Inside RedVDS: How a single virtual desktop provider fueled worldwide cybercriminal operations
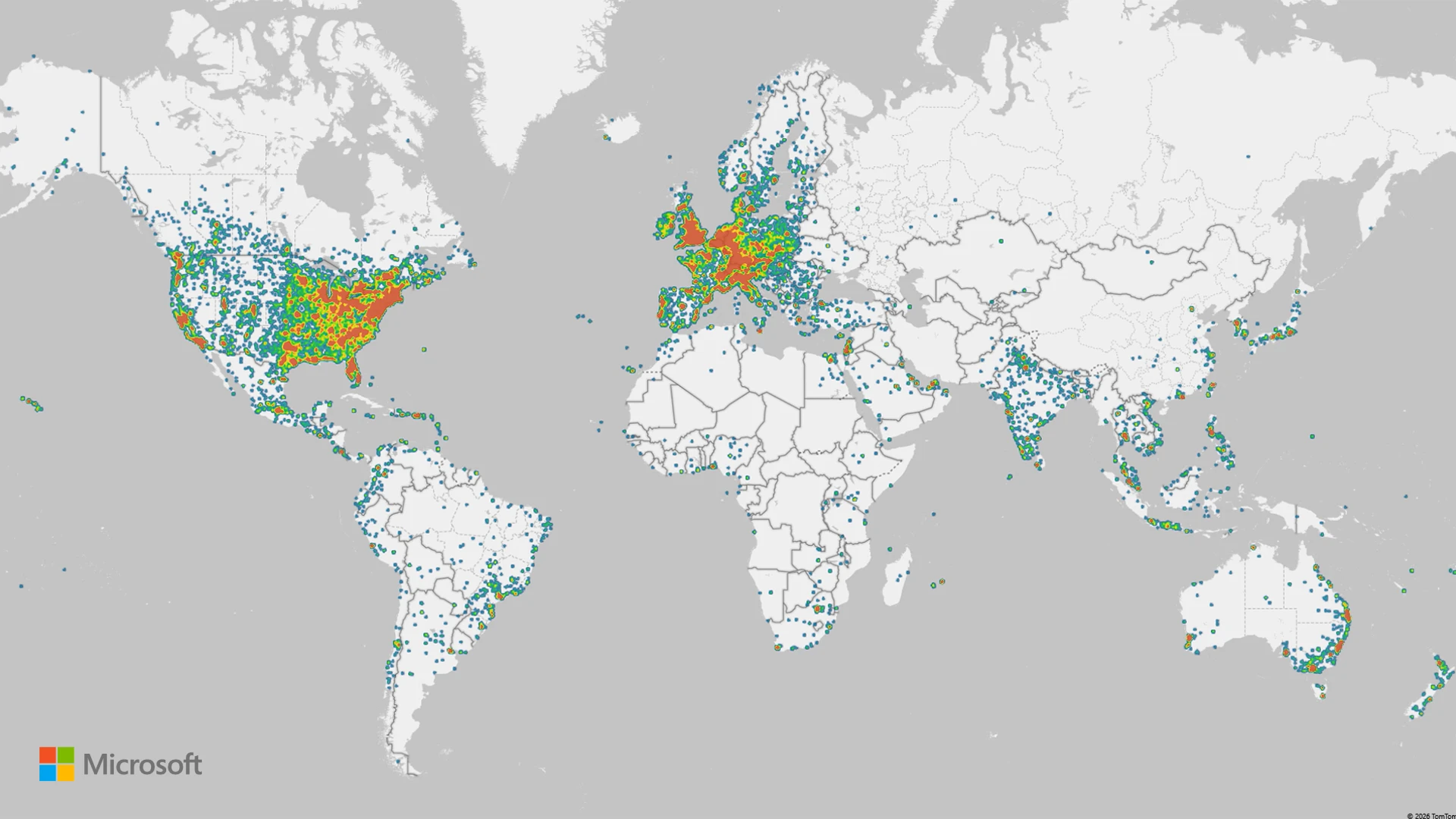
Over the past year, Microsoft Threat Intelligence observed the proliferation of RedVDS, a virtual dedicated server (VDS) provider used by multiple financially motivated threat actors to commit business email compromise (BEC), mass phishing, account takeover, and financial fraud. Microsoft’s investigation into RedVDS services and infrastructure uncovered a global network of disparate cybercriminals purchasing and using to target multiple sectors, including legal, construction, manufacturing, real estate, healthcare, and education in the United States, Canada, United Kingdom, France, Germany, Australia, and countries with substantial banking infrastructure targets that have a higher potential for financial gain. In collaboration with law enforcement agencies worldwide, Microsoft’s Digital Crimes Unit (DCU) recently facilitated a disruption of RedVDS infrastructure and related operations.
RedVDS is a criminal marketplace selling illegal software and services that facilitated and enabled cybercrime. The marketplace offers a simple and feature-rich user interface for purchasing unlicensed and inexpensive Windows-based Remote Desktop Protocol (RDP) servers with full administrator control and no usage limits – a combination eagerly exploited by cybercriminals. Microsoft’s investigation into RedVDS revealed a single, cloned Windows host image being reused across the service, leaving unique technical fingerprints that defenders could leverage for detection.
Microsoft tracks the threat actor who develops and operates RedVDS as Storm-2470. We have observed multiple cybercriminal actors, including Storm-0259, Storm-2227, Storm-1575, Storm-1747, and phishing actors who used the RacoonO365 phishing service prior its coordinated takedown, leveraging RedVDS infrastructure. RedVDS launched their website in 2019 and has been operating publicly since to offer servers in locations including the United States, United Kingdom, Canada, France, Netherlands, and Germany. The primary website used the redvds[.]com domain, with secondary domains at redvds[.]pro and vdspanel[.]space.
RedVDS uses a fictitious entity claiming to operate and be governed by Bahamian Law. RedVDS customers purchased the service through cryptocurrency, primarily Bitcoin and Litecoin, adding another layer of obfuscation to illicit activity. Additionally, RedVDS supports a broad range of digital currency, including Monero, Binance Coin, Avalanche, Dogecoin, and TRON.
The mass scale of operations facilitated by RedVDS infrastructure and roughly US $40 million in reported fraud losses driven by RedVDS‑enabled activity in the United States alone since March 2025 underscore the threat of an invisible infrastructure providing scalability and ease for cybercriminals to access target networks. In this blog, we share our analysis of the technical aspects of RedVDS: its infrastructure, provisioning methods, and the malware and tools deployed on RedVDS hosts. We also provide recommendations to protect against RedVDS-related threats such as phishing attacks.

Uncovering the RedVDS Infrastructure
Microsoft Threat Intelligence investigations revealed that RedVDS has become a prolific tool for cybercriminals in the past year, facilitating thousands of attacks including credential theft, account takeovers, and mass phishing. RedVDS offers its services for a nominal fee, making it accessible for cybercriminals worldwide.
Over time, Microsoft Threat Intelligence identified attacks showing thousands of stolen credentials, invoices stolen from target organizations, mass mailers, and phish kits, indicating that multiple Windows hosts were all created from the same base Windows installation. Additional investigations revealed that most of the hosts were created using a single computer ID, signifying that the same Windows Eval 2022 license was used to create these hosts. By using the stolen license to make images, Storm-2470 provided its services at a substantially lower cost, making it attractive for threat actors to purchase or acquire RedVDS services.
Anatomy of RedVDS Infrastructure


Service model and base image: RedVDS provided virtual Windows cloud servers, which were generated from a single Windows Server 2022 image, through RDP. All RedVDS instances identified by Microsoft used the same computer name, WIN-BUNS25TD77J, an anomaly that stood out because legitimate cloud providers randomize hostnames. This host fingerprint appears in RDP certificates and system telemetry, serving as a core indicator of RedVDS activity. The underlying trick is that Storm-2470 created one Windows virtual machine (VM) and repeatedly cloned it without customizing the system identity.


Automated provisioning: The RedVDS operator employed Quick Emulator (QEMU) virtualization combined with VirtIO drivers to rapidly generate cloned Windows instances on demand. When a customer ordered a server, an automated process copied the master VM image (with the pre-set hostname and configuration) onto a new host. This yielded new servers that are clones of the original, using the same hostname and baseline hardware IDs, differing only by IP address and hostname prefix in some cases. This uniform deployment strategy allowed RedVDS to stand up fresh RDP hosts within minutes, a scalability advantage for cybercriminals. It also meant that all RedVDS hosts shared certain low-level identifiers (for example, identical OS installation IDs and product keys), which defenders could potentially pivot on if exposed in telemetry.

Payment and access: The RedVDS service operated using an online portal, RedVDS[.]com, where access was sold for cryptocurrency, often Bitcoin, to preserve anonymity. After payment, customers received credentials to sign in using Remote Desktop. Notably, RedVDS did not impose usage caps or maintain activity logs (according to its own terms of service), making it attractive for illicit use. Additionally, the use of unlicensed software allowed RedVDS to offer its services at a nominal cost, making it more accessible for threat actors as a prolific tool for cybercriminal activity.
Hosting footprint: RedVDS did not own physical datacenters; instead, it rented servers from third-party hosting providers to run its service. We traced RedVDS nodes to at least five hosting companies in the United States, Canada, United Kingdom, France, and Netherlands. These providers offer bare-metal or virtual private server (VPS) infrastructure. By distributing across multiple providers and countries, RedVDS could provision IP addresses in geolocations close to targets (for example, a US victim might be attacked from a US-based IP address), helping cybercriminals evade geolocation-based security filters. It also meant that RedVDS traffic blended with normal data center traffic, requiring defenders to rely on deeper fingerprints (like the host name or usage patterns) rather than IP address alone.

We observed RedVDS most commonly hosted within the following AS/ASNs from December 5 to 19, 2025:

Malware and tooling on RedVDS hosts
RedVDS is an infrastructure service that facilitated malicious activity, but unlike malware, it did not perform harmful actions itself; the threat came from how criminals used the servers after provisioning. Our investigation found that RedVDS customers consistently set up a standard toolkit of malicious or dual-use software on their rented servers to facilitate their campaigns. By examining multiple RedVDS instances, we identified a recurring set of tools:
- Mass mailer utilities: A variety of spam/phishing email tools were installed to send bulk emails. We observed examples like SuperMailer, UltraMailer, BlueMail, SquadMailer, and Email Sorter Pro/Ultimate on RedVDS machines. These programs are designed to import lists of email addresses and blast out phishing emails or scam communications at scale. They often include features to randomize content or schedule sends, helping cybercriminals manage large phishing campaigns directly from the RedVDS host.
- Email address harvesters: We found tools, such as Sky Email Extractor, that allowed cybercriminals to scrape or validate large numbers of email addresses. These helped build victim lists for phishing. We also found evidence of scripts or utilities to sort and clean email lists (to remove bounces, duplicates, and others), indicating that RedVDS users were managing mass email operations end-to-end on these servers.
- Privacy and OPSEC tools: RedVDS hosts had numerous applications to keep the operators’ activities under the radar. For example, we observed installations of privacy-focused web browsers (likeWaterfox, Avast Secure Browser, Norton Private Browser), and multiple virtual private network (VPN) clients (such as NordVPN and ExpressVPN). Cybercriminals likely used these to route traffic through other channels (or to access criminal forums safely) from their RedVDS server, and to ensure any browsing or additional communications from the server were masked. Also present was SocksEscort, a proxy/socksifier tool, hinting that some RedVDS tenants ran malware that required SOCKS proxies to reach targets.
- Remote access and management: Many RedVDS instances had AnyDesk installed. AnyDesk is a legitimate remote desktop tool, suggesting that criminals might have used it to sign in to and control their RedVDS boxes more conveniently or even share access among co-conspirators.
- Automation and scripting: We found evidence of scripting environments and attempts to use automation services. For example, Python was installed on some RedVDS hosts (with scripts for tasks like parsing data), and one actor attempted to use Microsoft Power Automate (Flow) to programmatically send emails using Excel, though their attempt was not fully successful. Additionally, some RedVDS users leveraged ChatGPT or other OpenAI tools to overcome language barriers when writing phishing lures. Consequently, non‑English‑speaking operators could generate more polished English‑language lure emails by using AI tools on the compromised RedVDS host.

Below is a summary table of tool categories observed on RedVDS hosts and their primary purpose:
| Category | Examples | Primary use |
| Mass mailing | SuperMailer, UltraMailer, BlueMail, SquadMailer | Bulk phishing email distribution and campaign management |
| Email address harvesting | Sky Email Extractor, Email Sorter Pro/Ultimate | Harvesting target emails and cleaning email lists (list hygiene) |
| Privacy and VPN | Waterfox, Avast Secure Browser, Norton Private Browser, NordVPN, Express VPN | Operational security (OPSEC): anonymizing browsing, hiding server’s own traffic, geolocation spoofing |
| Remote admin | AnyDesk | Convenient multi-host access for cybercriminals; remote control of RedVDS servers beyond RDP (or sharing access) |
| Website | Business or service |
| www.apollo.io | Business-to-business (B2B) sales lead generator |
| www.copilot.microsoft.com | Microsoft Copilot |
| www.quillbot.com | Writing assistant |
| www.veed.io | Video editing |
| www.grammarly.com | Writing assistant |
| www.braincert.com | E-learning tools |
| login.seamless.ai | B2B sales lead generator |
Mapping the RedVDS attack chain
Threat actors used RedVDS because it provided a highly permissive, low-cost, resilient environment where they could launch and conceal multiple stages of their operation. Once provisioned, these cloned Windows hosts gave actors a ready‑made platform to research targets, stage phishing infrastructure, steal credentials, hijack mailboxes, and execute impersonation‑based financial fraud with minimal friction. Threat actors benefited from RedVDS’s unrestricted administrative access and negligible logging, allowing them to operate without meaningful oversight. The uniform, disposable nature of RedVDS servers allowed cybercriminals to rapidly iterate campaigns, automate delivery at scale, and move quickly from initial targeting to financial theft.

Reconnaissance
RedVDS operators leveraged their provisioned server to gather intelligence on fraud targets and suppliers, collecting organizational details, payment workflows, and identifying key personnel involved in financial transactions. This information helped craft convincing spear-phishing emails tailored to the victim’s business context.
During this phase, cybercriminals also researched tools and methods to optimize their campaigns. For example, Microsoft observed RedVDS customers experimenting with Microsoft Power Automate to attempt to automate the delivery of phishing emails directly from Excel files containing personal attachments. These attempts were unsuccessful, but their exploration of automation tools showed a clear intent to streamline delivery workflows and scale their attacks.
Resource development and delivery
Next, RedVDS operators developed their phishing capabilities by transforming its permissive virtual servers into a full operational infrastructure. They did this by purchasing phishing-as-a-service (PhaaS) infrastructure or manually assembling their own tooling, including installing and configuring phishing kits, using mass mailer tools, email address harvesters, and evasion capabilities, such as VPNs and remote desktop tools. Operators then built automation pipelines by writing scripts to import target lists, generating PDF or HTML lure attachments, and automating sending cycles to support high-volume delivery. While RedVDS itself only provided permissive VDS hosting, operators deployed their own automation tooling on these servers to enable large-scale phishing email delivery.
Once their tooling is in place, operators began staging their phishing infrastructure by registering domains that often masqueraded as legitimate domains, setting up phishing pages and credential collectors, and testing the end-to-end delivery before launching their attacks.
Account compromise
RedVDS operators gained initial access through successful phishing attacks. Targets received phishing emails crafted to appear legitimate. When a recipient clicked the malicious link or opened the lure, they are redirected to a phishing page that mimicked a trusted sign-in portal. Here, credentials are harvested, and in some cases, cybercriminals triggered multifactor authentication (MFA) prompts that victims approved, granting full access to accounts.
Credential theft and mailbox takeover
Once credentials were captured through phishing, RedVDS facilitated the extraction and storage of replay tokens or session cookies. These artifacts allowed cybercriminals to bypass MFA and maintain persistent access without triggering additional verification, streamlining account takeover.
With valid credentials or tokens, cybercriminals signed in to the compromised mailbox. They searched for financial conversations, pending invoices, and supplier details, copying relevant emails to prepare for impersonation and fraud. This stage often included monitoring ongoing threads to identify the most opportune moment to intervene.
Impersonation infrastructure development
Building on the initial RedVDS footprint, operators expanded their infrastructure to large-volume phishing and impersonation activity. A critical component of this phase was the registration and deployment of homoglyph domains, lookalike domains crafted to mimic legitimate supplier or business partners with near-indistinguishable character substitutions. During the investigation, Microsoft uncovered over 7,300 IP addresses linked to RedVDS infrastructure that collectively hosted more than 3,700 homoglyph domains within a 30-day period.
Using these domains, operators created impersonation mailboxes and inserted themselves into ongoing email threads, effectively hijacking trusted communications channels. This combination of homoglyph domain infrastructure, mailbox impersonation, and thread hijacking formed the backbone of highly convincing BEC operations and enabled seamless social engineering that pressured victims into completing fraudulent financial transactions.
Social engineering
Using the impersonation setup, cybercriminals further injected themselves into legitimate conversations with suppliers or internal finance teams. They sent payment change requests or fraudulent invoices, leveraging urgency and trust to manipulate targets into transferring funds. For example, Microsoft Threat Intelligence observed multiple actors, including Storm-0259, using RedVDS to deliver fake unpaid invoices to businesses that directed the recipient to make a same day payment to resolve the debt. The email included PDF attachments of the fake invoice, banking details to make the payment, and contact details of the impersonator.
Payment fraud
Finally, the victim processed the fraudulent payment, transferring funds to an attacker-controlled mule account. These accounts were often part of a larger laundering network, making recovery difficult.
Common attacks using RedVDS infrastructure
Mass phishing: In most cases, Microsoft observed RedVDS customers using RedVDS as primary infrastructure to conduct mass phishing. Prior to sending out emails, cybercriminals linked to RedVDS infrastructure abused Microsoft 365 services to register fake tenants posing as legitimate local businesses or organizations. These cybercriminals also installed additional legitimate applications on RedVDS server, including Brave browser, likely to mask browsing activity; Telegram Desktop, Signal Desktop, and AnyTime Desktop to facilitate their operations; as well as mass mailer tools such as SuperMailer, UltraMailer, and BlueMail.
Password spray: Microsoft observed actors conducting password spray attacks using RedVDS infrastructure to gain initial access to target systems.
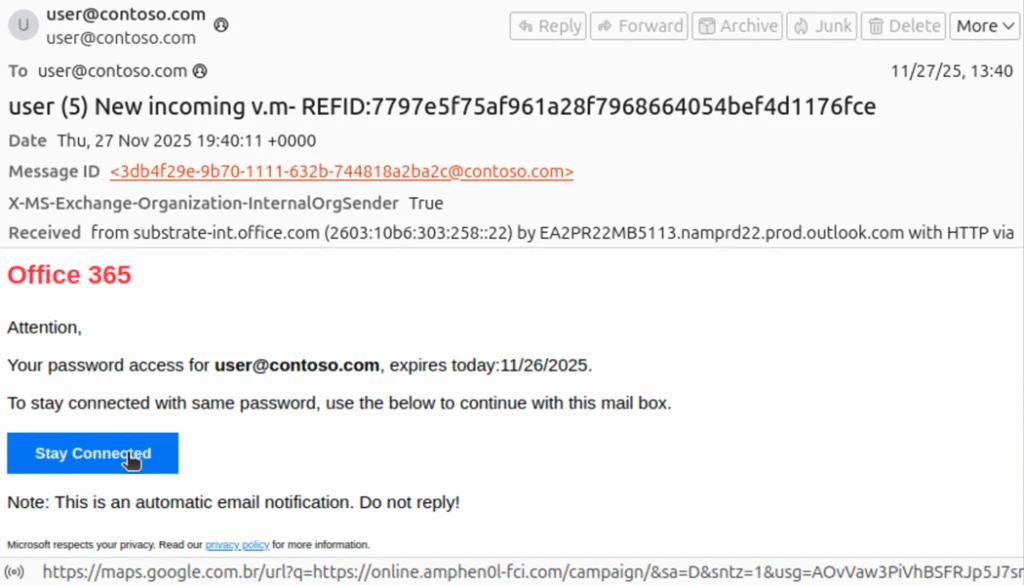
Spoofed phishing attacks: Microsoft has observed actors using RedVDS infrastructure to send phishing messages that appear as internally sent email communications by spoofing the organizations’ domains. Threat actors exploit complex routing scenarios and misconfigured spoof protections to carry out these email campaigns, with RedVDS providing the means to send the phishing emails in majority of cases. This phishing attack vector does not affect customers whose Microsoft Exchange mail exchanger (MX) records point to Office 365; these tenants are protected by native built-in spoofing detections.
Lures used in these attacks are themed around voicemails, shared documents, communications from human resources (HR) departments, password resets or expirations, and others, leading to credential phishing. Microsoft has also observed a campaign leveraging this vector to conduct financial scams against organizations, attempting to trick them into paying false invoices to fraudulently created banking accounts. Phishing messages sent through this method might seem like internal communications, making them more effective. Compromised credentials could result in data theft, business email compromise, or financial loss, all requiring significant remediation.
Business email compromise/Account takeover: Microsoft observed RedVDS customers using the infrastructure to conduct BEC attacks that included account takeovers of organizations or businesses. In several cases, these actors also created homoglyph domains to appear legitimate in payment fraud operations. During email takeover operations, RedVDS customers used compromised accounts in BEC operations to conduct follow-on activity. In addition to mass mailers, these cybercriminals signed in to user mailboxes and used those accounts to conduct lateral movement within the targeted organization’s environment and look for other possible users or contacts, allowing them to conduct reconnaissance and craft more convincing phishing emails. Following successful account compromise, the cybercriminals often created an invitation lure and uploaded it to the victim’s SharePoint. In these cases, Microsoft observed the cybercriminals exfiltrating financial data, namely banking information from the same organizations that were impersonated in addition to mass downloading of invoices, and credential theft.
Defending against RedVDS-related operations
RedVDS is an infrastructure provider that facilitated criminal activity, and it is not by itself a malware tool that deploys malicious code. This activity is not exclusively abusing Microsoft services but likely other providers as well.
While Microsoft notes that the organizations at most risk for RedVDS-related operations are legal, construction, manufacturing, real estate, healthcare, and education, the activity conducted by malicious actors using RedVDS are common attacks that could affect any business or consumers, especially with an established relationship where high volume of transactions are exchanged.
The overwhelming majority of RedVDS-related activity comprises social engineering, phishing operations, and business email compromise. Microsoft recommends the following recommendations to mitigate the impact of RedVDS-related threats.
Preventing phishing attacks
Defending against phishing attacks begins at the primary gateways: email and other communication platforms.
- Review our recommended settings for Exchange Online Protection and Microsoft Defender for Office 365 to ensure your organization has established essential defenses and knows how to monitor and respond to threat activity.
- Invest in user awareness training and phishing simulations. Attack simulation training in Microsoft Defender for Office 365, which also includes simulating phishing messages in Microsoft Teams, is one approach to running realistic attack scenarios in your organization.
- Follow Microsoft’s security best practices for Microsoft Teams.
- Configure the Microsoft Defender for Office 365 Safe Links policy to apply to internal recipients.
Hardening credentials and cloud identities is also necessary to defend against phishing attacks, which seek to gain valid credentials and access tokens. As an initial step, use passwordless solutions like passkeys and implement MFA throughout your environment:
- Use the Microsoft Authenticator app for passkeys and MFA, and complement MFA with conditional access policies, where sign-in requests are evaluated using additional identity-driven signals.
- Conditional access policies can also be scoped to strengthen privileged accounts with phishing resistant MFA.
- Your passkey and MFA policy can be further secured by only allowing MFA and passkey registrations from trusted locations and devices
Preventing business email compromise (BEC)
Organizations can mitigate BEC risks by focusing on key defense measures, such as implementing comprehensive social engineering training for employees and enhancing awareness of phishing tactics. Educating users about identifying and reporting suspicious emails is critical. Essential technical measures include securing device services, including email settings through services like Microsoft Defender XDR, enabling MFA, and promoting strong password protection. Additionally, using secure payment platforms and tightening controls around financial processes can help reduce risks related to fraudulent transactions. Collectively, these proactive measures strengthen defenses against BEC attacks.
- Ensure that admin and user accounts are distinct by using Privileged Identity Management or dedicated accounts for privileged tasks, limiting overprivileged permissions. Adaptive Protection can automatically apply strict security controls on high-risk users, minimizing the impact of potential data security incidents.
- Avoid opening emails, attachments, and links from suspicious sources. Verify sender identities before interacting with any links or attachments. In most RedVDS-related BEC cases, once the actor took over an email account, the victim’s inbox was studied and used to learn about existing relationships with other vendors or contacts, making this step extra crucial. Educate employees on data security best practices through regular training on phishing indicators, domain mismatches, and other BEC red flags. Leverage Microsoft curated resources and training and deploy phishing risk-reduction tool to conduct simulations and targeted education. Encourage users to browse securely with Microsoft Edge or other SmartScreen-enabled browsers to block malicious websites, including phishing domains.
- Enforcing robust email security settings is critical for preventing spoofing, impersonation, and account compromise, which are key tactics in BEC attacks. Most domains sending mail to Office 365 lack valid DMARC enforcement, making them susceptible to spoofing. Microsoft 365 and Exchange Online Protection (EOP) mitigate this risk by detecting forged “From” headers to block spoofed emails and prevent credential theft. Spoof intelligence, enabled by default, adds an extra layer of security by identifying spoofed senders.
Microsoft Defender XDR detections
Microsoft Defender XDR detects a wide variety of post-compromise activity leveraging the RedVDS service, including:
- Possible BEC-related inbox rule (Microsoft Defender for Cloud apps)
- Compromised user account in a recognized attack pattern (Microsoft Defender XDR)
- Risky sign in attempt following a possible phishing campaign (Microsoft Defender for Office 365)
- Risky sign-in attempt following access to malicious phishing email (Microsoft Defender for Cloud Apps)
- Suspicious AnyDesk installation (Microsoft Defender for Endpoint)
- Password spraying (Microsoft Defender for Endpoint)
Microsoft Defender XDR coordinates detection, prevention, investigation, and response across endpoints, identities, email, apps to provide integrated protection against threats. Customers with provisioned access can also use Microsoft Security Copilot in Microsoft Defender to investigate and respond to incidents, hunt for threats, and protect their organization with relevant threat intelligence.
Microsoft Security Copilot
Security Copilot customers can use the standalone experience to create their own prompts or run the following prebuilt promptbooks to automate incident response or investigation tasks related to this threat:
- Incident investigation
- Microsoft User analysis
- Threat actor profile
- Threat Intelligence 360 report based on MDTI article
- Vulnerability impact assessment
Note that some promptbooks require access to plugins for Microsoft products such as Microsoft Defender XDR or Microsoft Sentinel.
Threat intelligence reports
Microsoft Defender XDR customers can use the following threat analytics reports in the Defender portal (requires license for at least one Defender XDR product) to get the most up-to-date information about the threat actor, malicious activity, and techniques discussed in this blog. These reports provide the intelligence, protection information, and recommended actions to prevent, mitigate, or respond to associated threats found in customer environments.
Microsoft Defender XDR threat analytics
Microsoft Security Copilot customers can also use the Microsoft Security Copilot integration in Microsoft Defender Threat Intelligence, either in the Security Copilot standalone portal or in the embedded experience in the Microsoft Defender portal to get more information about this threat actor.
Indicators of compromise
The following table lists the domain variants belonging to RedVDS provider.
| Indicator | Type | Description |
| Redvds[.]com | Domain | Main website |
| Redvds[.]pro | Domain | Backup site |
| Redvdspanel[.]space | Domain | Sub-panel |
| hxxps://rd[.]redvds[.]com | URL | RedVDS dashboard |
| WIN-BUNS25TD77J | Host name | Host name where RedVDS activity originates from |
Learn more
For the latest security research from the Microsoft Threat Intelligence community, check out the Microsoft Threat Intelligence Blog.
To get notified about new publications and to join discussions on social media, follow us on LinkedIn, X (formerly Twitter), and Bluesky.
To hear stories and insights from the Microsoft Threat Intelligence community about the ever-evolving threat landscape, listen to the Microsoft Threat Intelligence podcast.
The post Inside RedVDS: How a single virtual desktop provider fueled worldwide cybercriminal operations appeared first on Microsoft Security Blog.