How to Get Malicious Macros Past Email Filters
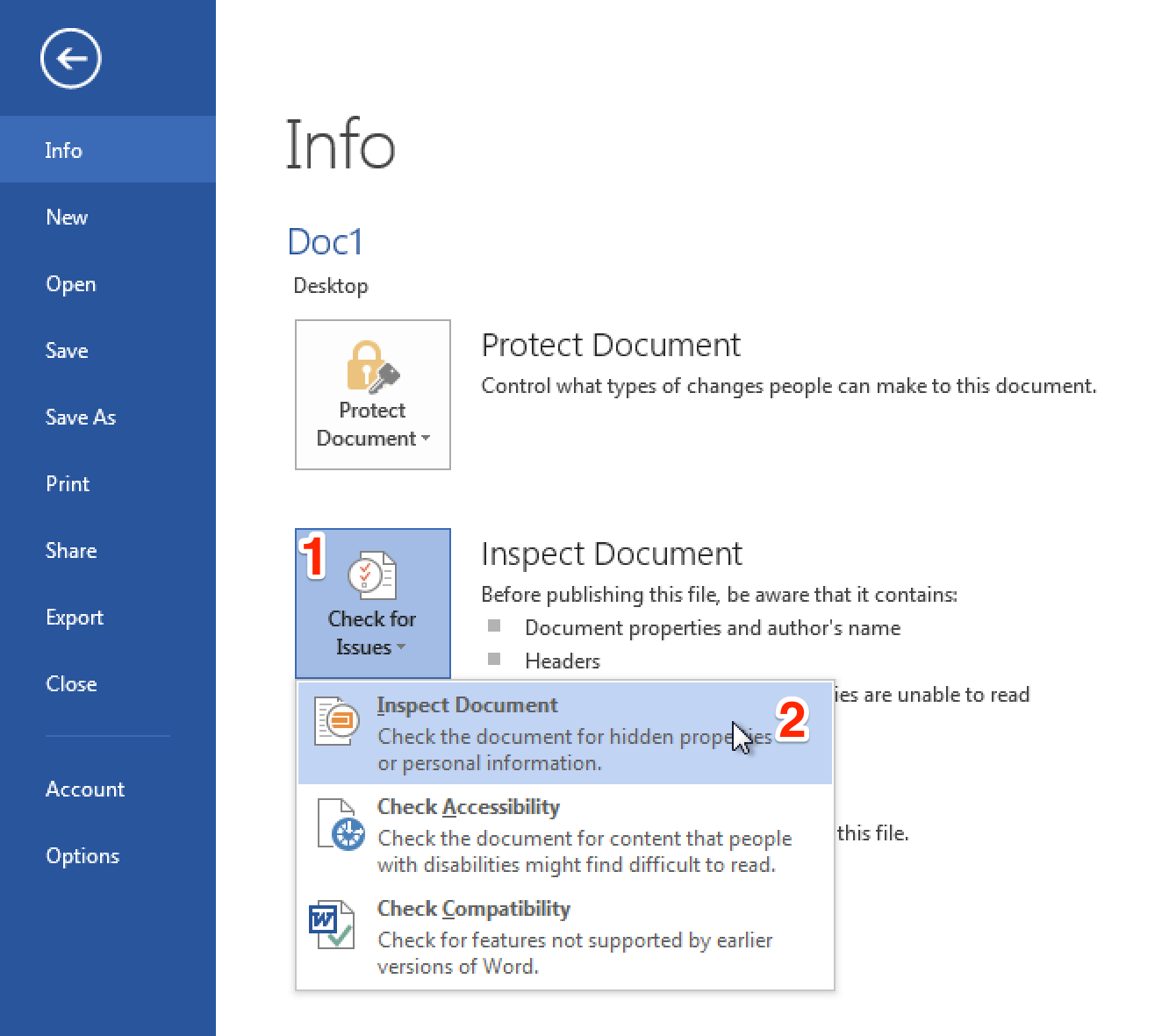
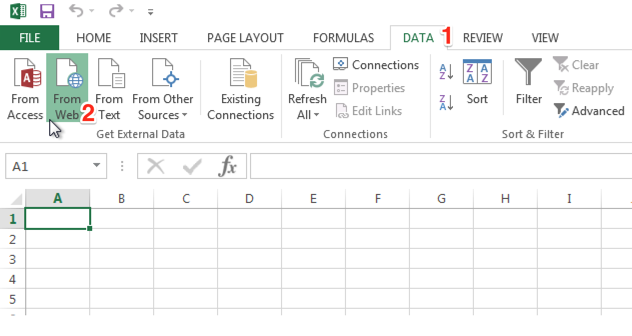
Carrie Roberts // A malicious macro in a Microsoft Word or Excel document is an effective hacking technique. These documents could be delivered in a variety of […]
The post How to Get Malicious Macros Past Email Filters appeared first on Black Hills Information Security, Inc..