Written by: Bhavesh Dhake, Will Silverstone, Matthew Hitchcock, Aaron Fletcher
The Criticality of Privileged Access in Today's Threat Landscape
Privileged access stands as the most critical pathway for adversaries seeking to compromise sensitive systems and data. Its protection is not only a best practice, it is a fundamental imperative for organizational resilience. The increasing complexity of modern IT environments, exacerbated by rapid cloud migration, has led to a surge in both human and non-human identities, comprising privileged accounts and virtual systems [compute workloads such as virtual machines (VMs), containers, and serverless functions, plus their control planes], significantly expanding the overall attack surface. This environment presents escalating challenges in identity and access management, cross-platform system security, and effective staffing, making the establishment and maintenance of a robust security posture increasingly challenging.
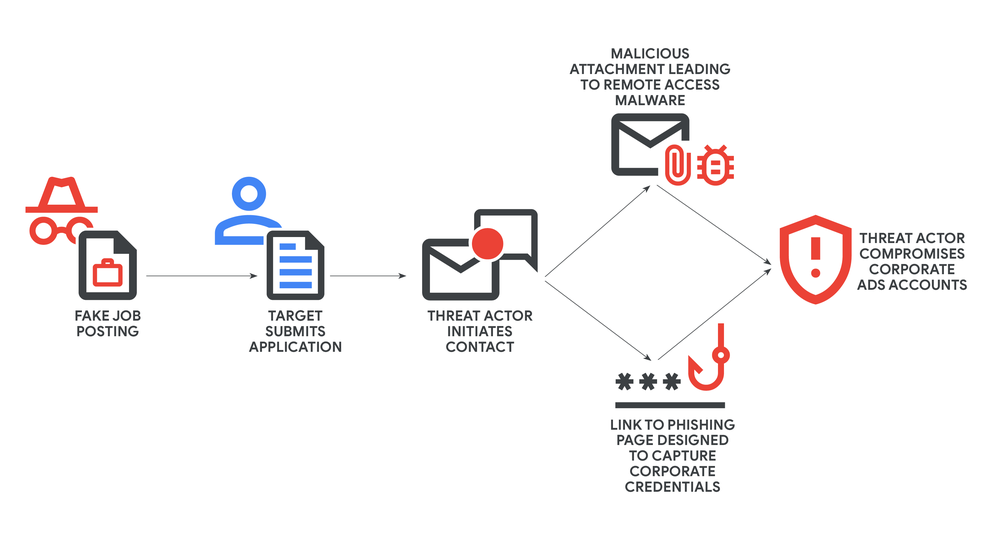
The threat landscape is continuously evolving, with a pronounced shift towards attacks that exploit privileged access. Mandiant's 2025 M-Trends report highlights that stolen credentials have surpassed email phishing to become the second-most frequently observed initial access method, accounting for 16% of intrusions in 2024. This resurgence is fueled, in part, by the proliferation of infostealer malware campaigns, which facilitate the collection and trade of compromised user credentials. However, threat actors of all types have found myriad new ways to compromise identity, including social engineering, which has been on the rise alongside several other tactics, techniques, and procedures (TTPs). ENISA documents criminal use of generative artificial intelligence (AI) for credential-stealing social-engineering and "fraud kits."
Stolen credentials provide not just a high-value vector for initial access during intrusions, but also further enable actors to conduct internal reconnaissance, move laterally, and complete their mission. Compromised credentials, alongside stolen session tokens, social engineering, and other techniques to compromise identity, underscore the critical need for organizations to make identity security one of the foundational pillars of their security posture. Even with advanced perimeter defenses, if privileged credentials are weak or poorly managed, attackers will inevitably find a way into an organization's critical systems. Breaches can be difficult to detect and contain; M-Trends 2025 reports a global median dwell time of 11 days in 2024—5 days when the adversary notifies, 26 days when an external entity notifies, and 10 days when detected internally. A concise defense-in-depth approach is required, where you should assume breach and implement layer controls so failure of one control is caught by the next layer of defense:
-
Verify every request (Zero Trust).
-
Require multifactor authentication (MFA) for all administrative paths.
-
Enforce privileged access management (PAM) with credential rotation and session recording.
-
Administer only from privileged access workstations (PAWs) on a segmented management network.
-
Tune security information and event management (SIEM) for privileged anomalies to reduce dwell time and radius.
Beyond external attacks, organizations face significant risk from account takeover (ATO) and insider activity. Adversaries routinely weaponize stolen credentials and session tokens, while negligent or malicious insiders can move quickly once they have access. In both cases, the trust model is being exploited, and privileged identities are the shortest path to impact.
At the same time, the business impact of breaches continues to rise and third-party exposure remains a frequent entry point. These realities reinforce an assume-breach posture with layered controls that reduce dwell time and blast radius.
This blog post provides recommendations and insights into preventing, detecting, and responding to intrusions targeting privileged accounts. To secure these "keys to your kingdom," Mandiant's strategy is built upon a comprehensive framework of three interdependent pillars:
- Prevention: Securing Privileged Access to Prevent Compromise
- Detection: Maintaining Visibility and Engineering Detections for Privileged Accounts
- Response: Taking Action to Investigate and Remediate Privileged Account Compromise
This blog post serves as a reusable resource, emphasizing practical, threat-informed strategies to secure the most valuable digital assets.
01: Prevention: Securing Privileged Access to Limit Attack Impact
Effective privileged access management begins with an understanding of what constitutes a privileged account and a strategy for securing these critical assets.
Defining Privileged Accounts: Beyond the Obvious
Access is a privilege; every account is a grant of trust. A privileged account is any human or non-human identity whose entitlements can change system state, alter security policy, or reach sensitive data beyond a normal role. Privilege is contextual to role and tier: an entitlement is "privileged" when misuse would cause material impact for that asset. In modern enterprises, this also includes business users with access to sensitive financial or personal data via web apps and developers with cloud-platform access.
The evolving definition of "privileged" directly reflects the decentralization of IT and the rise of cloud-native and DevOps environments. Attackers are no longer solely targeting domain admins; they increasingly focus on developers' workstations, service accounts, and API keys, knowing these give access to systems. This wider scope requires a more complete PAM strategy that covers the entire enterprise, not just traditional IT. The definition must also cover non-human accounts, such as service accounts, application accounts, and API keys. These are prime targets in real compromises because they hold broad access, yet are less monitored than human accounts. A PAM strategy that only focuses on human domain admins is incomplete and leaves attack surfaces open. Therefore, maintain a single inventory that classifies every human, service, and API account by business impact and maps each to a role with least-privilege entitlements—owner, purpose, systems touched, permitted actions, tier (T0/T1/T2), allowed pathways (PAW/jump), and Segregation of Duties (SoD) constraints—with quarterly attestation in the identity and access management (IAM) source of truth.
Categorizing and Tiering Privileged Accounts and Dependencies
Many organizations struggle with a broad and unclear understanding of "privileged accounts," limiting their focus to only domain admins or global admins. This narrow view overlooks the dependencies on which those accounts rely. Mandiant's Identity Security Modernization Engagements offer principles for better defining and categorizing privileged accounts beyond these views. These assessments help identify and reduce the number of accounts with highly privileged roles. This includes accounts or groups with permissions for modifying Group Policy Objects (GPOs), explicit permissions on domain controllers (DCs) or Tier-0 endpoints, privileged roles for virtualization platforms, and permissions to run processes as SYSTEM on many endpoints.
Dependencies often overlooked include jump servers, management workstations, specific network segments, applications, and continuous integration and continuous delivery/deployment (CI/CD) pipelines. "Trusted Service Infrastructure" directly addresses these dependencies, including management interfaces for asset and patch management tools, network devices, virtualization platforms, backup technologies, security tooling, and PAM systems themselves. Attackers target these components for persistence and lateral movement, knowing that compromising them can give broad control over an environment.
"Tiering" is key for PAM. It moves beyond a flat "privileged" versus "non-privileged" view by categorizing accounts based on compromise impact and their dependencies. For example, an account that can access a Tier-0 asset (like a domain controller) or the infrastructure supporting it (e.g., a jump server) poses a higher risk to the operation. Overlooking these dependencies means that even if a "privileged" account is secure, the less-secure system used to access it can become the weakest link. This shows the need for a holistic security approach that extends PAM controls to the entire "privileged access pathway," ensuring controls are layered across identities, endpoints, networks, and applications. The context of access—from where, when, and how—becomes as important as the identity itself.
Common Privileged Account Categories and Critical Dependencies
|
Category
|
Examples
|
Critical Dependencies
|
Criteria for Privileged Roles
|
|
Human accounts
|
Domain administrators, local administrators (Linux/Unix), business users, developers
|
Jump servers, management workstations, critical networks, CI/CD pipelines
|
Default privileged roles, GPO modification permissions, explicit permissions on DC, local admin access
|
|
Non-human accounts
|
Service accounts, application accounts, API keys
|
Asset management tools, network management tools, virtualization platforms, backup technologies, security tooling, PAM systems
|
Accounts or groups with permissions to invoke processes as SYSTEM on a large scope of endpoints
|
Establishing a PAM Foundation
A PAM program is not built overnight; it is a journey that progresses through distinct phases, each building upon the last to systematically reduce risk and enhance security posture.
The PAM Maturity Journey
Effective privileged access management adoption is an evolutionary process through levels of maturity. These levels build on each other, reducing risk and improving security. Mandiant sees four stages: Uninitiated, Ad-Hoc, Repeatable, and Iterative Optimization. As an organization moves through these stages, its protection covers more types of privileged users, sensitive systems, and their accounts.
Uninitiated. Privileged access sits largely uncontrolled: manual account creation, spreadsheet tracking, shared credentials, weak/absent MFA, loose password policy, and missed deprovisioning. Service/API accounts appear without owners or documentation. Security lacks a full map of privileged pathways and Tier-0 assets—high cyber risk by default.
Ad-Hoc. First risk reductions begin: a subset of shared credentials gets vaulted/rotated; a few guardrails appear. Operations stay reactive, tools remain fragmented, role/tier separation is limited, reporting and attestation is difficult. PAM exists as point solutions rather than a program.
Repeatable. Controls become consistent and broad. PAM covers business users, developers, third parties, servers, workstations, and software-as-a-service (SaaS). Role-based access control (RBAC) standardizes access; MFA is on all admin paths; local-admin rotation (e.g., Local Administrator Password Solution [LAPS]) is in place; PAWs for Tier-0/1; just-in-time/just-enough-administration (JIT/JEA) introduced; change control and ticketing integrated. Scheduled discovery, classification, role mapping, and quarterly attestation create a dependable operating rhythm.
Iterative Optimization. Automation and analytics drive continuous improvement. Full lifecycle orchestration—provision → approve/JIT → session oversight → auto-rotate → deprovision—runs end-to-end. SIEM / extended detection and response (XDR) / security orchestration, automation, and response (SOAR) detect and contain privileged anomalies. Human standing privilege trends toward zero; service/API identities move to group Managed Service Account (gMSA)/managed identities; dual-control on vault release; break-glass tested; controls validated through red/purple-team exercises. PAM is woven through IT and DevOps, reinforcing defense-in-depth so failure of one layer is caught by the next.
Implementing a Dedicated PAM Solution
A key step in building a strong PAM foundation is implementing a dedicated privileged access management solution (e.g., CyberArk, BeyondTrust, Delinea). Onboarding all privileged accounts into a centralized PAM system provides visibility into who accesses which credentials and from where. Leading PAM tools discover, vault, and manage credentials; enforce security policies (like checkout approvals and one-time passwords); and log all privileged activities for audit. For cloud control planes, pair your PAM with cloud-native PIM/JIT services (e.g., Google Cloud Privileged Access Manager, Microsoft Entra ID PIM) to grant time-bound elevation rather than standing admin rights. This greatly reduces the risk of unmanaged, ad hoc credential use.
However, simply deploying a PAM product is not enough—PAM must be treated as an ongoing program with defined policies and ownership. The organization should establish central governance and processes around privileged access: enforce tiered account structures, require multifactor authentication for all admin access, and mandate least privilege. Pair top-down role design with bottom-up discovery. Governance must also audit effective permissions at the resource level (access control lists [ACLs] on data stores, app/database (DB) roles, SaaS admin scopes, cloud IAM policies) to surface shadow admins—accounts that do not appear privileged in directory groups but can fully control sensitive resources (e.g., HR/finance datasets). Feed these findings into tier mapping and PAM onboarding so those identities are either right-sized to least privilege or brought under PAM with JIT/JEA and session oversight. Scheduled entitlement discovery can be done via identity governance and administration (IGA) / cloud infrastructure entitlement management (CIEM) or dedicated entitlement-analysis tools as well as native exports from the platforms themselves.
Having a PAM tool does not automatically mean you are "doing PAM." Many organizations park credentials in a vault yet fail to align with a tiered model or manage a full identity lifecycle. PAM must live inside a broader governance program. In practice, classify assets and platforms, map each privileged identity to that classification, then configure the tool to enforce policy (password rotation cadence, session recording, JIT/JEA, approvals, network restrictions). With that context, PAM simplifies the complexity by tying process to technology, turning policy into consistent, auditable controls. Run scheduled resource-permission crawls and reconcile deltas (new owners, new admin scope) back into the PAM inventory and approval workflows.
Properly implemented, a PAM solution yields many benefits: centralized insight into privileged access patterns, automated password management (eliminating hard-coded or stale credentials), and real-time alerting on suspicious behavior. Without such automation, managing thousands of privileged accounts manually is error prone and high risk. PAM tools mitigate human error by enforcing consistent policies and reducing reliance on individual administrators. They also integrate with monitoring systems (or built-in analytics) to flag anomalous admin activities. Organizations still relying on spreadsheets or disparate teams to manage admin passwords face scalability limits and blind spots. A dedicated PAM system, combined with strong processes, closes these gaps.
Considerations for Self-Managed PAM Initiatives
While a dedicated PAM solution is best for security and efficiency, organizations may manage some PAM aspects themselves, especially in earlier stages or for niche needs. If an organization undertakes a self-managed PAM initiative, these factors must be accounted for:
-
Manual Inventory and Tracking Overhead: Without automated discovery tools, keeping an accurate, up-to-date inventory of all privileged accounts (human and non-human, including application accounts, especially in finance organizations) becomes a large, error-prone, manual effort. This includes tracking permissions, dependencies, and owners across systems.
-
No Centralized Visibility: Separate manual processes lead to fragmented visibility. Combining logs from various sources (operating systems, applications, network devices) and correlating privileged activity for a unified view is hard without a central system (like a SIEM).
-
Inconsistent Policy Enforcement: Manual policy enforcement (e.g., password complexity, rotation, least privilege) across many privileged accounts is prone to human error and inconsistency, leading to security gaps.
-
Scalability Limits: Manual PAM processes do not scale. As privileged accounts grow, management overhead becomes too much, affecting security and operations.
-
Slower Incident Response: Without automated detection, real-time alerting, and integrated response, finding and containing a privileged account compromise will be slower, increasing dwell time and damage.
-
Higher Risk of Human Error: Manual management increases misconfigurations, forgotten deprovisioning, and accidental or coerced credential exposure, all leading to security incidents.
-
Compliance Burden: Showing compliance with regulations (e.g., PCI DSS, NIST) for privileged access becomes a laborious, manual audit process without automated reporting and session records.
-
Application-Specific Privileged Accounts: Applications, especially in finance, need attention to ensure they are managed with accounts that follow least privilege, rather than standard corporate accounts. This needs a detailed understanding of application roles and privileges.
-
No Bottom-Up Entitlement Discovery: Without resource-level audits of effective access, "shadow admin" rights remain invisible, leaving PAM scope incomplete and high-impact accounts unmanaged.
Organizations starting a self-managed PAM journey must know these limits and be ready to invest much manual effort and accept a higher risk than with a purpose-built PAM solution.
Hardening Critical Infrastructure and Credentials
Strong PAM needs hardening around it. Reduce privileged credentials to the minimum, lock down those that must exist, and restrict where/when they can operate. Treat the full credential lifecycle—creation, storage, use, rotation, retirement—as a control surface. Even if a password or token leaks, tight hardening should keep it noisy, short-lived, or useless.
Secure Administrative Access Paths (RDP, SMB, WinRM)
Admin pathways are prime lateral-movement rails. Collapse them into monitored, gated channels.
-
No direct exposure: Block Remote Desktop Protocol (RDP) / Secure Shell (SSH) from the internet. For remote admin, force access through PAWs or jump hosts with MFA and bastion logging.
-
Segregate management networks: Only PAWs and PAM session managers reach server admin interfaces; deny user subnets by default.
-
Protocol hygiene: Enforce Server Message Block (SMB) signing; prefer Kerberos; phase down NTLM; disable default admin shares (e.g., ADMIN$) where operationally viable.
-
WinRM/RDP hardening: Enforce encrypted Windows Remote Management (WinRM) always (AllowUnencrypted=0). In Active Directory (AD)-joined scenarios using Kerberos/Negotiate, WinRM over HTTP already provides message-level encryption; still prefer HTTPS to add TLS, server certificate validation, and for non-domain/cross-forest use. Require HTTPS for Basic auth, workgroup hosts, or any untrusted network path. Restrict to approved admin groups and endpoints; disable CredSSP unless explicitly required. For RDP, enable Network Level Authentication (NLA), limit access via firewall rules/GPO, and log via bastions/PAM session managers.
-
Broker sessions: Use PAM session management for high-risk systems (Tier-0/1) with keystroke/command capture and real-time termination.
Endpoint Security Controls (Least Privilege and Unknown-Code Execution)
Stop unapproved tools and script abuse on machines admins touch (endpoint privilege management [EPM]).
-
Least privilege by role: Remove local admin from user workstations; perform admin tasks only from PAWs.
-
Application control: Enforce WDAC/AppLocker allow-lists; block unsigned and unknown binaries; restrict PowerShell to Constrained Language Mode; enable AMSI + Script Block Logging.
-
Protect secrets on the host: Turn on Credential Guard/LSA Protection (RunAsPPL); disable legacy caches (e.g., WDigest); prefer AES-only Kerberos; shorten Ticket-Granting Ticket (TGT) lifetimes for admin roles.
-
Baseline + EDR: Apply CIS/Microsoft baselines via GPO/MDM; require endpoint detection and response (EDR) with tamper protection, USB/device control, and quarantine actions.
-
Classify by tier: Mark PAWs/jump hosts as T0/T1, workstations as T2, and enforce stronger baselines and update rings for higher tiers.
Credential Protection and Usage Hardening
Even when privileged accounts exist, we can limit their exposure and utility to attackers. Enforce technical controls such as:
-
Block Credential Reuse on Endpoints: Prevent privileged domain accounts from logging into standard user workstations. Administrators should use separate admin accounts only on admin systems (tiered access model). If a privileged credential is never used on a low-security machine, malware on that machine cannot steal it. Similarly, for local administrator accounts, disallow remote use (e.g., via Group Policy restrictions on those accounts' Security Identifiers [SIDs]) to stop lateral movement. Use Microsoft LAPS, CyberArk Loosely Connected Device (LCD) (feature designed to manage and rotate credentials for endpoints, regardless of their connection to the corporate network or Active Directory), or equivalent to ensure each machine's local admin password is unique and regularly rotated.
-
Service Account Restrictions and Residency: Define explicit residency for every service/API account, and which hosts, networks, and tiers they can run on. On Windows, prefer gMSA and restrict which computers may retrieve/use the credential via PrincipalsAllowedToRetrieveManagedPassword; grant "Log on as a service" only on those hosts; deny interactive and RDP logon everywhere; limit network logon as required. Use Kerberos constrained or resource-based constrained delegation only to named backend services; avoid unconstrained delegation. Residency boundaries enforce least privilege, prevent credential spread, and make misuse obvious in logs.
-
Memory and Credential Cache Protections: On Windows (Domain Member) systems, enable features like Protected Users group membership for admins (which disables legacy authorization protocols and forces Kerberos, etc.)—though do not apply this to service accounts, which may break if subject to those restrictions. Disable WDigest authentication and other settings that might keep credentials in memory in plaintext. These measures ensure that even if malware lands on a system, it is harder to scrape credentials from memory (Local Security Authority Subsystem Service [LSASS]). Reducing the "live" presence of passwords and tickets closes off common credential theft techniques (pass-the-hash, ticket reuse).
These hardening steps illustrate a mindset: even if privileged credentials exist, make them hard for attackers to capture or use. By reducing where they reside and how long they remain valid, you decrease the value of a stolen credential. This directly reduces an attack's impact, forcing attackers to spend more effort or give up.
Minimize Standing Privileges
An emerging best practice is to reduce the number of privileged accounts that exist with always-on rights. Instead of giving every administrator their own always-privileged user account, consider a model of ephemeral or checked-out privileges. For example, a team of 10 admins may not need 10 separate domain admins active at all times. Using PAM, you could maintain a small pool of privileged accounts that admins check out when needed (one-at-a-time, with unique login tracking for accountability) and that get automatically locked or rotated afterward. Many PAM solutions support "exclusive access" or one-time password checkout, ensuring no two people use the same shared account simultaneously and every action is tied back to an individual.
This approach shrinks the attack surface by having fewer privileged credentials in existence. It also enforces discipline—admins must go through the PAM process to get access, which is logged and monitored. While shared accounts are generally risky, with strict PAM controls (per-user checkouts, full session recording, and audited approvals) they can be used in a way that preserves accountability while limiting credential proliferation.
The goal is zero standing privilege: no one has permanent admin rights unless actively approved and in use. Just-in-time administration (discussed later in this post) is a related concept that achieves this by granting rights only when needed.
Secrets Management
For highly sensitive secrets—master encryption keys, signing certificates, cloud API keys, etc.—organizations should use dedicated secret management systems (often termed "key vaults"). A key vault (whether services like Azure Key Vault, HashiCorp Vault, or CyberArk's Identity Security Platform) is a hardened repository that securely stores secrets and tightly controls their access. The vault becomes the single source of truth for sensitive credentials, enabling fine-grained access control, auditing, and automated rotation from one central point. This reduces the risk of secrets sprawl (e.g., passwords stashed in configuration files or plaintext) and helps prevent unauthorized access to critical secrets.
When we say "secrets management," we refer to the general practice of centralized secrets management, not a specific product. For example, Azure Key Vault, Amazon Web Services (AWS) Key Management Service (KMS) / Secrets Manager, Google Cloud KMS, or a third-party vaulting tool all serve a similar purpose. The key is that these systems are purpose-built to protect secrets through strong encryption, access control, and monitoring.
Key considerations for effective secrets management include:
-
Hardware Security Module (HSM): Integrate key vaults with HSMs as they provide a tamper-resistant environment for cryptographic operations and key storage, protecting keys from logical and physical attacks.
-
Least-Privilege Access: Only authorized users or automated processes should be able to retrieve or manage secrets, and access should be granted on a just-in-time, just-enough basis.
-
Auditing and Monitoring: Implement comprehensive logging and monitoring of all access to and operations within the key vault. Integrate these logs with your SIEM (e.g., Google SecOps) to detect anomalous behavior and unauthorized access attempts in real time.
-
Automated Rotation and Lifecycle Management: Automate the rotation of secrets stored in the key vault to reduce the impact of any potential compromise. This includes automated certificate renewals, API key rotations, and password changes for managed accounts. The key vault should manage the entire lifecycle of secrets, from creation to destruction.
-
Geographical Dispersion and Redundancy: Deploy key vaults in a highly available and geographically dispersed architecture to ensure business continuity and disaster recovery.
-
Segregation of Duties: No single individual should have complete control over all aspects of the key vault.
-
Secure Backup and Recovery: Establish secure, offline, and encrypted backup procedures for the key vault itself. This ensures that even in a worst-case scenario, critical secrets can be safely restored.
Segregation of Duties and Tiered Access for Secrets Management: Robust Credential Security
Segregation of Duties (SoD) is a security cornerstone: no single individual controls critical processes. For key vaults, housing sensitive cryptographic keys, privileged credentials, SoD is vital.
SoD Imperative in Secrets Management
SoD prevents fraud, errors, and malicious activity by distributing control over critical processes so no single individual can act unilaterally. For key vaults, this prevents a single point of failure and mitigates the risk of insider threats and external attacks that exploit stolen credentials. Without SoD, a single compromised account could grant an attacker unfettered control, leading to immediate data exfiltration.
SoD proactively defends against cyberattacks by "decompressing" the attack pathway. Attackers use stolen credentials to bypass initial access defenses, but SoD fragments the control over a key vault, so even if one person's credentials are breached, the attacker lacks the full permissions needed to compromise the vault completely. This increases the complexity and time needed for an attack, making it easier to detect.
SoD deters malicious activity by ensuring accountability. When administrators know their actions are subject to forensic auditing, they are less likely to misuse their access. This architecture makes malicious activity more difficult, reduces human error, and fosters shared vigilance. By forcing privileged actions through approved, dual-controlled paths, the design makes unauthorized tradecraft noisy and easy to spot—attempts outside sanctioned workflows fail fast and alert.
Tiered Access Control for Key Vaults
Enforce tiering inside PAM and vault workflows. Treat the vault, PAM components, identity provider (IdP), and admin workstations as Tier-0 control planes. Permit Tier-0 identities only on Tier-0 systems; block cross-tier logons; require PAWs for Tier-0; isolate management networks so lower tiers cannot reach them. Make dual-control the default for vault release and role changes; ensure all break-glass paths are audited. Encode this in PAM: dedicated Tier-0 roles, approval chains, session isolation. Validate in SIEM: vault access, policy edits, role elevation, key retrieval.
Administrative Silos Per Tier
Build discrete silos for T0, T1, and T2. Separate admin groups, PAWs, credential stores, management tooling, logging, and network segments. No shared hosts, no shared identities, no shared jump paths across silos. Deny-by-default between tiers; allow only vetted, one-way orchestration flows.
Tier Controls that Protect Tiers from Each Other—and Themselves
-
Cross-tier protections: Block interactive logon from lower to higher tiers; restrict credential injection and token reuse; require JIT elevation with time bounds; enforce change windows and peer approval for T0 actions.
-
Intra-tier firebreaks: Session recording with command risk scoring; rate-limit or pause high-impact operations; require two-person integrity for destructive changes (key purge, policy delete); automatic rollback checkpoints for T0 policy edits.
Tier Definitions
-
T0 (crown-jewel control plane): AD domain controllers; cloud IdP tenants (Microsoft Entra ID, Okta, Ping); cloud management planes and root roles (AWS IAM/root, Azure management groups/subscriptions, Google Cloud org/projects), Kubernetes control plane; PAM infrastructure; secrets/key services (CyberArk Vault, HashiCorp Vault, Azure Key Vault, AWS KMS/Secrets Manager); public key infrastructure (PKI) / certificate authority (CA) and CI/CD orchestrators.
-
T1: Core business platforms (critical apps, databases).
-
T2: Workstations, lower-impact servers. Key vaults are unequivocally T0.
Tiering must extend across the entire privileged pathway—identities, endpoints, networks, and applications that touch the vault—in both on-premises and cloud environments so a weak hop cannot bypass controls. SoD + tiering work together: tiering sets asset criticality and isolation boundaries; SoD fragments authority so no single operator can subvert Tier-0. Net effect: PAM encodes and enforces the enterprise tier model for every vault operation, while monitoring, approvals, and session isolation keep even the most privileged actions accountable and recoverable.
Advanced PAM Capabilities: JIT and JEA (Just-In-Time / Just-Enough-Access)
Modern PAM programs are increasingly adopting just-in-time (JIT) access and just-enough-access (JEA) models to enforce least privilege dynamically. These approaches aim to eliminate standing high-level access and only grant privileges when and to the extent needed.
Just-Enough-Access (JEA). Constrain privilege to the exact commands required for the task—nothing more. Example: instead of making a helpdesk user a domain admin, expose a PowerShell JEA endpoint that can only unlock accounts. JEA forces least privilege per command, produces high-fidelity logs, and blocks actions outside the allowed scope by design.
Application Control / EPM as the runway to JEA. Before or alongside JEA, apply application allow-listing and per-process elevation so only approved binaries run and only approved binaries can receive elevation. Concretely: WDAC/AppLocker on Windows, sudoers and signed-binary policies on Linux/macOS, or endpoint privilege management (e.g., CyberArk EPM) to elevate a specific installer/tool without giving the user local admin. This shrinks the privilege surface on endpoints and makes the later jump to JEA much smoother.
Just-In-Time (JIT) Access. JIT focuses on time-bound privilege elevation. Instead of an account having 24x7 admin rights, it can be configured so that admin privileges can be activated for a short window when needed, often requiring approval. For instance, a cloud administrator might not normally have the Owner role on a production subscription, but through a privileged identity management (PIM) service (like Microsoft Entra ID PIM or CyberArk Secure Cloud Access), they can request that role, and upon approval it is granted for one or two hours and then removed automatically. JIT ensures that even if an account's credentials are stolen, an attacker cannot do anything privileged with them unless they happen to steal it during an active privileged window (which is unlikely). It minimizes the duration of elevated access, cutting off opportunities for abuse.
Zero-Standing Privilege (ZSP). Target state: no human holds always-on admin rights. Access requires an approved request, step-up MFA, and either (a) time-bound role assignment or (b) an ephemeral token/credential. Session recording and command controls run by default. ZSP combines JEA (scope) + JIT (time) + strong approvals, making privilege both temporary and tightly bound.
App control/EPM prevents unknown tools from running; JEA restricts allowed actions; JIT/ZSP removes 24×7 rights; secure web sessions capture and deter misuse. Together they reduce blast radius, raise attacker friction, and generate auditable evidence for every privileged step.
Hardened Access Pathways
Restricting access to key vaults via hardened pathways is critical. Organizations should use PAWs or jump servers, which are highly secure, segmented systems used exclusively for privileged administrative tasks. This prevents attackers from moving laterally from a compromised, less-secure workstation to a high-value Tier-0 asset.
Hardening common lateral movement protocols like RDP, SMB, and WinRM is also vital. This includes disabling administrative shares, avoiding direct internet exposure, and enforcing MFA for RDP sessions. These measures contain a compromise even if initial access is gained.
Automated Credential Management
Automated secret rotation (for passwords, SSH keys, API keys, and certificates) is vital for reducing the window of opportunity for attackers. This automation is a form of SoD, as it removes the human element from handling sensitive credentials, minimizing accidental exposure or malicious manipulation during rotation. Dedicated PAM solutions can automate this process at scale, ensuring consistent policy application and reducing the "privilege of knowledge" by limiting how long any human needs to know a sensitive secret.
Dual Authorization and Approval Workflows
The "four-eyes" principle, or dual authorization, is a direct and stringent application of SoD. It requires a second or more, independent approval for high-impact actions within a key vault, such as retrieving a master encryption key or modifying critical policies. This ensures no single individual can perform a potentially irreversible action without independent verification, raising the bar for attackers and malicious insiders.
Monitoring and Auditing
Collect comprehensive logs from vault/PAM (checkouts, policy edits, session telemetry), IdP sign-ins, PAWs/jump hosts, EDR, and network controls. Correlate and aggregate these streams in the SIEM (e.g., Google SecOps) to build a single privileged-activity timeline. Combine analytics with context/assurance signals (device trust, geographic risk, user risk) to score events. Let automation auto-contain clear cases (suspend token, rotate secret), and surface in-role but abnormal activity to humans with the correlated context needed for fast decisions beyond automation.
These monitoring capabilities are also critical for compliance. Many regulatory frameworks, such as PCI DSS and NIST SP 800-53, mandate detailed auditing of all actions taken by individuals with administrative privileges.
02: Detection: Maintaining Visibility and Engineering Detections for Privileged Accounts
Distinguishing Privileged Account Monitoring from Normal IAM Abuse
Basic security tooling misses privileged misuse. Firewalls, simple intrusion detection systems (IDS), or SIEMs used as raw-log buckets give a flat view with little actor intent, leaving audit gaps. Close those gaps with defense-in-depth observability: collect high-fidelity, user-centric signals across control planes and correlate them—PAM vault checkouts, elevation/approval workflow events, session transcripts/commands, IdP sign-ins and Conditional Access outcomes, PAW posture, EDR process trees, network flows, change/configuration logs, and ticket metadata. Tie each privileged action to who/what/when/where/why/how, then apply behavioral analytics to flag authorized but abnormal use, verify dual-control, and automatically kill sessions, revoke tokens, or rotate secrets. On the defender side, organizations that deploy security AI/automation see materially better outcomes. IBM's study reports ~USD $2.2M lower average breach costs and a shorter breach lifecycle—reinforcing the need for automated detections.
Key differences vs. normal IAM abuse:
-
Observation depth. Privileged activity demands Who, What, When, Where, Why, and How context captured from the aforementioned user-centric signals for both real-time and post-event assessment.
-
Impact-first triage. Prioritize by asset tier and action impact rather than "detect-all" volume.
-
Authorized-abuse focus. Validate approvals and scope; alert on mismatches in approver, time, device, or target.
-
Analytics + response. Combine PAM telemetry with identity threat detection and response (ITDR) and User Entity Behavior Analytics (UEBA) in SIEM/XDR to drive automated containment (session terminate, token revoke, secret rotation).
Key Distinctions: Privileged Account Monitoring vs. Normal IAM Abuse
|
Criteria
|
Privileged Account Monitoring
|
Normal IAM Abuse Monitoring
|
Shortcomings of Traditional Tools
|
|
Granularity
|
High-fidelity, user-centric context (screen, keystrokes, metadata)
|
Basic event logs; general access attempts
|
Incomplete picture, lack of detail, scattered events
|
|
Impact of Compromise
|
Disproportionately high impact (financial, operational, reputational)
|
Lower/variable impact; general threat detection
|
Fails to differentiate critical from non-critical events effectively
|
|
Contextual Understanding
|
Deep understanding of intentions/impacts; behavioral analysis
|
Focus on basic access patterns
|
No user-centric context; difficult interpretation
|
|
Compliance Requirements
|
Strict regulatory demands (PCI DSS, NIST, etc.)
|
Broader compliance; general logging
|
"Audit gap" where traditional logs do not meet detailed requirements
|
|
Insider Threat Mitigation
|
Primary focus for insider threat mitigation (malicious or negligent)
|
General threat detection; less specific focus on insider misuse
|
Cannot effectively identify subtle insider misuse
|
Engineering Specific Detections and Hunts
To monitor privileged accounts, organizations must move beyond static, rule-based detections to dynamic, intelligent approaches, including behavioral analytics with machine learning.
Generalized Detections for Anomalous Behavior
SIEM anomaly detection constantly monitors and analyzes data from network sources to establish a normal behavior baseline. Any deviation, like unusual login times, unexpected data transfers, or access by unfamiliar users, is flagged as an anomaly. Machine learning is at the heart of modern SIEM anomaly detection, letting the system learn from vast data, adjust baselines as the network changes, and find complex patterns across data sources. This finds subtle, low-and-slow attacks typical of threat actors. For instance, a system might detect a privileged user suddenly accessing new resources or acting outside their usual hours. While individual actions may seem harmless, their combination can show compromised credentials or insider misuse, which traditional rules might miss.
Nuanced Brute-Force Monitoring
Not all brute-force looks equal. Tune sensitivity by target impact and identity legitimacy. Deprioritize sprays at low-risk users; treat attempts against super admin/root, PAM/vault, secrets management, IdP break-glass, and cloud control planes as high-severity. Go beyond failure counts: classify the campaign by username quality (invalid-name ratio → enumeration; high valid-name ratio → likely stolen list), technique (spray vs. stuffing vs. targeted), MFA outcomes, lockout/rate-limit evasion, and source reputation. Correlate with role catalogs and allowed activity for that role: a spray that yields a success on a Tier-0 identity followed by atypical actions (token creation, role elevation, policy edits) signals compromise. Suppress noise by allow-listing approved scanners and pen-test windows; require change-ticket or source-IP tags to mark "legit testing." Drive a risk score per campaign that blends target tier, username legitimacy, success events, and post-authorization behavior, then trigger automated response (step-up auth, session kill, account disable, secret rotation) only for high-risk series.
Privileged Session Monitoring and Auditing
For privileged activity, high-fidelity session capture (screens, keystrokes/commands, metadata) provides intent and impact at review time, detects insider misuse, and proves compliance. Feed session telemetry to SIEM/XDR and Privilege Threat Analytics/ITDR to enrich with risk factors: asset tier, origin/device trust, time, approval chain, command rarity, data movement. Link sessions to brute-force outcomes and dual-control artifacts (who requested, who approved). Use analytics to auto-summarize what mattered (privilege elevation, new tokens/keys, policy changes, lateral pivots) and assign a risk score so investigators can triage fast; auto-action when thresholds are crossed (terminate session, revoke tokens, rotate credentials). This keeps reviews focused on abnormal behavior while preserving full evidence for forensics.
Specific Detections and Hunts (Examples)
When engineering detections and hunts for privileged accounts, focus on high-impact behaviors and unusual patterns, covering human and non-human privileged entities.
-
Credential Exposure: Look for account lockouts or unexpected password resets, more login attempts on multiple services, logins from new devices or unfamiliar locations, multiple accounts accessed by the same device or IP address, uninitiated changes to account settings (e.g., recovery emails, security questions), and the use of emulators or virtual machines.
-
GPO Modifications: Detect Group Policy Object (GPO) modifications by checking Security event logs on domain controllers for Windows Security Event ID 5136. "Audit Directory Service Changes" must be on. Watch for modifications of GPOs like the Default Domain Policy or scheduled task additions via GPO.
-
Trusted Service Infrastructure Activity: Detect authentications and activities within platforms like asset and patch management tools, virtualization platforms, and security tooling.
-
Virtualization Infrastructure: Ensure centralized SIEM/logging platforms capture authentication, authorization, access events, and configuration changes for virtualization platforms. Baseline these events, then alert on any access where privileged identities are used.
-
Privileged Service Account Behavior: Keep an inventory of where and when privileged service accounts log on and create detections for any activity outside these baselined parameters. This is key for applications, especially in finance, that might be managed by service accounts. Detections should flag if a service account used for a financial application tries to access a different application, or logs in from an unexpected host.
-
Threat Hunting: Do regular, proactive threat hunting to find compromise evidence missed by existing detections. This also helps find visibility gaps and build new detection uses.
-
Compliance-Driven Auditing: Follow industry standards and regulations. PCI DSS requires auditing all actions by root or administrative privileges, and invalid logical access attempts. NIST SP 800-53 requires session audits at system start-up, user session content capture, and real-time viewing of user sessions.
By providing these detection examples, organizations can improve security. Linking detections to compliance standards adds a mandatory reason for implementation. Inventorying and monitoring service accounts, a common hurdle, can also be addressed.
Sample Detections for Privileged Account Activity
|
Detection Category
|
Specific Activity/Indicator
|
Potential Threat
|
Recommended Action (Google SecOps)
|
|
Anomalous Login
|
Login of a privileged account from a new geolocation or unusual IP address
|
Account Takeover, Compromised Credential
|
High-severity alert, automated account suspension
|
|
High-Impact Brute-Force
|
Rapid failed-login burst to a Tier-0 admin from one origin fingerprint (same IP, device/hostname, ASN/geo, user-agent) within minutes
|
Account Takeover, Credential Stuffing
|
Critical alert, force password reset, automated account lockout
|
|
Credential Exposure
|
Uninitiated password reset or account setting change on a privileged account
|
Account Takeover, Insider Threat
|
High-severity alert, trigger forensic investigation playbook
|
|
GPO Modification
|
Windows Security Event ID 5136 on domain controller for modification of Default Domain Policy or addition of a scheduled task
|
Ransomware Deployment, Lateral Movement, Persistence
|
Critical alert, automated GPO rollback (if feasible), immediate investigation
|
|
Privileged Service Account Anomaly
|
Privileged service account login or activity outside of baselined hours or on unapproved systems
|
Lateral Movement, Insider Threat, Compromised Service Account
|
Medium-to-high severity alert, automated account suspension/disablement
|
|
Trusted Service Infrastructure Access
|
Unusual authentication or activity within asset/patch management tools, virtualization platforms, or security tooling
|
Privilege Escalation, Command & Control, Data Exfiltration
|
High-severity alert, isolate source system, initiate threat hunt
|
Leveraging Google SecOps for Enhanced PAM Visibility
Google SecOps, especially its SOAR capabilities, serves as a central nervous system for privileged account monitoring. Its ability to ingest and analyze data from various sources is key for PAM.
Centralized Aggregation and Analysis
Google SecOps integrates with PAM solutions (e.g., CyberArk, via Syslog ingestion) and infrastructure logs (like Google Workspace activity). This allows central data aggregation and analysis, addressing "scattered events" and "incomplete pictures" from traditional logging. Once ingested, Google SecOps maps fields to a unified data model (UDM), enriching data with context and standardizing event types. This normalization is key, allowing cross-platform correlation and a unified view of privileged account activity across the enterprise. This aggregation and normalization overcome disparate log source limits, enabling better anomaly detection and threat hunting that might otherwise be impossible.
Automated Detection and Response Workflows
PAM data integration with Google SecOps' SOAR enables automated response workflows. This addresses the need for fast action when privileged accounts are compromised. Google SecOps can trigger automated workflows for actions like revoking access, suspending accounts, or granting temporary access for incident response. When a PAM solution, integrated with the SIEM, detects deviations from a baseline, it can alert and then initiate actions like rotating compromised credentials or enforcing MFA to contain attacks.
This automation means that upon detecting a high-severity anomaly (e.g., a brute-force attempt on a super admin account), Google SecOps can automatically initiate containment, reducing manual Security Operations Center (SOC) effort and attacker opportunity. This shifts security from reactive alerting to proactive, automated defense. Automating containment, like suspending a compromised account or forcing a password reset, reduces "SOC effort" and "impact," letting human analysts focus on investigation rather than initial containment. Google SecOps is a key enabler for a mature, efficient PAM program that detects and responds to threats fast, improving security.
03: Response: Taking Action to Investigate and Remediate Privileged Account Compromise
Even with prevention and detection, organizations must be ready for a privileged account compromise. Response speed and thoroughness dictate incident impact.
Tactical Hardening and Positioning During an Incident
Prepare before an incident: Map every service account to owner and workload, run continuous discovery cycles (using PAM discovery/scanning tools) to find systems and credentials, and onboard all human and non-human privileged identities into PAM; enforce unique credentials, MFA, and API-based rotation; migrate Windows services to gMSA / standalone Managed Service Account (sMSA) and block interactive logon for service accounts; create pre-approved, tested runbooks for bulk rotation, quarantine, and vault/IdP audit escalation; store break-glass credentials offline with dual-control retrieval and immutable logging; secure executive sponsorship for Tier-0 ownership and cross-team responsibilities (platform, app, IAM, PAM).
Immediate isolation: Pull suspected admin workstations off the network; restrict east-west to Tier-0; in cloud, revoke refresh tokens and active sessions, then force re-authorization. For vaults/IdP/DCs showing anomalous activity, sever untrusted network paths, keep console access for responders, and snapshot logs/state before change. Raise audit levels on targets (operating system [OS], IdP, vault, PAM) to capture follow-on actions for forensics.
Credential resets: Coordinated, not piecemeal. Use PAM to bulk-rotate human + service secrets once initial containment stabilizes. Close a common gap by onboarding service accounts comprehensively, blocking interactive logon, mapping each to an owner/workload, and attaching to rotation workflows. For Windows services, migrate to gMSA/sMSA to gain automatic, frequent password changes with no human handling; for non-Windows/app credentials, store in PAM and rotate via API. This yields rapid, low-friction resets without tipping the actor.
Break-glass that actually works: Maintain offline, tightly held emergency access for Tier-0 (e.g., local admin on vault/DC, offline DA credential) with dual-control retrieval, immutable logging, and post-use rotation. Drill these paths routinely.
Incident response (IR) support: Engage internal IR plus an external partner early for memory capture, log triage, and containment strategy while platform teams sustain core services. (IR playbooks should already assume the aforementioned Tier-0 model to avoid re-exposure during response).
Effective Investigation and Remediation
Investigation for privileged account compromise must be holistic, combining forensic analysis with understanding how privileged access is abused. This shows the need for logging and monitoring setup in the detection phase.
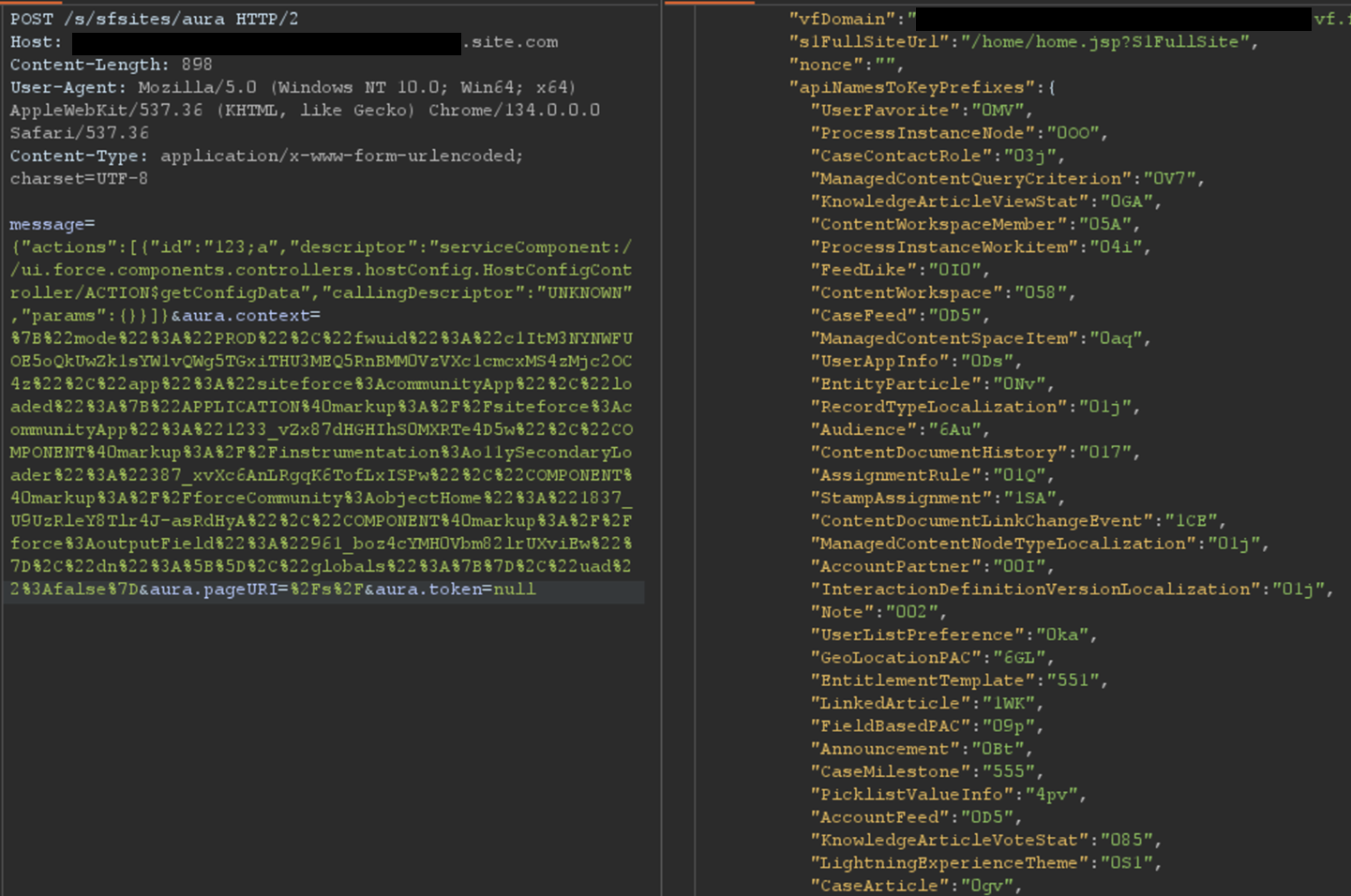
Investigation should include analyzing systems that interact with privileged infrastructure, like developer and signing systems, for malware. Initial access vectors, particularly phishing campaigns (e.g., fake job offers) and malicious web pages, must be investigated. Reviewing logs for interactions with privileged infrastructure, especially sending transactions from secret management platforms or API gateways, is also key. Understanding the full attack path—how access was gained, how privileges were increased, how lateral movement used privileged access, and what actions were done—is key for remediation and preventing recurrence.
Eradication hinges on a coordinated enterprise password reset (EPR)—a planned, organization-wide rotation of credentials and secrets to evict an attacker's ability to reuse stolen material. Initiate EPR when there is evidence or strong suspicion of mass credential exposure (e.g., NTDS.dit dump, DCSync/DCShadow, Kerberoasting, or secrets pulled from code/repos/vaults). Scope EPR to cover domain, local, service, and application/technology accounts; API keys and embedded secrets; cloud sync/bind identities; and third-party integrations. Run it as a cross-functional operation (IR, IAM/PAM, platform, app/dev, cloud ops, SOC, help desk, legal/communications, executives) with staged playbooks, (e.g., dual KRBTGT rotations, trust key resets, service-account updates via PAM/gMSA, and immediate revocation of exposed tokens/keys). Executed well, EPR restores positive control with minimal disruption and removes the attacker's persistence.
Recovery Planning for Critical Systems
A PAM strategy goes beyond immediate incident response to include recovery planning for systems, ensuring resilience in a catastrophic event.
Virtualization Infrastructure Hardening and Protections
Treat vCenter/ESXi, Hyper-V, cloud consoles as Tier-0 choke points. Use dedicated admin identities and/or privileged directories (separate forest or platform-local), vault them, require MFA, and put all hypervisor/out-of-band management on segmented admin networks reachable only from PAWs/jump hosts. For HPE Integrated Lights-Out (iLO) / Integrated Dell Remote Access Computer (iDRAC) / Intelligence Platform Management Interface (IPMI), place on a dedicated management network, disable internet exposure, replace default certs, avoid IPMI-over-LAN, and restrict operators to a tiny vetted group with session recording and aggressive rotation/certificate-based authentication.
Harden ESXi hosts. Enable Lockdown Mode to force host admin via vCenter, reserve direct console/ Direct Console User Interface (DCUI) for break-glass; minimize SSH, disable when not needed; enforce vCenter RBAC and strong password policies. Centralize telemetry in SIEM for VM create/delete, role/permission changes, snapshot/optical disk image (ISO) mounts high-signal events for ransomware staging. Monitor vpxuser across hosts; keep automatic rotation enabled (30-day default) and, if compromise suspected, change rotation interval in vCenter so it propagates, rather than requiring manual changes on hosts.
Harden PAM servers themselves as Tier-0: Dedicated machines, not domain-joined or isolated to a Tier-0 silo; vendor hardening baselines; minimal services; host firewalls; controlled console access; continuous health/telemetry to SIEM. CyberArk's Digital Vault Security Standard and hardening guidance provide concrete checklists.
Backup Infrastructure Protections
Backup infrastructure is the ultimate privileged access target for ransomware operators, as its compromise can stop recovery. Protecting identities that manage backups is a PAM concern, ensuring the "keys to the recovery kingdom" are secure. Organizations must find all dependencies and interconnectivity needs for backup infrastructure availability. The backup architecture should be effective and timely, considering isolated recovery environments and immutable backups—following the 3-2-1 rule of 3 copies in 2 locations and 1 offline.
A defined recovery and reconstitution sequencing strategy, based on business importance, guides restoration. Planning for secure, validated restoration using isolated network enclaves is key to prevent reintroducing malware. Strategies include using unique, separate credentials (not with primary identity provider) with MFA for backup infrastructure, securing offline copies of emergency access credentials, and using unique programmatic service accounts with regular rotation. Implementing firewall rules to restrict admin traffic to a dedicated backup admin network, isolating backup servers from production, and using immutable backups or "write once, read many" (WORM) capabilities are also vital. Finally, admin access to backup infrastructure should be restricted via secure access workstations, and detection strategies should find illegitimate modifications to backup retention and purge policies.
Conclusion: A Proactive Stance on Privileged Access Security
Privileged accounts remain the primary target for attackers, serving as the gateway to financial and operational impact within any organization. The threat landscape, with more credential compromise, account takeovers, and insider threats, shows the need for privileged account monitoring and a mature privileged access management (PAM) program.
Effective PAM goes beyond the narrow definition of privileged accounts, covering human and non-human entities across IT environments and their dependencies. It needs a maturity journey, guiding organizations from an Uninitiated posture to Iterative Optimization—an automated, continuously improving defense. Dedicated PAM solutions are foundational, but must sit on firm system hardening and enforced policy baselines—tiering and SoD, PAWs-only administration, conditional access/MFA, application allow-listing, credential hygiene/rotation—followed by protocol controls such as RDP, SMB, and WinRM. Together these measures reduce attack surface and sharply limit the utility of stolen credentials.
In detection, traditional logging limits mean moving to specialized monitoring. Distinguishing privileged account activity from normal IAM abuse needs more detailed context and a focus on compromise impact. Using advanced analytics, especially machine learning anomaly detection, finds subtle, "in-role but abnormal" behaviors that show compromise or misuse. Nuanced alerting, like prioritizing brute-force attempts against super admin accounts, optimizes security operations. High-fidelity session monitoring gives proof for investigation and compliance. Google SecOps, with its central aggregation, unified data model, and automated response, is a platform to make these PAM monitoring strategies work, enabling real-time threat detection and fast containment.
Finally, a PAM strategy demands practiced incident response and recovery planning. Immediate tactical hardening, better logging, and isolation are key during an incident. Thorough investigation and remediation, including secret rotation and system rebuilding, are needed for eviction and future resilience. Planning for critical system recovery, like key vaults, virtualization infrastructure, and backup systems—with isolated, encrypted, and tested backups—is the ultimate safeguard against loss.
By taking a proactive stance on privileged access security, organizations can reduce risk, protect assets, and build a more defensible and resilient digital ecosystem.