urgency, fear, and confusion in the hope of pushing recipients to call back before they have time to think critically.
These robocalls typically try to collect personal information, pressure victims into paying fake tax debts, or funnel them into questionable tax-relief services.
Below are transcripts of two recent voicemail examples submitted by anonymized Scam Guard users that illustrate how these scams operate.
Voicemail #1
“Hi, this is <REDACTED_NAME> calling on March 3rd from the eligibility support and review division at the tax resolution assistance center. I’m contacting you because your account remains under active confirmation review. There is still an opportunity to verify your standing while this evaluation period remains open. To make this simple, we provide a direct proprietary verification line with no weight, allowing immediate access to clear and accurate information. This verification step is brief and focused strictly on determining current eligibility and available options. Please call back at 888-919-9743. Again, 888-919-9743. If this message reached you in error, please call back and press 3 to be removed”
Characteristics:
Voicemail #2
“Hi, this is <REDACTED_NAME> with professional tax associates. Today is Tuesday March 3rd. I’m calling to follow up on back taxes and missed filings. This may be our only attempt to reach you, and due to new resolution programs that are available for a limited time, we highly recommend you give us a call today. This will be your best opportunity to get a fresh start before it becomes a bigger and permanent issue. Please call us back today at 8338204216 again 8338204216. If you’ve already resolved this issue. You may disregard this message or call back using the number on your caller ID to opt out. Thank you. If you were reached in error or wish to stop future outreach, please press 8 now and you will be removed from future outreach. Thank you and we look forward to assisting you. “
Characteristics:
While the wording differs slightly, the structure and psychological tactics are nearly identical.
Both messages use generic but authoritative language:
These names sound legitimate but don’t identify a specific, verifiable company. Scammers often rely on institutional-sounding phrases to create credibility without providing any real details.
Both messages also reference vague “account” problems, but neither voicemail mentions:
Instead, they reference:
This vagueness is intentional. It allows the same robocall script to target thousands of people, regardless of their actual tax situation.
What you will always see with scams is urgency. Both calls attempt to rush the recipient into action:
Creating urgency reduces the likelihood that someone will pause, research the number, or consult a trusted source.
The second voicemail includes the promise of a “fresh start before it becomes a bigger and permanent issue.” This is a common emotional hook, blending fear (a permanent problem) with hope (a fresh start), which can encourage impulsive callbacks.
Both messages push recipients to call a direct number rather than referencing an official website or established contact method. Legitimate tax agencies, including the IRS, do not initiate contact through unsolicited robocalls asking you to call back immediately.
Both scripts include instructions like:
These opt-out options create an illusion of compliance and legitimacy. In reality, pressing numbers or calling back can confirm that your phone number is active, which may lead to more scam calls.
Knowing how to identify scam calls is an important step. So, here are some key red flags to watch for:
If a message checks at least one of these boxes, it is very likely not legitimate.
We don’t just report on threats—we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your, and your family’s, personal information by using identity protection.


A Swiss canton has suspended its pilot of electronic voting after failing to count 2,048 votes cast in national referendums held on March 8.…


Dutch police have arrested a 17-year-old boy who detectives suspect was responsible for 16 bank card frauds across the Netherlands.…