Intro to Data Analytics Using SQL
![]()
In this video, Ethan Robish discusses the fundamentals and intricacies of data analytics using SQL.
The post Intro to Data Analytics Using SQL appeared first on Black Hills Information Security, Inc..
![]()
In this video, Ethan Robish discusses the fundamentals and intricacies of data analytics using SQL.
The post Intro to Data Analytics Using SQL appeared first on Black Hills Information Security, Inc..
![]()
| Ethan Robish It’s been nearly a year since Lastpass was breached and users’ encrypted vaults were stolen. I had already migrated to a different password manager for all my […]
The post Rotating Your Passwords After a Password Manager Breach appeared first on Black Hills Information Security, Inc..
![]()
Are you tired of spinning up an entire OS in a VM just to run a tool? Have you ever struggled to install a program you needed? When was the […]
The post Webcast: What Can Docker Do for Me? appeared first on Black Hills Information Security, Inc..
![]()
Ethan Robish // Why Segment Your Network? Here’s a quick recap from Part 1. A typical home network is flat. This means that all devices are connected to the same […]
The post Home Network Design – Part 2 appeared first on Black Hills Information Security, Inc..
![]()
Ethan Robish // WebSockets Overview WebSockets is a technology to allow browsers and servers to establish a single TCP connection and then asynchronously communicate in either direction. This is great […]
The post How to Hack WebSockets and Socket.io appeared first on Black Hills Information Security, Inc..
![]()
Ethan Robish // In this series of posts, I’ll discuss how I segmented my home network using VLANs and how I moved away from using a risky consumer-grade router at […]
The post Home Network Design – Part 1 appeared first on Black Hills Information Security, Inc..
![]()
Ethan Robish // In my last two posts I showed how to insert tracking bugs in both .docx (Part 1) and .xlsx files (Part 2). But don’t let all that effort go […]
The post Bugging Microsoft Files: Part 3 – Clearing Metadata appeared first on Black Hills Information Security, Inc..
![]()
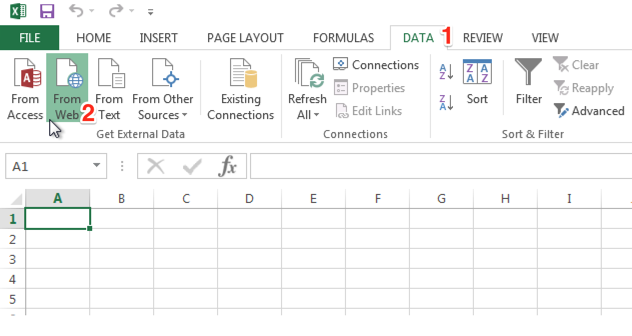
Ethan Robish // As promised in my previous post, part 1, this post shows how to place a tracking bug in a native .xlsx file. Full credit for this method […]
The post Bugging Microsoft Files: Part 2 – Xlsx Files using Microsoft Excel appeared first on Black Hills Information Security, Inc..

![]()
Ethan Robish // If you’re familiar with ADHD and Web Word Bugs, you likely already know the method to create web tracking software using .html files renamed as .doc files. […]
The post Bugging Microsoft Files: Part 1 – Docx Files using Microsoft Word appeared first on Black Hills Information Security, Inc..
Ethan Robish // Let’s Encrypt is a free service that allows you to obtain a free (as in beer) SSL/TLS domain validation certificate to use as you wish. Here is what […]
The post How Does Let’s Encrypt Gain Your Browser’s Trust? appeared first on Black Hills Information Security, Inc..
Ethan Robish // Ads serve an important function on the internet. For many websites, ads are the main form of revenue that funds the site’s content or service. This, however, […]
The post How to Block Ads on All Your Devices appeared first on Black Hills Information Security, Inc..
Ethan Robish // Here’s a short intro for anyone not familiar with ssh config files, which are usually located at ~/.ssh/config As an example, you have ssh running on port […]
The post SSH Config Files appeared first on Black Hills Information Security, Inc..
Sierra Ward & Ethan Robish // Intro by Ethan: Sierra came up with the idea to interview me for this blog. I thought it was a great idea and after watching Rick […]
The post Get to Know a Tester: Ethan Robish appeared first on Black Hills Information Security, Inc..